What is Endpoint Security?
Endpoint security focuses on protecting the devices that connect to a network, often referred to as endpoints. These include laptops, desktops, smartphones, servers, and other systems that access organisational resources. The aim is to secure each of these entry points so they do not become vulnerabilities that attackers can exploit.
As remote work and device diversity continue to increase, securing endpoints has become a critical part of any cybersecurity strategy. Endpoint security solutions apply protection directly at the device level, using tools such as antivirus and anti-malware software, firewalls, encryption, and intrusion detection systems to monitor and block suspicious activity.
Modern solutions go beyond traditional protection by incorporating machine learning and AI to detect advanced threats, including zero-day exploits and persistent attacks that may bypass conventional defences. This allows organisations to identify and respond to threats more quickly and effectively.
A major advantage of endpoint security is its ability to protect devices outside the traditional network perimeter. With employees working remotely or using personal devices, endpoints are no longer confined to a controlled environment. Security tools help enforce policies and provide continuous protection, regardless of location.
By securing endpoints, organisations can reduce the risk of cyberattacks, protect sensitive data, and maintain the integrity of their systems. As threats continue to evolve, strong endpoint security remains essential for safeguarding digital environments.
What Does Endpoint Security Software do?
Next-generation endpoint security tools are based in the cloud and monitor each device in your network for threats like viruses and malware.
Once a threat is detected, they notify the user and implement automated remediation to fix the problem.
When searching for endpoint security solutions, you will find that the capabilities of these platforms differ depending on which vendor you buy from. However, some of the main features you can expect to see include:
- Endpoint management
- Antivirus
- Integrated firewall
- Network access control
- Whitelisting tools
- Intrusion detection and response (including zero-day threats)
- Root cause analysis
Endpoint security platforms are usually cloud-based and centralized so that the user can manage multiple devices from one location. Many solutions will not only be able to detect cyber attacks but will also be able to respond with remediation actions automatically to resolve security issues as they emerge.
Automated endpoint security tools are very useful for enterprises because they detect and address threats quickly. Faster remediation means there is a lower time to resolution and decreases the risk of downtime, which lowers the level of cost/disruption of an attack.
Antivirus vs Endpoint Security
It is important to note that endpoint security software offers a far more diverse range of functionality than an antivirus system, which primarily focuses on combating viruses.
Antivirus software and endpoint security solutions have the same goal to protect network infrastructure, but they differ in the way in which they confront these threats.
While an antivirus and endpoint protection solution each aim to protect endpoints, they both serve a different purpose. An antivirus solution is designed to detect and remediate viruses on a single device; whereas an endpoint security tool protects an entire network and detects threats like malware and viruses across multiple devices.
From a security standpoint, endpoint protection tools are superior to antivirus solutions because they enable you to manage a network full of devices from a single location. While antivirus tools are excellent at detecting and removing malware from devices, they often need to be installed on each device, which creates more manual work for an administrator.
Why is Endpoint Security Important?
Endpoint security is vital for modern organizations because endpoints are a key target for cyberattackers. The growth of sophisticated online threats has meant that securing devices requires much more than installing an antivirus.
Keeper and Poneman Institute have found that 82% of SMBS have experienced attacks in which malware evaded their legacy antivirus solutions.
As a result, companies need up-to-date solutions to be able to protect against these emerging attacks that frequently sidestep traditional antivirus solutions.
At the same time, networks as a whole are becoming more decentralized. With an increased number of wireless devices in the workplace and the widespread adoption of IoT devices fast approaching, there is a distinct need for scalable centralized endpoint security solutions to secure devices.
In the future, enterprises will need centralized endpoint security solutions to detect threats on devices and manage security policies remotely. Those enterprises that don’t update are likely to struggle against the next generation of cyberattacks.
Common Threats to Endpoint Security
When securing endpoints throughout your environment, there are many endpoint security threats that you need to be aware of. Some of the most common threats to endpoints include:
- Phishing attempts
- Ransomware
- Unpatched software
- Data theft
1. Phishing Attempts
One of the most common threats companies encounter are phishing attempts. Phishing attempts are when a cyberattacker masquerades as someone else to trick the recipient into giving up sensitive information. For example, in an email phishing attempt, an attacker could send you a bogus email from a corporate address to trick you into clicking a link or downloading an attachment.
Many employees receive email from corporate spoofed email addresses with a link requesting that they reset their password. If they click on the link and reset the password the attacker acquires their login information and can use it to gain access to services in the network.
2. Ransomware
Ransomware is a type of malware that encrypts the victim’s files. After the files have been encrypted an attacker will demand a ransom from the victim so that they can have access to their files. The victim will be sent instructions detailing how to pay the fee and obtain a description key. Many attackers demand payments in the form of cryptocurrencies like Bitcoin.
3. Unpatched Software
Unpatched software leads to vulnerabilities. Attackers generate exploits to services every single day, and patching devices is essential for issuing updates that protect against those vulnerabilities. Enterprises that don’t install patches give attackers an opportunity to exploit those vulnerabilities and gain access to the network.
4. Data Theft
Another increasingly common threat is that of data theft. Cyber attackers are targeting businesses and hacking into corporate networks to steal private information. Attackers will break into a network and then copy information from all the resources they can get their hands on. These intrusions usually take place to obtain financial data that can be used for fraudulent activity.
Endpoint Security Challenges
1. Too Many Services
Despite the abundance of endpoint security solutions on the market, many companies struggle to keep internal systems secure. One of the main reasons for the difficulties protecting endpoints is the number of services modern companies use each day.
The sheer diversity of devices, applications, and services used in a network can make it difficult to maintain transparency and to verify that all activity is legitimate. Endpoint security solutions, network monitoring tools, and configuration managers are key to maximizing visibility and detecting malicious activity.
2. Too Much Admin
Another key challenge is the tremendous amount of manual administration required to manage a large network of devices. Many large companies lack automated solutions for managing devices, which makes it difficult for administrators to identify and troubleshoot security issues promptly.
It’s not unusual for network administrators to have to spend countless hours conducting tedious manual tasks like installing security patches and updates to devices. All the time spent on manual administration takes time away that the administrator could be using to respond to threats. This is why automated configuration management tools, network monitors, and endpoint security tools are valuable for saving time.
3. Limited Physical Security Controls
Finally, even if an enterprise has the right solutions to monitor employee endpoints, it often lacks physical security controls. These controls are essential for protecting against data breaches by preventing on-site systems from being breached by unauthorized users.
Physical security controls are one of the most underrated aspects of endpoint security, and many organizations are over-reliant on software to protect against attackers. If an attacker is on-site, then you need to have controls like passwords and locks in place to protect against breaches.
Endpoint Security Best Practices
1. Adhere to the Principle of Least Privilege
Given that your endpoints are an entry point to your network, you need to take steps to limit access where possible. If a malicious entity obtains physical access to your devices then there is a high risk of a data breach and data loss. One of the best ways to mitigate this threat is to embrace the principle of least privilege.
The principle of least privilege is where subjects are only given the privileges necessary to complete a function or task. The idea is that users shouldn’t have the authorization to access services that aren’t essential to their daily tasks.
Adhering to the principle of least privilege will limit the exposure of your IT assets to internal threats. The lower the number of employees who have administrator access to a device, the less chance that the device will become compromised.
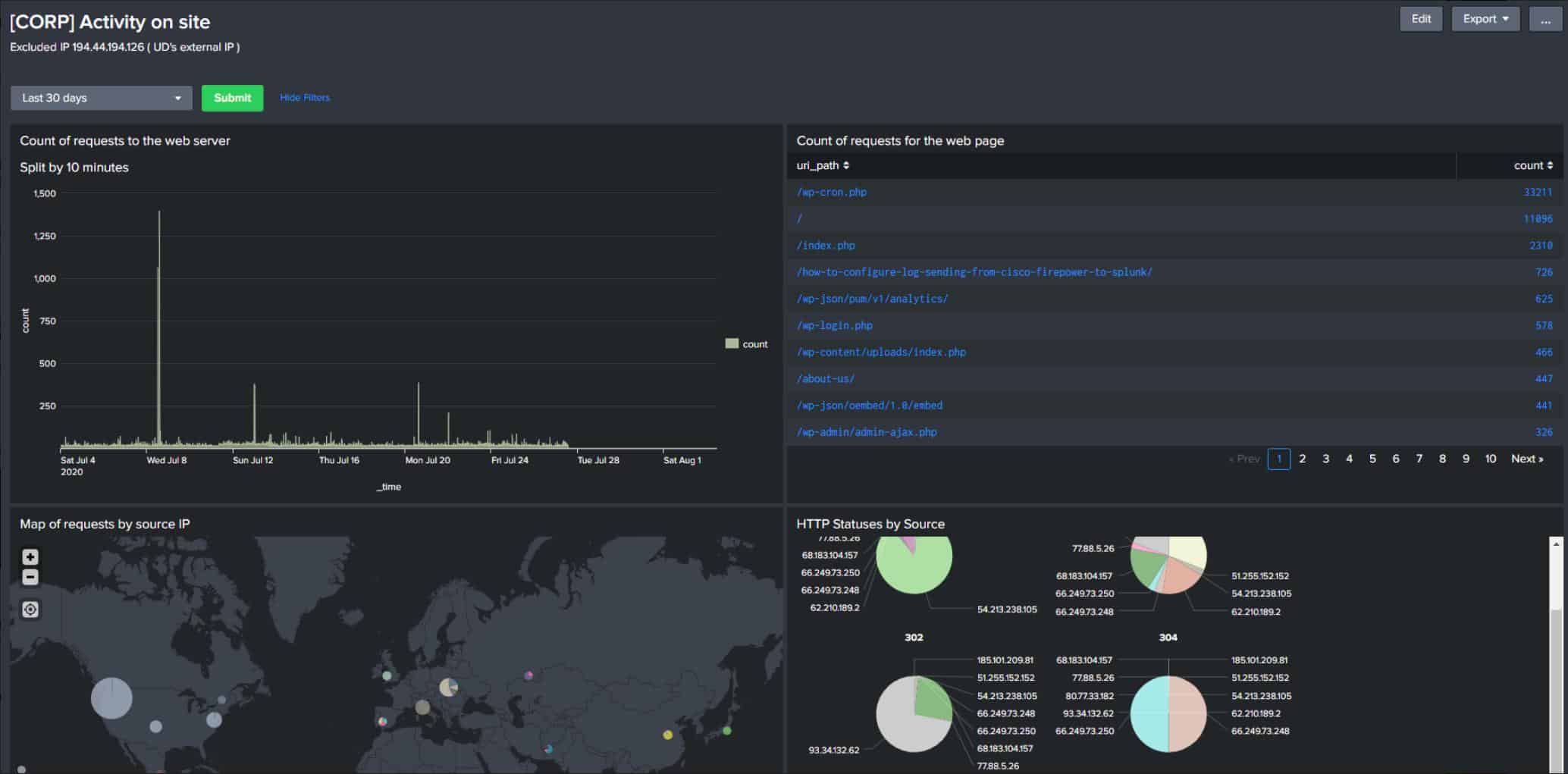
2. Real-time Network Monitoring
To increase visibility over your network you need to be using network monitoring tools. Using a network monitoring tool with a real-time dashboard allows you to keep an eye on network performance and to see when devices are performing poorly or acting suspiciously.
Many tools also come with alerts that will notify you when a security event takes place. Types of tools you can use to monitor your network include everything from hardware monitoring tools to system monitoring tools and log analyzers.
Proactively monitoring your network will enable you to catch cyberattacks early, and help you to take action before unwanted downtime. Network monitoring software is very important to endpoint security because it’s impossible to monitor a network full of devices manually.
3. Employee Training
If you want to make your environment more secure then you need to make your employees become more cyber-conscious. Educating employees about the signs of cyberattacks like DDoS attacks or phishing attempts, and how to respond to those effectively is a must for reducing the risk of damage and downtime.
Employees should also be made aware of general cybersecurity best practices such as: selecting strong passwords, changing passwords regularly, using password managers if recording multiple passwords, not clicking on suspicious email links, locking access to computers when they’re away, and reporting suspected attacks to an administrator.
4. Update Devices Regularly
Regularly updating your devices is a must for keeping them secure. Famous threats like the WannaCry Ransomware could have been prevented if companies were up-to-date with device patching. One of the easiest ways to update your devices continuously is to use patch management software.
Patch management tools allow you to automate the deployment of patches and updates throughout your environment so you can keep every device updated without having to spend hours deploying updates manually.
Here is our list of the best endpoint security systems:
- Guardz EDITOR’S CHOICE This cloud-hosted SaaS security package includes endpoint security alongside data protection and cloud security. Tools include vulnerability scanning, activity monitoring, and Dark Web scanning to protect against malware, intruders, and insider threats. Get a 14-day free trial.
- ThreatLocker (GET DEMO) This cloud based service protects endpoints by preventing all software from running – approved packages are then selectively allowed. Protection for Windows, macOS, and Linux. Access the free demo.
- UnderDefense MAXI MDR (GET DEMO) This is a managed security service that provides cybersecurity experts to either to run a company’s security systems remotely or to provide advice on-demand. Start a free demo.
- CrowdStrike Falcon This security platform offers an on-device unit that performs antivirus functions while also gathering data for a cloud-based threat hunting module. The endpoint unit also implements threat remediation actions instructed by the central security server.
- Bitdefender GravityZone Business Security This AI-based malware detection package also blocks infected websites. Runs on Windows, Windows Server, macOS, and Linux.
- Sophos Intercept X An AI-based malware detection system that has a crowd-sourced threat intelligence feed. Protects Windows and Linux.
The Best Endpoint Security Providers
As cybersecurity strategies have evolved tons of providers have started to offer endpoint security platforms. There are so many tools to choose from that it can be difficult to pick which is best.
In this section, we’re going to look at some of the top solutions on the market that enterprises you can use to keep your devices protected. Please note that the list is not an exhaustive run-down of all cybersecurity solutions, but a quick look at the top providers in the endpoint security segment of the market.
Our methodology for selecting endpoint security tools
We reviewed the market for bandwidth analyzer systems and analyzed the options based on the following criteria:
- Systems to block malware from operating on the endpoint
- A service that scans for security weaknesses
- Patching for operating systems and software
- Methods to control user access to administration privileges
- A system that centralizes event logs for threat hunting
- A free trial or a demo to enable assessment before buying
- Value for money from an endpoint security package that provides several threat blocking functions
1. Guardz (FREE TRIAL)
Guardz is a cloud platform of security services that protects endpoints and cloud storage accounts. The system searches for malware and intrusion and it also scans incoming emails, which are frequently used as a point of entry for attacks.
Key Features:
- Blocks account takeovers
- Scans for malware
- Automated responses
Why do we recommend it?
Guardz scans endpoints, looking for indicators of hacker activity and malware. This package will automatically shut down the threats that it detects, which means that it keeps an IT system safe without any manual intervention by technicians. The package will root out human intruders and malware that includes spyware, adware, keyloggers, ransomware, Trojans, and viruses.
The Guardz system is able to analyze user behavior and spot when it changes. This could indicate an account takeover, which is the typical beginning of an advanced persistent threat. In an APT, a hacker gets long-term access to a company’s network and all of its resources. The use of valid accounts removes the urgency behind the exploration of the system. These attacks can go unnoticed for years and so the ability of Guards to shut down an intruder is a useful protection service.
Account takeover starts with credentials theft and the main avenue for that is the phishing attack. The email scanner in the Guardz package spots phishing emails and removes them from the mailboxes of users. The tool also removes spam, impersonation attempts, and malware.
Who is it recommended for?
Guardz is suitable for all sizes of businesses. The platform is a subscription service with a charge rate per user – the minimum team size is one. A quirk of the Guardz system is that the company will only sell to managed service providers. So, if you already have a deal with an MSP, tell them about Guardz, but if you don’t have one, get one. One way around this requirement is to opt for the managed security service plan from Guardz.
Pros:
- Prevents threats from getting onto a system through emails
- Searches for intruders and malware on endpoints
- Protects email systems and cloud storage systems
Cons:
- Needs to be administered by a managed service provider
If you don’t already have a contract with a managed service provider, Guardz provides a list of recommended MSPs. You could also opt for the Ultimate plan of Guardz, which is a managed service. Sign up for a 14-day free trial of Guardz.
EDITOR'S CHOICE
Guardz is our top pick for an endpoint security system because it provides both preventative measures and live security scanning. The vulnerability manager in the package checks on the external attack service of each endpoint and of the network as a whole. The service recommends configuration changes that will tighten security. The tool watches all activity on each endpoint to establish normal activity per user. It will trigger an alert and response actions if a user account starts behaving differently. This includes the system account, which could be running malware. You can block intruder activity and insider threats with this tool as well. Other security measures include a Dark Web scanner to identify stolen company user credentials.
Download: Start a 14-day FREE Trial
Official Site: https://app.eu.guardz.com/signup
OS: Cloud-based
2. ThreatLocker (GET DEMO)
ThreatLocker provides a different approach to endpoint security. You read in this report about the principle of least privilege earlier in this report – ThreatLocker applies that strategy to software instead of to users. This mechanism removes the need to detect malware and remove it. Instead, by default, all software is blocked from running, which means even if malware gets onto your endpoints, it won’t be able to execute.
Key Features:
- Blocks all software by default
- Allowlisting
- Software ringfencing
- Network security
- Blocks fileless malware
Why do we recommend it?
ThreatLocker prevents all programs from launching on a protected endpoint. Once that baseline is in effect, the administrator lists approved software systems that are allowed to run. This strategy removes the possibility of users installing their own software and it also means that malware can never run.
You assemble an application whitelist, which ThreatLocker calls an allowlist. The software systems on that list are allowed to run – anything that isn’t on the list is permanently disabled. Software controls also extend to rules about what resources each package is allowed to access. This is called “application fencing.”
ThreatLocker applies the same closed security stance to USB ports and the peripheral devices that connect to them. All USB ports are blocked but they can be unlocked by the administrator at the request of a user. This permission will apply to a specific USB device for use by a specific user. This permission can be revoked at any time. This control is intended to block data theft rather than to block malware from getting onto the endpoint because if the stick is infected, that malware will not be able to run on the computer, so it is no threat.
Who is it recommended for?
The ThreatLocker system is easy to implement and it creates a complete block on malware. The package also includes user activity tracking and controls for access to data. The network security feature provides an interface that enables anyone to construct sophisticated defense without any cybersecurity knowledge. This is a particularly good service for small businesses.
Pros:
- Blocks software from running
- Permits whitelisted applications to run
- Controls the resources that software can access
- Can protect cloud platforms as well as site resources
Cons:
- Doesn’t include a full access rights manager
ThreatLocker combines the efficiency of a cloud-based service with the accuracy of an on-board system. Threatlocker offers many other add-on services that can enhance the security of a business by hardening the configurations of endpoints and by gathering worldwide intelligence on current attack campaigns. ThreatLocker is a cloud-based service and it can administer controls on any endpoint anywhere – they don’t all need to be on the same network. It can also apply its Zero Trust application controls on cloud platforms. Access a demo to discover more about the ThreatLocker package.
3. UnderDefense MAXI MDR (GET DEMO)
UnderDefense is a managed security service provider. The company is an outsourced facilities provider, offering to run the security systems of their clients. The group can support an existing security team or replace it completely. UnderDefense technicians work remotely.
Key Features:
- Flexible solution
- Provisioning advice
- Security orchestration, automation, and response
Why do we recommend it?
Under Defense MAXI MDR is a managed detection and response service. This goes a little further than EDR and XDR because it provides the staff to manage security. You can choose your preferred security systems and UnderDefense will advise you on those purchases and set up the software for you.
This isn’t an out-of-the-box service. You decide on the cybersecurity tools that are going to be used to monitor your site and UnderDefense can advise you. The company will also install and configure those tools for you. If you already have cybersecurity software in place, the UnderDefense team will assess it and optimize its settings to improve performance.
Although the UnderDefense team uses third-party security software. The group does have some of its own tools to offer. These include online guides for compliance requirements, risk assessment templates, and a Dark web scanner. These operate for all clients no matter what other cybersecurity systems they choose to use.
Clients can choose to hire the UnderDefense team as consultants for on-demand guidance. Another option is to hire the team to remotely take over all management of the client’s security software.
Who is it recommended for?
This system is suitable for companies that just can’t find the right experts to run a corporate security system. This could be because there just aren’t any experienced cybersecurity consultants looking for work in the neighborhood or it could be that they are just too expensive.
Pros:
- Security experts on call
- A fully staffed remote security operations center
- Flexible plans
- Choose your preferred security software
- Free tools
Cons:
- There is no free trial of the SOC services
UnderDefense offers a free account, which gives access to the Dark Web scanner, compliance guide, and risk assessment template library. Consult with the group to decide on a package of security management services. Start by registering for a free demo.
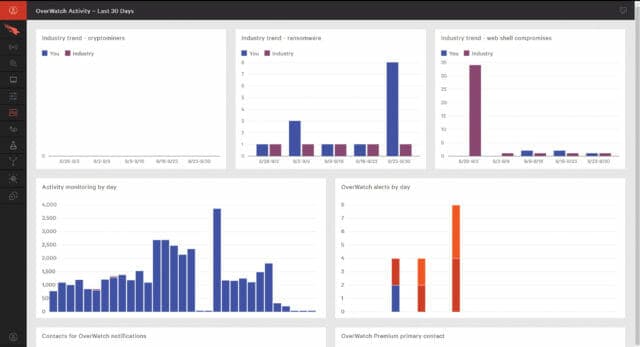
4. CrowdStrike Falcon
CrowdStrike Falcon is a Next-Generation Antivirus (NGAV) and endpoint protection solution that can be used to secure endpoints throughout your network. CrowdStrike Falcon uses threat intelligence, machine learning, and AI to detect known/unknown malware, ransomware, and malware-free threats.
Key Features:
- Package options
- A core antivirus system
- Extensions for threat hunting
Why do we recommend it?
CrowdStrike Falcon is a suite of cybersecurity systems that can all work together. All of those units are based in the cloud, except for one: Falcon Prevent. That module is a standalone antivirus package that needs to be installed on each endpoint. The tool can communicate with other units in the suite but its protection will continue if the endpoint is disconnected from the network.
The platform helps to increase transparency over threats with a process view of cyberattacks. A process tree includes contextual information you can use during the troubleshooting process to remediate a security issue. Detection details are stored for 90 days so that you can dissect security incidents after the event.
To improve your incident response process, CrowdStrike Falcon’s threat intelligence assesses the severity of threats so that you can choose which issues to prioritize. It also provides you with monitoring alerts to notify you about detected threats.
CrowdStrike Falcon is aimed at enterprises that want to secure online and offline endpoints. Prices start at $8.99 (£7.07) per endpoint per month for Falcon Pro. You can start the free trial.
Who is it recommended for?
The Falcon system is designed for use by mid-sized and large organizations. The suite has many options and it can scale up into a comprehensive corporate-wide XDR. However, adding on all of the options gets expensive and the core Prevent unit is a little pricey.
Pros:
- Doesn’t rely on only log files to threat detection, uses process scanning to find threats right away
- Acts as a HIDS and endpoint protection tool all in one
- Can track and alert anomalous behavior over time, improves the longer it monitors the network
- Can install either on-premise or directly into a cloud-based architecture
- Lightweight agents won’t slow down servers or end-user devices
Cons:
- Would benefit from a longer trial period
CrowdStrike Falcon is aimed at enterprises that want to secure online and offline endpoints. Prices start at $8.99 (£7.07) per endpoint per month for Falcon Pro. You can start the free trial.
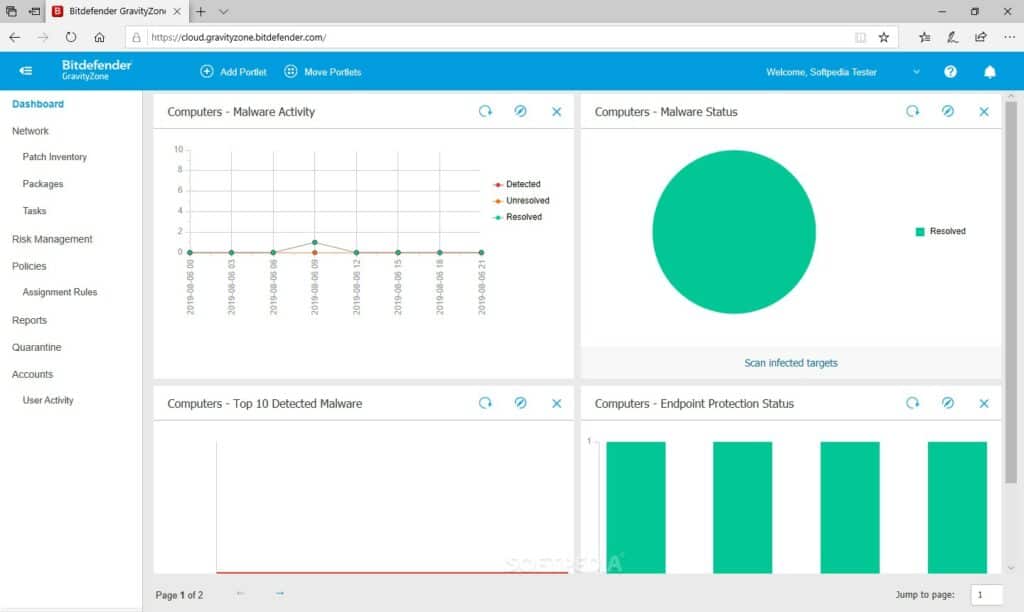
5. Bitdefender GravityZone Business Security
Bitdefender GravityZone Business Security is a top endpoint security provider that leverages AI and machine learning to detect the latest cyber threats. The solution comes with machine learning that uses the Bitdefender Global Protective Network to process malicious file samples gathered from over 500 million endpoints to detect new malware/ransomware attacks.
Key Features:
- Plans for different sizes of business
- Antivirus
- Backup and recovery
Why do we recommend it?
Bitdefender GravityZone Business Security is an anomaly-based antivirus system. This is an on-device software package that protects each endpoint individually. It establishes a baseline of normal activity and then watches all processes on the computer. So, it doesn’t block the download of malware – that’s the job of a firewall.
The solution also protects employees while they browse online by scanning web traffic in real-time and blocking malware from being downloaded. Web filtering lowers the chance of employees being exposed to bogus web pages. There is also an advanced anti-exploit feature that can detect and block exploit attempts including API caller verification and return-oriented-programming.
In addition, a network defense functionality blocks cyberattacks that target vulnerabilities in your network. The network defense feature can stop brute force attacks, password stealers, network exploits, and more. Shutting down these attempts head-on makes sure that users can carry on working unhindered.
Bitdefender GravityZone Business Security is widely regarded as one of the best endpoint security platforms on the market. The price depends on the number of devices and servers you want to support. Prices start from $77.69 (£61.06) for three devices and one server. You can try the free trial.
Who is it recommended for?
The great feature of the GravityZone system is that it also includes a backup and recovery unit. All data is stored and you can choose where to keep your repositories, keeping a local and a remote store. All files are scanned for viruses before going into the repository and on the way out. This is an affordable solution for small businesses.
Pros:
- Simple UI reduces the learning curve and helps users gain insights faster
- Uses both signature-based detection and behavior analysis to identify threats
- Offers disc encryption on top of endpoint protection
- Includes device control options for locking down USB ports
Cons:
- Could use more documentation to help users get started quicker
6. Sophos Intercept X
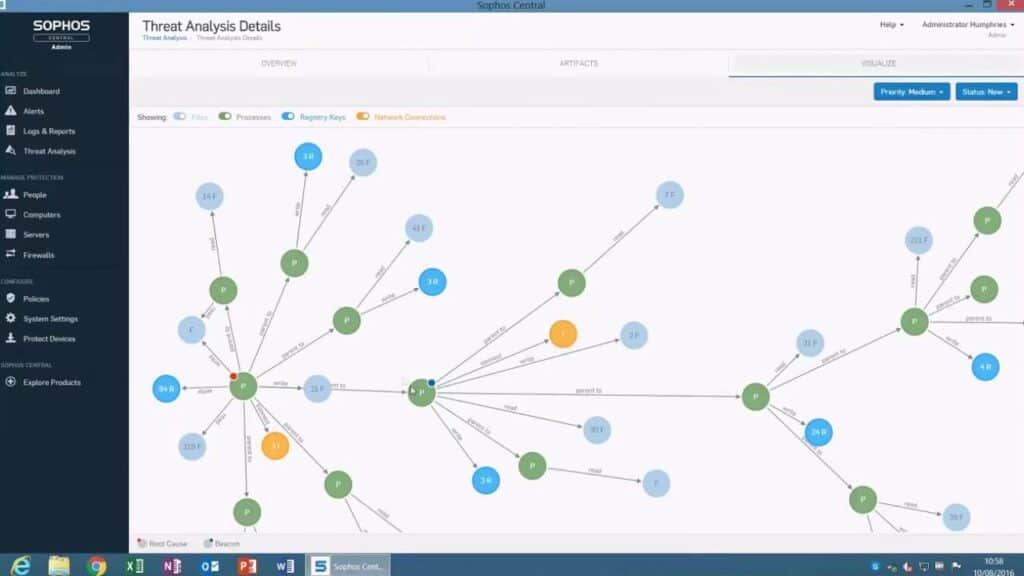
Sophos Intercept X is another highly-regarded endpoint security solution with malware detection and response capabilities. Sophos Intercept X uses machine learning to detect known and unknown malware. The platform takes threat data from over 100 million endpoints through SophosLabs.
Key Features:
- Anomaly-based detection
- Threat intelligence
- Ransomware protection
Why do we recommend it?
Sophos Intercept X was one of the first antivirus systems to use machine learning for anomaly-based threat detection – now this method is common throughout the industry. The antivirus package has special processes for dealing with ransomware, which includes a file protection system called CryptoGuard.
The platform automatically detects threats with machine learning and prioritizes the most important events with the biggest security risk. There are also anti-exploit and anti-ransomware capabilities to limit exposure to threats.
In terms of threat response, Sophos Intercept X can clean up malware and eliminate any malicious code or registry key changes made by the software. The response helps the user to get back to normal operations ASAP, with minimal disruption.
Sophos Intercept X is designed for enterprises that want an advanced threat detection solution to protect endpoints. Sophos Intercept X has a customizable pricing model so you need to contact the sales team for a quote. You can start the 30-day free trial.
Who is it recommended for?
Sophos designs its software to target the mid-sized business market. As well as providing antivirus software, Sophos offers a managed service, called Intercept X MDR. This will be of interest to businesses that don’t have their own cybersecurity experts on site; also companies operating a virtual office will be drawn to this outsourced option.
Pros:
- Leverages machine learning and artificial intelligence to stop new and evolving threats
- Offers protection against file-less malware and ransomware
- Users can implement automation to stop threats, or immediately escalate issues
- Scans external devices as soon as they’re plugged into the computer
Cons:
- Better suited for small to medium-sized companies
Endpoint Security: A Must for IT-Driven Enterprises
If IT plays an integral role in your company, then having a strategy in place to secure endpoints is a must to protect your network from attackers. While adopting endpoint security tools is a good place to start, it’s just the tip of the iceberg, and should be part of a wider strategy of cybersecurity measures and awareness.
To tighten your defenses, your employees need to be aware of all the latest security threats and best practices. Having employees that understand how to secure endpoints, what suspicious activity/threats to look out for, and how to respond in an emergency will enable them to continue their work safely and productively.