A Privacy Impact Assessment (PIA) is a structured process that allows organizations to evaluate how their handling of personal data may affect individuals’ privacy rights. With privacy regulations such as GDPR, CCPA, and HIPAA evolving rapidly, PIAs have become a crucial practice not only for compliance but also for protecting sensitive information and maintaining stakeholder trust. Businesses of all sizes rely on PIAs to proactively identify privacy risks arising from projects, operations, or policies, giving them the opportunity to implement safeguards before problems occur.
The main objective of a PIA is to scrutinize how personal data is collected, processed, stored, and shared, ensuring alignment with both legal requirements and ethical best practices. By pinpointing gaps or vulnerabilities, organizations can adjust workflows and technology practices to minimize the risk of breaches, unauthorized access, or regulatory violations. Beyond compliance, a well-conducted PIA demonstrates an organization’s commitment to responsible data stewardship, helping build confidence among customers, partners, employees, and regulators.
Typically, a PIA follows several key steps. It begins with scoping the project and identifying the types of data involved. Next, potential privacy risks are assessed, followed by evaluation of the impact of those risks and recommendations for mitigation. Specific areas often examined include data minimization, consent management, security controls, and incident response readiness. Some PIAs also consider long-term implications, such as how new technologies or business models might affect privacy in the future.
PIAs are especially vital in sectors that handle highly sensitive information, including healthcare, finance, and government, where the consequences of breaches can be severe. They are also increasingly important for businesses deploying innovative technologies, such as AI or IoT devices, where personal data usage must be carefully managed from the outset. By embedding privacy considerations early in a project’s lifecycle, organizations can reduce risks while maintaining operational efficiency.
Ultimately, a Privacy Impact Assessment is more than a compliance checkbox. It provides actionable insights that help organizations anticipate, evaluate, and mitigate privacy risks, aligning security practices with evolving regulations and ethical standards. By integrating PIAs into standard procedures, companies not only protect sensitive information but also foster trust, improve resilience, and strengthen their long-term success in today’s digital landscape.
Overview of Privacy Impact Assessment
A Privacy Impact Assessment (PIA) is a type of impact assessment conducted by an organization such as a government agency or corporation to determine the impact that a new technology project, initiatives or proposed programs and policies might have on the privacy of individuals. It sets out recommendations for managing, minimizing, or eliminating that impact. A key goal of the PIA is to effectively communicate the privacy risks of new technology initiatives. It also provides decision-makers with the information necessary to make informed policy decisions based on an understanding of the privacy risks and the options available for mitigating those risks.
PIA is very much similar in principle to the term Environmental Impact Assessment (EIA) where the environmental implications of a new project or plan are identified prior to the decision to move forward with the proposed action. Long before PIA became mainstream, Technology Assessment (TA) was used as a means of assessing and rating the societal impact of new technologies. As computing technology began to gain popularity in the 1990s, there became a need to measure the effectiveness of an organization’s data security and privacy risk of its systems, especially with most data now being stored on computers or other electronic platforms. This gave rise to the idea of Privacy Impact Assessment, and the methodology used by both TA and EIA inspired or formed the basis for the creation of the PIA.
PIA provides benefits to various stakeholders, including the initiating organization itself as well as its customers. PIA implementations can help build trust with stakeholders and the user community by demonstrating due diligence and compliance with privacy best practices. Privacy issues that are not adequately addressed can impact the community’s trust in an organization, project, or policy.
PIA provides a way for an organization to demonstrate commitment to, and respect for user privacy. Other key benefits include:
- Reduces future costs in legal expenses, damage to reputation, and potential negative publicity, by considering privacy issues early in a project.
- Demonstrates to employees, contractors, customers, citizens that your organization is committed to protecting and upholding privacy rights.
- Provides a way to detect and mitigate privacy problems before they occur to avoid costly or embarrassing privacy mistakes.
- Promotes and demonstrates awareness and understanding of privacy issues within your organization.
- Provides evidence that an organization attempted to prevent privacy risks
- Helps your organization gain public trust and confidence.
When to Undertake a Privacy Impact Assessment?
The very first step of the PIA process is to determine whether it is required. If an organization discovers that there is the potential that a project they are about to undertake has a high risk of impact on user privacy, it should carry out a privacy impact assessment. This will ensure that privacy risks and impacts that may be associated with the project are identified and mitigated.
So the question is: What exactly constitutes a high privacy risk project? Well, according to experts, one of the obvious signs to look out for in a project is if it involves a new or changed way of collecting, storing, analyzing, sharing, or destroying personal information. A project may be a high privacy risk if it involves new or changed ways of handling personal information that are likely to have a significant impact on user privacy. Determining whether a project meets this threshold requires a thorough understanding of all aspects of a project.
A threshold assessment is a preliminary assessment to help you determine if a project you are about to undertake could be a high privacy risk project, or has the potential to impact user privacy. This will give you an insight into the level of risk associated with the project. Of course, not every project will require a PIA. What a threshold assessment does is help unravel inherent privacy implications by looking out for factors that point to the potential for a high privacy risk, which will require a PIA to be conducted. These factors may include activities such as the collection of new or additional personal information, or actions that lead to an individual loss of control over their personal information. The consequences, including negative impacts on mental or digital wellbeing, could be significant for one individual, group of individuals, or the society at large—for example, increased facial recognition or biometric mass surveillance.
Once you have determined that a project portends high privacy risk to the user community, you should initiate a privacy impact assessment in accordance with the level of risk, to demonstrate commitment to and respect for user privacy. In fact, a PIA should be undertaken early enough in the project so that its findings can influence the overall design or outcome of the project. Failure to undertake a PIA at this point may expose your organization to risks such as privacy breaches, negative publicity, bad reputation, and user resentment, among others.

How to Undertake Privacy Impact Assessment?
Several regulatory standards around the world including the EU GDPR mandate organizations to undertake PIA before embarking on any project that presents a specific privacy risk by virtue of its nature, scope, or purposes. The scale and complexity of your PIA will depend on the scale and complexity of your intended project. For complex projects, the PIA process and the resulting PIA report may contain more detailed and highly technical information. But due to the lack of a unified guideline on how to carry out such an assessment, most organizations processing personal data find it difficult to carry out a PIA.
| Features | ISO (International) | ICO (UK) | BSI RFID PIA (Germany) | IPC PbD (Canada) | HIQA (Ireland) | PIA Guide (US) | Privacy & Data PIA (EU) |
|---|---|---|---|---|---|---|---|
| Document Type | Framework | Guideline | Guideline | Framework | Guideline | Guideline | Framework |
| Target Audience | Organization processing personally identifiable information | Organization handling personal data | RFID operators | Organization processing personally identifiable information | Health and social care | SEC system owners and developers | RFID applications |
| Methodology | 4-phase PIA | 5-phase PIA | 6-phase PIA | Guided by the PbD principles | 4-phase PIA | 2-phase PIA | 6-step PIA |
Table 1.0 Comparison of PIA Frameworks and Guidelines
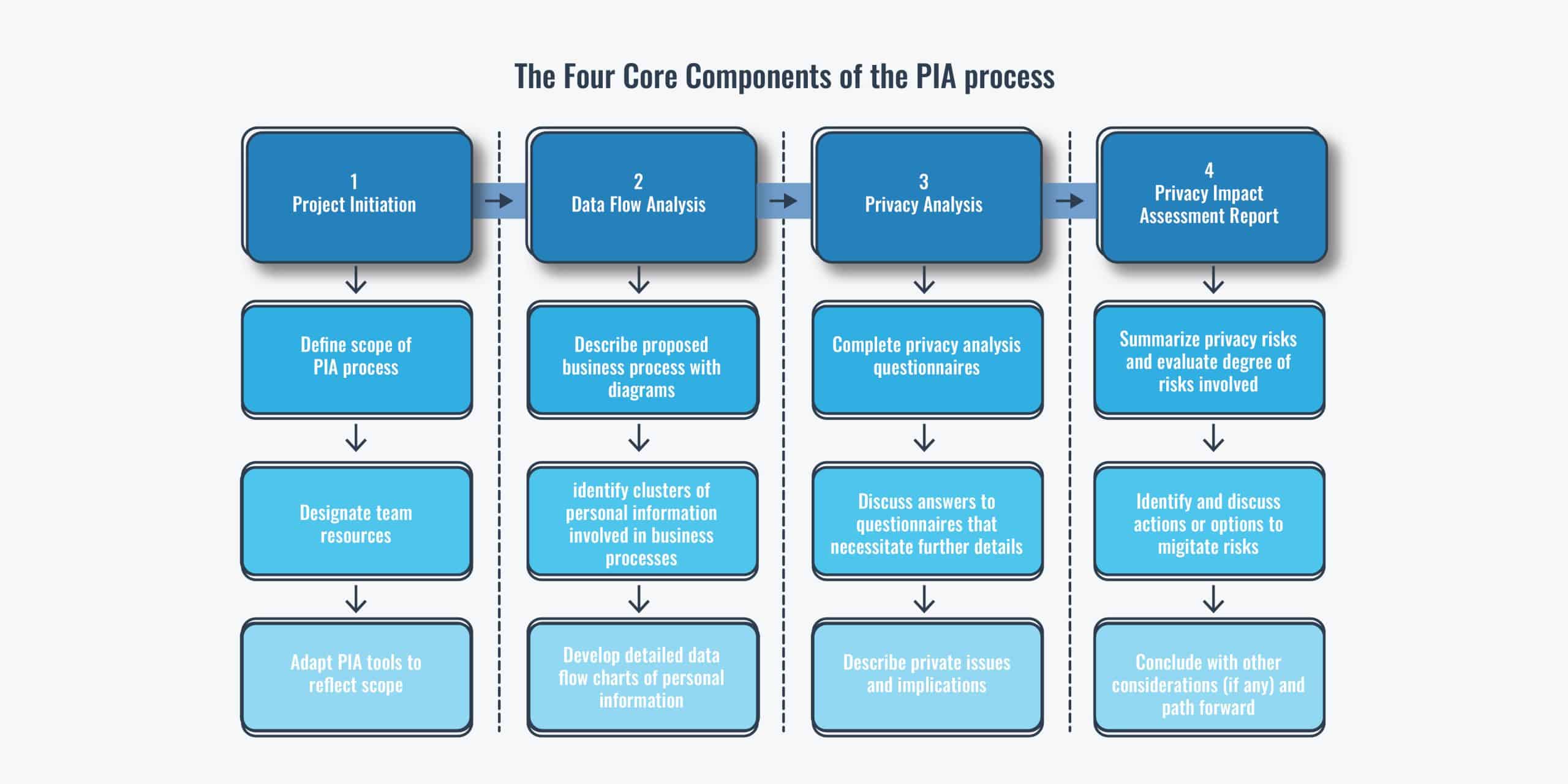
However, most Data Protection Authorities (DPAs) around the world such as the UK Information Commissioner’s Office (ICO), the Treasury Board of Canada Secretariat, and the International Organization for Standardization (ISO), among others have published high-level guidelines or frameworks that serve as a guide to conducting a successful PIA. Please see Table 1.0 above for a detailed comparison of some of the popular PIA frameworks and guidelines. The methodologies may vary, but the fundamental core components are similar. The PIA process from the various PIA frameworks and guidelines can be summarized in the following four core components:
- Project Initiation: The project initiation phase is the first phase of the PIA process life cycle. It is at this stage that the actual scope of the PIA process is determined and defined. If the details of the project are not yet clear at this stage, the organization may choose to do a preliminary PIA to determine the type of personal information involved in the project. The preliminary analysis is important at the early stage of the project so that the resulting PIA process can be considered in the project execution. Once the details of the project become clearer and you discover that there is the potential that the project has a high risk of impact on user privacy, you can then move on with a full PIA. Some the information to consider at this stage include:
- Documents relevant to the project such as the project charter, project designs, project plan, as well as any legislation relevant to the project.
- Information about the type of data involved in the project and how it is captured, stored, accessed, analyzed, and shared.
- Any relevant agreements such as information sharing agreements, disclosure agreements, data use agreements, Memorandum of Understanding (MoU), research agreements, etc.
- Any existing relevant PIAs already completed for this project.
- Data Flow Analysis: The data flow analysis phase involves a description and analysis of the detailed data flow, architecture, business processes, and mapping out how the personal information flows through the organization as a result of the intended technology implementation. The purpose of mapping information flows is to describe how your project deals with personal information. A clearly mapped information flow helps to identify privacy issues in the PIA process. Diagrams and tables are usually used to depict the flow of personal information, and the different types of personal information to be used in the project.
- Privacy Analysis: The privacy analysis phase is focused on the data flows in the context of applicable privacy policies and legislation, and to expose gaps that may lead to a breach of user privacy and public trust. Questionnaires are usually used as a checklist that facilitates the identification of major privacy risks and issues associated with the intended project. The questionnaires are to be completed by the personnel involved with the movement of personal information. This helps to gauge conformity with relevant privacy regulations and other privacy best practices and to bring to the attention of the project board or decision-makers any privacy issues directly or indirectly associated with the project that may raise public concerns.
- Privacy Impact Assessment Report: This is the final and most critical component of the privacy impact assessment process. A privacy impact report seeks to identify and document the privacy risks and the associated implications of those risks along with a discussion of possible remedies or mitigation plans. The report should be submitted to the project board or project steering committee for review and approval. The approved PIA report serves as an effective communications tool that demonstrates a commitment to transparency and shows that the project has been designed with privacy in mind. The PIA report should among other things include:
- Recommendations on how to manage or mitigate privacy risks, as well as any privacy risks that cannot be mitigated
- The outcome of your privacy impact analysis and compliance checks
- A description of the information flows involved in the project
- The methodology used to undertake the PIA
Automated PIA Tools
Like many other business procedures, a Privacy Impact Assessment can be supported with automation. Ketch, for example, is a privacy and compliance management platform that includes features for automating PIA work. The system helps the different business teams involved in a PIA work together more effectively, and it also integrates with third-party tools to exchange data used in assessment steps.
Another tool that automates PIA processes is Cookiebot. This tool can automatically create a custom privacy policy for your website and update it to meet the evolving requirements. Besides saving costly legal fees and time-consuming research, this tool also supports compliance with GDPR and other U.S. privacy laws.
You can read more about Ketch, Cookiebot, and the other PIA tools we recommend in The Best PIA Software and Tools.
What Makes a Good PIA?
PIAs are only as good as the process (internal and/or external) that produces and supports them. This means that the right privacy culture, data privacy governance model, and the independence of the assessor must be fully guaranteed and embedded in the PIA process and the organization initiating it.
Here are some of the essential characteristics to look for in a good PIA:
- It should answer the following questions: What personal information is collected? How is the information collected? Why is the personal information collected? What is the intended use of the personal information? Who will have access to the personal information? To whom will the personal information be shared? What safeguards are used to protect personal information? How long will the data be retained? How will the data be decommissioned and disposed of?
- It should identify risks to all forms of privacy including the privacy of the person, personal behavior, personal communications, and personal data as well as information about how those risks can be mitigated.
- It should go beyond merely fulfilling compliance requirements with relevant privacy and data protection legislation.
- Is a “living” document that should be revisited and updated if changes to the design of the project create new privacy impacts that were not previously considered.
- Is especially effective if they are published before a technology implementation is completed.
It is important that actions are taken to implement the recommendations made in a PIA report. It can often be helpful to prepare a plan for implementing the recommendations including what actions need to be taken, roles and responsibilities, and time-frames.