What is HIDS or Host Intrusion Detection System?
HIDS is an acronym for host intrusion detection system. It will monitor the computer/network on which it is installed looking for both intrusions and misuse. If found, it will log the suspicious activity and notify the administrator.
HIDS is similar to the use of smart security cameras in your home; if an intruder were to break into your house the camera would start recording and send a real-time alert to your mobile device.
Here is our list of the best HIDS tools:
- SolarWinds Security Event Manager EDITOR’S CHOICE This HIDS collects and collates log messages from around your system and then trawls records for threats, raises alerts, and implements automated responses. Runs on Windows Server but also collects data from Linux, macOS, and Unix systems. Start a 30-day free trial.
- Papertrail (FREE PLAN) Cloud-based log aggregator from SolarWinds in both free and paid versions. Try the free plan.
- ManageEngine EventLog Analyzer (FREE TRIAL) This tool examines log file data from Windows Server or Linux and adds in threat intelligence from other sources. Start a 30-day free trial.
- OSSEC Free log file processor that implements both host-based and network-based detection strategies. Installs on Windows, Linux, Unix, and Mac OS.
- Sagan Free host-based intrusion detection tool that uses both signature and anomaly-based strategies. Can run on Linux, Unix, and Mac OS.
- Splunk Free host-based intrusion detection software with a paid edition that includes network-based methods as well. Installs on Windows, Linux, and Mac OS and there is also a Cloud-based version.
Intrusion detection has become an important protection method for networks in order to combat security weaknesses inherent in any system that includes a human element. No matter how strong your user access policies are, hackers can always get around them by tricking an employee into disclosing access credentials.
Hackers with access can occupy a corporate system for years without being detected. This type of attack is called an Advanced Persistent Threat (APT). IDSs specifically aim to root out APT’s.
A HIDS tool focuses on monitoring log files. Most applications generate log messages and storing these records to files enables you to search through them over time and spot indications of intrusion. One big problem of gathering every log message on your system is that you will end up with a large amount of data. Storing log messages in a systematic manner helps you identify the right file to get data by application and date. So, the first step in getting meaningful information out of your logging system is to organize the file names and directory structure of your log file server.
The next step in implementing a HIDS is to get some automated detection. A HIDS will search through log messages for specific events that look like they may have recorded malicious activity. This is the core of a HIDS tool and the detection method that specifies which records to retrieve is set by policies and a rule base.
Many HIDS allow you to write your own alert generating rules. However, what you are really looking for when you choose a security system is a set of pre-written rules that incorporate the expertise of the security experts that write the software.
A HIDS is only as good as the policies that it provides. You can’t be expected to keep up with all of the latest attack vectors while also dedicating time to the everyday tasks of your job and there isn’t any point in trying to know everything if you can get that expertise provided for you by the HIDS tool.
The importance of log files
The volume of log and event messages can be overwhelming and it is tempting just to ignore them. However, the risk of litigation triggered by data disclosure or the damage that can be done to a business through loss of data means that failing to protect data can now ruin your business.
Security and data protection issues have now become integrated into contract requirements and there are many standards that industries now follow in order to reassure stakeholders and keep the business secure. Compliance to data integrity standards includes requirements for log file maintenance.
Depending on which standard your company implements, you will need to store log files for a number of years. So, log file management has now become an important business requirement. While you are setting up a log server, you might as well integrate security measures into it, and that’s what HIDS does.
Log file security
The maintenance of log file integrity is an essential part of HIDS. Event messages can identify intrusion attempts and so log files are targets for hackers. An intruder can cover his tracks by manipulating log files to remove incriminating records. Therefore, a log server that backs up log files and checks for unauthorized alterations is important for data security standards compliance.
HIDS systems cannot effectively protect the resources of your system if its source information is compromised. The protection of log files also extends to the authentication system of your network. No automated protection system of log files would be able to distinguish between authorized and unauthorized log file access without also monitoring the security of user permissions.
HIDS vs NIDS
Host-based intrusion detection systems are not the only intrusion protection methods. Intrusion detection systems are divided into two categories. HIDS is one of those sectors, the other is network-based intrusion detection systems.
Both HIDS and NIDS examine system messages. This amounts to both looking at log and event messages. However, NIDS also examines packet data as it passes along networks. The rule of thumb that splits the responsibilities of intrusion detection between these two methodologies is that NIDS captures live data for detection and HIDS examines records in files.
The advantage of NIDS is that they offer a faster response than HIDS. As soon as a suspicious event occurs on the network, the NIDS should spot it and raise an alert. However, hackers are sneaky and constantly adjust their methods to evade detection. Some activity patterns only become apparent as malicious when considered in a broader context.
Whether it is better to get a HIDS or a NIDS is not a big issue because really you need both.
Related post: Best NIDS software
Key HIDS attributes
By analyzing historical data on activities, a HIDS is able to spot patterns of activity that occur over time. However, even on mid-sized networks, the volumes of log records generated on a daily basis can be very large, so it is important to pick an efficient sorting and searching tool.
Your HIDS will not be worth using if it is too slow. Remember, that new records are accumulating constantly, so a speedy HIDS can often be better than a very well-presented tool. Smart system administrators prefer to compromise on presentation to get speed. However, a HIDS tool that is both fast and well-presented is the best deal of all.
HIDS and SIEM
You will encounter the term SIEM a lot when you investigate network security systems. This acronym stands for Security Information and Event Management. This is a composite term that evolved by combining Security Information Management (SIM) and Security Event Management (SEM). Security Information Management examines log files, and so it is the same as a HIDS. Security Event Management monitors live data, making it the equivalent of a NIDS. If you implement a hybrid intrusion detection system, you will have created a SIEM.
Intrusion Prevention Systems
As an intrusion detection system, a HIDS is an important element of network protection. However, it doesn’t provide all of the functionality that you need in order to protect your company’s data from theft or damage. You also need to be able to act on the information that an IDS provides.
Threat remediation can be carried out manually. You may have network management tools at your disposal that will assist you in blocking off intruders. However, linking detection and remediation together creates an intrusion prevention system (IPS).
Both intrusion detection and intrusion prevention strategies work on the assumption that no firewall or antivirus system is infallible. IDS is the second line of defense and many IT security experts warn that no one should rely on a strategy of protecting the network at its boundaries because any security system can be undermined by user mistakes or malicious employee activities.
“Intrusion prevention system” is a bit of a misnomer because IPS’ close off security breaches once they have been detected rather than making a system so watertight that no intrusion attempt could possibly occur in the first place.
Advanced Threat Protection
Another term that you might see when addressing advanced persistent threats is ATP. This stands for Advanced Threat Protection. In its basic form, an ATP system is the same as an IDS. However, some ATP providers stress threat intelligence as a defining characteristic of their systems. Threat intelligence is also a part of the definition of an IDS and a SIEM system.
In a HIDS, threat intelligence is based on the rule base of data search terms and system tests that identify malicious activity. This can be provided in the form of coded checks or adjustable rules set as policies. Threat intelligence can also be formulated within an IDS through AI. However, the policy-forming strategies of automated systems can only be as comprehensive as the inference rules hard-wired into them at their creation.
ATP providers stress their central threat awareness services as a defining feature. These services are offered either as an additional subscription to the ATP software or are included in the purchase price. This is an information-sharing element that enables the ATP software provider to distribute new policies and detection rules based on the successful identification of new attack vectors by other organizations. Some HIDS providers include this service and some HIDS are supported by user communities that share new detection policies. However, HIDS providers are not as strong on this threat information distribution element of their services as ATP providers.
HIDS detection methods
Both HIDS and NIDS can be divided into two subcategories according to their detection methods. These are:
- Anomaly-based detection
- Signature-based detection
There is no direct mapping between NIDS and HIDS for either of these two strategies. That is, it cannot be said that NIDS relies more on one of these methods and HIDS is all about the other detection methodology. Both HIDS and NIDS can use either or both of these detection strategies.
A HIDS with a signature-based strategy works in the same way as antivirus systems; a signature-based NIDS operates like a firewall. That is, the signature-based approach looks for intrusion patterns in data. A firewall looks for keywords, packet types, and protocol activity on incoming and outgoing network traffic, while a NIDS performs the same checks on traffic traveling within the network. An antivirus program will look for specific bit patterns or keywords in program files and a HIDS does the same for log files.
An anomaly would be unexpected behavior by a user or process. An example of this would be the same user logging into the network from Los Angeles, Hong Kong, and London all on the same day. Another example would be if a server’s processors suddenly started working hard at 2:00 AM in the morning. An anomaly-based HIDS would look through log files for records of these unusual activities; an anomaly-based NIDS would try to spot these irregularities as they happen.
As with the choice between HIDS and NIDS, the decision on whether to go for signature-based detection or anomaly-based IDSs is solved by going for both.
Checksum Database & HIDS
A method of identifying whether log files have been tampered with lies in checksum databases. The log protection system calculates a number, based on attributes of a file, such as permissions, size, and modifications date it then converts this number as a hash, or by systems such as MD5 or SHA1. The checksum for each file is then stored in a database.
Older log files that are not still being added to shouldn’t change at all. If they are altered intentionally in an authorized manner, this should be done through the SIEM system’s data access viewer. In that case, on updating the file, the SIEM system would update the stored value for that file in the checksum database.
Periodic recalculations of the checksums of files in storage, compared to the relevant entries in the checksum database, will indicate whether a file has been altered without authorization. In such an event, the SIEM system will restore the original version of the file from a backup version.
Recommended HIDS tools
You can narrow down your search for a host-based intrusion detection software by reading through our recommendations. This list represents the best of breed for each aspect of a HIDS.
You will find free tools in the list, some of which have very poor user interfaces, but made it onto the list because they have very fast data processing speeds. You will also find tools on the list that include general log file management procedures and were specifically written to comply with well-known data security standards. Other tools are comprehensive and give you everything you need in a HIDS both in the backend and in the interface.
Our methodology for selecting a host-based instruction detection package
We reviewed the market for host-based intrusion detection systems and analyzed the options based on the following criteria:
- A package that can collect event data from multiple devices connected to a network
- A consolidator that creates a standardized pool of source data
- A threat detection strategy
- A system of triage to speed up the detection
- An alerting mechanism that draws attention to live threats
- A free trial for a paid system or a tool that is free to use
- A paid system that is worth the money or a free tool that provides meaningful protection
1. SolarWinds Security Event Manager (FREE TRIAL)
SolarWinds has created a HIDS that has automated remediation capabilities, making this an intrusion prevention system, the Security Event Manager. The tool includes compliance audit reports to help you keep on track with PCI DSS, SOX, HIPAA, ISO, NCUA, FISMA, FERPA, GLBA, NERC CIP, GPG13, and DISA STIG.
Key Features:
- On-Premises Package: Deployed on-site for full control over the security environment.
- Log Collection and Consolidation: Collects and consolidates logs from multiple sources for comprehensive monitoring.
- Event Correlation: Correlates events across systems to detect complex threats.
- Automated Threat Detection: Automatically detects and responds to security threats.
- Manual Analysis Option: Allows for detailed manual analysis of logs and events.
Why do we recommend it?
SolarWinds Security Event Manager is a SIEM and log management package. This combination provides the classic HIDS configuration. However, the toll is also able to collect SNMP reports, which gives it live network data as well. This means that the tool is also a network-based intrusion detection system (NIDS).
Log file protection features that are built into this utility include encryption in transit and storage, and folder and file checksum monitoring. You can forward log messages and backup or archive entire folders and files. So, the log file management and integrity features of this tool are exceptional.
The tool will constantly monitor your log files, including those that are still open for new records. You don’t have to issue queries manually, because the Security Event Manager will raise alerts automatically whenever a warning condition is detected. There is also an analysis tool within the package that enables you to perform manual checks on data integrity and spot intrusion with a human eye.
Who is it recommended for?
This package is able to collect and manage logs from many devices simultaneously. It has the capacity to cater to very large companies. Thus, this package would be too much for small businesses and is aimed at mid-sized and large companies. Multi-site companies would be particularly interested in the solution.
Pros:
- Enterprise-Focused HIDS: Offers extensive integrations, making it suitable for large enterprises.
- Easy Log Filtering: Simplifies log filtering without the need for a custom query language.
- Quick Setup: Templates enable quick deployment with minimal customization.
- Historical Analysis: Provides tools for historical analysis to detect anomalous behavior efficiently.
Cons:
- Learning Curve: The advanced features and capabilities require time and effort to master.
Although this software will only install on Windows Server, it will collect log data from other operating systems, including Linux and Unix. You can get a 30-day free trial of the SolarWinds Security Event Manager.
EDITOR'S CHOICE
SolarWinds Security Event Manager is our top pick for a host-based intrusion detection system because it runs on your own server, giving you total control and privacy over threat hunting actions. You can let this package collect event data and analyze it without human intervention and get on with other tasks until a threat is detected and requires your attention. Set up the system to notify a technician to get threats analyzed manually or let it roll on automatically to threat responses.
Download: Get a 30-day free trial
Official Site: https://www.solarwinds.com/security-event-manager/registration
OS: Windows Server
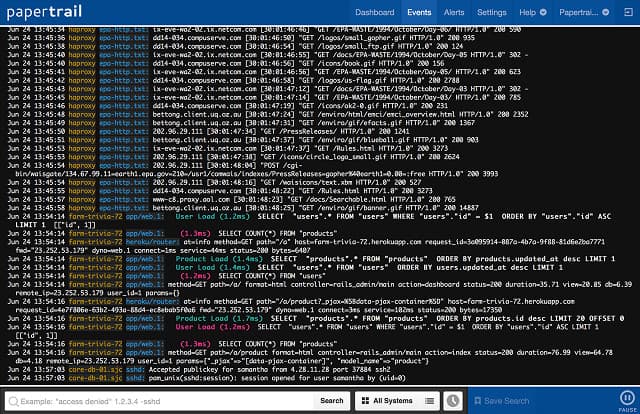
2. Papertrail (FREE PLAN)
SolarWinds runs a Cloud-based log management service, called Papertrail. This is a log aggregator that centralizes your log file storage. Papertrail can manage Windows event logs, Syslog messages, Apache server log files, Ruby on Rails program messages, and router and firewall notifications. Messages can be viewed live in the system dashboard as they travel to log files. As well as managing log files, the tool includes analytical support utilities.
Key Features:
- Cloud-Based: Offers a cloud-based solution for log management and storage.
- Log Server and Consolidator: Centralizes log file storage from various sources.
- Anomaly and Signature-Based Detection: Utilizes both anomaly and signature-based methods for comprehensive monitoring.
- Log Backup and Archiving: Automatically backs up and archives log files for compliance and security.
Why do we recommend it?
Papertrail is a log manager that collects log messages in many different formats and then standardizes them. The tool is based in the cloud and a subscription includes storage space for your log files. The Papertail system live-tails messages for analysis in a data viewer. Save and automatically implement your own security scans.
Log data is encrypted both in transit and at rest and access to log files is guarded by authentication. Your files are held on the Papertrail server and SolarWinds takes care of backups and archiving, so you can save money on buying, managing, and maintaining file servers.
Papertrail employs both anomaly and signature-based detection methods and you benefit from policy updates learned from threats aimed at other Papertrail customers. You can also assemble your own detection rules.
Who is it recommended for?
This system is important for businesses that need to manage log files for compliance auditing. The tool is able to archive older files and then revive them for access when needed. The service lets you construct your own performance and security monitoring tool, thanks to its customizable alerting mechanism.
Pros:
- Scalable Solution: The cloud-hosted service allows easy scaling of log collection without additional infrastructure costs.
- Data Encryption: Encrypts data both in transit and at rest to ensure security.
- Automatic Backup and Archiving: Automatically handles log backups and archiving, reducing administrative burden.
- Comprehensive Detection: Uses both signature-based and anomaly detection for thorough monitoring.
- Free Version Available: Includes a free plan, making it accessible for small businesses and startups.
Cons:
- Learning Curve: Requires time to fully explore and utilize all features and options.
SolarWinds offers Papertrail on subscription with a range of plans, the lowest of which is free.
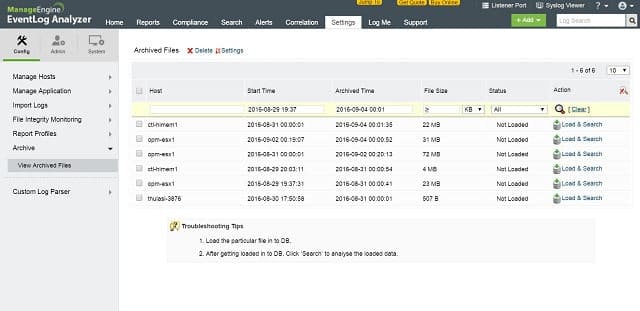
3. ManageEngine EventLog Analyzer (FREE TRIAL)
ManageEngine EventLog Analyser is both a HIDS and a NIDS. The log management module collects and stores Syslog and SNMP messages. Metadata about each Syslog message is also stored.
Key Features:
- On-Premises for Windows and Linux: Available for deployment on Windows Server and Linux systems.
- Log Collection and Analysis: Collects and analyzes logs from various sources, including Syslog and SNMP messages.
- Compliance Auditing: Provides auditing tools for compliance with standards such as PCI DSS, FISMA, and HIPAA.
Why do we recommend it?
ManageEngine EventLog Analyzer is a major rival to SolarWinds Security Event Manager. This system collects, consolidates, and files log messages as well as performing security scans. Like the SolarWinds system, this tool also collects live network activity statistics, making it a NIIDS as well as a HIDS.
Log files are protected by both compression and encryption and access is protected by authentication. Backups can be restored automatically when the analyzer detects log file tampering.
The dashboard is customizable and different screens and features can be allocated to different user groups. Reporting includes compliance audits for PCI DSS, FISMA, and HIPAA among others. You can also activate system compliance alerts.
Who is it recommended for?
This tool is offered as a SaaS platform or as a software package for Windows Server or Linux. There is a Free edition, but that is limited to log collection from five sources. The paid package is sized to be accessible for SMEs – larger companies pay extra for capacity expansion.
Pros:
- Customizable Dashboards: Tailor dashboards for different user groups, enhancing usability for network operation centers.
- Multiple Alert Channels: Sends alerts via SMS, email, or app integration to ensure timely notifications.
- Anomaly Detection: Uses anomaly detection to help technicians identify and respond to unusual activities.
- File Integrity Monitoring: Monitors file integrity to detect and prevent ransomware, data theft, and unauthorized access.
- Forensic Log Audits: Offers forensic log audit features to generate reports for legal cases or investigations.
Cons:
- Search Functionality: The search function could be improved, particularly around using operator functions like wildcards.
The EventLog Analyzer runs on Windows or Linux and can integrate with ManageEngine’s infrastructure management tools. A Free Edition of this tool is available allowing up to 5 log sources only. You can also download a 30-day free trial.
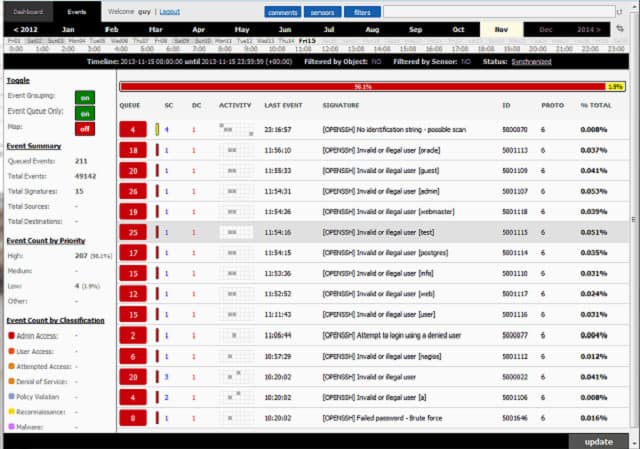
4. OSSEC
OSSEC is a free open source HIDS produced by Trend Micro. It also includes system monitoring features that are normally attributed to NIDSs. This is a very effective processor of log file data, but it doesn’t come with a user interface. Most users put Kibana or Graylog on the front of OSSEC.
Key Features:
- Free Tool: Completely free and open-source, making it accessible for any organization.
- NIDS Features: Includes system monitoring features typical of Network Intrusion Detection Systems (NIDS).
- Customizable Interface: Requires third-party tools like Kibana or Graylog for a user interface, allowing customization.
Why do we recommend it?
OSSEC is a long-running free, open-source HIDS system. This is a highly-respected package but its management has become a little complicated in recent years and now there are three official versions to choose from. We recommend prioritizing the OSSEC+ edition, which is an improvement on OSSEC but it is still free.
This tool will organize your log file storage and protect files from tampering. Intrusion detection is anomaly-based and is implemented through “policies.” These rule sets can be acquired for free from the user community.
The OSSEC software can be installed on Windows, Linux, Unix, or Mac OS. It monitors Windows event logs and also the registry. It will guard the root account on Linux, Unix, and Mac OS. Support is available for free from the active user community, or you can pay Trend Micro for a professional support package.
Who is it recommended for?
OSSEC is suitable for all types of businesses, thanks to its different editions. The basic OSSEC is being overshadowed by the enhanced version, called OSSEC+, which is free and is the most attractive package of the three options. Large businesses that need professional support will opt for the paid Atomic Enterprise OSSEC.
Pros:
- Multi-Platform Support: Compatible with Windows, Linux, Unix, and Mac OS.
- Combination SIEM and HIDS: Functions as both a Security Information and Event Management (SIEM) tool and a Host-based Intrusion Detection System (HIDS).
- Customizable and Visual: Highly customizable with the ability to integrate visual interfaces through additional tools.
- Community Support: Active user community provides free support and templates for quick setup.
Cons:
- Requires Additional Tools: Needs secondary tools like Graylog and Kibana for enhanced analysis and user interface.
- No Paid Support: The open-source version lacks professional paid support, which might be needed for larger enterprises.
5. Sagan
Sagan is a free HIDS that installs on Unix, Linux, and Mac OS. It is capable of collecting Windows event log messages, even though it doesn’t run on Windows. You can distribute the processing of Sagan to keep the overhead on your log server’s CPU light. The system uses both anomaly and signature-based detection methods.
Key Features:
- Free to Use: Completely free and open-source, accessible for any organization.
- Anomaly and Signature-Based Detection: Uses both methods to detect intrusions effectively.
- Automated Response Rules: Allows setting actions to occur automatically when an intrusion is detected.
Why do we recommend it?
The Sagan open-source core is a HIDS system that analyzes log files for security breaches. There are paid editions available from Quadrant Information Security, which owns the Sagan brand. This is a rival to OSSEC but is at a marketing disadvantage because it isn’t available for Windows.
You can set actions to occur automatically when an intrusion is detected. The tool has a few unique features that some of the more prominent HIDS lack. These include an IP geolocation facility that will enable you to raise alerts when activities of different IP addresses are traced to the same geographical source. The tool also allows you to set time-related rules to trigger alerts. The system was written to be compatible with Snort, which is a network detection system, giving Saga NIDS capabilities when combined with a network data collector. Sagan includes a script execution facility that makes this an IPS.
Who is it recommended for?
Sagan Core is free to use but you will find it harder to set up and manage than the new OSSEC+ package. Large businesses should look at the Sagan Security Analytics Platform from Quadrant, which is a paid tool and comes with a professional support package.
Pros:
- Free Log Analysis Tool: Provides comprehensive log analysis capabilities without cost.
- Compatibility with Open-Source Tools: Works well with other open-source tools like Zeek and Snort for enhanced security.
- IP Geolocation: Features an IP address locator that provides geopolitical information on addresses.
Cons:
- No Windows Support: Cannot be installed on Windows operating systems, limiting its compatibility.
- Primarily a HIDS Tool: More focused on host-based intrusion detection rather than traditional IDS.
- Steep Learning Curve: Requires significant effort to set up and manage, especially for new users.
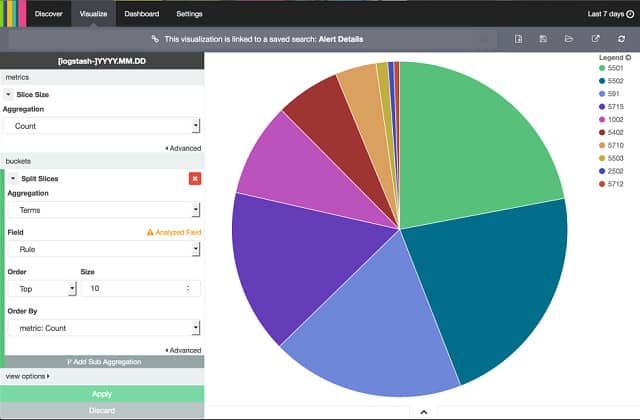
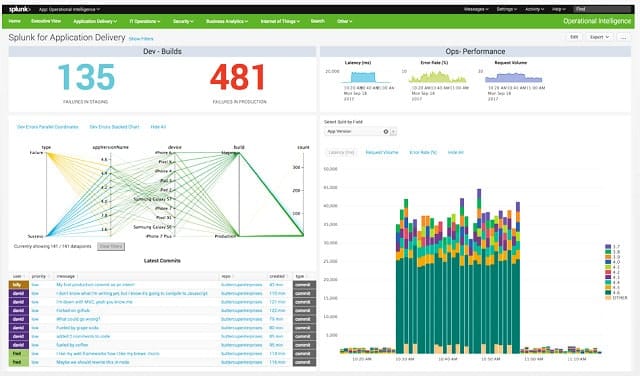
6. Splunk
Splunk offers both HIDS and NIDS features. The base package of this tool is free to use and it doesn’t include any network-based data alerts, so it is a pure HIDS. If you are looking for an anomaly-based HIDS, this is a very good option. The top edition of Splunk is called Splunk Enterprise and there is a Software-as-a-Service (SaaS) version of this, which is called Splunk Cloud. Between the Free version and the Enterprise edition sits Splunk Light, which has some service limitations. There is also an online version of Splunk Light, called Splunk Light Cloud.
Key Features:
- Data Analysis Tool: Provides powerful data analysis capabilities for various use cases.
- SIEM Add-On: Includes a SIEM service that adds security functions to the base data analyzer.
- On-Premises or Cloud: Available as on-premises software or as a SaaS solution.
Why do we recommend it?
Splunk is a data analysis package and by itself isn’t a security tool. However, Splunk, Inc has created a security platform around the data analyzer. This security system is ever-expanding with a SIEM service, which includes HIDS functions. You can also investigate the system performance monitoring options from Splunk.
Splunk has workflow automation features that make it an intrusion prevention system. This module is called the Adaptive Operations Framework and it links automated scripts to trigger alerts. The automation of solutions to detected problems is only available with the higher-paid options of Splunk.
The dashboard of Splunk is very attractive with data visualizations such as line graphs and pie charts. The system includes a data analyzer in all of the editions of Splunk. This enables you to view records, summarize, sort, and search them, and get them represented in graphs.
Who is it recommended for?
Splunk is a major data analyzer. However, this is a paid tool and each of the pre-written analysis packages, such as Splunk Enterprise Security make the tool more expensive. Small businesses will need to keep an eye on the add-on prices before settling on this tool.
Pros:
- Behavior Analysis: Utilizes behavior analysis to detect threats not found through logs alone.
- Excellent User Interface: Features highly visual and customizable dashboards with data visualizations like graphs and charts.
- Event Prioritization: Simplifies the prioritization of events for better incident response.
- Enterprise Focused: Designed for large enterprises with robust security and data analysis needs.
- Cross-Platform: Available for both Linux and Windows environments.
Cons:
- Pricing: Requires contacting sales for pricing, which can be cost-prohibitive for small businesses.
- Learning Curve: Uses a custom Search Processing Language (SPL) for queries, which can be challenging to learn.
- More Suited for Large Enterprises: The cost and complexity make it less ideal for small businesses.
All levels of Splunk run on Windows, Linux, and macOS. You can get a 30-day free trial of Splunk Light, a 60-day free trial of Splunk Enterprise, and a 15-day free trial of Splunk Cloud.
Selecting a HIDS
There are so many log management tools with analysis capabilities available on the market that you could spend a very long time assessing all of your HIDS options. With the list in this guide, you now have a lot of the research done and the next step is to focus on those tools that run on the operating system of your server. If you want to use Cloud-based services, then Papertrail and Splunk Cloud should interest you most.
Fortunately, all of the tools in our list are either free to use or are available on free trials, so you can install a couple of candidates to run them through their paces without any financial risk.
Do you currently operate a HIDS? Which system did you opt for? Do you think it is important to pay for a tool or are you happy using a free utility? Leave a message in the Comments section below and share your experiences with the community.
Host-Based IDS FAQs
What is the purpose of file integrity monitoring?
File integrity monitoring is concerned with unauthorized changes to important system files. If a file is changed through a valid process or by a permitted user, the FIM will update its validity records for that file – which is usually a checksum. If a file has been changed without authorization, the FIM will restore its original version from a backup.
What is the advantage of a host-based IDS?
A host-based IDS keeps records of all events and preserves those records for future examination. While traditional security systems see intrusion blocking as their only task, HIDS adds the ability to identify all actions performed by an intruder to its responsibilities. The existence of activity records makes it possible to repair damage and deal with possible data leaks.
Image: IT Security from Pixabay. Public Domain.