Signal Sciences, now part of Fastly, is a cloud-native security platform built to safeguard modern applications and APIs in real time. Originally developed to provide application-layer security monitoring, it has evolved into a widely used solution for detecting and mitigating web application threats and vulnerabilities. Integrated into Fastly’s edge cloud platform, it helps organisations defend against an increasingly complex cyber threat landscape.
Signal Sciences delivers protection through real-time telemetry, behavioural analysis, and security analytics that monitor application traffic as it flows through systems. Instead of relying on traditional rule-based web application firewalls, the platform uses adaptive detection techniques to identify and block threats such as SQL injection, cross-site scripting (XSS), and automated bot attacks based on behavioural patterns and anomalies.
Designed for cloud-native environments, it integrates easily into modern application architectures, whether deployed on-premises, in cloud infrastructure, or at the network edge. This allows teams to maintain consistent visibility into application traffic, user behaviour, and potential attack patterns, making it particularly useful in fast-moving development and DevOps environments.
Beyond threat detection, the platform also supports compliance requirements such as PCI DSS, HIPAA, and GDPR. Its reporting and visibility features help organisations maintain audit readiness while improving response times to security incidents.
How Does Signal Sciences Work?
Rather than setting up a complicated configuration, Signal Sciences has simplified this process by having its customers modified their DNS to point incoming application traffic to their cloud engine. Alternatively, you can run the WAF on-premises, which requires an agent install and several additional steps to set up.
From there, incoming traffic is analyzed, identified, and eventually forwarded to the client-server if it is determined legitimate. This approach to setting up a WAF is considerably faster than most onboarding procedures found in more legacy solutions.
It allows for protection across a wide variety of environments including containers, hybrid environments, and standard cloud setups. Application and programming language do not matter, as Signal Sciences can redirect traffic from AWS, Microsoft Azure, or Google Cloud. If your server receives HTTP traffic, it works with Signal Sciences.
Signal Sciences WAF is completely agentless as it works in the cloud to apply both managed and custom rulesets to your application traffic. Protections extend beyond the OWASP Top 10 and include defense from botnet attacks, account takeovers, credential stuffing, API abuse, and DDoS mitigation.
Automatic blocking and scanning are applied to Signal Sciences’ cloud engine which processes nearly 200 billion requests per week. While legacy WAF products require signature tuning to rule out false positives, Signal Sciences SmartParse virtually eliminates incorrect detections. An impressive 95% of their customers run Signal Sciences WAF on full blocking mode.
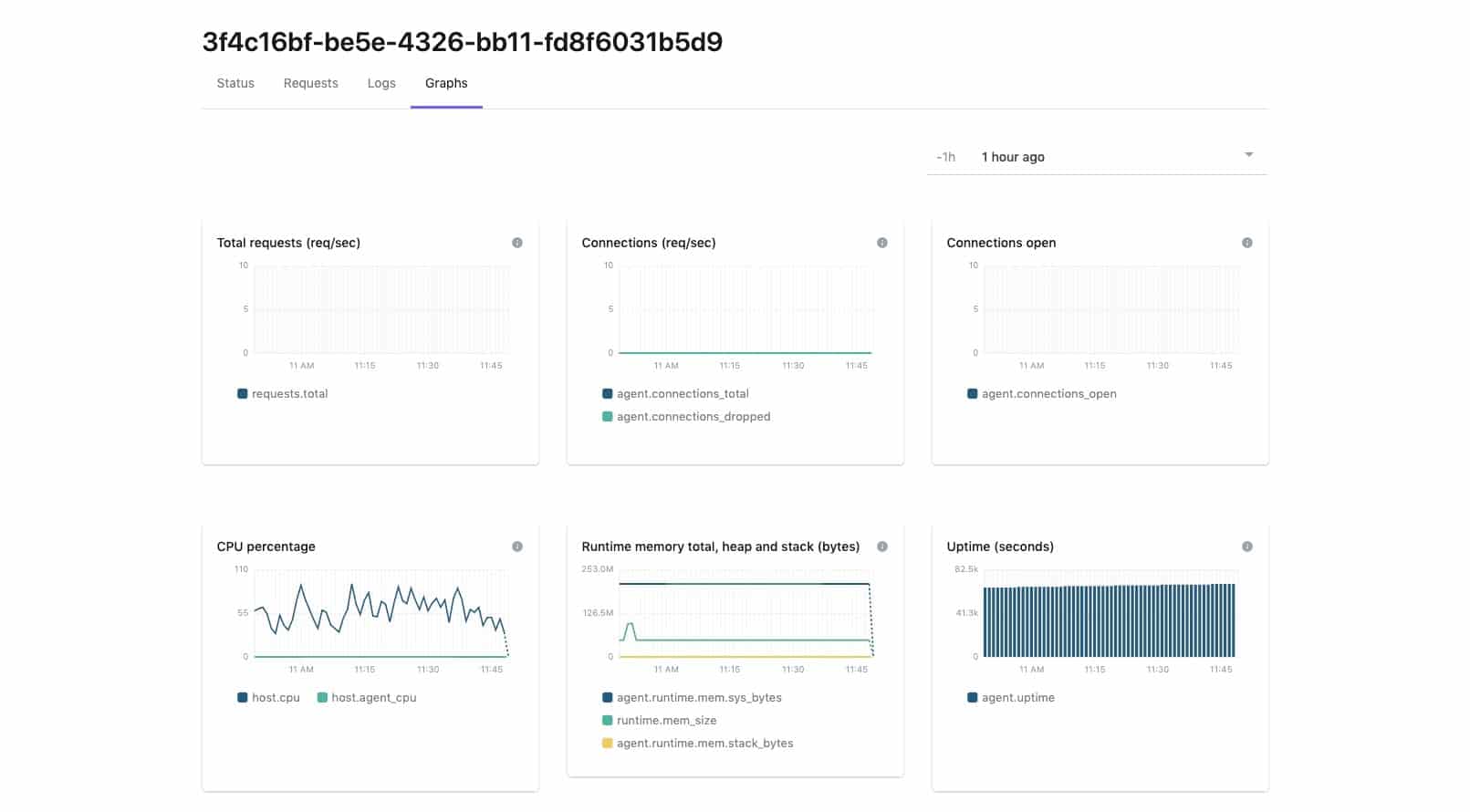
Gaining visibility into your WAF can all be done from a single management console built right into the WAF. This provides real-time reporting capabilities, historical threat data, and reporting all from the same tool without the need for third-party plugins or logins.
Signal Sciences Features
The power behind how Signal Sciences protects its users lies almost entirely in their proprietary SmartParse system. While much of how this system works is not publicly documented we can assume it uses some level of artificial intelligence and behavioral analysis to not only monitor traffic but understand the context from which it was sent. This approach aims to simplify the WAF setup process and provide a more ‘set it and forget it’ service for Signal Sciences customers.
As most of the heavy lifting is done in the cloud, users can configure their WAFs using Power Rules. These rules can be executed without any complicated scripting languages or regex modifications. Power Rules acts as a user-friendly bridge that makes pairing an input condition with an output action simple and intuitive.
From a simple drop-down menu, you can define your own signals and choose from a number of different inputs such as path, method, user agent, or query parameter. While you can build your own workflows and rules Signal Sciences has a suite of templates you can use to defend against everything from account takeover attempts to bot activity.
For more streamlined blocking you can upload entire lists of countries, IP addresses, strings, or wildcards to include in your custom ruleset. While the lists feature only supports four types of data, this still makes it easier to import lists used elsewhere in your organization or import a list found elsewhere such as an IP reputation service.
The Signal Sciences platform definitely takes a more proactive approach to secure its clients’ applications. While most WAFs use managed rules for quick configuration Signal Sciences takes in all traffic and does all of the sorting for you. This can feel a bit controlling at times but since it works so well many customers do not have a problem with it.
One of the more notable features is the ability to tag your request logs. Whenever a threat or anomaly is detected, you can configure the WAF to request and send key metadata and header information to the dashboard. This allows for a manual review of the event and normally provides enough context to either escalate the issue or identify it as a false positive.
Developers can configure thresholds that trigger actions to block and alert suspicious or threatening traffic as it attempts to contact the webserver. This can be set to both alert and block, or just apply a block after that limit has been exceeded. You can fine-tune your thresholds and alerting to ensure no one on your team is getting flooded with requests from false positives.
As thresholds are breached, alerts can be sent via email, or push notifications to apps like PagerDuty, Datadog, Slack, or Splunk. This type of flexible integration makes Signal Sciences easier to plug into your current application security infrastructure.
Ease Of Use
When comparing Signal Sciences WAF against how legacy WAFs operate, there really is no comparison. Signal Sciences eliminates the need for complicated setup and configuration, as well as the manual tweaking, or importing of signatures and policies used for more primitive rule sets and detection.
You can even argue that Signal Sciences WAF is easier to use than some of the more competitive WAF products such as Cloudflare or AWS WAF. Throughout the setup process, it’s clear that one of the product’s main goals is to streamline the setup and implementation as much as possible. The fact that a simple DNS change can get you up and running on their cloud version already puts it ahead or a majority of existing alternatives.
Even installing Signal Sciences as an on-premises solution seemed easier than similar solutions such as AWS WAF. While testing I found the cloud installation takes roughly five minutes, whereas the on-premises setup is about 10 to 15.
Sometimes products that try to enhance user experience end up putting their customers in a box of limitations and templates. With Signal Sciences, that’s not the case. While there are a number of wizards and managed rulesets that help you get off the ground, it never feels like you’re limited from a technical perspective. Even with managed rules you can still get granular and choose how those rules function or turn them off entirely.
There are times that Signal Sciences almost has a ‘done for you’ feel to it, which at first made me a bit skeptical. With 95% of Signal Sciences customers running in full blocking mode, I anticipated at least some false positives during testing, but I was pleasantly surprised.
Viewing real-time and historical security events can easily be done through the analytics dashboard. Much of the filtering and sorting feels intuitive and similar to other popular cloud-based interfaces. The event tagging and custom ruleset configuration may take some trial and error to get set properly, but with a built-in test function, you can still be confident you’re releasing solid security policies.
Overall, Signal Sciences is definitely leading the way when it comes to simplifying the WAF setup and management.
Integrations
Signal Sciences categorizes alert integrations into two types, corporate integrations, and site integrations. Corporate integrations are designed to notify you or your team about activity that takes place on the administrative end of your Signal Sciences WAF. This includes changes to settings, sites, and users. This can be used to add an extra layer of protection to your environment as well as create an audit of changes you and your team make.
Currently, corporate integrations support alerting via email, Microsoft Teams, and Slack.
Site integrations are made to keep you informed on events that take place within specific sites on your WAF. This can include threshold alerts, IP flagging events, changes to rulesets, and modifications to site-level settings. Below is a list of currently available integrations.
- Datadog
- Generic Webhooks
- JIRA
- Mailing List
- Microsoft Teams
- OpsGenie
- PagerDuty
- Pivotal Tracker
- Slack
- VictorOps
Outside of just alerting, Signal Sciences WAF supports other meaningful workflow integrations for 40 other products and services. For example, Signal Sciences can hook into Palo Alto or Cisco Threat Response to execute automated incident responses or store and compress your log data for long term analysis.
Customer Identity and Access Management (CIAM) can be implemented through vendor integrations by companies like Cloudentity or Ambassador Edge Stack. Lastly, Signal Sciences supports PaaS integration through VMware Tanzu (formerly Pivotal).
This gives teams who work in the cloud an option to import Signal Sciences WAF as a build-pack directly into the Pivotal Cloud Foundry platform, or through a deployment option in the Pivotal Container Service.
Signal Sciences WAF is a fairly holistic security solution. You may find yourself needing additional analytic data past the 30-day mark. For this, an integration to a SIEM or other third-party storage platform would be necessary.
Hunting for threats is possible through Signal Sciences, but you may find that your existing SIEM solution is better suited for that task. In most cases, an API integration can securely move those logs, as well as any tags you’ve applied to that other system.
Pros & Cons
Pros:
- Sleek interface – easy to use
- Does a good job of simplifying complex RASP environments
- Lightweight – carefully avoids impacting app performance
- Can detect API abuse, account takeover, and other threats
Cons:
- Can take time to fully explore all options available
Pricing
Currently, Signal Science does not make its pricing publicly available, but it does touch on how its WAF reduces costs in most environments.
Signal Science drastically lowers costs by leveraging its SmartParse technology, which effectively eliminates the need for managed service fees and costly installation and onboarding. By using artificial intelligence there is no need for rule tuning or the manual configuration of pattern matching settings.
It’s safe to say if you’re currently paying managed service fees for installation and rule management, you’ll find Signal Sciences WAF priced considerably less than what you’re currently paying. Reportedly its WAF solution is often one third to one half the cost of more traditional WAF pricing models.
Why choose Signal Sciences WAF?
Signal Sciences WAF proves to be on the cutting edge of threat detection technology, leveraging proprietary artificial intelligence to stop threats and execute automatic remediation.
The use of AI in these settings helps reduce costs, and those savings are ultimately passed down to the customer. With its mix of intuitive design, fast implementation, and scalable pricing, Signal Sciences WAF is one of the most competitive offerings on the market today.
Signal Sciences Alternatives
If you’re looking to compare Signal Sciences WAF to a list of alternatives, look no further. If you’re still on the hunt for the best application firewall, be sure to check out our best web application firewalls post.
Below is a shortlist of other WAFs comparable to Signal Sciences:
- AppTrana Managed Web Application Firewall This WAF solution comes with its own fully managed security team and features customized security policies, contractual SLAs, and 24×7 support.
- Cloudflare WAF Leverages its large cloud-based infrastructure to build powerful rulesets and policies with relative ease through intuitive dashboards and wizards.
- F5 Advanced Web Application Firewall Utilizes proactive botnet defenses, behavioral analytics, and application-layer encryption to defend your services against threats, and secure communications between your ancillary systems.
- Barracuda Web Application Firewall Barracuda has three WAF offerings that provide adequate protection from threats and a host of automated remediation. Solutions include on-premises, cloud-based, and as a managed service.
- NGINX App Protect WAF Leverages automation to reduce costs and unclog bottlenecks that are commonly found in workflow rules. Features a suite of non-disruptive security controllers developers can use in DevOps environments.