Cybersecurity vulnerabilities, essentially flaws in software code, pose significant risks by granting attackers access to networks and systems. These vulnerabilities expose businesses and individuals to threats like malware and account takeovers.
The National Vulnerability Database (NVD) and the Common Vulnerabilities and Exposures (CVE) list record over 176,000 such vulnerabilities, including notable ones like the CVE-2017-0144 Windows flaw and the Mirai botnet. Upon discovery, developers rush to release patches, but slow update implementation often exposes systems, allowing attackers to exploit these vulnerabilities, sometimes years after their discovery.
This post consolidates key cybersecurity vulnerability statistics and facts to highlight the magnitude of this ongoing security challenge.
1. Over 26,000 vulnerabilities were published in 2023
In contrast to the 8,051 vulnerabilities published in Q1 of 2022, a significant increase was observed in 2023. 26,447 vulnerabilities were disclosed, surpassing the previous year’s count by over 1,500 CVEs. This marks a continuous upward trend in the discovery of vulnerabilities year after year.
2. High-risk vulnerabilities exploited by threat actors & ransomware groups
In 2023, more than 50% of the 206 high-risk vulnerabilities tracked by Qualys were leveraged by threat actors, ransomware, or malware to compromise systems. This indicates a significant portion of vulnerabilities remain critically exploitable, underscoring the necessity for robust and comprehensive cybersecurity measures.
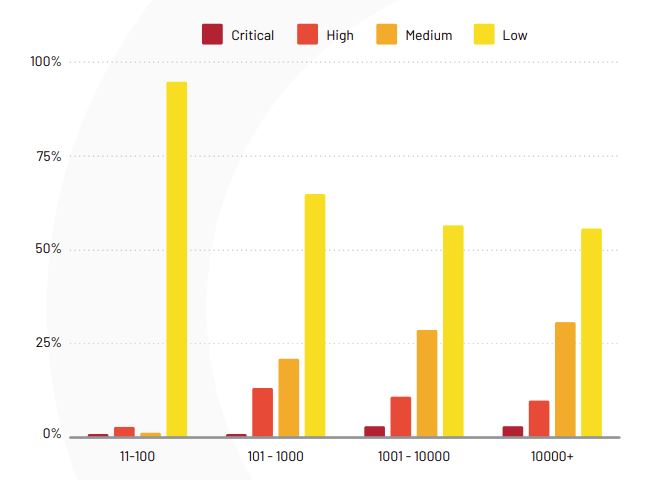
3. Organizations with more than 100 staff see more high or critical-risk vulnerabilities
Edgescan’s 2021 report broke down the severity of vulnerabilities according to company size. Smaller companies with 100 employees or fewer saw the lowest portion of medium, high, or critical-risk vulnerabilities (five percent total). Companies with 10,000+ employees see the largest portion of medium and critical-risk vulnerabilities while medium-sized organizations with 101–1,000 employees saw the largest portion of high-risk vulnerabilities.
4. The mean time to remediation (MTTR) is around 58 days
According to Edgescan, the average time taken to remediate internet-facing vulnerabilities was 57.5 days. That is a slight improvement over the year prior when the MTTR was 60.3 days.
This varies from one industry to another, though. Public administrations, for instance, had a MTTR of 92 days, whereas healthcare organizations had an MTTR of just 44 days. The data shows that the smaller an affected organization is, the more quickly it tends to recover.
5. The most severe vulnerability of 2021 was CVE-2021-44228
CVE-2021-44228 is a vulnerability impacting Log4j, an open-source logging library used in thousands of projects, applications, and websites. This vulnerability allowed attackers to run arbitrary code on any affected system, and while it was swiftly patched out, it’s extremely likely that a high number of vulnerable applications remain online.
6. The oldest vulnerability discovered in 2020 was 21 years old
Interestingly, Edgescan found a pretty old vulnerability that has been around since 1999: CVE-1999-0517. This affects Simple Network Management Protocol version 2 (SNMPv2), which is used for managing devices and computers on an IP network. The vulnerability can allow unauthorized SNMP access via a guessed community string. It has a base Common Vulnerability Scoring System (CVSS) score of 7.5 making it a high-severity weakness.
7. The first critical vulnerabilities in a major cloud infrastructure were found in January 2020
In early 2020, Check Point researchers discovered and reported critical vulnerabilities in the Microsoft Azure infrastructure. According to the Check Point article detailing the vulnerability, researchers “wanted to disprove the assumption that cloud infrastructures are secure.” The vulnerabilities received the highest CVSS score of 10.0. The qualitative severity ranking of a score of 9.0-10.0 is “critical.”
These vulnerabilities enable malicious actors to compromise apps and data of users who utilize the same hardware.
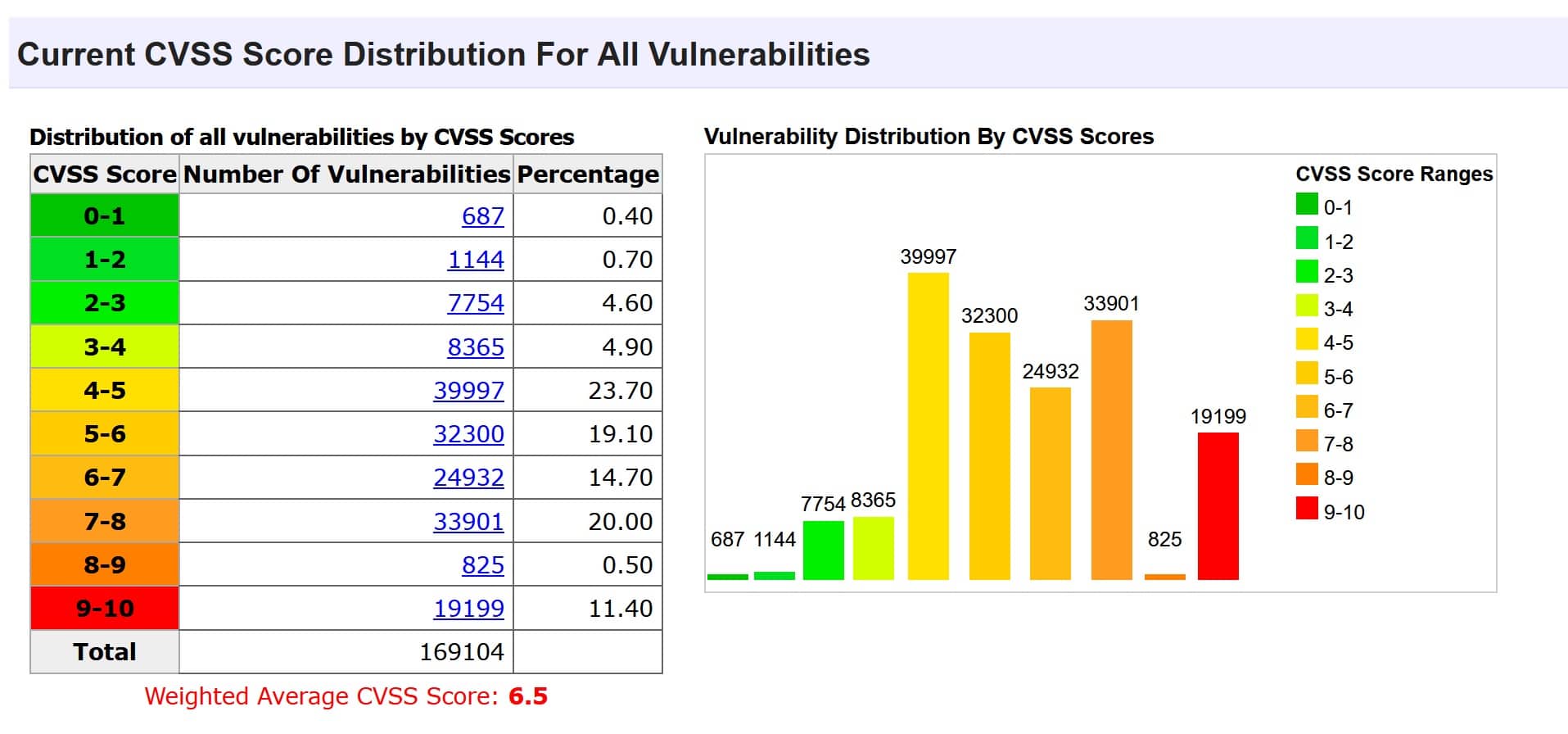
8. More than 11% of vulnerabilities have a critical score
According to CVE Details, out of roughly 176,000 vulnerabilities, more than 19,000 have a CVSS score of 9.0–10.0. That said, the vast majority (77.5 percent) have a score between 4.0 and 8.0.
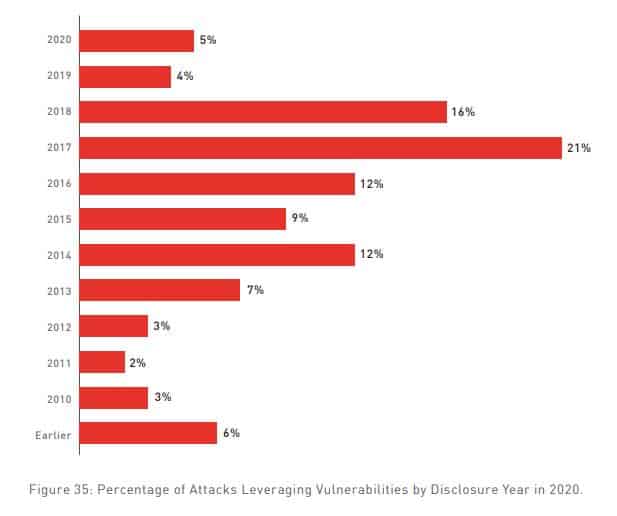
9. 75% of attacks in 2020 used vulnerabilities that were at least two years old
According to the Check Point Cyber Security Report 2021, three out of four attacks took advantage of flaws that were reported in 2017 or earlier. And 18 percent of attacks utilized vulnerabilities that were disclosed in 2013 or before, making them at least seven years old.
10. Citrix remote access vulnerability attacks increased 2,066% in 2020
According to Check Point, the number of attacks exploiting vulnerabilities in remote access products increased substantially in 2020. Citrix attack numbers increased more than 20-fold, while Cisco, VPN, and RDP attacks increased by 41%, 610%, and 85%, respectively.
11. 31% of companies detected attempts to exploit software vulnerabilities
A 2020 report from Positive Technologies tells us that almost one-third of detected threats involve software exploit attempts. According to the report:
“More than half of attempts involved vulnerability CVE2017-0144 in the implementation of the SMBv1 protocol. This is the same vulnerability leveraged by the infamous WannaCry ransomware, and for which a patch was released back in 2017. But attackers have kept it in their arsenals as they search for computers that have not been updated in the last 3.5 years.”
12. High-risk vulnerabilities are present on the network perimeters of 84% of companies
Another study from Positive Technologies uncovered the alarming statistic that 84 percent of companies have high-risk vulnerabilities on their external networks. It also found that more than half of these could be removed simply by installing updates.
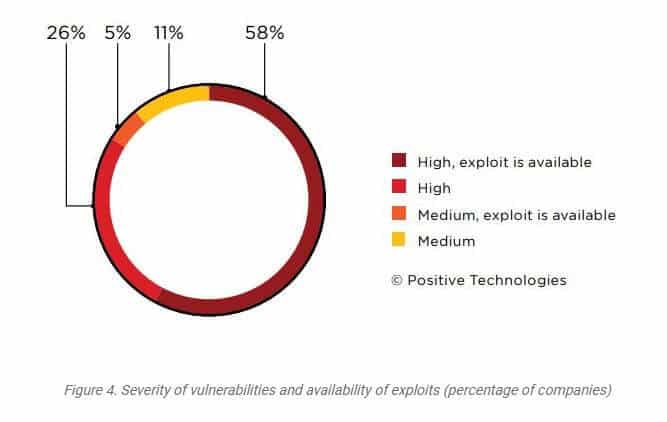
13. More than one in four companies are still vulnerable to WannaCry
Positive Technologies also found that 26 percent of companies remain vulnerable to the WannaCry ransomware as they have not yet patched the vulnerability it exploits. That’s particularly concering given that WannaCry attacks spiked in Q1 of 2021.
14. XSS remains a huge threat
Hacker One research found that cross-site scripting (XSS) weaknesses were the most common type of vulnerability in 2020, accounting for 23 percent of all reports. Rounding out the top three weakness types was information disclosure (18 percent) and improper access control (10 percent).
15. The most profitable industry for bounty hunters is computer software
When it comes to which industries earn the most for bounty hunters, computer software weaknesses are the highest earners by quite a significant amount. The average bounty payout for a critical vulnerability is around $5,754. The electronic and semiconductor industry pays $4,633 per critical vulnerability and the cryptocurrency and blockchain field pays about $4,481.

16. “80% of public exploits are published before the CVEs are published”
A report published by Palo Alto Networks in August 2020 found that 80 percent of studied exploits were made public before their related CVEs had even been published. Perhaps more concerning is the length of time that passes between publish dates. On average, exploits are published 23 days before their respective CVEs. As noted in the report:
“As a result, there is a good chance that an exploit is already available when the CVE is officially published – illustrating one more way that attackers are too often a step ahead of security professionals.”
17. More than 28,500 WordPress vulnerabilities have been detected over the past 8 years
The number of new vulnerabilities has been increasing steadily since WPScan first started tracking in 2014. More than 3,000 new vulnerabilities were discovered in 2021, and in the first quarter of 2022, we’ve already seen an additional 700.
18. In Q4 2021, zero-day exploits were involved in 66% of malware
WatchGuard’s Internet Security Report – Q4 2021 tells us that from October to December of 2021, zero-day malware accounted for two-thirds of all threats. This was a marginal decrease over the previous quarter.
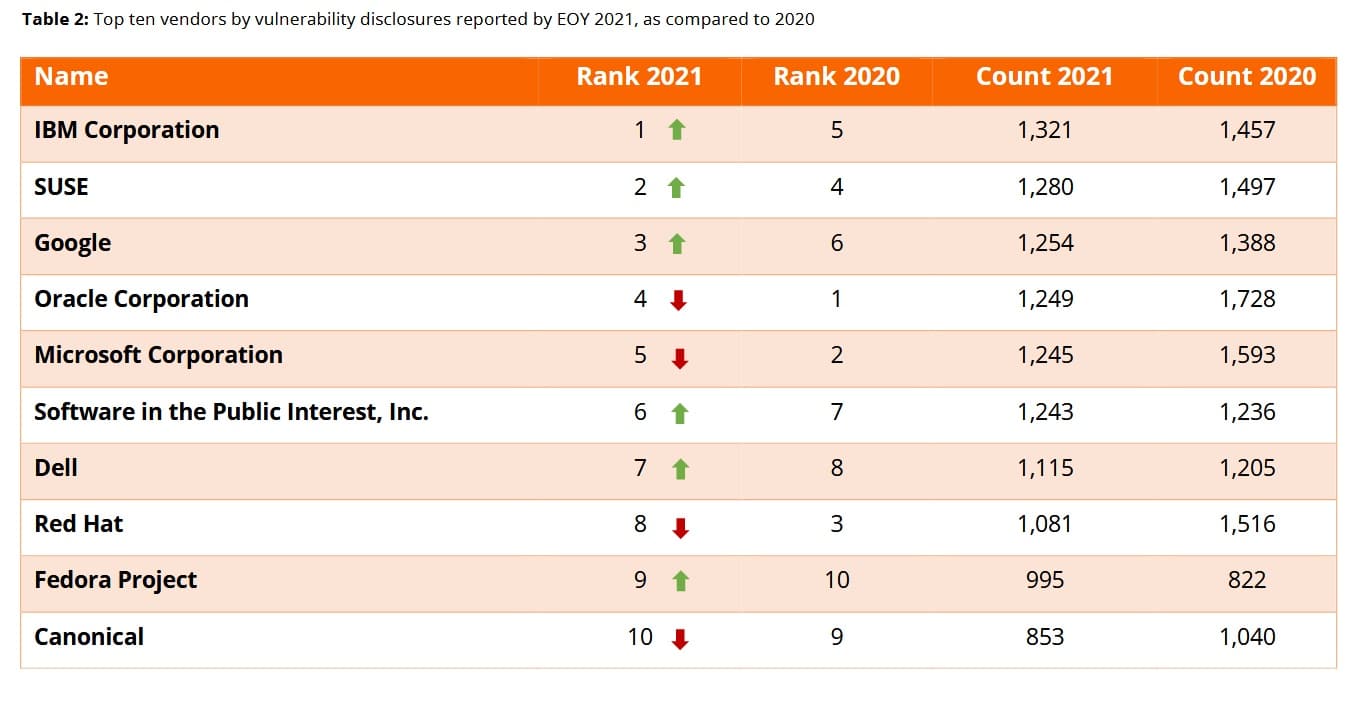
19. Lower numbers of vendor-specific vulnerabilities in 2021
According to RiskBased Security’s 2021 Year End Report, IBM was the vendor with the most confirmed vulnerabilities this year. However, it’s worth noting that most vendors actually have fewer vulnerabilities than last year. The exceptions are Software in the Public Interest, Inc and Fedora project, which saw a small increase.
20. Over 75 percent of applications have at least one flaw
Veracode’s State of Software Security Report Volume 11 released in October 2020 found that more than three-quarters (75.2 percent) of applications have security flaws. That said, only 24 percent of those are considered to have high-severity flaws.
21. Information leakage flaws are the most common
Veracode also tells us that the most common types of flaws are information leakage, CRLF injection (where an attacker injects unexpected code), cryptographic issues, code quality, and credentials management.
22. One in four flaws are still open after 18 months
A fairly alarming finding from Veracode’s 2021 report is that after a year and a half, around 27 percent of flaws are still open.
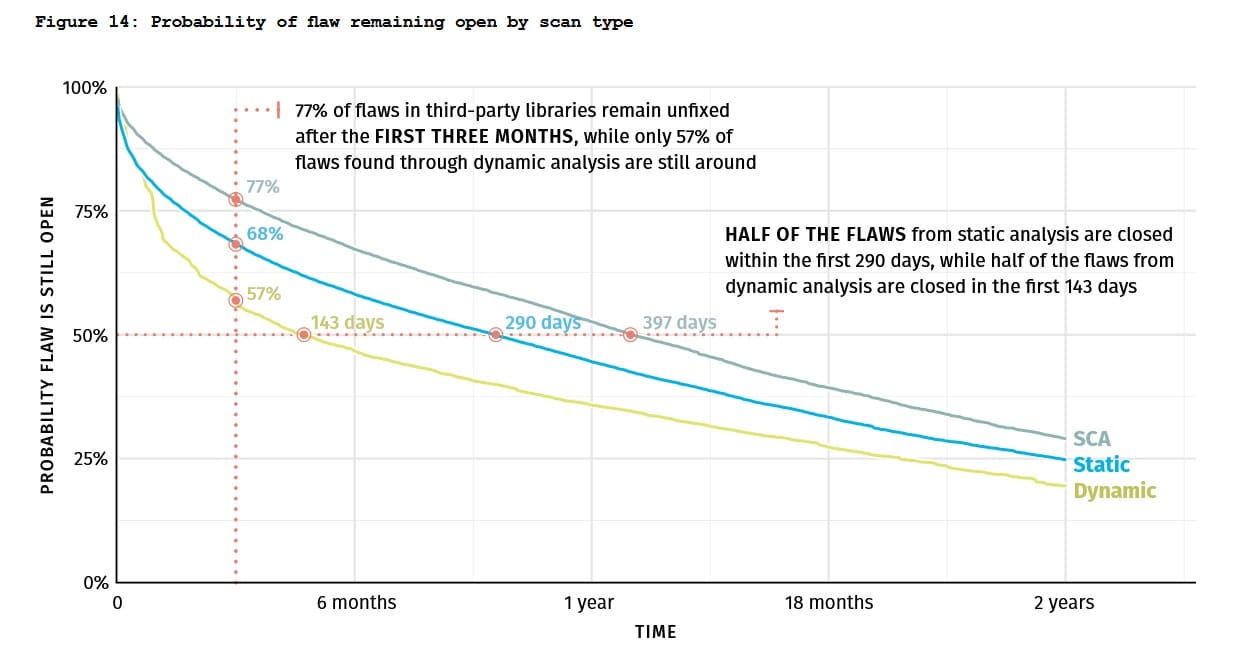
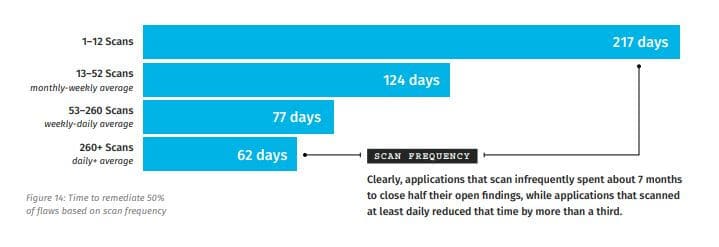
23. Frequent scanning correlates to much faster remediation time
Veracode did find that applications that scanned for flaws regularly saw much faster average remediation times. Those with 260+ scans per day remediated 50 percent of flaws within 62 days. That time was extended to 217 days for applications running just 1–12 scans per day.
24. Google has paid $35 million in bug bounties since 2010
Google’s Vulnerability Reward Program (commonly referred to as a bug bounty program) rewards researchers for discovering and reporting bugs in the company’s software. It has paid out $35 million since 2010. 696 researchers from 62 countries were paid bounties in 2021, with the largest single award amounting to $157,000.
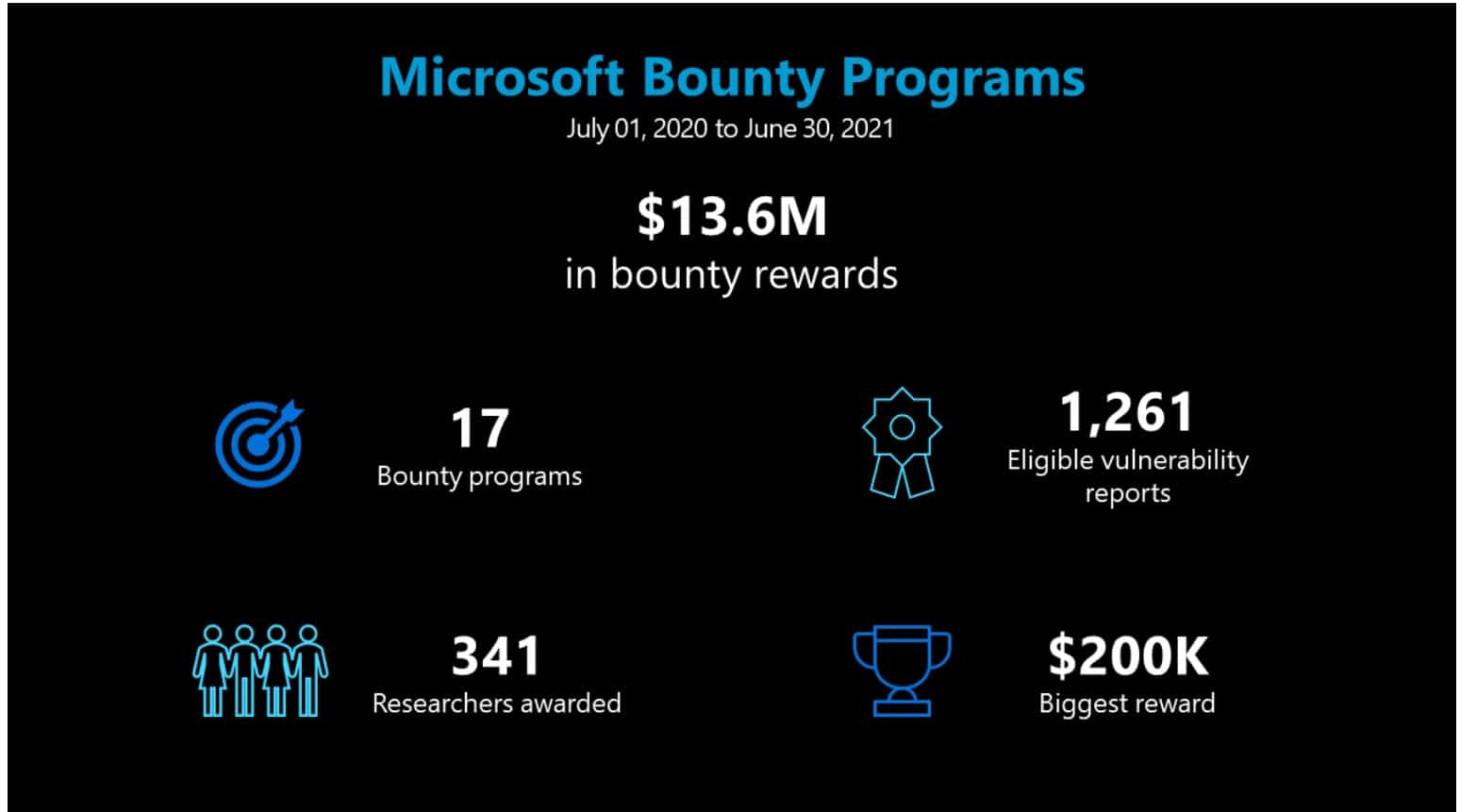
25. Microsoft paid almost $14 million in bug bounties in one year.
In a similar vein, Microsoft rewards researchers that spot and report bugs in its software. In an July 2021 review, the company reported it had paid $13.6 million in bug bounties in the past 12 months. This is more than double the amount Google paid out in 2019. In total, 340 researchers were awarded with the largest award amounting to $200,000.
26. Facebook (now Meta) has awarded almost 7,000 bounties since 2011
A December 2021 blog post by Facebook (now known as Meta) tells us that since its bug bounty program began in 2011, the company has received over 150,000 reports and awarded 7,800 bounties. At the time of the report, 2021 bounties totaled $2.3 million. Around 25,000 reports had been received, and more than 800 bounties were awarded. Its highest bounty to date is $80,000.
27. Unpatched vulnerabilities were involved in 60% of data breaches
According to a 2019 Ponemon Institute Vulnerability Survey:
“60% of breach victims said they were breached due to an unpatched known vulnerability where the patch was not applied.” However, an even higher portion (62 percent) claimed they weren’t aware of their organizations’ vulnerabilities before a breach.
28. The global IT security market is set to reach almost $400bn by 2028
According to a report by Fortune Business insights, the value of the information security market is forecast to hit $366.1bn by 2028. The exponential growth is driven by the integration of machine learning, the Internet of Things (IoT), and a surge in the number of eCommerce platforms.
FAQs about cyber security vulnerabilities
How do you identify cyber security vulnerabilities?
Whether you’re a home user or using a system for business, there are several ways to identify a cyber security vulnerability to help prevent threats from cybercriminals. These are some best practices to follow:
- Check that your device software and operating systems are up-to-date.
- Use an internet security suite to monitor your network for any vulnerabilities.
- Keep up with the latest cyber threat information to avoid risks of ransomware and phishing attacks.
What are the different types of cyber security vulnerabilities?
Cyber security vulnerabilities generally fall into four categories, these include:
- Operating system vulnerabilities arise when the OS is outdated, often allowing an attacker to find an exploit yet to be patched to gain entry to a system.
- Network vulnerabilities, i.e., issues with software or hardware on a network that could allow an outside entity to gain malicious entry.
- User error is one of the most common ways that sensitive data falls into the wrong hands, a.k.a, human vulnerabilities.
- Process vulnerabilities are when processes aren’t followed correctly or are not in place to begin with. Reused passwords or weak passwords can make a system more vulnerable for an attacker to penetrate.
How can I determine how secure a website is?
There are a few ways to tell if a website is secure. One way is to look for https:// in the URL of the website. This indicates that the website is using a secure connection. Another way is to look for a padlock icon in the address bar of your web browser. This indicates that the website is using a secure connection. Finally, you can check the security certificate of the website to verify that it is valid.
What should I do if I think my personal information has been compromised?
If you think your personal information has been compromised, you should take action immediately. First, you should change your passwords for any online accounts that may have been affected. Next, you should contact the website or service where you believe your information may have been compromised and let them know. You should also contact your bank or credit card company if you think your financial information may have been compromised.
Can a cybersecurity vulnerability have legal implications?
Yes, a cybersecurity vulnerability can have legal implications. Depending on the severity of the vulnerability and what type of data it affects, companies may be liable for any damages caused by a breach or other data theft. Companies that fail to take necessary steps to protect their networks from cyber threats could face stiff fines from government agencies and regulatory bodies. In some cases, individuals responsible for failing to prevent an attack could even face criminal charges.
Additionally, customers affected by a security lapse may be able to sue for compensation if their personal information is compromised in a breach.
Furthermore, organizations that do not follow industry-standard best practices regarding data security may be found negligent in a court of law. Therefore, organizations should take all necessary steps to secure their networks and data to avoid potential legal liabilities associated with cybersecurity vulnerabilities. This includes using adequate security measures, conducting regular staff training, and following industry guidelines for data protection. Doing so can help protect the organization and its customers against potential legal liabilities associated with cyber attacks.
The bottom line is that cybersecurity vulnerabilities have genuine legal implications that organizations must be aware of. Taking proactive steps to protect your network from threats can help reduce the risk of enforcement actions or lawsuits due to a data breach or other incident. Furthermore, having a robust security framework can also help protect your business from reputational damage from a cyber attack. Ultimately, taking a proactive approach to cybersecurity can go a long way toward mitigating potential legal risks.
What are the consequences of cybersecurity vulnerabilities?
Cybersecurity vulnerabilities are like the chinks in a superhero’s armor – they can have severe consequences for individuals and businesses alike. The impact can be significant, whether it’s a minor annoyance or a catastrophic failure.
Data breaches are the kryptonite of cybersecurity vulnerabilities, exposing sensitive information to the world. Cybercriminals can use this information to wreak financial havoc or commit identity theft, leaving individuals and businesses in a tough spot.
Losing trust is another consequence that can make even the mightiest companies tremble. Customers may think twice about doing business with a company with a history of cybersecurity issues, leading to a decline in revenue and a seriously damaged reputation.
Non-compliance with cybersecurity regulations can result in legal and regulatory penalties, including hefty fines, legal fees, and maybe even a little orange jumpsuit time. Intellectual property theft and cyber espionage can also leave businesses feeling like they’ve been hit with a sonic blast.
It’s vital to remember that a single data breach can have severe consequences, affecting an organization’s reputation and bottom line. Trust is hard-won and easily lost, and cybersecurity vulnerabilities can be the villain that takes it all away.
In short, cybersecurity vulnerabilities are no laughing matter. From data breaches to legal penalties, the impact can be significant. Therefore, it’s essential to take cybersecurity seriously and implement measures to prevent vulnerabilities from happening in the first place.
How long does it take on average to patch a known vulnerability?
Fixing a vulnerability can take different amounts of time depending on various factors. These factors include how severe the vulnerability is, how complicated the affected system is, and how efficient the organization responsible for the software or system is. Generally, reliable software vendors and organizations try to release patches for serious vulnerabilities as soon as possible. However, it can take a few days to several weeks to implement the patch due to internal procedures, testing, and coordination needed to ensure it works and doesn’t cause any new issues.

