Managing event logs effectively is essential for maintaining security, performance, and compliance across modern IT systems. These logs provide detailed visibility into system activity, network behaviour, and potential security issues, making them a key resource for troubleshooting, auditing, and threat detection.
As organisations grow and adopt remote and distributed working environments, log data is generated across a wide range of endpoints, servers, and network devices. This has made traditional, decentralised approaches to log handling increasingly difficult to manage at scale.
Here is our list of the best remote event log management software:
- ManageEngine EventLog Analyzer EDITOR’S CHOICE An on-premises log management system that provides audit trails for data protection standards compliance. Runs on Windows Server and Linux. Start a 30-day free trial.
- ManageEngine Log360 (FREE TRIAL) A SIEM package that includes a log collection and management service with automated and manual data analysis tools. Runs on Windows Server. Start a 30-day free trial.
- Paessler PRTG Log Monitor (FREE TRIAL) An all-in-one network, server, and applications monitor that can collect event log messages from any site.
- Datadog Log Collection & Management A SaaS log manager that can receive and file event log messages and works well in combination with the Datadog Ingest for archiving.
- SolarWinds Security Event Manager Log-based SIEM tool that has strong log file management features. The event log management services in this tool make it a good option for those requiring record storage for data standards compliance.
- Logstash A free data gathering tool that forms part of the Elastic Stack (ELK).
- Sematext Logs A hosted implementation of ELK with a highly customized interpretation of Kibana. It can be subscribed to just for log management.
Remote event log management solutions address this challenge by enabling organisations to collect and analyse logs from multiple sources in a centralised platform. This consolidation improves visibility across the entire infrastructure and supports faster investigation and resolution of issues. Many log management tools also include automated collection and real-time monitoring capabilities to ensure continuous oversight of system activity.
In addition to operational benefits, these tools are also important for meeting regulatory requirements. Standards such as HIPAA, PCI DSS, and GDPR often require organisations to retain and monitor log data for compliance purposes. Advanced analytics features further support the detection of anomalies, security threats, and policy violations.
This guide explores the importance of remote event log management and reviews leading tools designed to handle logs in distributed environments. It compares solutions based on usability, scalability, security features, and integration capabilities, helping organisations choose the most effective platform for centralising and analysing event logs across their IT infrastructure.
Event log management
Log files are also important for data security compliance standards. You need to capture and store all log messages, including event logs, in order to prove compliance. Not only do you need to store those messages, but you need to be able to make them available for searches by a compliance auditor at a moment’s notice.
Event log management involves more than just capturing and filing event log messages. You also need to be able to retain those messages for long periods – the exact retention period depends on the data security standard that you are implementing.
A standard commercial Windows-based system generates a lot of event messages each day. Storing these messages results in a large volume of data. So, you also need to be able to archive older files, while making it possible to bring them back to current storage on demand. The event log manager you choose should include searching and viewing feature and also be able to rotate logs so each file is of a manageable size.
The event log manager should have a meaningful strategy on log file storage structures and file naming conventions to make the Event logs from a particular part of the system on a specific day easy to locate.
The Best Remote Event Log Management Software
Our methodology for selecting event log management software
We reviewed the market for remote event log management systems and analyzed tools based on the following criteria:
- Opportunity to consolidate event logs from multiple sites
- Connection security for internet-based data transfers
- Logfile management
- Log viewer
- Analysis features
- A free trial or a demo service for a no-cost assessment period
- Good value for money, represented by an efficient, time-saving log management tool that is reasonably priced
With these selection criteria in mind, we have identified competent event log collectors that can centralize the management of log files
1. ManageEngine EventLog Analyzer (FREE TRIAL)
ManageEngine EventLog Analyzer is a log management system that provides data collectors, a log server, a consolidator, and a filing system. The package is able to merge records written in different formats, which include Windows Events and Syslog. Arriving messages are displayed in the console of EventLog Analyzer and log records can also be read back into the data viewer of the dashboard from files.
Key Features:
- Log Consolidation: Centralizes and merges different log formats for simplified management.
- Insightful Analysis: Offers statistical tools for in-depth log examination and understanding.
- Comprehensive Analyzer: Equipped with tools for detailed log data analysis, enhancing security insights.
Why do we recommend it?
ManageEngine EventLog Analyzer is a close competitor to the SolarWinds tool. It is able to collect Windows Events and Syslog messages from around the network and from cloud platforms. The service is able to accept logs sent from software packages and it will convert all logs into a standard format for searching and storing.
The data viewer in the package includes analytical features, such as search, group, and sort. This supports the manual analysis of data. The package also includes automated analysis in the form of statistical data, such as message arrival rates per type and source. The package includes templates that provide prewritten threat detection rules.
The identification of a problem or a threat triggers alerts. These can be forwarded as emails, SMS messages, or posts to PagerDuty or Slack. This enables the support team to get on with other tasks, leaving the EventLogAnalyzer to monitor standard activity.
There are also templates in the package that produce compliance reports from the collected log data.
Who is it recommended for?
Two editions of this system make it suitable for a mid-size business with a single LAN and for a large company with a WAN. There is also a Free edition that is limited to collecting logs from five sources. The software installs on Windows Server or Linux and it is also available as a SaaS package.
Pros:
- Compliance Assistance: Facilitates meeting regulatory standards with predefined reporting templates.
- Secure Audit Trails: Maintains an accurate and secure log of all network activities for auditing purposes.
- Effective Log Management: Ensures efficient log collection, storage, and analysis for enhanced operational integrity.
- Real-Time Monitoring: Displays log messages live for immediate insight into network health and security.
- Historical Trend Analysis: Utilizes historical data to identify patterns and potential security threats.
Cons:
- No Cloud Solution: Lacks a cloud-based version, limiting flexibility in deployment options.
ManageEngine EventLog Analyzer installs on Windows Server and Linux. It isn’t limited to collecting logs from its host, so if you run the package on Windows Server, you can also collect logs from Linux systems across the network. You can get a 30-day free trial of the EventLog Analyzer.
EDITOR'S CHOICE
ManageEngine EventLog Analyzer is our leading choice for remote event log management, offering a comprehensive platform that supports distributed and remote systems with ease. Administrators benefit from a centralized interface that securely collects logs from servers, devices, and applications, giving complete visibility into network activity across the organization. Advanced log analysis is a standout feature, allowing IT teams to correlate events, identify patterns, troubleshoot issues, and proactively manage security. Real-time monitoring provides immediate alerts for suspicious activity or potential threats, helping teams respond quickly and reduce risk. Compliance is made simpler through automation, supporting standards such as HIPAA, GDPR, and PCI DSS by handling log collection, retention, and reporting efficiently. Customizable dashboards and built-in reports give administrators actionable insights and an overview of performance metrics without manual effort. EventLog Analyzer also offers powerful search, filtering, and auditing capabilities, ensuring that even distributed or remote systems are properly monitored and protected. Its combination of visibility, security, and workflow flexibility makes it a reliable solution for organizations seeking effective remote event log management.
Download: Get a 30-day FREE Trial
Official Site: https://www.manageengine.com/products/eventlog/download-free.html
OS: Windows Server or Linux
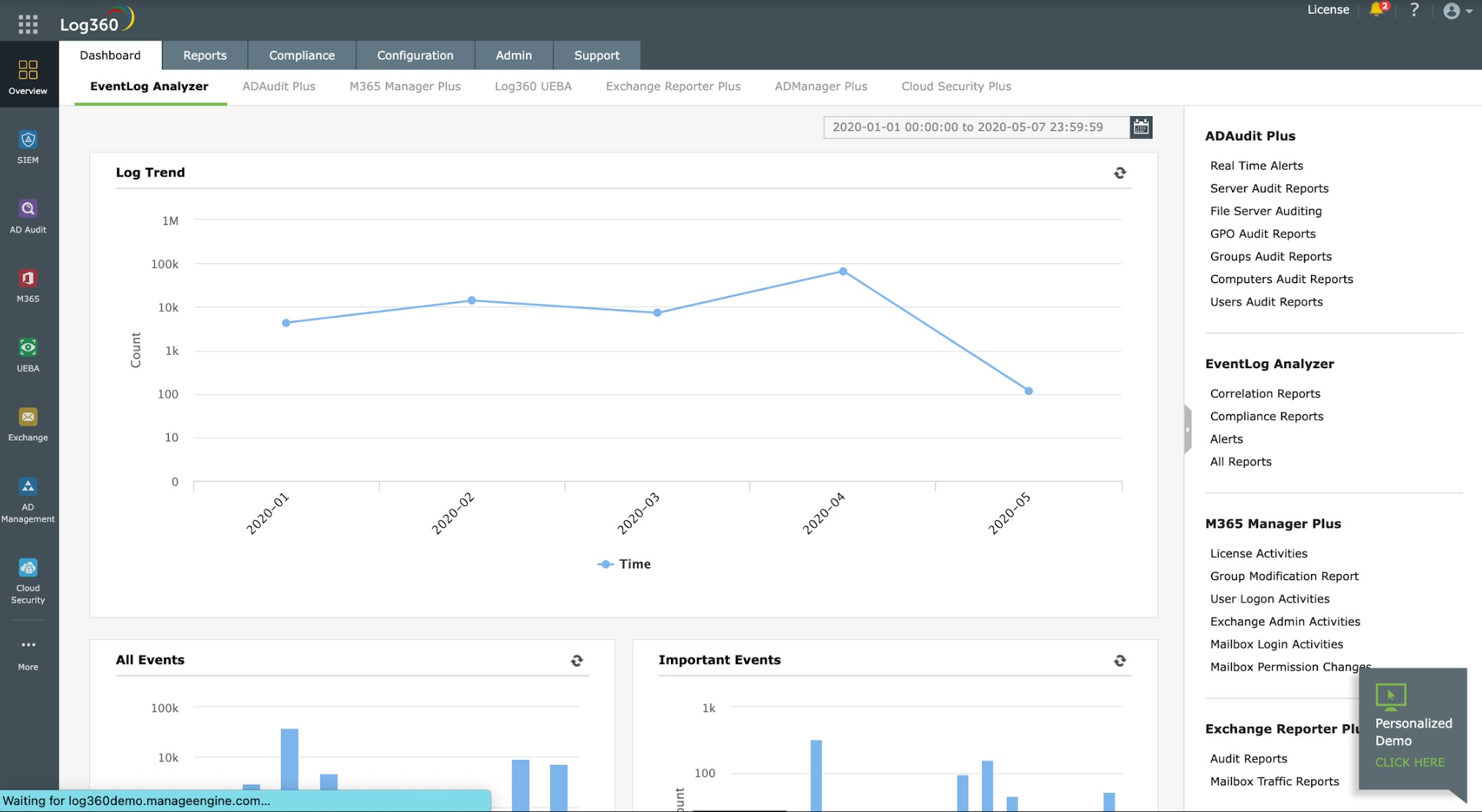
2. ManageEngine Log360 (FREE TRIAL)
ManageEngine Log360 is a security information and event management (SIEM) package that focuses on detecting intrusion on a network and its endpoints. The tool performs this task by gathering and consolidating log messages from around the network. So, as well as a security tool, this package provides a log management system.
Key Features:
- Unified Log Management: Centralized log collection and analysis for comprehensive network surveillance.
- Advanced Analytics: Utilizes statistical methods to dissect data, enhancing threat identification.
- Proactive Threat Hunting: Employs sophisticated mechanisms to detect and alert on potential security breaches.
Why do we recommend it?
ManageEngine Log360 is a super bundle of five ManageEngine modules that are also available individually. These are ADAudit Plus, EventLog Analyzer, M365 Manager Plus, Exchange Reporter Plus, and Cloud Security Plus. The inclusion of EventLog Analyzer gives the package log management capabilities.
The Log360 system is very similar to ManageEngine’s EventLog Analyzer (above) except that it also takes live network activity data as an input. The log collector can interact with applications to extract activity data as well as picking up the standard Windows Events and Syslog messages that circulate around your network.
The package includes prewritten searches that automatically sift through arriving data. It is also possible to create your own threat detection rules. Searches are enhanced by a threat intelligence feed, which enables the threat detection system to focus on indicators of current hacker attack campaigns.
Remediation automation is implemented by forwarding notifications through service desk tools, such as ManageEngine ServiceDesk Plus, Jira, and Kayoko. This lets your ticket management system’s routing rules deliver threat notifications through to the relevant specialist technician.
Who is it recommended for?
This is a very large package and so, is commensurately expensive. Not all businesses will need all of the features in the package. For example, if you don’t use Microsoft 365 or Exchange Server, you would be better off just getting the EventLog Analyzer by itself.
Pros:
- Comprehensive Security Suite: Combines multiple ManageEngine tools for a robust security and log management solution.
- Customizable Threat Detection: Offers flexibility in crafting threat detection rules, bolstered by a threat intelligence feed.
- Seamless Service Desk Integration: Automates alert forwarding to service desk tools, streamlining the remediation process.
- Rich Data Insight: Extracts and analyzes performance data from applications, aiding in informed decision-making.
Cons:
- Limited Platform Compatibility: Excludes support for Linux environments, restricting its applicability.
ManageEngine Log360 will run on Windows Server. However, it can also collect logs from Linux computers across the network. You can examine the Log360 system with a 30-day free trial.
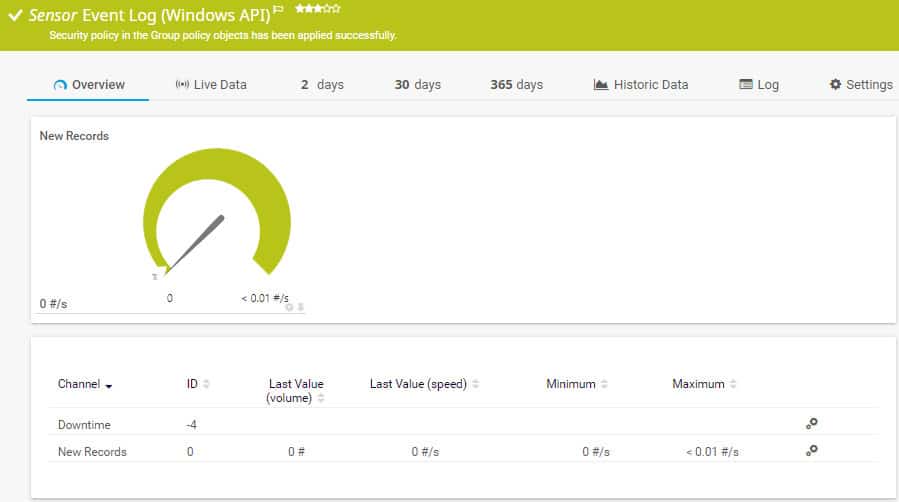
3. Paessler PRTG Log Monitoring (FREE TRIAL)
Paessler PRTG is a collection of monitoring utilities. Each of them is called a “sensor”. One of the sensors in the package is called the Syslog Receiver Log Sensor. This tool collects event log messages and files them. The service can store messages and access them for up to 365 days.
Key Features:
- Multi-Site Collection: Gathers logs from various platforms and locations.
- Real-Time Statistics: Tracks log arrival rates for immediate insights.
- Complimentary Plan: Includes a free option for basic monitoring needs.
Why do we recommend it?
Paessler PRTG Log Monitoring is implemented as a WMI Event Log Sensor and a Syslog Receiver Sensor. While you can collect and store Syslog messages, the WMI sensor only records statistics about the throughput of Windows Events. A direct Windows Event sensor was deprecated due to enhanced security procedures in the Windows Events mechanism.
It is possible to watch Syslog messages as they arrive. Records can be loaded into a viewer in the PRTG dashboard for searching and sorting. This facility is ideal for those who need to provide access to records to a compliance auditor. The system doesn’t include an archive mechanism.
A WMI Event Log Sensor calculates statistics about Windows Event generation, but it doesn’t collect Windows Event messages. It is possible to set a threshold of throughput that acts as a warning level, triggering an alert.
Who is it recommended for?
Since the deprecation of the Event Log sensor, you can only monitor event message generation rather than collect them. However, as a workaround, you could channel your Windows Evernts through a forwarder that will convert them into Syslog messages, then the PRTG system will be able to receive them.
Pros:
- Customizable Monitoring: Offers adaptable sensors for tailored monitoring solutions.
- Generous Free Offering: Supports comprehensive monitoring with an allowance of up to 100 sensors.
- Flexible Deployment: Available in both on-premises and cloud configurations.
- Holistic Monitoring: Ideal for businesses seeking a wide-angle view of their IT ecosystem.
Cons:
- Steep Learning Curve: The platform’s depth and breadth may require significant time to master.
Paessler PRTG is able to include cloud servers and remote sites in its monitoring system. This makes it ideal for centralizing all event log records for a multi-site business. Paessler PRTG is charged according to the number of sensors that are activated. The system is free for up to 100 sensors. You can get a 30-day free trial of PRTG with no limit on active sensors.
4. Datadog Log Collection & Management
Datadog is a cloud-based system monitoring service that is marketed in a series of modules. The service includes two products that are excellent choices for remote event log management. These are Ingest, which collects the log messages and files them, and Retain or Rehydrate, which manages the archives. The Ingest system includes a “live tail” feature, which displays all log messages in the console as they arrive.
Key Features:
- Comprehensive Collection: Centralized log collection across multiple platforms and formats.
- Live Monitoring: Features a “live tail” for real-time log viewing.
- Archiving Capability: Offers modules for efficient log storage and retrieval.
- Application Insight: Specializes in capturing detailed application log data.
Why do we recommend it?
Datadog Log Collection and Management is implemented in two modules. The first of these is called Ingest, which is the traditional log server with a data viewer. This system will collect Windows Events and Sylog messages from operating systems and from software packages. The second service is called Retain or Rehydrate, which manages archiving.
As a cloud-based system, the Datadog Ingest service can collect log messages from anywhere, not just the site of your IT department. It can consolidate records from all sites into a common file or separate messages for each location – it all depends on the way you set the data collection system up. The service isn’t limited to collecting event log messages because it can also collect Syslog messages and proprietary log messages from a long list of vendor equipment and software.
The Ingest system doesn’t store records – you connect it to your own data store, which can be on-premises or in the cloud. The Retain or Rehydrate service does include storage with a retention period of up to 60 days. This length of time isn’t long enough for data security standards requirements, so you will still need to arrange a backup storage server for archives.
Who is it recommended for?
The Datadog system is resident in the cloud and it provides you with storage options. Essentially, the Retain or Rehydrate is a repository service, which you can use alongside the Ingest package. However, it is also possible to point the Ingest system to save your log files to a different platform.
Pros:
- Versatile Logging: Enables real-time monitoring and archival of logs for comprehensive analysis.
- Global Reach: Collects data across all locations, offering a unified view of IT infrastructure.
- Scalable Solution: Adapts to business growth with flexible storage and pricing options.
Cons:
- Limited Trial Period: A more extended evaluation period is desired for thorough testing.
The Log Rehydration service manages access to archive logs, which is necessary for compliance audits. Both Ingest and Retain or Rehydrate are available for 14-day free trials.
5. SolarWinds Security Event Manager
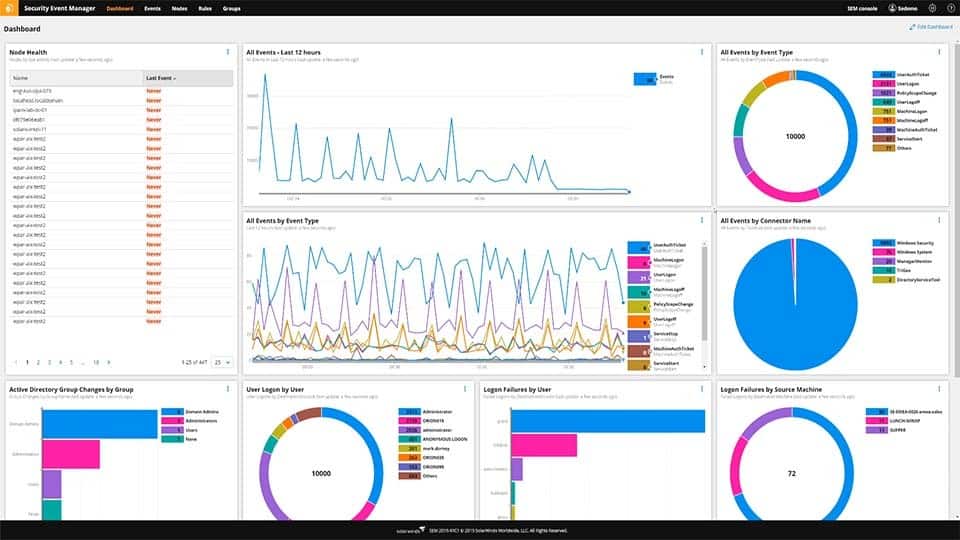
SolarWinds offers a number of tools that manage event logs. Of these, the Security Event Manager is the best option. However, as with all free versions, that solution has limitations. The main reason why any business would need to step up from the Event Log Collector to the Security Event Manager is that the log collector lacks an archiving feature.
Key Features:
- Unified Log Management: Centralizes collection of Windows and Syslog messages for streamlined analysis.
- Broad Compatibility: Seamlessly integrates with various applications for comprehensive monitoring.
- Log Centralization: Aggregates logs efficiently, simplifying data management.
- Advanced SIEM: Offers sophisticated security information and event management capabilities.
- Detailed Log Analysis: Facilitates manual examination of logs for in-depth insights.
Why do we recommend it?
SolarWinds Security Event Manager is a SIEM and it is also a log server. This system can collect Windows Events and also Syslog messages from operating systems and applications. No matter what format messages have when they arrive at the log server, they are converted to a common format for searching and storage.
One of the main reasons any business has to store event log records is in order to comply with data security standards. This requires those event log messages to be stored for a very long time – the mandatory retention period differs from standard to standard.
The Security Event Manager isn’t just limited to collecting log messages from Windows environments. It is also able to collect Syslog messages and firewall log data. The log message server gathers messages through a series of “connectors”. Each connector specializes in a specific log messaging standard, so if you only want to gather Event messages, you would just activate that connector.
All collected messages are filed in an accessible folder structure with parallel validity checks performed on each message as it arrives. Log files are protected from tampering through file integrity monitoring.
As well as log file management and archiving, the Security Event Manager includes a log record viewer. This includes sorting and searching features, which are necessary utilities that your business will have to provide to compliance auditors. This feature and pre-written reports support compliance to HIPAA, PCI DSS, SOX, ISO, NCUA, FISMA, FERPA, GDPR, GLBA, NERC CIP, GPG13, and DISA STIG.
Who is it recommended for?
This tool is able to collect messages from remote sites and cloud platforms as well as from the LAN to which its host is connected. The software for the Security Event Manager runs on Windows Server and it can accept messages from other operating systems if you set it as your software’s log destination.
Pros:
- Comprehensive Integration: Caters to enterprises with extensive support for various log sources.
- Ease of Use: Filters logs without requiring complex query knowledge, enhancing user accessibility.
- Rapid Deployment: Features numerous templates for quick start-up and minimal customization.
- Network Anomaly Detection: Historical tools identify unusual activity, aiding in security management.
Cons:
- Professional Learning Curve: Geared towards experts, necessitating a period of learning for full proficiency.
The SolarWinds Security Event Manager installs on Windows Server. Although it is on-premises software it is not limited to operating on the local network. It is able to receive event messages from remote sites. You can access the Security Event Manager on a 30-day free trial.
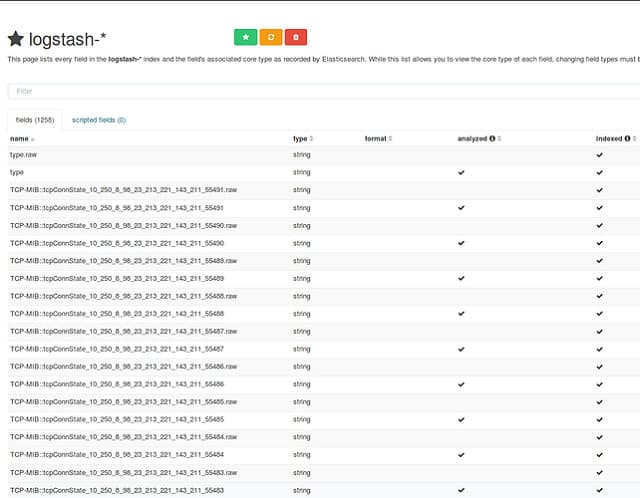
6. Logstash
Logstash is part of Elastic Stack, which is also known as ELK. The L in ELK stands for Logstash, the E stands for Elasticsearch, and the K stands for Kibaba. These three tools can be used together or individually, While Logstash is a log file server, Elasticsearch provides record-searching utilities and Kibana is a data viewer and frontend for the whole stack.
Key Features:
- Open Source: Available for free, facilitating cost-effective log management.
- Cloud Integration: Offers a premium cloud service for enhanced log handling.
- Format Flexibility: Harmonizes logs from diverse sources into a standardized format.
Why do we recommend it?
Logstash is the lesser-known log processing partner of the world-famous Elasticsearch. The design behind these modules of the Elastic Stack is that Logstach prepares log messages while Elasticsearch forms applications that mine that data. However, you can use Logstash by itself if you want and just have it for receiving and storing log messages.
The purpose of Logstash is to be a data receiver. You have to set WMI to forward all event log records to your Logstash implementation. So, it is possible to forward event log messages from several sites to one central Logstash receiver. This connection is facilitated by an EventLog plugin for Logstash.
All three tools in ELK are free and open source. Kibana is particularly widely used because it can interface for many different data analysis engines. It is probable that you would use Kibana and Elasticsearch to provide access to your stored event log files.
Logstash has capabilities to manage many different types of data so you could end up using it for other record collections and not just event logs.
Logstash is able to split existing files and you can set it up to rotate log files by date or message source. It will even manage a meaningful directory structure to make files easier to manage.
Who is it recommended for?
Logstash is free to use if you download it individually. You can download each of the ELK elements individually for free and then use them as a suite on your own server. However, the suite is also available in a hosted version, for which there is a charge.
Pros:
- Intuitive Interface: Features a user-friendly dashboard for easy navigation and visualization.
- Elastic Stack Integration: Part of a powerful trio, enhancing log analysis capabilities.
- Cloud Compatibility: Efficiently processes logs from major cloud platforms.
- Advanced Search: Utilizes Elasticsearch for sophisticated data filtering.
Cons:
- Plugin Dependency: Requires additional setup for handling various data types.
- Community Support: Lacks direct, paid support, relying on community for troubleshooting.
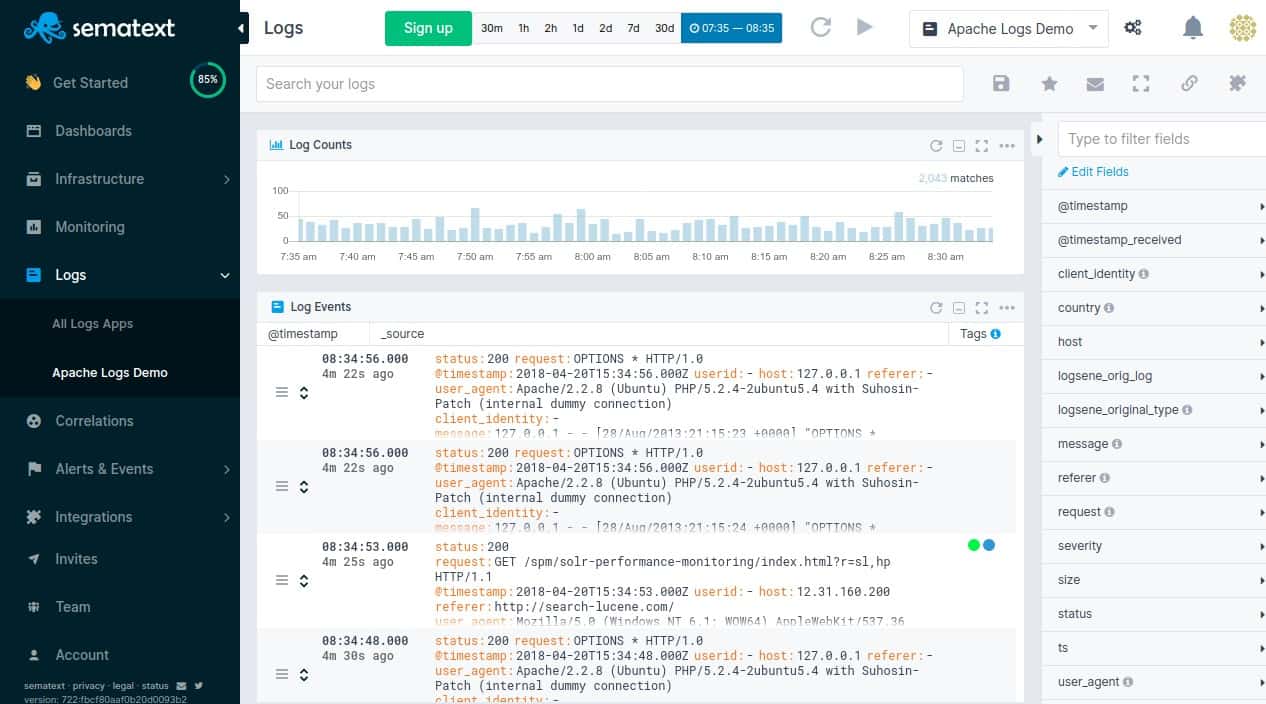
7. Sematext Logs
Sematext offers a hosted version of ELK. You get Logstash, Elsticstack, and Kibana in this package and it’s a great combo for collecting and managing event log messages from anywhere. It might seem a bit strange that people would pay Sematext for access to ELK, which is otherwise free. However, not all organizations have the skills onsite to install and manage technical software, So, Sematext is a bundle of server, software, and expertise that a non-technical organization would gladly pay for.
Key Features:
- Managed ELK Stack: Offers a hassle-free, hosted ELK solution for comprehensive log management.
- Cloud Convenience: Enables centralized log consolidation and analysis from any location.
- Format Versatility: Harmonizes diverse log data into a unified format for easier analysis.
Why do we recommend it?
Sematext Logs is a third-party system that hosts ELK and that includes Logstash, which is explained above. The Sematext platform provides other packages, such as Synthetic Monitoring for websites and Infrastructure Monitoring, which are formed by pre-written Elasticsearch queries. So, you have the option of building your own applications on top of Sematext Logs or buying an off-the-shelf solution.
Sematext has customized Kibana beyond recognition to create its own dashboard for customers to access data. Arriving event log messages are shown on the screen and pre-written Elasticsearch queries are shown as buttons and controls in the Sematext dashboard. This service is primarily geared towards security monitoring but the system collects and stores log messages as its primary activity.
Who is it recommended for?
Sematext Logs has a free edition, called Basic, which will be of interest to small businesses. Two higher plans cater to mid-sized and large organizations. You can adjust the throughput allowance and the retention period. However, be aware that increasing these factors will increase the price.
Pros:
- Flexible Data Queries: Leverages Elasticsearch for adaptable and powerful data interrogation.
- Broad Log Support: Capable of handling a wide array of log types, including SNMP data.
- Automated Alerts: Facilitates proactive monitoring with threshold-based alerting.
- Accessible Trial: Includes a no-cost version suitable for initial evaluations and small-scale deployments.
Cons:
- No Local Deployment: Lacks an option for on-premises installation, limiting flexibility for some users.
- Dependent on Customized Dashboard: Utilizes a heavily modified Kibana interface for data visualization, which may have a learning curve.
Sematext Logs is a subscription service, available in three plan levels: Basic, Standard, and Pro. The Basic service is free forever but it is limited to processing 500 MB of data per day. Its retention period is seven days. The standard and Pro services have adjustable data throughput and retention periods. The Standard service offers retention for 7 and 15 days and daily throughput volumes of 1, 5, or 10 GB. The Pro plan can go up to 150 GB of data per day and a retention period of up to a year. Both the Standard and Pro plans are available for a 14-day free trial.
Choosing Remote Event Log Software
Most of the software that manages event logs have extra capabilities. In fact, it is difficult to find a tool that just manages event logs. The main market for event log data lies in SIEM systems. They will manage event log messages solely to provide the security inference engine with source data.
In many software packages, log file management is not an end product. You may have to pay for those clever security operations that you might not want or need if you are just looking for a way to manage event log files.
The “remote” part of your requirements should not be difficult to fulfill. Most event log servers operate over a network and any tool that can communicate over a network can connect to other sites across the internet.