Improvements in technology are driven by fierce competition that drives every provider to include new innovations to keep ahead of rivals. New and innovative businesses entering the market push that need for new approaches even further.
The field of cybersecurity is very active at the moment, with new techniques and attack prevention methods appearing almost every day. In the vanguard of cybersecurity, there’s an elite group of innovative companies building AI into products in order to defeat attackers and win customers. In this review, we’ll look at these companies in more detail.
Here’s our list of ten key innovators in cybersecurity that are using AI to give their products an edge:
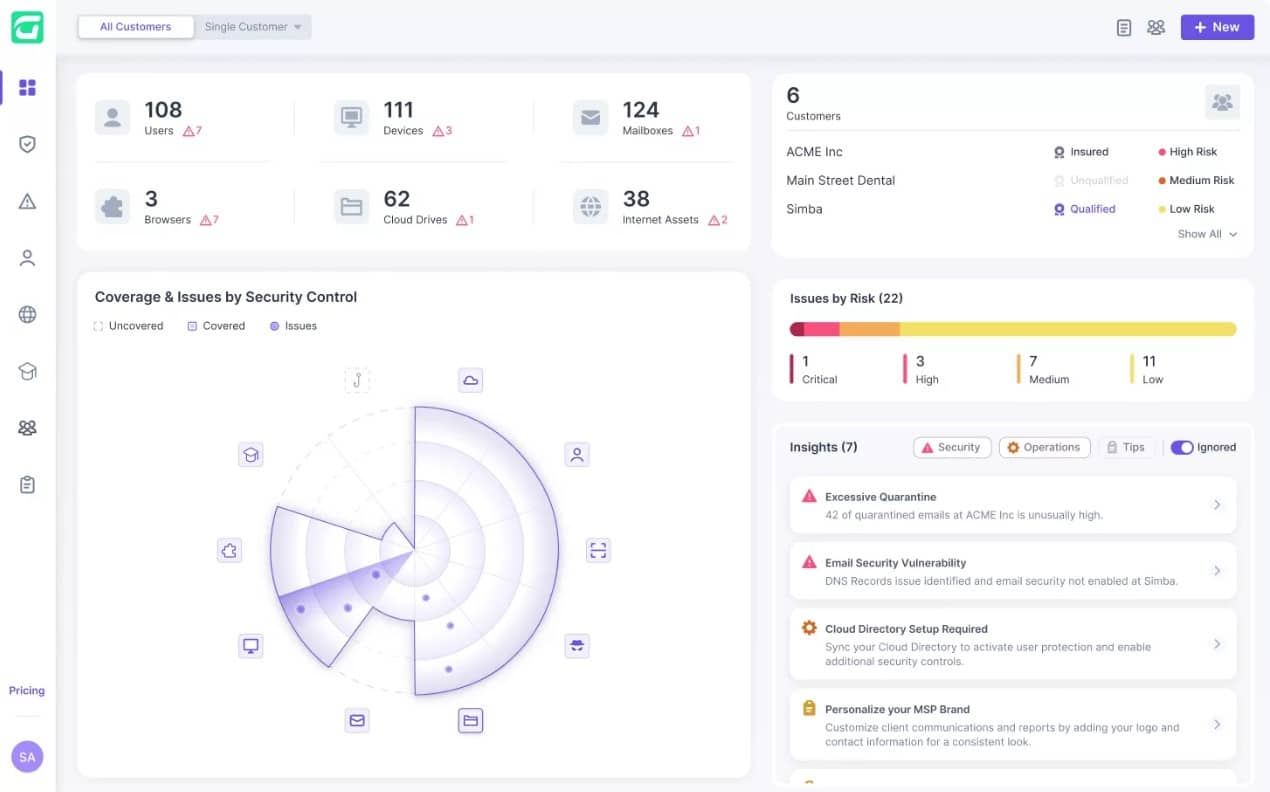
- Guardz EDITOR’S CHOICE This company creates security software for use by managed service providers. The targets for protection are the clients of the MSP rather than the MSP itself.Access a 14-day free trial.
- CrowdStrike
- Darktrace
- Cynet
- FireEye
- Check Point
- Symantec
- Sophos
- Fortinet
- Cylance
Before we delve into each of these companies, we’ll first briefly discuss the concept of AI.
About artificial intelligence
AI is the application of “heuristics” to programming. Rather than running through a list of instructions like a procedural programming language, AI methods maintain a database of instructions and act on data as variable. The selection of the next action to take relies on the application of probabilities.
This methodology enables the programs to write their own rule bases by tracking activities on a network. The longer a program is resident, the less likely it is that your business’s activities will be crippled by “false positives” that cause the security software to shut down internet access and close down programs.
The leading AI cybersecurity firms
Machine learning and variable workflows have transformed the cybersecurity industry. Here are details of how each of the key players are making their contributions to this advancement.
1. Guardz EDITOR’S CHOICE
Guardz operates a SaaS platform that provides three cybersecurity tools: Phishing Protection, Ransomware Protection, and Data Loss Prevention. These services are marketed to managed service providers for them to sell on to their clients as an extra service. The platform is the property of Guardz Cyber Ltd.
The company began operations in May 2021 and is based in Tel Aviv. Guardz is part of the large cybersecurity sector in Israel and maintains offices in the United States and the Netherlands. The US office focuses on sales, with the American market offering greater opportunities to Guardz than its home market. The Tel Aviv headquarters provides operations services and the Dutch offices, in Amsterdam, operate data center services.
The location in the Netherlands is necessary in order to be compliant with GDPR, which stipulates a requirement that information on individuals in the EU must be held and accessed within the EU. That location enables the company to operate in all of the nations of the European Union.
The US offices are in Miami, Florida. This is an attractive location that enabled the company to pitch to US venture capitalists. The business completed a Series A funding round, raising $18 million in December 2023. It is a private company with six major investors, including the George Kaiser Family Foundation, iAngels Crowd Ltd, and Hanaco Venture Capital.
The company was founded by Dor Eisner, who is currently the Chief Executive Officer, and Alon Lavi, who is now the company’s Chief Technology Officer. Eisner came up with the idea for the company when he learned about the existence of Attack-as-a-Service platforms that miscreants can use to try attacks on multiple companies through automated processes.
Those “spray and pray” systems are low-cost and spread attacks by cycling through IP address ranges without any particular knowledge of any targets. While larger businesses are well prepared to resist these attacks, SMEs are usually not so well protected. So, Eisner teamed up with Lavi to set up a cybersecurity platform to protect those smaller businesses.
A unique feature of the Guardz system is that it combines security tools with an insurance policy. One complication of the insurance feature is that it can’t be priced upfront in the way that software systems can. The Guardz platform provides three plan levels and the lower two do not include the insurance policy. These are priced per user per month – that is by the number of users in each client company that is served by the MSP.
The insurance policy is only included in the Ultimate plan. The edition’s definition doesn’t state a particular excess or limit to cover. This is because the terms of the insurance are flexible and depend on the requirements of the MSP that is managing the contract and the client that will benefit from it. That means that a single MSP could be managing several different policies.
The insurance policy is an interesting feature of the Guardz service and provides the company with a unique selling point. However, it could be seen as simply a way for the company to benefit from two sales to a single prospect. That is, it is a salesman’s dream come true but not necessarily a good deal for the client who should get several quotes for insurance before settling on one provider.
It could be seen that any client being proposed the Guardz system by its MSP could compare the Pro plan, which doesn’t include the insurance policy with the quoted price for the Ultimate plan, thus identifying the price of the insurance. That company should then get alternative quotes and decide whether to opt for the Guardz Pro plan plus a third-party insurance policy or choose the Ultimate plan.
Examining the options available to potential clients, it can be seen that the combination of cybersecurity and insurance is more of a gimmick than an innovative business plan. The company is still private and relatively new. It doesn’t publish what proportion of its sales are provided by each of its editions, so it remains to be seen whether the Ultimate plan is actually a big draw. Register for access to a 14-day free trial.
EDITOR'S CHOICE
Guardz is our top pick for a cybersecurity firm to watch because it founders are still with the relatively new company and are clearly interested in providing innovative cybersecurity solutions for small businesses. SMEs tend to be an overlooked market in the cybersecurity field. However, the idea of marketing the tool through MSPs offers Guardz a method of aggregating a number of small clients into a reasonably sized sale, thus distributing the costs of marketing and keeping the plan price affordable. The concept of offering insurance along with cybersecurity services is novel but it remains to be seen whether this is an industry disruptor. Guardz is well placed to try other products alongside its existing list of phishing protection, ransomware detection, and data loss prevention.
Download: Access a 14-day FREE Trial
Official Site: https://app.eu.guardz.com/signup
OS: Cloud-based
2. CrowdStrike

CrowdStrike is a relatively new name in the cybersecurity market. The business started up in 2011 and is officially called CrowdStrike Holdings, Inc. Its key security system is called CrowdStrike Falcon and this combines both cloud and on-device elements.
The secret weapon of the CrowdStrike Falcon system is an AI-based detection system, known as user and entity behavior analytics (UEBA). The UEBA concept is one of the major innovations that has thrust the system security industry forward, escaping the flawed AV detection model that had started to let too many new viruses onto devices.
The biggest problem with virus protection is that the service can never rest. Traditional anti-virus systems refer to a database of signatures, which are usually file or process names to look out for. However, as soon as AV providers detect a new virus and add it to the threat database, hackers simply tweak the names of their infected files to avoid detection.
Another problem is that it can take some time for AV providers to spot a new virus. The research labs that they need to run just to keep up with the new viruses that are produced are cost overheads. The UEBA strategy wipes out the need for those labs and also ends the problem that quite a few businesses always get hit by a new attack before the AV companies do anything about it. These new attack systems are called zero-day attacks.
The AI approach adopted by CrowdStrike monitors all activity on an endpoint, profiling each user’s activity and watching all of the system processes that get run on any normal day. This establishes a baseline of regular activity. The system continues to monitor all processes and raises an alert if a user suddenly does something different or if a previously unencountered system process starts up. This is a flag that draws extra activity tracking procedures into play.
The endpoint detection and response module that is associated with the UEBA will then kill the process, suspend the user account and/or isolate the device from the network to prevent further malicious activity.
Not only does the UEBA system shut down zero-day virus attacks, it also spots intruders, account takeover, and insider threats.
CrowdStrike started out as a cybersecurity consultancy. Its main business lay in assisting large businesses that had been hit by hacker. The company’s technicians were able to spot malicious activities, identify any damage or data theft that has occurred, and also kick those intruders off the system.
The company, based in Sunnyvale, California, first came to the public’s attention when it worked on detecting and cleaning out intruders and malware in the Sony Pictures data theft hack in 2014. CrowdStrike’s work to trace a series of email thefts from the Democratic National Committee (DNC) from 2015 to 2016 got the company’s name on news feeds regularly and pushed the brand into broader recognition.
During its early years, CrowdStrike had developed its own investigative tools for in-house use during work for its beleaguered clients. In 2013, the company adapted some of these systems and, with further work, produced CrowdStrike Falcon.
The founders of CrowdStrike were George Kurtz, Dmitri Alperovitch, and Gregg Marston. While Marston and Alperovitch have since retired from the company, Kurtz is still the CEO of CrowdStrike. The startup reached a valuation of $1 billion in 2017 and went public with a listing on Nasdaq (CRWD) in June 2019. As of August 2021, CrowdStrike has a market capitalization of $58 billion.
3. Darktrace
Darktrace developed its Enterprise Immune System as a platform for all of its cybersecurity products. EIS uses AI methodologies and populates status rule bases through unsupervised machine learning. The first thing that EIS needs to do when installed on a network is to establish a baseline of normal activity. This is termed the “pattern of life” in Darktrace terminology. Traffic pattern for each network, the activity of each device on the network, and the behavior of each user is modelled to provide this record of standard conduct.
With the pattern of life established, the monitoring system is then able to identify any event that is out of the ordinary. Deviations from the standard traffic patterns on the network raise alerts. The learning mechanism of EIS does not stop, but continues to refine the pattern of life models throughout its service life.
The EIS system’s establishment of a norm means that it doesn’t have to maintain a threat database. Any unusual occurrence on the network is treated as a threat. The pattern extends out beyond the corporate LAN to cover wifi segments, cloud-based resources, WANs, and the internet connections between them.
The detection of an anomaly triggers an automated response, which also relies on AI technology. This creates a full AI-powered Intrusion Prevention System (IPS). AI is also deployed in the Darktrace Threat Visualizer to connect together attacks of similar characteristics, enabling planners to understand the full complexity of threats to corporate resources.
Darktrace was founded in 2013, with directors who previously worked at Autonomy and key staff members with mathematics experience gained at the University of Cambridge. Other key members include former secret service personnel, such as the former CIO of the CIA, Alan Wade, and the former Director General of MI5, Lord Evans of Weardale KCB.
The company is headquartered in Cambridge, UK and has a second head office in San Francisco. The business reached a valuation of $1.65 billion by 2018. However, it is not registered on any stock exchange. Investors in the company include venture capital funds, including KKR, Summit Partners, Vitruvian Partners, and Samsung Venture Investment Corporation.
4. Cynet
Cynet deploys AI in its network threat detection systems that examine threats and act on them automatically. The ethos at Cynet is to make advanced threat protection as straightforward as running any system monitoring package.
The Cynet network protection suite is written to provide accessible threat protection to organizations that do not have specialist cybersecurity personnel. That said, the system is not just for understaffed small enterprises. The service’s customer base includes large multinationals with tens of thousands of employees, including organizations with a high cost of security failure, such as banks.
Cynet has one product, called Cynet 360. This is a complete cybersecurity system that includes AV endpoint protection through to device detection, threat prediction, user behavior modelling, and vulnerability management. The system has a discovery phase, which uses standard network topology mapping methods to discover all network devices and endpoints. The system checks through event logs and tracks traffic patterns to build up a baseline model of regular network activity. This logging stage creates a risk ranking for traffic sources and types of behavior. With these actions, Cynet 360 creates its AI knowledge base and threat monitoring can begin.
Threat detection extends to the placement of decoys masquerading as real endpoints, files, and servers, that aim to attract attackers away from genuine network resources.
The company is relatively new, being launched in 2015 by “boy security wonder,” Eyal Gruner. Young Gruner had already developed and sold off cybersecurity firm Versafe by the age of 25 in 2013.
Gruner’s solid reputation as an innovator and high flyer no doubt helped the fact that by 2018, Cynet was picking up speed, expanding to serve large corporations and drawing in venture capitalists. A 2018 sale of a small stake in the company to IT investors for $20 million gave the entire enterprise a multi-billion dollar price tag.
Key investors in Cynet include Shlomo Kramer, founder of Checkpoint, which is also on our list. Other key providers of funds are Norwest Venture Partners and Ibex Investors. Cynet is based in Tel Aviv, Israel and is still a private company with no stock exchange listing. Eyal Gruner still heads the board as co-CEO, alongside Uzi Krieger.
5. FireEye
FireEye is much older than the two previous companies examined in this list. It was founded in 2004 and specialized in threat research and recovery consultancy services. This is a labor-intensive field of work and didn’t make the company any money.
Through innovation and acquisition, the company has moved into the production of cybersecurity tools that use AI to monitor networks and spot anomalies. This strategy, together with moving from a fee-based structure to a subscription Software-as-a Service has made the business profitable and turned what was beginning to look like an overrated novelty into a sought-after investment.
FireEye was founded in 2004 by a former Sun Microsystems engineer, called Ashar Aziz. One of the first financial backers of the company was In-Q-Tel, the investment arm of the CIA. The company expanded through acquisition, resulting in a high revenue, but no profit. Ashsar was the CEO of the company until the end of 2012. He stepped down on the appointment of former McAfee CEO, David DeWalt.
DeWalt was seen as an attractive corporate head for the stock market, which was a key attribute needed for a company that wanted to launch an IPO. FireEye listed on the NASDAQ stock exchange in late 2013. As a tech startup, FireEye never had problems raising finance. However, the bar of expectation is much higher for listed companies and FireEye needed to go through a restructuring in 2016 to finally push the business into generating profit. Today the business is worth $3.3 billion.
6. Check Point
Check Point is a maturing technology company that has managed to transition from “startup” status through to established multinational. This Israeli company has long been at the forefront of the use of AI in cybersecurity.
Starting off as a firewall producer, the company consolidated its position in that market in 2003 with the acquisition of Zone Labs, the makers of ZoneAlarm security software. Check Point expanded into threat detection and prevention in 2006 with the acquisition of NFR. This purchase indicated the main move of the company into more complex cybersecurity solutions.
Rather than producing a specific AI-based threat management product, the company invested in the development of three AI-driven platforms that contribute to many of the business’s key offerings. These are Campaign Hunting, Huntress, and Context-Aware Detection (CADET).
Campaign Hunting is a centralized service that updates client-site threat detection systems with the latest attack vectors and defense strategies. This is similar to the virus databases used by antivirus providers. The data transmission is two-way because onsite implementations report back to the Check Point lab when any new threats are detected. This tool accounts for about 10 percent of Check Point’s successful threat prevention events.
Huntress is a sandbox for software that is about to be introduced to a network. The AI-based system analyzes the performance and behavior of the program under examination and reports back to Check Point’s central system if anomalies are encountered. Once again, the solutions derived for this analysis are shared with all of Check Point’s customers.
CADET is an entire platform for all of Check Point’s network protection products. A network discovery and monitoring system underlies this platform and its research extends through to applications and out into the cloud. The monitor continually assesses all events occurring in the business’s network, including email contents and exchanges with web servers.
The CADET AI engine aggregates event data in real-time, so attack vectors that exploit seemingly unrelated resources simultaneously can be blocked. The unsupervised machine-learning feature of CADET hones the threat database to cut down crippling false positives. It creates a digital security analyst and triggers prevention measures automatically.
As an early leader in the cybersecurity field, Check Point has hothoused many of the cybersecurity stars of the industry. This is where Imperva founder Shlomo Kramer first built his credibility in the industry, and Palo Alto Networks founder, Nir Zuk made his name at Check Point before going on to found a rival company. To a certain extent, this talent flight makes Check Point a victim of its own success, as it has acted as a training academy for future rival startup entrepreneurs.
The company went public in June 1996 with a listing on the NASDAQ exchange. The headquarters of the business are still in Tel Aviv, Israel, where the company first started up, and there’s a major development center in San Carlos, California. Thanks to Check Point’s ability to keep ahead of the competition and exploit new technologies, such as AI, the company now has a market capitalization of $19.4 billion. This is the highest valuation of all of the innovative cybersecurity firms on our list.
7. Symantec
Symantec is a well-known brand, with which the general public is familiar. The company is famous for its firewall and antivirus products, but in recent years it has harnessed the innovation of AI to expand its excellence into threat detection and prevention. Symantec also owns the Norton brand and uses that to market its consumer products to the general public. Since a demerger of its information management functions into Veritas Technologies in 2016, Symantec has become a highly focused corporate cybersecurity solution provider.
The key development at Symantec that puts it on our list of the leading AI innovators is its Targeted Attack Analytics (TAA) tool. Symantec decided to pour resources into AI research in 2014 and the results of all of that R&D is now feeding through the development pipeline into innovative products. TAA is one of the fruits of that labor.
TAA was released in May 2018. It uses unassisted machine learning to model patterns of behavior on the network and create a baseline of performance. Any deviation from regular activity raises an alert. The AI functions of TAA sit on top of the Symantec Cyber Defense Platform, which is able to gather performance data from many points on the network simultaneously. TAA is principally integrated into the Symantec Advanced Threat Protection family of products, but it will probably eventually roll out to all Symantec cybersecurity packages.
As a publicly traded company, Symantec is an easy investment to make. The company is listed on the NASDAQ exchange and currently has a market capitalization of $14.5 billion. It’s a component of the NASDAQ 100 and the S&P 500. As a large corporation, Symantec offers a safe investment. However, mature corporations don’t usually deliver much capital growth.
The innovative deployment of AI by the company makes it a good blend of capital-increasing risk and savings-defending stability. Symantec’s large investment in AI was a calculated risk, and after four years of intensive research, that gamble is starting to pay off.
8. Sophos
British-based Sophos has its headquarters just outside of Oxford. It also has a US base in Burlington, Massachusetts and offices around the world. The company began as an antivirus producer in 1985. Sophos expanded its range of products and opened new offices across the globe to feed its expansion, much of which was driven by acquisition. The move by Sophos into AI-based cybersecurity products occurred in February 2017 with its acquisition of Invincea.
Invincea was founded in 2006 under the name Secure Command, LLC. Its first aim was to produce security products for mobile devices. It landed a $21 million commission from DARPA to secure the Android devices used by the military and its personnel. The fruit of this project is called X and it is based on AI-driven deep learning techniques. Sophos has applied the X strategy to products for a range of operating systems.
The two main AI-based Sophos products are Intercept X for endpoint protection and the XG Firewall to protect networks.
Intercept X uses AI to avoid the need for a threat database distributed from a central location. The heat of the service is a deep learning neural network that was developed by Invincea. This monitors regular activity on the protected device and raises alerts when unexpected events occur. Endpoint Detection and Response (EDR) triggers workflows and actions to shut down exploits and isolate infections once they are detected.
The Intercept X methodology has been particularly effective at blocking ransomware attempts. It is also a comprehensive solution to zero-day attacks, which means that no company needs to be the first victim of a new virus.
The XG firewall is a hardware device for networks. Its dashboard gives feedback on current events and traffic on the network, but its main value lies in its automated response mechanisms that enforce security without the delays caused by the necessity for human intervention.
Sophos was funded by venture capitalists until June 2015, when it floated on the London Stock Exchange. It is now a component of the FTSE 250 index and has a market capitalization value of £1.5 million ($2 billion). Venture capitalists are still major holders of stock and the company has become of interest to IT and security-related exchange-traded funds.
9. Fortinet
Although Fortinet is not a well-known brand to the general public, it is a leader in the cybersecurity industry and is slightly bigger, in terms of market capitalization, than the more famous Symantec.
The company has its headquarters in Sunnyvale, California and was started up in 2000 as Appligation, Inc. by brothers Ken and Michael Xie. Ken Xie had previously been an executive of NetScreen Technologies, a company that he co-founded, and Michael Xie was an executive of ServeGate before starting up Application. The company name was changed to AppSecure in late 2000 and then became Fortinet.
The first product that the company produced was FortiGate, a hardware firewall. This is still a key product of Fortinet, although it has been through a number of redevelopment phases over the years. The firewall is now also available as a cloud service.
The company developed the concept of the security fabric to express a strategy that collects network activity points from several points in the enterprise to search for threats. The general industry term for this category of service is “unified threat management.” This workflow includes endpoint protection, access protection, application monitoring (such as email and web security), and advanced threat protection.
The various data collection points in the organization collect threat intelligence, which is compiled at a central point on the networks to monitor for intrusion or infection. Fortinet developed the AI-based Self-Evolving Detection System (SEDS) as the main analytical engine of the security fabric. The defense mechanism requires access to network resources, such as firewall rules and operating systems, to enable it to trigger automated defense actions to block any detected threats.
Fortinet has continuously proved to be a good bet for investors. It first turned a profit in 2008. By 2009 the company supplied 15 percent of the unified threat management market. When the company floated on NASDAQ in November 2009, its share price rose from $9 to $16.65 on the first day of trading. Today, Fortinet has a market capitalization of $14.84 billion.
10. Cylance
Cylance started out as an independent cybersecurity company, but since November 2018, it has been a division of BlackBerry Limited. The company’s sale valued it at $1.4 billion. BlackBerry has maintained Cylance as a separate brand.
The founder of Cylance, Stuart McClure is well-known in the cybersecurity industry. He co-founded a security consultancy, called Foundstone in 1999 and sold it on to McAfee in 2004. That buyout saw McClure appointed to Chief Technology Officer at McAfee. That position, together with his book Hacking Exposed, gave McClure a high public profile.
Cylance began existence in 2012 at a base in Irvine, California. It is reputed to be the first cybersecurity protection provider to apply AI to its system. The company became a leader in the field of IPS. Key early backers included Dell Ventures, CapitalOne Ventures, and Insight Venture Partners.
The strong reputation of McClure and his concept of malware prevention rather than removal appealed to venture capitalists, who recognized the founder’s vision as an industry disruptor. This prediction provided to be accurate as all of the other companies on this list followed McClure’s lead.
All of Cylance’s products integrate AI technology. Its main packages are:
- Cylance Protect
- Cylance Optics
- Cylance Threat Zero
- Cylance Smart Antivirus
Cylance Protect is an endpoint security system. Essentially this is an AI-based anti-malware system that looks for changes in patterns of activity on the device rather than relying on a threat list distributed over the internet from the AV provider. In addition to checking on activities, this system controls access to the device.
Cylance Optics is a corporate version of Cylance Protect. The threat detection is applied to all devices on the system and stored centrally. The responses to a detected intrusion are triggered automatically, making this a classic IPS.
Cylance Threat Zero is the consultancy arm of the company. Consultants propose a blend of products and can also customize protection software.
Cylance Smart Antivirus is another AI-based AV system, which is suitable for home users and small businesses.
BlackBerry is also innovating its security products by integrating AI, so the acquisition of Cylance will propagate this new technology throughout the parent company and its other divisions. The company is based in Waterloo, Ontario, Canada, and it focuses on business software and Internet of Things (IoT) firmware. The company is listed on the Toronto Stock Exchange and has a market capitalization of C$6.25 billion ($4.75 billion).
Investing in AI-based cybersecurity
If your quest for information about AI-based cybersecurity firms is driven by an interest in investing, you can see that a number of the companies discussed here are listed on stock markets, making it easy for you to buy shares in them.
Successful startups make the most capital growth for their investors. However, they also endure the highest risk. New cybersecurity firms can take years to gain visibility in the market and some fold before they get an opportunity to attract customers.
It can be very difficult to work out which loss-making innovators are worth the investment and which are a waste of money. For example, Fortinet didn’t make any profit for its first eight years. Venture capital funds can be difficult to get into and some lock you in, so you can’t recoup your nest egg whenever you want.
The best option for investing in AI-based cybersecurity probably lies with exchange-traded funds (ETFs). Here are some worth looking into:
ETFMG Prime Cyber Security ETF (NYSEARCX:HACK)
This fund was one of the first to invest specifically in cybersecurity firms. It currently has about $1.58 billion dollars invested in the sector. The company spreads its risk by making sure it never invests more than 4.62 percent of its fund in one company. It currently holds investments in 52 cybersecurity enterprises that range from Cisco Systems and FireEye, through Sophos, down to new arrivals on the stock exchange. It focuses investments on components of the Prime Cyber Defense Index.
First Trust NASDAQ Cybersecurity ETF (CIBR)
This fund was set up in 2015 and has attracted $760 million in funds. The company is another holder of Sophos, which is on our list of cybersecurity firms to watch. The EFT is sponsored by First Trust Advisors and has the components of the Nasdaq CTA Cybersecurity Index as its investment targets.
ALPS Disruptive Technologies ETF (NYSEBATS:DTEC)
As a fund that prioritizes innovators, this is one to go for if you are looking for AI investment in general. The managers reserve 10 percent of the fund for investments in cybersecurity firms.
SPDR Kensho Future Security ETF (NYSEARCA:XKFS)
Set up in 2017, this fund spreads its risk across 62 companies with a policy to not invest more than 2.79 percent of its money in one stock. Targets for this investment fund include cybersecurity and military technology.
Industry disruption
As you can see from the narrative contained in the sections above, one innovator adopting new technology in a sector causes many others to follow. For newcomers, a fresh take on technology, such as AI can provide them the wedge to force open a space in an already crowded and competitive market. When that happens, established actors in the market are faced with the risk of ignoring the new approach, which may fail, or pouring resources into integrating the new technology to a greater extent than the newcomer.
Innovations such as AI will continue to emerge and change the way a hitherto stable group of software operates. Cybersecurity, along with all of the technology sector will continue to evolve and the leaders of the industry will change according to their success or failure in adopting new technology.
Image: Binary castle from Pixabay. Public domain.