Like most ransomware, WastedLocker attacks computers running Windows. However, WastedLocker is a big game hunter
WastedLocker attacks large corporations and asks for huge ransoms. While many ransomware attacks ask for a few hundred dollars, it demands millions of dollars.
The hacker group behind WastedLocker is very well organized. Since the early years of this century, the team has been in operation and has earned more than $100 million.
Here is our list of the best ransomware tools that will protect against WastedLocker:
- ManageEngine Ransomware Protection Plus EDITOR’S CHOICE Provides end-to-end protection across all endpoints. It identifies, mitigates, responds to, and helps recover from a WastedLocker ransomware attack. Get a 30-day free trial.
- ManageEngine DataSecurity Plus (FREE TRIAL) This large package is delivered in four units, which can be purchased individually and they provide data protection methods to block ransomware tempering. Runs on Windows Server. Start a 30-day free trial.
- CrowdStrike Falcon Insight Provides two levels of protection through a full anti-malware package on each device and a cloud-based threat hunter that gathers activity reports from endpoint units. Installs on Windows, macOS, and Linux.
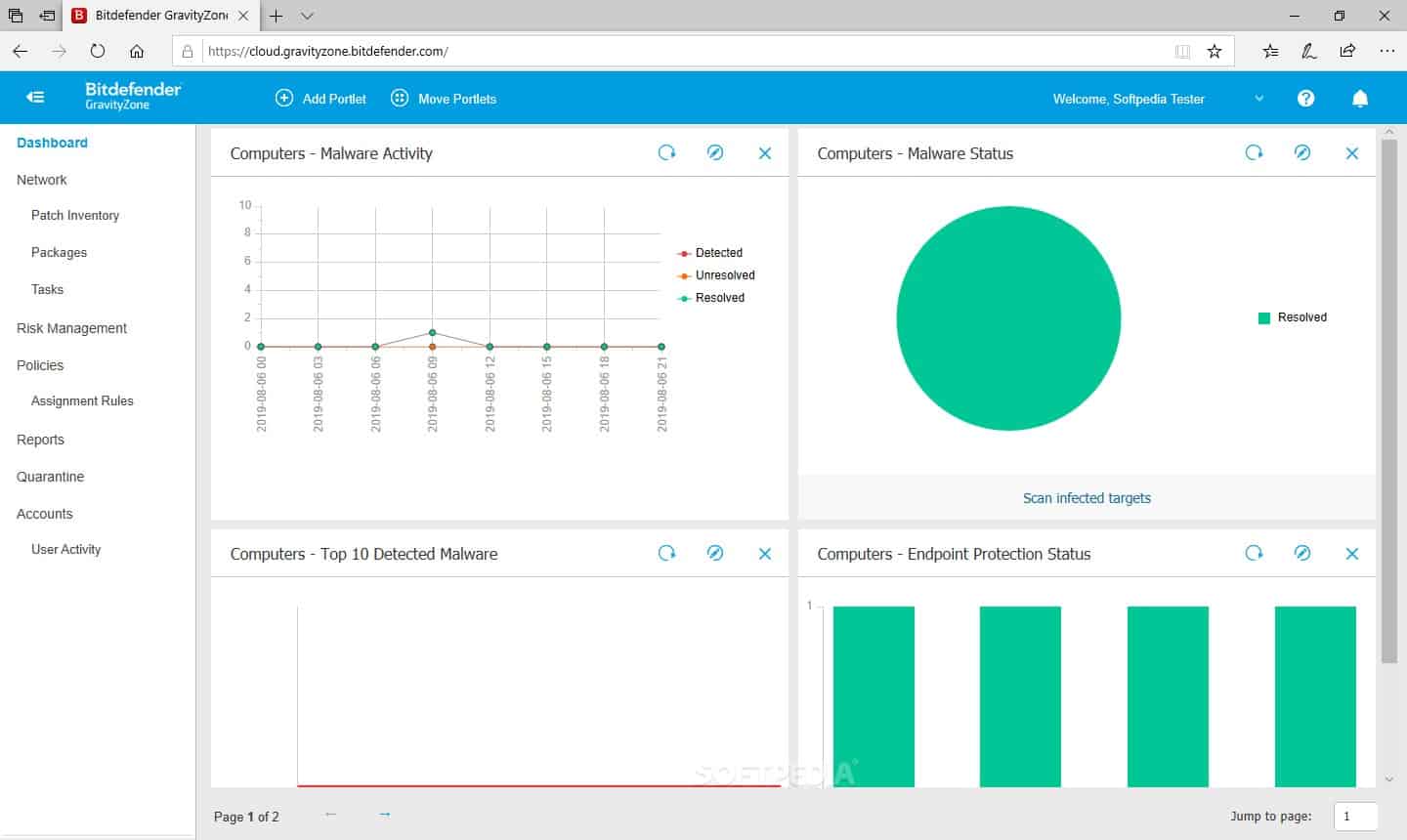
- Bitdefender GravityZone This package of malware protection and backup software is available in editions to suit different sizes of businesses. Runs on Windows, macOS, and Linux.
Who is behind WastedLocker ransomware?
WastedLocker is a product of Evil Corp, which is also known as Indrik Spider. This is a Russian hacker group that had its first success with Zeus, a banking Trojan. The most famous product of this group was Dridex, a banking Trojan that earned a lot of money. Dridex was active from 2011 to 2020, and it was developed as an enhancement of Zeus.
The Evil Corp group is led by Maksim Yakubets and Igor Turashev. In December 2019, the U.S. Treasury Department’s Office of Foreign Assets Control (OFAC) issued an arrest warrant for the pair. In addition, it offered a reward of $5 million for information leading to their arrest. But, unfortunately, they still haven’t been arrested.
The main reason for the US authorities’ interest in Evil Corp is Dridex, not the WastedLocker ransomware. However, the serious attention of the US security agencies forced Evil Corp to reassess all of its activities, and the group went quiet, temporarily, through to early 2020.
The source of WastedLocker ransomware
Evil Corp first developed ransomware in 2017 with the Bitpaymer crypter. This was a “big game hunter”, which was aimed at large corporations, and asked for large ransoms. Bitpaymer was the forerunner of WastedLocker ransomware.
Bitpaymer was launched in 2017, targeting hospitals in the UK. Attacks then moved on to focus on large US corporations. The ransomware’s delivery mechanism was based on Dridex modules.
In 2019, Evil Corp created a variant of Bitpaymer, called DoppelPaymer, a Ransomware-as-a-Service system. RaaS allows other hackers to use a ransomware system for a fee without letting them access the code.
In May 2020, the group launched WastedLocker as a replacement for Bitpaymer. The new ransomware shares some procedural similarities to Bitpaymer, but with completely different code.
WastedLocker attacks are highly tailored. Not only does the group conduct extensive research to gain entry to a network, but it produces different modules for each attack and a targeted ransom note. The group is also able to adjust an attack as it happens. In some cases, network managers have been able to spot and remove the WastedLocker dropper, causing the group to drop a stealthier replacement manually.
The start of a WastedLocker attack
The majority of the targets for the WastedLocker ransomware have been large US corporations. The victim sees a popup when visiting specific sites that advise them to update their browser. The popup, when pressed, downloads a zip file, which contains a JavaScript module called SocGolish.
The websites that popups appear on are not properties of Evil Corp. Rather, they are owned and run by legitimate organizations, and the Evil Corp group has managed to infect them. News websites are regularly targeted for this infection.
The module installs and executes PowerShell scripts and the Cobalt Strike backdoor. This gives the hackers entry, and they will use both manual and automated methods to proceed with the attack.
What happens in a WastedLocker ransomware attack?
The hacker’s starting point is an endpoint on the system that got the Cobalt Strike backdoor installed. Using experience and a toolkit of system scanning services, the hacker then builds up a profile of user accounts on the endpoint and connections through to other endpoints across the network. The hacker will also investigate backup processes and drop files to get them uploaded to the backup server to trigger a ransomware infection.
At this point, activity is more along the lines of an advanced persistent threat than a ransomware attack. Tools include systems to capture credentials and access a user’s account on the accessed device through a remote access system that enables the hacker to acquire the user’s identity and communicate with others in the organization.
The reconnaissance phase of the attack allows the hacker to move across the network to locate major file stores and database servers, which will become infection targets. Once the team leader is satisfied that enough high-value targets have been acquired, the WastedLocker ransomware is activated.
WastedLocker encryption
The ransomware performs several tasks before it launches encryption. It deletes all shadow copies of working documents that are generated by autosave functions. It will also disable Windows Defender, elevate its account access to Administrator, and install the encryption process as a service.
The system generates a different encryption key for each file. This is an AES cipher with a 256-bit key. Those keys are then listed in a file, which is encrypted with a 4096-bit RSA cipher. This is the public key, which encrypted the files. RSA uses a different key to decrypt. This cannot be derived from the encryption key. Therefore, knowing the public key is no use to the victim. However, it can be used as a reference code for the decryption process. The RSA key pairs seem to be generated offsite, and the public key is sent to the target system while the private key is held on the Evil Corp server for delivery after payment.
The WastedLocker does not encrypt system files or executables, so the computer is still operational. However, it will encrypt working files, such as documents, spreadsheets, images, video, and audio files. It also encrypts database storage files. Rather than just working through a computer alphabetically or starting with the first contacted computer, WastedLocker identifies the most critical data store and begins with what seems to be its highest value directory.
Each file is overwritten with its encrypted version. The filename then gets an extra extension added to it. This is the name of the target company and wasted, for example, a file called expenses.docx on a computer in a company called NewWorks, Inc. will end up with the name expenses.docx.newworkswasted. The encryption process also generates a ransom note for each encrypted file. The note’s text is the same in every case, so you only have to open one of them. This is a text file and has the same name as the encrypted file but with _info. So, in the case of the example, the associated ransom note would be expenses.docx.newworkswasted_info.
The ransom note has the following format:
<victim name>
YOUR NETWORK IS ENCRYPTED NOW
USE <actor email 1> | <actor email 2> TO GET THE PRICE FOR YOUR DATA
DO NOT GIVE THIS EMAIL TO 3RD PARTIES
DO NOT RENAME OR MOVE THE FILE
THE FILE IS ENCRYPTED WITH THE FOLLOWING KEY:
[begin_key]<base64 encoded public key>[end_key]
KEEP IT
The email addresses used for contact are used only for one attack. They are always on the following domains:
- PROTONMAIL.COM
- AIRMAIL.CC
- ECLIPSO.CH
- TUTANOTA.COM
- PROTONMAIL.CH
Once the attack has encrypted all of the target files on the victim’s system that can be reached, the ransomware process ends. It doesn’t continue with other attack strategies, such as deleting files or infecting the boot process. Any new files created after the attack will not be encrypted.
Recovering from a WastedLocker attack
There is no way to decrypt files that have been encrypted during a WastedLocker ransomware attack without paying the ransom. The AES encryption that converts the files is uncrackable, and so is the RSA encryption that protects the list of AES keys. There are no cybersecurity consultancies that offer a decryption service.
The best way to recover from an attack without paying is to ensure that you have backups of all critical files, and that your backup process and stores are all very well protected. As the Evil Corp group uses manual exploration and will move around the system for as long as it takes to get all the essential data stores, those backup locations usually also get encrypted.
WastedLocker ransom demands range between $500,000 and $10 million. The most famous attack to date was against US technology firm Garner in October 2020. The company was asked for $10 million. No one knows whether the company paid that total amount. However, they did pay because they got the decryption key. So it seems that the Evil Corp group is prepared to negotiate.
Defending against WastedLocker ransomware
The good news is that WastedLocker is no longer active. However, its successor, called Hades, is in circulation. This is very close to WastedLocker but has some extra obfuscation features to be regarded as WastedLocker II.
The best defense lies in intelligent cybersecurity, susceptible, and sensitive data, which has additional regulations surrounding its use and protection. Here are three cybersecurity packages that provide competent defense against WastedLocker ransomware.
Our methodology for selecting a ransomware tool that will protect against WastedLocker
We reviewed the market for anti-ransomware systems that can prevent or recover from WastedLocker and other ransomware strains and assessed tools based on the following criteria:
- Malware blocker for Windows – the target operating system for WastedLocker
- User education to spot social engineering and phishing
- Browser security to identify fake websites that impersonate well-known corporate sites
- Popup blocker
- Blacklist of known hacker domains
- Free trial or a demo that enables an assessment before buying
- Value for money from a system that can block all types of malware and automated threats, not just WastedLocker
1. ManageEngine Ransomware Protection Plus (FREE TRIAL)
ManageEngine Ransomware Protection Plus takes a multi-pronged approach to protecting your endpoints and infrastructure from a WastedLocker ransomware attack. Its low system impact and 24/7 security greatly reduce the chances of an attack. Even in the event of an attack, it helps your device recover quickly.
Key Features:
- Behavioral detection engine: Uses machine learning to detect patterns that can indicate a WastedLocker ransomware attack.
- Device isolation: Once detected, it isolates the infected device to prevent lateral spread.
- Kill modes: it can kill ransomware processes to mitigate its impact.
- Recovery and rollback: Connects with backup systems to restore files to their pre-attack state.
- Root cause analysis: Pinpoints the root cause of the attack.
Why do we recommend it?
Ransomware like WastedLocker can quickly disable security systems, and this is where a tool like ManageEngine Ransomware Protection Plus comes in handy. It goes beyond just signatures and uses machine learning and behavioral analysis strategies to identify the attack as early as possible.
After it identifies the attack, this tool isolates the device and kills processes to prevent its further spread. In the meantime, it also connects with backup systems to recover data, thereby mitigating the impact of this ransomware.
Finally, it also identifies the vulnerability that led to the attack, so you can fix the problem.
Who is it for?
It is a good choice for large enterprises with a distributed network. Also, it is helpful for IT teams that need comprehensive ransomware protection. It can also work well for businesses with limited cybersecurity staff or expertise.
Pros:
- Highly accurate
- Minimal impact on system resources
- Extensive forensics
- Flexible deployment
- Highly scalable
Cons:
- Complex setup
ManageEngine Ransomware Protection Plus has a free edition that supports up to 25 endpoints. The Enterprise Edition starts at $6.99 per endpoint per year. Start a 30-day free trial.
.
EDITOR'S CHOICE
ManageEngine Ransomware Protection Plus earns our Editor’s Choice award for its extensive detection and remediation of ransomware attacks. It combines detection, mitigation, recovery, and diagnosis into a single platform for easy use. More importantly, it uses minimal resources and does not require extensive human interference. Its use of advanced technologies makes it highly scalable and relevant for the future.
Download: Start a 30-day FREE Trial
Official Site: https://www.manageengine.com/ransomware-protection/
OS: Windows
2. ManageEngine DataSecurity Plus (FREE TRIAL)
ManageEngine DataSecurity Plus is a sensitive data protector designed for businesses that need to comply with HIPAA, PCI DSS, and other data privacy standards.
Key Features:
- File Activity Monitoring: Audit, track, receive alerts on, and report all file access and modifications in real time.
- Sensitive Data Protection: Detect, block, and respond to potential data leaks through USBs, email, printers, and other channels.
- Data Classification & Risk Assessment: Inspect content, analyze context, and classify files based on sensitivity and risk level.
- File Management & Analysis: Review disk usage, identify redundant or junk data, assess file permissions, and flag at-risk files.
Why do we recommend it?
Businesses that manage sensitive data need a data loss prevention system, such as ManageEngine DataSecurity Plus. This service discovers the locations of data and then scours it for instances of special information, such as PII. This search will be adapted according to a data security standard, including GDPR, PCI DSS, HIPAA, or FISMA.
The system includes an eDiscovery module that identifies sensitive data stores and categorizes the types of data held there. This enables you to increase security measures for those locations. In addition, the defense system of DataSecurity Plus is implemented as a file integrity monitor (FIM). This will spot encryption actions immediately and block them.
The system examines the processes that try to access sensitive data stores and measures their intent. The package will then block any malicious activity by killing processes and suspending compromised user accounts.
Who is it recommended for?
As well as protecting sensitive data, this tool has user activity tracking and file integrity monitoring services. These modules will detect automated or manual malicious actions. The package watches data exfiltration points, such as FTP connections, emails, and detachable storage. This should help to block ransomware that steals data for disclosure.
Pros:
- Web & Cloud Safeguards: Monitor web traffic, detect shadow IT apps, and enforce policies to block malicious or inappropriate content.
- Email Data Security: Inspect attachments for sensitive information, warn users of policy violations, and prevent confidential data leaks.
- Ransomware Containment: Detect potential ransomware activity early and isolate infected devices automatically to limit spread.
- Insider Threat Detection: Continuously monitor file activity, removable devices, data transfers, and application use to identify anomalies.
Cons:
- No Cloud Option: This is a Windows Server software package only.
DataSecurity Plus is an on-premises software package that installs on Windows Server. It is available for a 30-day free trial.
3. CrowdStrike Falcon Insight
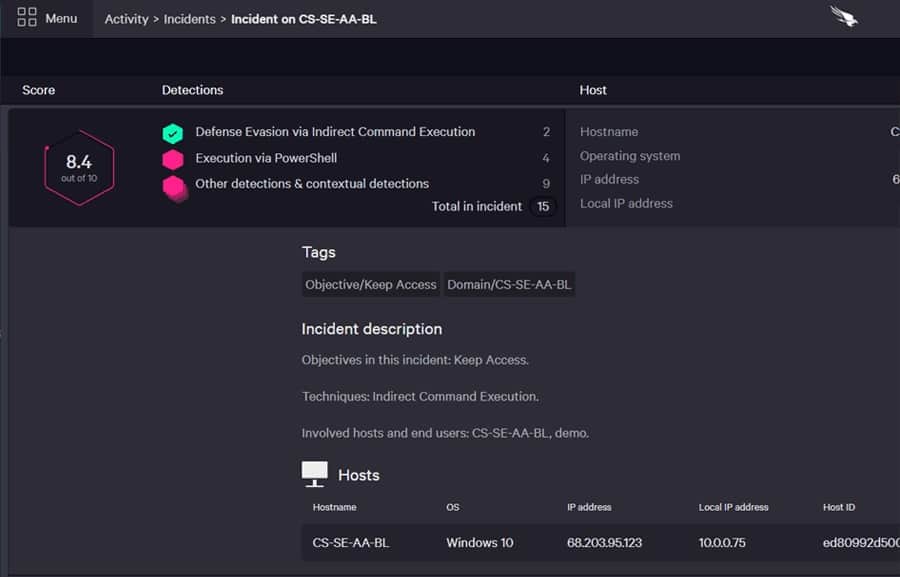
CrowdStrike Falcon Insight is an endpoint detection and response (EDR) package. It includes a coordinating module to create enterprise-wide protection. The endpoint agent installs on Windows, macOS, and Linux and the overseer is a cloud-based service.
Key Features:
- AI-Driven Threat Detection: Uses artificial intelligence to identify and prioritize threats with high accuracy.
- Continuous Endpoint Monitoring: Tracks device activity and analyzes data in real time.
- Detailed Attack Insights: Provides visibility into attack paths and adversary behavior.
- Immediate Threat Response: Offers Real Time Response (RTR) for direct system access and automated mitigation.
- Integrated Intelligence Feeds: Leverages threat intelligence to improve detection accuracy.
Why do we recommend it?
An adaptable threat such as WastedLocker needs a flexible detection system. The CrowdStrike Falcon Insight system includes AI processes to spot unusual activity, which can extend beyond malware to catch intrusion. The system is able to disconnect a computer, leaving a local module to fight the infection, while protecting the rest of the network.
The combination of device protection and system monitoring is an excellent defense against ransomware systems such as WastedLocker and Hades. The on-site modules use anomaly detection, enabling it to spot brand new malware or seemingly genuine activities performed by legitimate user accounts. The EDR will isolate devices if it spots suspicious activity. It can also delete malware files and kill processes. The endpoint protection system is fully autonomous, and it can be bought separately. It is marketed as CrowdStrike Falcon Prevent.
The cloud-based module is a threat hunter that relies on uploads of activity logs from the endpoint agents. This gets threat intelligence feeds from CrowdStrike that update its data search strategies. The coordinator will inform all endpoints of detected threats, whether identified in the data or notified by an endpoint.
Who is it recommended for?
Insight has two elements, which are Falcon Prevent, installed on each device, and then the Falcon Insight SIEM on the cloud. So, this is a package of tools rather than a single product. This makes the service very effective but it also makes it expensive. This solution is suitable for mid-sized and large organizations.
Pros:
- Centralized Management: Single console for endpoint, identity, cloud, and data protection.
- 24/7 Threat Hunting (MDR): Managed detection and response services around the clock.
- Flexible Scalability: Adapts to growing organizational security requirements.
- Comprehensive Endpoint Protection (EDR): Continuous monitoring to detect, investigate, and respond to advanced threats.
- Cloud-Native Platform: No on-premises hosting required; operates fully in the cloud.
Cons:
- Cost Considerations: Deployment on every device can make this solution expensive for larger organizations.
You can get a 15-day free trial of Falcon Prevent.
4. Bitdefender GravityZone
Bitdefender GravityZone is a bundle of cyber defense systems that work very well in combination to protect against WastedLocker and Hades. The most important defense is its managed backup service.
Key Features:
- Exploit & Vulnerability Protection: Guards vulnerable applications by monitoring memory access and blocking exploit techniques.
- AI-Driven Malware Detection: Uses machine learning trained on billions of files to predict and stop advanced threats.
- Process Monitoring & Remediation: Continuously tracks running processes for suspicious activity and automatically mitigates threats.
Why do we recommend it?
Bitdefender GravityZone is the ideal package for combatting the classic ransomware attack that encrypts data and then expects a payment to decrypt it. The two elements of the GravityZone system are an antivirus and a backup service. The package even scans files for infection on the way in and out of the backup repository.
GravityZone implements malware scanning at several points of the system. It scans endpoints and all files downloaded onto them. The system also guards access to the backup store, scanning every file before letting it on. That even includes manually commanded transfers.
The GravityZone package has a vulnerability scanner and a patch manager to reduce your attack surface. There is also a file integrity monitor in there as a last resort. GravityZone implements automated responses. It can isolate a device as soon as it spots suspicious activity. That will limit the potential damage that WastedLocker and Hades could cause.
Who is it recommended for?
Bitdefender produces GravityZone in a range of editions that suit different business types. For example, there is an edition for home offices and another for managed service providers. The package is affordable and easy to set up. However, this service alone won’t protect your business against the data theft strategy of ransomware such as WastedLocker.
Pros:
- Fileless Threat Defense: Detects and blocks attacks that bypass traditional antivirus methods.
- Ransomware Prevention: Proactively identifies and halts ransomware before files are encrypted.
- Network Attack Protection: Prevents attacks targeting network vulnerabilities.
Cons:
- Limited Data Loss Prevention: Primarily focused on malware protection rather than sensitive data control.
Bitdefender GravityZone is a software package that runs as a virtual appliance. It is available for a one-month free trial.