Unified Threat Management (UTM) offers a complete security protection system that leaves no gaps for hackers to exploit. Replacing your anti-virus and firewall systems with a full UTM package makes sense because those separate cybersecurity services should be working together in order to address the serious system threats that are constantly evolving.
Here is our list of the best Unified Threat Management software packages:
- ManageEngine Log360 EDITOR’S CHOICE This all-in-one SIEM solution combines integrated DLP and CASB functionality to provide real-time threat detection, centralized log management, and compliance reporting across on-premises, cloud, and hybrid environments. The platform is designed to run on Windows Server. Start a 30-day free trial.
- ESET Protect MDR This threat detection and response package is managed by a team of cybersecurity experts. Endpoint agents run on Windows, Linux, macOS, iOS, and Android.
- Fortinet FortiGate UTM This physical appliance is produced by a leading network security provider and creates a “security fabric” for the entire organization. SD-WAN options are also available to extend protection over several sites.
- Datadog Security Monitoring This Cloud-based cybersecurity system collected event data from every part of your system and identifies any activity that is suspicious. AI-based detection methods narrow down threat identification, so you don’t get overwhelmed by false-positive reporting.
- Check Point Quantum NGFW This range of firewall appliances has units for all sizes of businesses. It is positioned as the network gateway and can detect all external threats by examining incoming and outgoing traffic.
- Cisco UTM This package is offered by the network equipment giant and so is particularly strong on network security but also offers monitoring for endpoints. Offered as a physical or virtual appliance or as a cloud service.
- SonicWall UTM A system security package that can be built into SonicWall appliances that connect to the network and monitor all activity. Also offered as a virtual appliance.
- Huawei Unified Security Gateway (USG) A series of network appliances that include onboard system security software. That software can also be run separately as a virtual appliance.
- WatchGuard Firebox UTM This is a range of physical appliances that implement system-wide security monitoring. Also available as a cloud-based service or a virtual appliance.
UTMs and NextGen-Firewalls
The traditional approach is to deploy several single-function security products from different vendors. However, this method requires installing and integrating several products, which of course involves individual familiarity, learning different management consoles, and managing updates and upgrades from several vendors. Next-generation firewalls (NGFWs) are also a viable option as they are much more effective than traditional firewalls, but still lack important features that are critical to detecting and responding to all the latest threats. But in recent times, organizations are embracing a concept known as Unified Threat Management (UTM) solution that combines two or more security services into one application or appliance.
UTM is a term used to describe an all-in-one approach to information security, where a single converged platform ( software or hardware) provides multiple security functions such as network firewalls, intrusion detection and prevention, gateway anti-virus, business VPN, email and web content filtering, etc. UTM’s seemingly appeal stems from the fact that it simplifies information security management by providing a single management and reporting point for the security administrator rather than managing multiple products from different vendors. Instead of having several single-function applications or appliances, network administrators can centrally administer their security defenses from one box.
Evaluating UTM tools
When evaluating a UTM product, you need to ensure that the device’s different functionalities address your security risks and policy requirements. You don’t want to get caught up in the sales and marketing hype that tends to surround most security products. There are key questions you need to consider, such as: What security problem are you trying to solve? Is a UTM solution right for your organization? What security features are most important? Do you require the UTM to support geographically dispersed branch locations and remote workers? What is the infrastructure bandwidth for your environment, and how many users and devices does the organization need to support today and in the future? Is it easy to deploy, manage and maintain? Other factors to consider include performance, scalability, vendor support, and of course cost.
The best UTM Software:
Unified Threat Management breaks down the silos between security services for different system elements. We discover the best UTM software available on the market today.
There are quite a few UTM systems on the market today. However, deciding what to look for and narrowing down the field can be time-consuming.
Our methodology for selecting a Unified Threat Management system
We reviewed the market for UTM solutions and analyzed tools based on the following criteria:
- A package that will protect endpoints, networks, and cloud resources
- A centralized system that offers a single console for threat management
- The option to extend centralized threat protection over several sites
- A secure communication path for data transfers over the internet
- Zero-day threat protection
- A free trial or a money-back guarantee to reduce the risk of being fleeced
- Value for money from a single package that replaces individual cybersecurity systems
With these selection criteria in mind, we identified a shortlist of centralized UTM packages that provide excellent cybersecurity protection at a reasonable price.
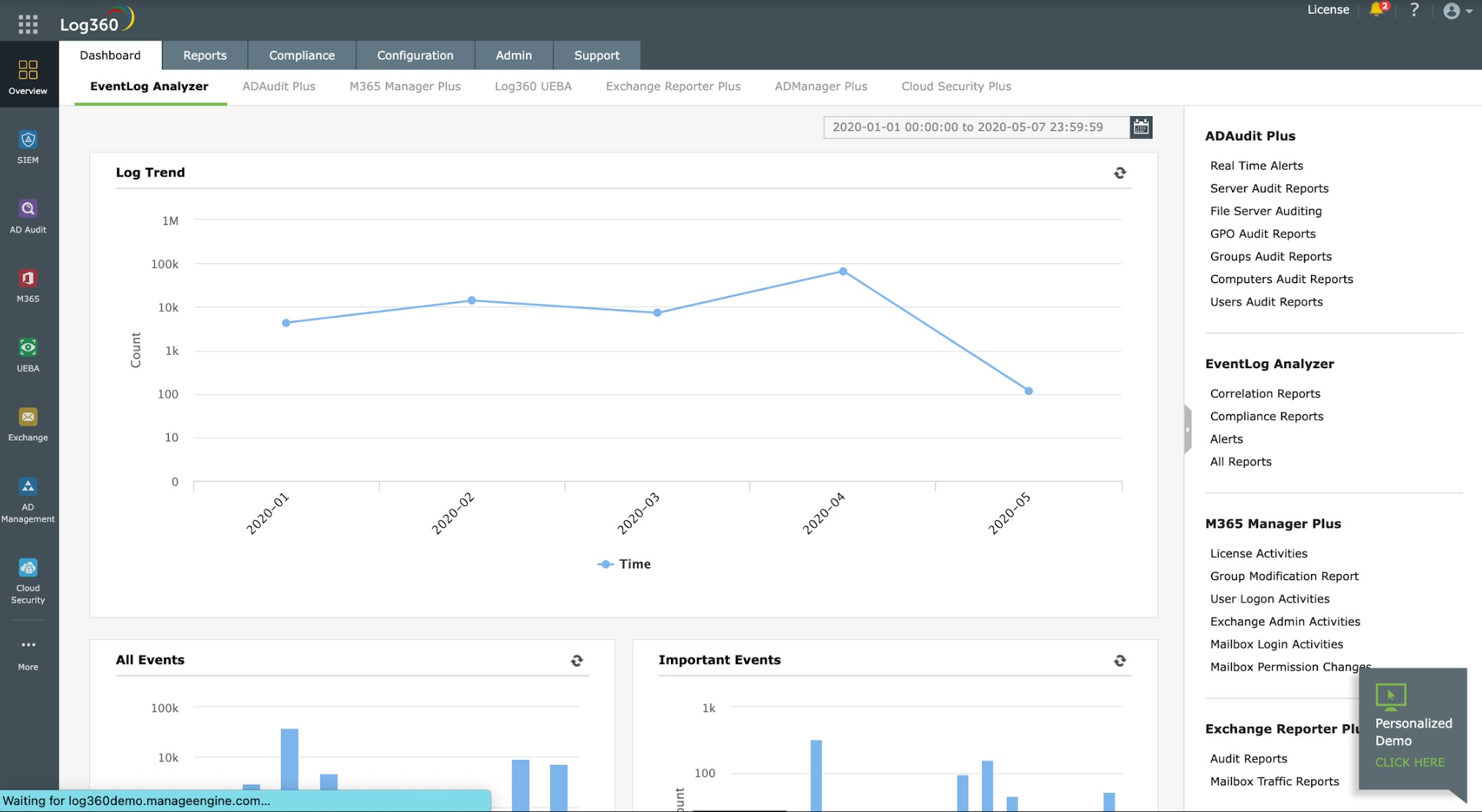
1. ManageEngine Log360 (FREE TRIAL)
ManageEngine Log360 is an on-premises system that runs on Windows Server. The service isn’t limited to examining events on its host because it can ingest log messages from all other endpoints on the network and also on cloud platforms. This means that Log360 can unify threat hunting for many platforms. The package includes a library of agents for all of the major operating systems, including Linux and cloud systems, such as AWS and Azure. The agents interact with the operating system and more than 700 software packages to collect log messages, which are forwarded to a central log server, where they are converted into a unified format.
Key Features:
- Unified Threat Management: Centralizes threat detection across on-premises, cloud, and hybrid environments with extensive OS and software integration.
- Comprehensive Security: Integrates SIEM capabilities, cloud security, automated threat response, and compliance reporting into a single package.
- File Integrity Monitoring: Tracks data access and file changes, crucial for compliance with various data protection standards.
- Centralized Log Oversight: Aggregates, analyzes, and stores logs from multiple sources, providing visibility and supporting security investigations.
- Dark Web Surveillance: Continuously scans the dark web for exposed credentials and sensitive personal information, helping organizations identify potential risks.
Why do we recommend it?
ManageEngine Log360 is a bundle of ManageEngine packages that relate to log file management and scanning. There is a SIEM at the heart of this system, which is the main threat management tool in the bundle. Other elements provide cloud security, automated threat response, and compliance reporting.
While all of the tools in this list centralize threat management, most of the options available today are cloud-based. Not everyone is comfortable with cloud services and if you are someone that prefers to host your security software in-house, this is the best option.
The Log360 package provides many security features, which include file integrity monitoring. The tool records all data access and file change events, which is greater for data security standards compliance. This system also produces compliance reports for GDPR, GLBA, HIPAA, PCI DSS, FISMA, and SOX.
Who is it recommended for?
This is a large bundle of services that includes user activity tracking and account auditing to protect against insider threats and account takeovers. Therefore, it is way more than small businesses need. Companies that used Active Directory for their access rights management are particularly suited to this system. The tool is an on-premises package for Windows Server.
Pros:
- In-depth Security Features: Offers a rich set of functionalities including live log tailing, manual analytical tools, log management, and file protection.
- Compliance Reporting: Generates reports for GDPR, HIPAA, PCI DSS, and more, facilitating adherence to regulatory requirements.
- Agent-Based Data Collection: Provides a comprehensive library of agents for efficient log message collection from diverse systems.
- Threat Feed Integration: Supports importing Sigma rules to identify and flag suspicious activity across the network.
- Automated Correlation: Uses predefined correlation rules to improve detection of complex or hidden threats.
Cons:
- Platform Limitation: Primarily designed for Windows Server, limiting server deployment options to this OS despite having an agent for Linux.
ManageEngine Log360 is available for a 30-day free trial.
EDITOR'S CHOICE
ManageEngine Log360 is our number one choice for a unified threat management platform, providing a comprehensive solution for monitoring, detecting, and responding to security threats across an organization’s network infrastructure. As cyber threats grow increasingly sophisticated, Log360 distinguishes itself by integrating key security capabilities—such as SIEM, User and Entity Behavior Analytics (UEBA), and Active Directory monitoring—into a single platform. A standout feature of Log360 is its ability to collect and correlate log data from diverse sources, including servers, network devices, applications, and endpoints. This centralized visibility enables security teams to identify suspicious activity and potential threats more effectively. By applying advanced correlation rules, the platform can detect security incidents that might otherwise go unnoticed, reducing the time required to respond to attacks. The platform also includes real-time threat intelligence, helping organizations stay updated on emerging risks. Using a combination of predefined and custom detection rules, supported by AI and machine learning, Log360 can automatically flag abnormal behavior or potential security threats. This proactive approach gives organizations an edge in anticipating and mitigating cyberattacks. Log360’s adaptable console and customizable reporting tools allow security teams to analyze events and generate actionable insights efficiently. It also delivers robust compliance reporting, making it a practical choice for organizations with regulatory obligations.
Download: Get a 30-day FREE Trial
Official Site: https://www.manageengine.com/log-management/download.html
OS: Windows Server
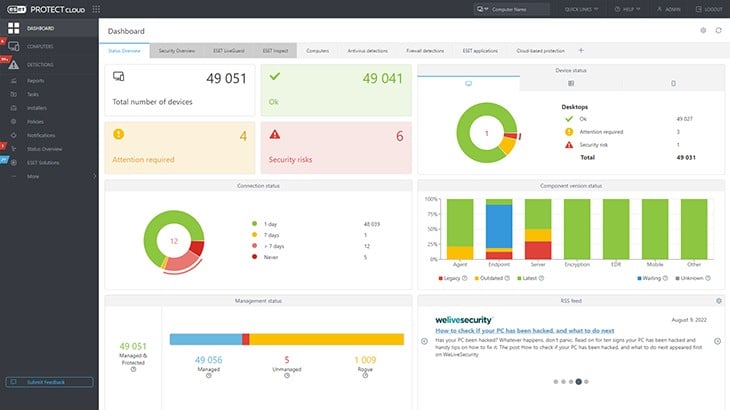
2. ESET Protect MDR
ESET Protect MDR is a centralized XDR system that is hosted on the cloud but draws source data for threat hunting from endpoint protection software. That anti-virus package will run on Windows, macOS, Linux, iOS, and Android. While that AV will detect and stop malware and human threats, the central XDR can identify company-wide attacks.
Key Features:
- Managed Detection and Response: Offers a managed security service, including endpoint protection, centralized threat hunting, automated responses, and vulnerability scanning.
- Comprehensive Endpoint Protection: Provides antivirus protection across a wide range of operating systems, including Windows, macOS, Linux, iOS, and Android.
- XDR Capabilities: Enhances threat detection with Extended Detection and Response (XDR), identifying broader company-wide attack patterns.
Why do we recommend it?
ESET Protect MDR is a managed security service. It provides the technicians to run the ESET Protect software, which includes endpoint protection, centralized threat hunting, automated responses, vulnerability scanning, and patch management. This service can also protect cloud resources and email systems.
MDR stands for Managed Detection and Response. This is an add-on to one of the ESET Protect XDR packages and includes technicians to monitor the security software. The lowest edition of ESET Protect is an AV. This won’t give you endpoint detection and response but it acts as a device agent for the higher plans. Those three upper plans each offer successively longer lists of services.
The ESET Protect Advanced system is the entry-level SIEM service that supplements the abt-virus activities of the endpoint units. ESET Protect Complete plan provides automated responses to detected threats. This edition also includes email security and protection for cloud services. This plan also provides a vulnerability scanner and a patch manager.
While the ESET Protect Complete system will send response instructions back to the ESET endpoint agents, the top plan, ESET Protect Elite will interface with third-party security tools as well.
Although these plans provide automated responses, there will always be borderline situations that need to be assessed. The vulnerability can fix out-of-date through its connection to the patch manager in the ESET package, but it won’t fix other detected weaknesses. For these reasons, buyers of the ESET system will need cybersecurity experts on their staff. Those companies that do not have such expertise available would benefit from the ESET Protect MDR system.
The top plans of ESET Protect don’t just detect threats, they also scan for system vulnerabilities. The package will fix some of those weaknesses with a patch manager or issue guidance on what system changes need to be made. ESET Protect MDR provides security management for these tasks.
Who is it recommended for?
The ESET Protect MDR plan is ideal for those businesses that can’t source suitably qualified cybersecurity experts and those that are too small to provide full-time employment for such technicians. The managed security service provider is able to provide a round-the-clock security operations center for businesses of all sizes.
Pros:
- 24/7 Monitoring: Ensures continuous oversight of security posture with managed services, ideal for businesses lacking in-house cybersecurity expertise.
- Customizable Security Packages: Offers flexibility with multiple security plans tailored to different organizational needs, from basic antivirus to complete security suites.
- Vulnerability Management: Integrates a vulnerability scanner and patch manager to address system weaknesses and maintain up-to-date defenses.
Cons:
- No Free Trial: Lacks a trial option to evaluate the service before commitment, which may hinder preliminary assessment for potential users.
The MDR system is a technician add-on service to your choice of ESET Protect plan, so there isn’t a free trial for this system. You need to contact ESET to discuss your requirements.
3. Fortinet FortiGate UTM
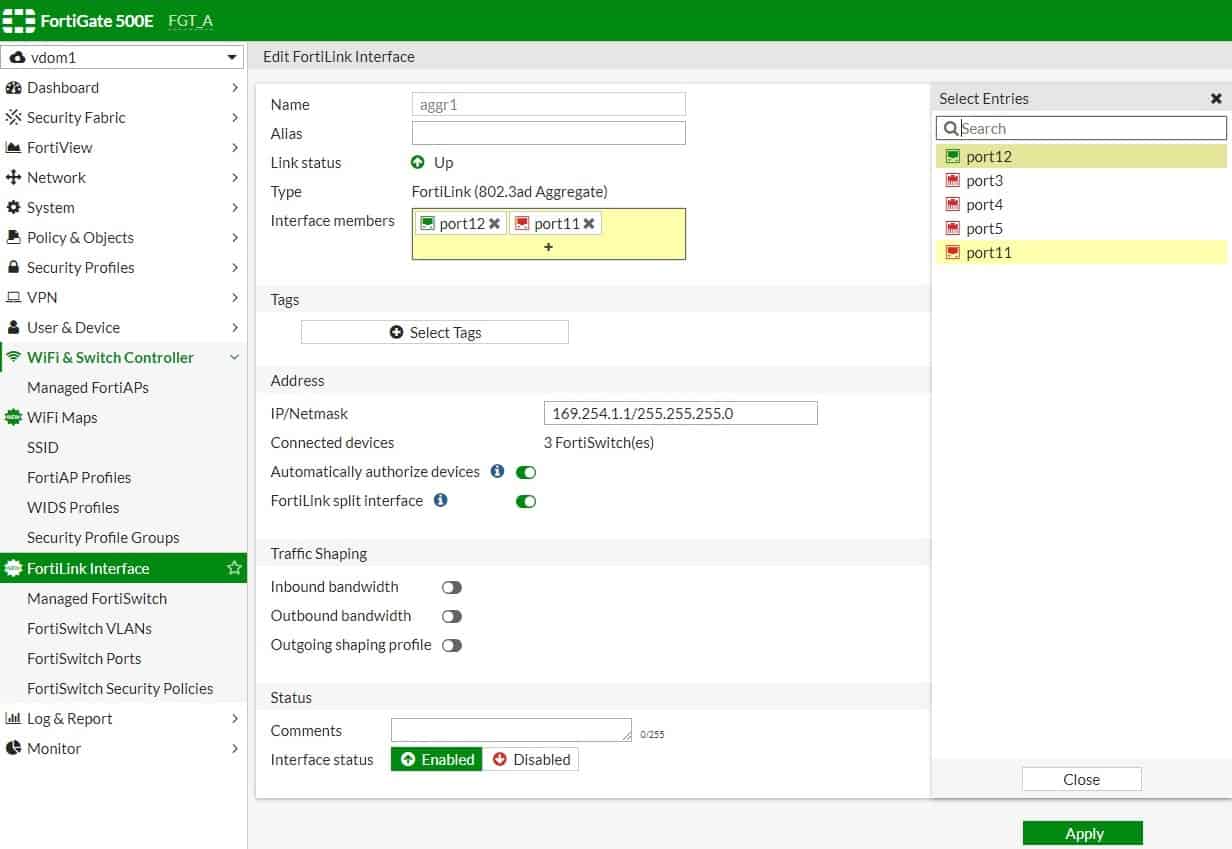
Figure 1.0 Screenshot showing FortioS configuration interfaceThe Fortinet FortiGate UTM is among the leading UTM products or applications in the market. It has been recognized by Gartner as a leader in its annual UTM Magic Quadrant report since 2008. It has also been named a 2020 Gartner Peer Insights Customers’ Choice. FortiGate UTM supports deployments across physical, virtual, and cloud environments. It’s available in different models ranging from entry-level hardware appliances targeted at small offices, to ultra-high-end appliances designed for data centers and multi-tenant cloud environments, as well as a software virtual appliance for deployment on your own hardware.
Key Features:
- Versatile Deployment: Supports physical, virtual, and cloud environments, accommodating diverse IT infrastructures.
- Comprehensive Security: Combines SD-WAN, NGFW, intrusion prevention, DLP, VPN, email/web/content filtering, and more into a unified solution.
- Advanced Threat Protection: Offers APT defense, anti-malware, IP reputation services, SSL inspection, and integrated WLAN controller for extensive network security.
Why do we recommend it?
Fortinet FortiGate UTM is part of a family of FortiGate products that can be loaded onto a hardware firewall. The firewall appliance is Fortinet’s signature product with a special architecture to speed up data processing. Fortinet produces add-on services for this firewall and the UTM is one of them. Fortinet now also produces a virtual appliance and cloud versions of FortiGate.
FortiGate UTM is powered by FortiOS software, which also enables the Fortinet Security Fabric—an adaptive architecture providing integrated detection and automated responses to cybersecurity threats. It utilizes machine learning and AI to provide behavioral-based cyber threat detection and prevention.
Fortinet licenses UTM security features which it calls FortiGuard Services, on a per-device basis. FortiGuard Services are available as a single subscription or software bundle with or without hardware. FortiCare device-based support is the foundation of the support services, providing firmware updates, technical support, and foundational FortiGuard subscriptions. Customers can also purchase advanced premium support services to complement the standard FortiCare support plan.
Who is it recommended for?
The FortiGate firewall has always been a high-end product aimed at large businesses. However, now it is available without the necessity of buying a physical appliance, its appeal has widened to mid-sized businesses as well. This UTM is an add-on to the firewall, so existing owners of FortiGate firewalls are the most likely buyers of this tool.
Pros:
- Leadership Recognition: Acknowledged by Gartner as a leader in UTM, reflecting its robustness and reliability in threat management.
- Integrated Security Fabric: Utilizes FortiOS for an adaptive security architecture, enhancing threat detection with machine learning and AI.
- Flexible Licensing: FortiGuard Services provide a scalable subscription model, allowing tailored security features on a per-device basis.
Cons:
- Complexity: Feature-rich platform requiring time to fully leverage its extensive capabilities and integrations.
Related post: The best Fortinet analyzers
4. Datadog Security Monitoring

Datadog is a SaaS platform of monitoring and system management services that are charged for by subscription. The service includes a Security Monitoring package, which is part of a wider Security Monitoring Platform.
Key Features:
- Cloud-Centric Security: Delivers a SaaS-based security monitoring solution that excels in protecting both on-premises and cloud-based assets.
- SIEM and CSPM: Features a SIEM for unified security management and Cloud Security Posture Management for cloud hardening.
- Integration and Orchestration: Seamlessly works with third-party tools and existing security systems, enhancing overall security posture.
Why do we recommend it?
Datadog Security Monitoring provides protection for on-premises systems and cloud services. This unifies the security services for hybrid environments. The package includes a SIEM for all environments, Cloud Security Posture Management for cloud systems hardening, and a Cloud Workload Protection Platform that implements continuous threat detection for cloud services.
The Security Monitoring system is appropriate for use by IT Operations departments for supervising the security of the enterprise’s entire IT infrastructure. The Security Monitoring Platform includes extra testing band protection services for DevOps environments.
The Datadog Security Management service is a SIEM system. This means that it collects log messages and system monitor outputs, such as SNMP reports, and gathers them together into a single pool of data for threat detection. This means that activity data from every part of your IT system – endpoints, networks, and applications, is included in the protection system.
While the Datadog Security Monitoring service doesn’t replace your existing firewall, it will integrate that service into its unified security management system. Activity data from the firewall feeds into the SIEM and automated response instructions can be sent back to it.
By coordinating existing services, Datadog Security Monitoring creates efficiency. The system gets even more cost-effective if you combine the security features with other services offered by Datadog, such as its Network Monitoring packages because all of the Datadog systems use the same on-site agent for data collection.
Datadog Security Monitoring efficiently provides monitoring for any resource no matter where it is located, giving you the ability to centralize the security protection for all of your IT assets, including on-premises systems and cloud resources. The ability of this service to gather activity information from all of your IT assets creates an easy way to implement security management without having to re-install software or alter system settings. Combining the Security Monitoring service with other Datadog packages increases value for money and efficiency.
Who is it recommended for?
You would need to be using cloud services to really benefit from this package. If you use both on-premises services and cloud platforms, then even better. Businesses that work with only a few SaaS systems would probably be better off with a system that focuses more attention on protecting on-premises assets.
Pros:
- Scalable Solution: Offers cloud-based scalability, ideal for monitoring applications across multiple sites and WANs.
- Customization and Integration: Supports over 500 integrations and provides flexible templates for a wide range of use cases.
- Efficient Monitoring: Centralizes security for IT assets regardless of their location, leveraging a single agent for data collection.
Cons:
- Trial Limitation: The trial period might be considered short for fully exploring the extensive capabilities of the platform.
Datadog offers a menu of services that are all run from its cloud platform and you can try all of them on a 14-day free trial.
5. Check Point Quantum Next-Generation Firewall
Check Point provides a range of hardware firewalls under the Quantum brand. These cater to businesses of different sizes. Each firewall appliance provides additional security services, such as SD-WAN management, data loss prevention, and email filtering.
Key Features:
- Diverse Range: Offers a tailored firewall solution for different business sizes, from small offices to data centers and industrial environments.
- Cutting-edge Protection: Incorporates SandBlast Zero-Day protection, connection security for cloud services, and R81 Unified Security Management.
- Scalable Solutions: Quantum Lightspeed for data centers, Security Gateway for various enterprise sizes, Spark for small businesses, and Rugged for industrial settings.
Why do we recommend it?
The Check Point Quantum Next Generation Firewall is a similar product to the Fortinet FortiGate range. You get a piece of hardware that hosts all of your security systems. That removes the need to find server space for your threat management software and it also ensures that no threats can get onto the network and cause havoc before they are detected.
The fit for each product in the range is:
Quantum Lightspeed Firewall for data centers
Quantum Security Gateway in capacities for high-end, large, and mid-sized enterprises, and branch offices
Quantum Spark for small businesses
Quantum Rugged for industrial environments
Check Point also offers a Cloud Native Security package to add on to your Quantum package and a larger appliance called the Maestro Orchestrator, which is a hardware appliance that coordinates between multiple Lightspeed devices. This is a complicated system but you narrow down the complexity by zooming in on the device that is suitable for your business size.
As it sits as a gateway between the internet and your network, the Quantum device can also act as an endpoint for a secure virtual network. As such, it will manage Site-to-Site VPN connections and offload encryption, to enable boundary packet inspection that gets right into the payload of each packet rather than just their headers.
The Cloud Native Security add-on provides a cloud-based system to check all of your cloud assets and accounts. This can also coordinate with your on-premises Quantum device to implement connection security and application fencing.
The SandBlast module is a sandboxing service that tests unknown executables as they download. The system previews each program by running it in a protected environment and checking its intent before allowing it through to an endpoint on your network.
Who is it recommended for?
Check Point covers all enterprise sizes with its hardware range. However, this means that a Quantum appliance will only be of interest to businesses that want an on-premises network device for a firewall implementation. You would need to have considerable on-site assets to justify this deployment option. Businesses that operate virtual offices or rely heavily on cloud SaaS packages wouldn’t be well served by this system.
Pros:
- Pre-emptive Threat Detection: Positions security at the network gateway to intercept threats before they penetrate the network.
- Comprehensive Coordination: Facilitates secure connections across sites and cloud services, integrating security management across platforms.
- Performance Optimization: Offloads security processing to dedicated hardware, improving server efficiency for core business functions.
Cons:
- Hardware Requirement: Necessitates the installation of physical devices, which may not align with the operational models of virtual or heavily cloud-reliant businesses.
6. Cisco UTM
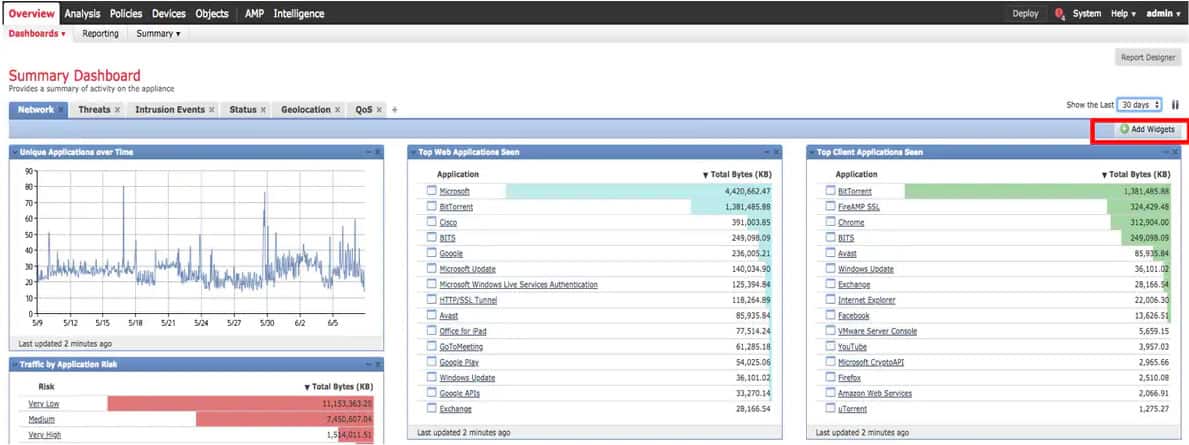
Figure 4.0 Screenshot showing Cisco FMC dashboardCisco is a household name when it comes to network infrastructure products and services. It is therefore not surprising to know that it is also a force to reckon with in network security, especially in the UTM market. It is recognized as the lead challenger in the most recent Gartner UTM Magic Quadrant published in 2018. It was also named a 2018 Gartner Peer Insights Customers’ Choice for UTM.
Key Features:
- Wide Range of Appliances: Offers a variety of UTM hardware appliances tailored to different business sizes, including Firepower and Meraki MX series.
- Unified Management: Central platform via Firepower Management Center for comprehensive control over UTM features.
- Extensive Security Features: Includes IPS, VPN, URL filtering, DDoS protection, application control, and more.
Why do we recommend it?
The Cisco Secure Firewall is a hardware appliance and si it competes with the Fortinet and Check Point options on this list. Like those competitors, Cisco produces a range of device sizes that caters to different business sizes. The appliance can host multiple functions, so you can add on extra software.
Cisco offers several UTM hardware appliance options with Firepower series, ASA 5500-X series with FirePOWER services, and Meraki MX series, as well as software virtual appliance for public and private cloud infrastructure. All of these can be managed from a central platform called Firepower Management Center (FMC). Cisco lets customers try out Meraki MX products on their own networks at no charge.
Cisco is a particularly good fit for companies seeking a broad range of security products and services that integrate with the firewall. But incidentally, the sheer number of different products and a wide array of features makes buying decisions cumbersome. Key features include but are not limited to IPS, VPN, URL filtering, DDoS protection, application control, identity services, endpoint protection, web gateway, email security, network access control, and high availability.
All purchases can be made via accredited Cisco partners. Cisco UTM licensing is subscription-based and it comes with standard and premium support. Licensing covers specific security features and services used by the appliances. Customers are required to purchase a license for cloud services on a per-device basis. Existing ASA customers have the opportunity to upgrade the software to the Firepower 9300 without replacing the ASA device. Cisco even provides small businesses with flexible payment options via the Cisco Easy Pay plus. Cisco is well known for its strong support system for customers. As with other products, Cisco provides full online documentation for installing and configuring all of its UTM software and appliances.
Who is it recommended for?
The Cisco hardware firewall range has advantages for on-site systems. However, if you specialize in providing Web applications or use SaaS systems more than on-premises services, you should look at the Cisco Secure Firewall Cloud Native product. Cisco also offers a cloud-based Web application firewall that provides bot and DDoS protection as well.
Pros:
- Integration Potential: Seamlessly works with other Cisco products for an integrated security ecosystem.
- Flexibility: Provides options for businesses of all sizes, from small offices to large data centers.
- Support and Documentation: Well-known for strong customer support and extensive online resources.
Cons:
- Complex Selection Process: The broad product range can make it challenging to identify the most suitable solution.
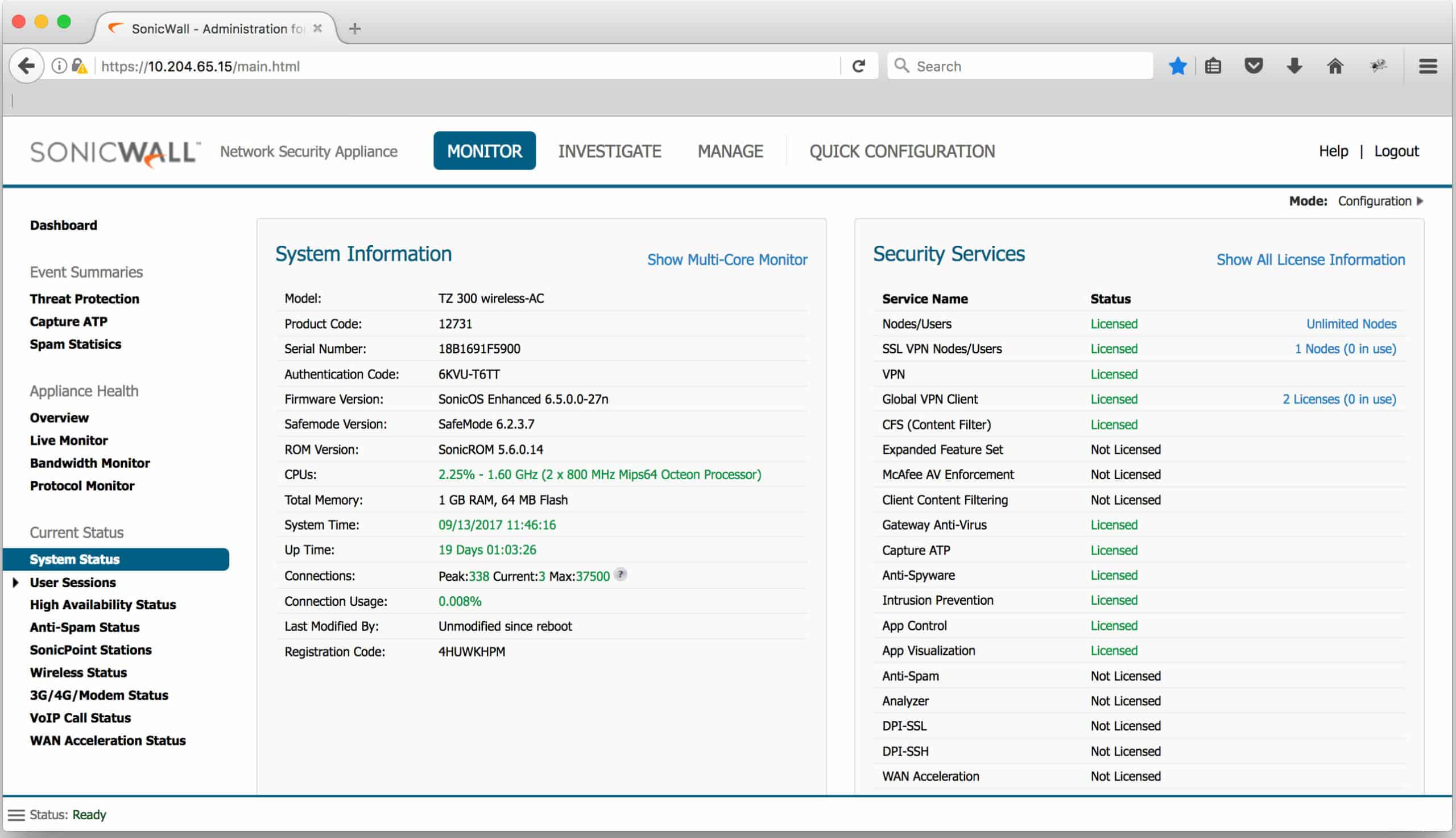
7. SonicWall UTM
Figure 5.0 Screenshot showing SonicOS configuration interfaceSonicWall has been in the UTM business from the earliest days. They have produced good value UTM product sets and models to meet the needs of businesses of all sizes. It is recognized as a challenger in the Gartner 2018 UTM Magic Quadrant.
Key Features:
- Diverse Product Line: Caters to all business sizes with the TZ SOHO series, NSA series, NSSP series, and NSV series for virtual environments.
- Cloud Management: Integrated with the Capture Cloud Platform for centralized management and threat intelligence.
- Robust Security Features: Offers NGFW, intrusion prevention, VPN, web content filtering, and anti-malware capabilities.
Why do we recommend it?
The SonicWall product range is centered on a line of hardware firewalls. These devices are constructed in versions that cater to different sizes of enterprises. There is also a cloud-based range of systems for Cloud service protection and a Web application firewall. By combining several products and running them on the firewall appliance, you create a UTM.
Just like other vendors, SonicWall UTM supports deployments across physical, virtual, and cloud environments. Its appliances are powered by a software called SonicOS that enables all the UTM security and networking features. The SonicWall UTM are grouped under the following categories:
SonicWall TZ SOHO Series: These are entry-level UTM products (in wired and wireless models) that combine threat prevention and SD-WAN technology, targeted at small to mid-size organizations and remote offices.
Network Security Appliance (NSA) series: These are hardware appliances that range from NSA 2650 series to NSA 9650 series, and are targeted at mid-sized networks to distributed enterprises and data centers.
Network Security Services Platform (NSSP) series: These are also hardware appliances made up of NSSP 12400 and NSSP 12800 series that combine cloud intelligence with appliance-based protection, designed for large distributed enterprises, data centers, and service providers.
Network Security Virtual (NSV) series: These are full-featured SonicWall UTM software applications ranging from NSV 10 to NSV 1600, designed to deal with vulnerabilities within virtual environments.
One notable feature and capability of SonicWall UTM is the availability of an integrated cloud-based centralized management service called Capture Cloud Platform, and online live demos, that helps you experience real product demonstrations without going through the trouble of putting a test box in your environment.
SonicWall UTM licensing is subscription-based and it comes with standard and premium support. Before deciding to purchase or renew the SonicWall UTM subscription, you first need to determine the appliance type, model, and subscription that is right for your business.
Who is it recommended for?
If you have decided that you want to implement your threat protection on a network device, then this is one of your options along with Cisco, Check Point, and Fortinet. This route will enable you to construct a range of virtual network configurations by combining site protection with a cloud-based entry point, so you can have an SD-WAN or a SASE with the SonicWasll service.
Pros:
- Specialized Products: Tailors its UTM offerings to specific network sizes and requirements, enhancing suitability.
- Demonstration Accessibility: Provides online live demos, allowing prospective users to explore features without hardware installation.
- Comprehensive Support: Known for excellent support and training resources, facilitating effective use of their products.
Cons:
- Configuration Migration: Transitioning settings to advanced models requires meticulous planning, posing a potential challenge.
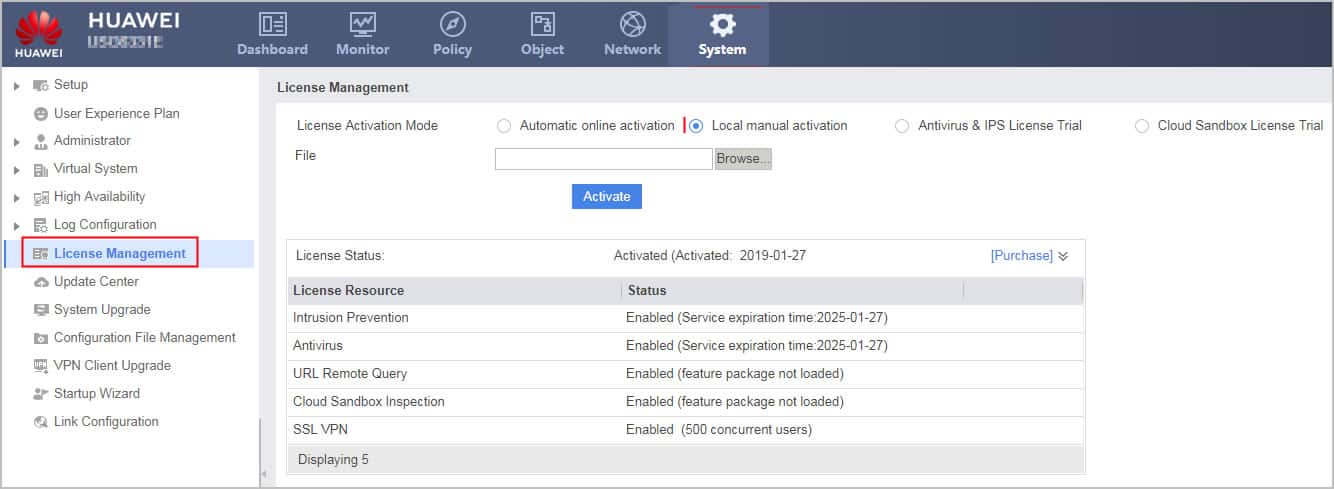
8. Huawei Unified Security Gateway (USG)
Figure 6.0 Screenshot showing Huawei USG admin dashboardHuawei UTM solution which it brands as Unified Security Gateway (USG) provides integrated security for midsize, large enterprises, chain organizations, cloud service providers, and large data centers. It is recognized as a challenger in Gartner’s most recent UTM Magic Quadrant alongside Cisco and SonicWall in 2018, and it has also earned the coveted NSS Labs’ “Recommended” rating in 2019. Huawei is a well-known brand in Europe, the Middle East, Africa, and Asia (EMEAA) markets.
Key Features:
- Versatile Deployment: Offers desktop, rackmount, data center chassis, and software virtual appliance models to suit a wide range of organizational needs.
- AI-Based Threat Defense: Utilizes artificial intelligence for sophisticated threat identification and mitigation.
- Comprehensive Security: Features NGFW, application control, IPS, bandwidth management, and more for robust network protection.
Why do we recommend it?
Huawei is another network device provider with a hardware solution for its firewalls. However, the company also offers a number of software-based threat detection systems, which include the HiSec Insight Advanced Threat Analytics System and the SecoManager Security Manager, which is a SOAR solution that optimizes the performance of your existing security systems.
Huawei USG UTM solution comes in desktop, rackmount, data center (DC) chassis, and software virtual appliance model, giving you the flexibility to deploy as hardware or software virtual appliance in a physical, or virtual environment.
Desktop model: The Huawei HiSecEngine USG6500E series such as USG6510E and USG6530E is the desktop hardware appliance model UTM targeted at SMBs, branch offices, and franchise businesses.
Rackmount model: HiSecEngine USG6500E series (fixed-configuration), USG6600E series, and USG6700E series (fixed-configuration) are hardware rackmount appliance designed for small and medium-sized enterprises, chain organizations, institutions/campuses, and data centers.
DC Chassis model: The USG9500 series such as USG9520, USG9560, and USG9580 is an all-in-one data center model that delivers up to 1.92 Tbit/s in firewall throughput to cloud service providers and large-scale enterprise campus networks.
Software virtual appliance model: The Huawei USG6000V series such as USG6000V1 to USG6000V8 are a software virtual appliance model designed to run in virtual environments, providing virtualized gateway services such as vFW, vIPsec, vLB, vIPS, vAV, and vURL Remote Query.
One of the remarkable features of the Huawei USG UTM solution is the innovative AI capabilities it brings to threat defense. Other features include NGFW, application control, IPS, bandwidth management, URL filtering/web protection, antivirus, VPN, DLP, DDoS mitigation, policy management, among others. All Huawei USG products can be purchased directly from Huawei or via accredited partners.
Who is it recommended for?
These options are aimed at mid-sized and large businesses. Huwawei’s security gateways are particularly suitable for large data centers. The systems are geared towards protecting on-site assets rather than cloud services and they are designed for use by software consumers rather than providers.
Pros:
- Flexible Models: Caters to SMBs, branch offices, and large enterprises with tailored hardware and virtual solutions.
- Innovative AI Capabilities: Enhances security measures with AI-driven threat detection and response mechanisms.
- Ease of Use: User-friendly interface and object-based policies simplify security management.
Cons:
- Geographical Limitations: Potential regulatory restrictions in certain regions, notably the US, may limit its availability and suitability.
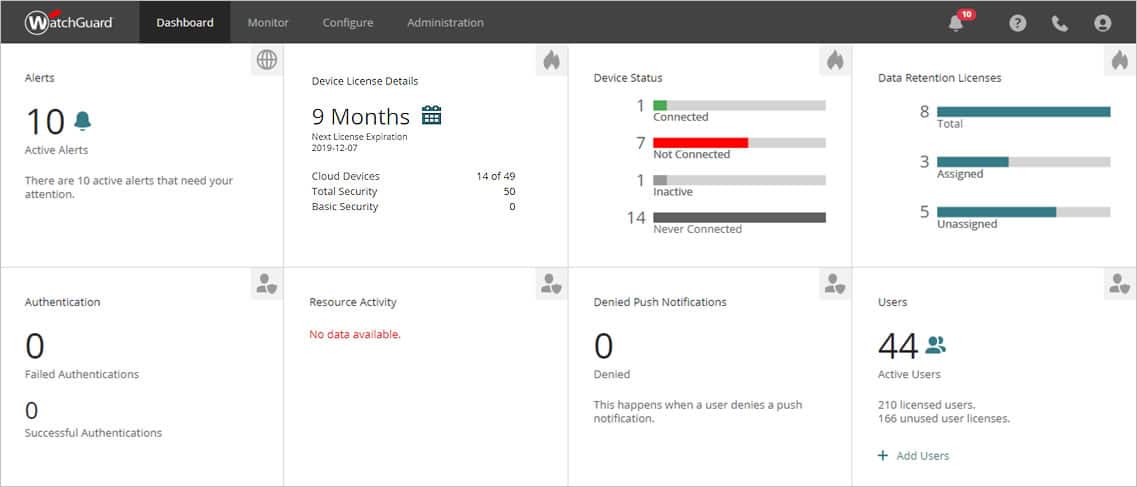
9. WatchGuard Firebox UTM
Figure 7.0 Screenshot showing Watchguard cloud dashboardUTM solution from WatchGuard delivers an all-in-one network security platform and protection for mostly small, midsize, and distributed enterprises. It does not directly address large conglomerates or big data centers. It is among the industry’s finest when it comes to performance. WatchGuard is recognized as the only visionary in Gartner’s most recent Magic Quadrant for UTM published in 2018.
Key Features:
- SMB Focus: Tailored for small to midsize businesses with a range of tabletop, rackmount, and virtual/cloud appliance options.
- All-in-One Security: Delivers comprehensive protection including IPS, URL filtering, Gateway AV, application control, and advanced threat features.
- Flexible Deployment: Available as physical appliances for on-site deployment or as virtual/cloud solutions for flexible infrastructure integration.
Why do we recommend it?
The WatchGuard Firebox is like a Fortinet FortiGate appliance designed for small businesses. You buy the network device and then choose which security software you want to load onto it. Thus, you assemble your own UTM package. Options include an anti-virus service, application fencing, connection security management, and an intrusion prevention system.
WatchGuard Firebox UTM comes in tabletop, rackmount, and software virtual appliances to give you the flexibility to deploy the solution as a hardware appliance in a physical environment, or as software in a virtual or cloud infrastructure.
Tabletop Firebox appliances: Just as the name implies, these are small form-factor, high-performance, tabletop hardware appliances ranging from T15 to T80 designed for home office, SMB, and branch office locations.
Rackmount Firebox appliances: The 1U rack-mount appliance ranging from M270 to M670 is designed for small and growing midsize businesses, and M4600 and M5600 is targeted at distributed enterprise organization.
Virtual/cloud Firebox solution: FireboxV and Firebox Cloud is the software version of the Firebox UTM with all of the security and performance required for any size organization moving their IT infrastructure to a virtual environment—private or public cloud.
Some of the key features of WatchGuard’s UTM solution include standard IPS, URL filtering, Gateway AV, application control, and antispam, and features for combating advanced threats such as file sandboxing, data loss prevention, ransomware protection, and much more
WatchGuard sells subscriptions for the security software modules for UTM appliances, either individually or as a suite. Your Support license gives you access to updates and enhancements, and all new releases at no cost. All WatchGuard hardware includes a one-year hardware warranty.
All WatchGuard UTM appliances come with a minimum of 90 days subscription and support, which includes software updates and hardware replacement, among other services. WatchGuard also offers one-year, and three-year Basic and Total Security subscriptions to unlock security services. Customers can purchase a subscription to Standard, Plus (24/7), Gold, or Premium that offers a higher priority to your support case. If you are considering WatchGuard UTM solution for your business, the steps below will guide you in your buying decision:
Choose your product or appliance type
Select your preferred security package—Total Security Suit or Basic Security Suite
Contact a WatchGuard certified reseller
Who is it recommended for?
You would need to be interested in protecting a site or sites to use this tool because it is geared towards scanning traffic in and out of a network, so it is no good at protecting cloud assets. WatchGuard produces FireboxV as a virtual appliance for site protection and Firebox Cloud, which is an AWS or Azure-resident software version.
Pros:
- Versatile Solutions: Offers hardware and software options to fit various business sizes and deployment preferences.
- Subscription Services: Provides access to a suite of security services with options for Basic or Total Security subscriptions.
- Customer Support: Includes a hardware warranty and subscription support with options for enhanced service levels.
Cons:
- Support Tiering: Expedited support requires purchase of a higher-tier subscription, potentially adding costs for businesses needing priority service.
Unified threat management FAQs
What is unified threat management system?
A unified threat management (UTM) system is a security platform that replaces multiple individual security tools, such as anti-virus, firewall, email and Web filtering, data loss prevention, and intrusion detection. The package can be delivered from the cloud or run on an appliance. Some UTMs are available for installation over a hypervisor to operate as a virtual appliance.
Is a UTM a firewall?
Unified threat management (UTM) systems are sometimes called next-generation firewalls (NGFW). The big difference between the two is that firewalls examine and control incoming traffic but UTMs also examine outgoing traffic so that they can block data theft.






Hi,
I believe you made a small mistake while mentioning a free domestic use of FortiGate. You actually linked the free home version of Sophos.
Is there an actual free version of FortiGate? I saw there is a free trial for business us but you may have reffered to something else.
Otherwise great article.
Thank you
Thank you Maxime for that observation. You’re actually right, the link in question was meant for Sophos not Fortinet. I have effected the correction. Thanks for the feedback.