If you are using a Unix-based operating system, such as Linux or macOS, you can utilize tcpdump, a powerful command-line tool, to analyze and capture network traffic. This utility is a staple for network administrators and security professionals, providing a detailed view of packet data traversing your network.
Tcpdump is an open-source program, available to download and use for free. Its simplicity and functionality make it a valuable resource for troubleshooting, monitoring network performance, and detecting suspicious activities. Despite its robust capabilities, tcpdump is not typically included as a default component in most Unix or Unix-like operating systems. Therefore, you will need to install it manually.
To access tcpdump, you can download it from the tcpdump GitHub repository, where the most recent versions and updates are maintained. Alternatively, it is also available on the official tcpdump website, which provides reliable access to the latest releases. For many Linux distributions, tcpdump can also be installed directly from the system’s package manager, simplifying the installation process.
While tcpdump’s core functionality is straightforward, its extensive list of commands and options allows for granular control over the type of traffic you monitor. From basic packet capture to advanced filtering using Berkeley Packet Filter (BPF) syntax, the tool provides incredible flexibility.
This article will guide you through the basics of tcpdump, from installation to practical usage, ensuring you can leverage this tool to understand and manage your network traffic effectively. Whether you are a seasoned network professional or a newcomer to network analysis, tcpdump remains an essential tool for your Unix-based systems.
Elements of tcpdump
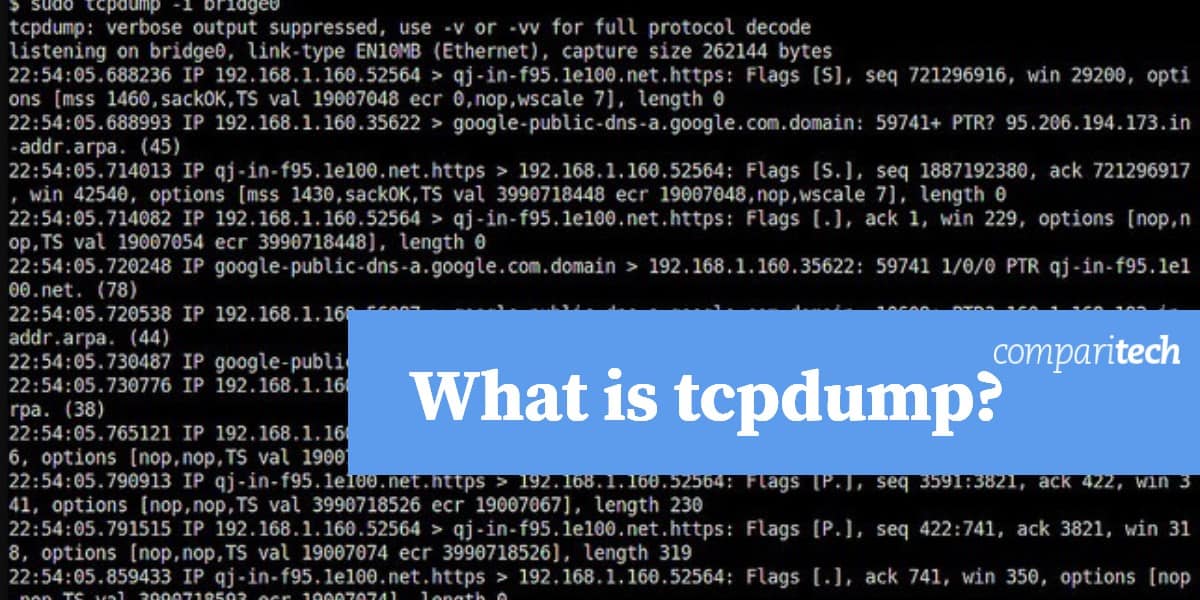
The packet capture utility used by tcpdump is provided by libpcab, which is a C/C++ library of procedures. The main tcpdump program is the interface for the packet capture process. When run, it will start the libcap process to capture network packets and then display their contents on the screen. Unless a limit to the number of packets to be captured is specified when the program starts, it will continue to run forever. The processing is then terminated by an interrupt signal (Control-C).
The program is run at the command line and includes several options, which are indicated by flags. These flags alter the behavior of the program to get it to select packets that match a specified pattern, limit its running time, or get it to read stored packets from a file rather than from the network interface.
Tcpdump format
The tcpdump command can be issued by itself or with options, parameters, and/or regular expressions. None of these elements are mandatory and the order is not important.
tcpdump <-option_identifier> <option_name> <parameter> <parameter_value> <regular expressions>
Tcpdump options
The command tcpdump is followed by options, which are also known as flags. Each of these is denoted by a hyphen followed by a letter. Below is a list of each of these flags.
-A print packets in ASCII without the link-level headers
-b show the AS number is ASDOT format
-B buffer_size in units of KiB (1024 bytes
-c count – the limit of packets to capture
-C file_size – the process will create a new file once this file size limit is filled; Size is x 1 million bytes
-d Dump the compiled packet-matching code in ASCII
-dd Dump packet-matching code as a C program fragment
-ddd Dump packet-matching code as decimal numbers preceded with a count
-D List all accessible interfaces
-e Print the link-level header on each dump line
-E spi@ipaddr algo:secret – for decrypting IPsec ESP packets:
spi is the Security Parameter Index
ipaddr is the destination address on the packet
algo is the algorithm, defaulted to des-cbc and the field is optional.
Possible values are:
- des-cbc
- 3des-cbc
- blowfish-cbc
- rc3-cbc
- cast128-cbc
secret is the ASCII text for ESP secret key. If preceded by 0x, then it is a hex value
-f Print `foreign’ IPv4 addresses numerically rather than symbolically
-F file – use file as input for the filter expression
-G rotate_seconds – period to rotate save file of -w option, will add timestamp to name
-h Print the tcpdump and libpcap version strings, print a usage message, and exit
-H Detect 802.11s draft mesh headers
-i interface – the interface on which to listen, defaults to lowest name alphabetically
-I monitor-mode | immediate-mode – removes buffering
-j tstamp_type – set the timestamp type for the capture to tstamp_type
-J tstamp_precision – set the time stamp precision (micro or nano) default is micro. If tstamp_precision is null, list timestamp types and exit
-K Don’t verify checksums
-l Stdout line buffered. E.g. tcpdump -l | tee dat or tcpdump -l > dat & tail -f dat
-L List the known data link types for the interface, in the specified mode, and exit
-m module – load SMI MIB module definitions from file module.
-M secret – shared secret value for validating with the TCP-MD5 option
-n Don’t convert addresses (i.e. host addresses, port numbers, etc.) to names
-N Don’t print domain name qualification of host names
-# Print an optional packet number at the beginning of the line
-O Don’t run the packet-matching code optimizer
-p Don’t put the interface into promiscuous mode
-Q direction – send/receive direction. Can be in, out, or inout
-q Print less protocol information
-r file – read packets from file. Specify – for standard input
-S Print absolute TCP sequence numbers
-s snaplen – snarf snaplen bytes from each packet, not the default 262144 bytes
-T type – interpret packets as the specified type. Options are:
- aodv Ad-hoc On-demand Distance Vector Protocol
- carp Common Address Redundancy Protocol
- cnfp Cisco NetFlow Protocol
- lmp Link Management Protocol
- pgm Pragmatic General Multicast
- pgm_zmtp1 ZMTP/1.0 inside PGM/EPGM)
- resp REdis Serialization Protocol
- radius RADIUS
- rpc Remote Procedure Call
- rtp Real-Time Applications protocol
- rtcp Real-Time Applications control protocol
- snmp Simple Network Management Protocol
- tftp Trivial File Transfer Protocol
- vat Visual Audio Tool
- wb distributed White Board
- zmtp1 ZeroMQ Message Transport Protocol 1.0
- vxlan Virtual eXtensible Local Area Network
-t Don’t print a timestamp on each dump line
-tt Print the timestamp as offset since January 1, 1970 on each dump line
-ttt Print a delta (micro-second resolution) between current and previous line
-tttt Print a timestamp: date, hour, minute, second on each dump line
-ttttt Print a delta (micro-second resolution) between current and first line
-u Print undecoded NFS handles
-U Packet buffered
-v Slightly more verbose output
-vv More verbose output
-vvv Most verbose output
-V file – read a list of filenames from file. Standard input is used if file is –
-w file – write output to file
-W limit – the maximum number of files to be created by the -C and -G options
-x Print the data of each packet minus its link level header in hex
-xx Print the data of each packet, including its link level header, in hex
-X Print the data of each packet minus its link level header in hex and ASCII
-XX Print the data of each packet, including its link level header, in hex and ASCII.
-y datalinktype – Set the data link type to use while capturing packets to datalinktype
-z postrotate-command – process save files usually with compression, eg -z gzip
-Z user – change the user ID to user and the group ID to the primary group of user
Related post: tcpdump Cheat sheet
Tcpdump parameters
The parameters for tcpdump are also known as primitives. These specify whether the packet capture should only get data sourced from specified hosts. These parameters can also be expressed as conditions using the Boolean operators and, or, and not. You don’t need to put an equals sign (=) between the parameter name and its value and you don’t need to space parameters with punctuation. In each case, you just need a space.
The most commonly used of these parameters is host, which allows you to limit the capture to transmissions from just one source. In each case a device name as a parameter value can be replaced by its address. Where a parameter has a dst version, that variation limits output to just packets that have that attribute for its destination. Parameters that include src look for packets that have the given value in data related to their origin.
Here are the parameter options:
host host_name – also dst host or src host.
Can also be prepended with ip, arp, or rarp
ether ehost – value from /etc/ethers or a number. Also ether src and ether dest.
gateway host – get packets that passed through gateway host
net network_num – source or destination IP includes network_num Also dst net and src net
port number|name – also dst port and src port. Can be with tcp or udp to limit protocol
ip proto protocol – capture IP packets of the named protocol. Name must be in /etc/protocols
ether proto protocol – capture packet of ether protocol type. Options for protocol are a number or:
- ip
- ip6
- arp
- rarp
- atalk
- atalkarp
- decnet
- decdts
- decdns
- lanbridge
- lat
- mopdl
- moprc
- pup
- sca
- sprite
- stp
- vexp
- vprod
- xns
Broadcast Captures Ethernet broadcast packets. Also written as ether broadcast
ip broadcast Captures ip broadcast packets
multicast Captures Ethernet multicast packets. Also written as ether multicast
ip multicast Captures IP multicast packets
decnet host host_name – if either the DECNET source or destination is host_name
decnet src host_name – capture if DECNET source is host_name
decnet dst host_name – capture if DECNET destination is host_name
wlan host ehost – if the first, second, third, or fourth IEEE 802.11 address is ehost
wlan addr1 ehost – capture if the first IEEE 802.11 address is ehost
wlan addr2 ehost – capture if the second IEEE 802.11 address is ehost
wlan addr3 ehost – capture if the third IEEE 802.11 address is ehost
wlan addr4 ehost – if the fourth IEEE 802.11 address is ehost. Only used for WDS
type type – capture if the IEEE 802.11 frame type is type, which is a number or:
- data
- mgt
- ctl
subtype subtype – capture if the IEEE 802.11 frame is subtype, which is a number or:
- assocreq
- assocresp
- reassocreq
- reassocresp
- probereq
- proberesp
- beacon
- atim
- disassoc
- auth
- deauth
- data
dir dir – capture if the IEEE 802.11 frame direction is dir, which is a number or:
- nods
- tods
- fromds
- dstods
Tcpdump expression
The expressions segment of a tcpdump command allows you to add a little programming to your packet selection. Unlike a regular program, however, this set of instructions has to be written in one line. If you are a frequent user of Unix or Linux, you will be used to the regular expressions of shell scripting and should have no problems understanding the format of these filters.
Packets that meet the test laid down by the expression will be captured. So the result of each expression has to be “true”.
There are a few expression conditions that are not generally encountered in shell scripting and these are listed below:
len
This returns the length of a packet. Usage example: len != 5.
proto[expr:size]
In this object:
proto is the name of a protocol layer. It can be:
- ether
- fddi
- ip
- arp
- rarp
- tcp
- udp
- icmp
expr is the byte offset. This needs to be included, but it can be given as 0 in order to take the value from the beginning of the object.
size is optional and it represents the number of bytes in the option. The default value is 1, but it can also be 2, 3, or 4.
Usage examples:
ether[0] & 1 != 0 is true for all multicast traffic.
ip[0] & 0xf != 5 is true for all IP packets with options.
ip[6:2] & 0x1fff = 0 is true for unfragmented datagrams and frag zero of fragmented datagrams.
Tcpdump examples
In all of these cases, the results of the command will show on the screen, unless a file-related option is included or unless the command is launched with a stand output redirect, or pipe to a file.
Display packets traveling from or to the computer identified as lab1:
tcpdump host lab1
Display all IP packets travelling between lab1 and any node other than reception:
tcpdump ip host lab1 and not reception
Display all ftp traffic through internet gateway styx:
tcpdump ‘gateway styx and (port ftp or ftp-data)’
Display the SYN and FIN packets of each TCP conversation that involves a non-local host:
tcpdump ‘tcp[tcpflags] & (tcp-syn|tcp-fin) != 0 and not src and dst net localnet’
Display IP broadcast or multicast packets that were not sent via Ethernet broadcast or multicast:
tcpdump ‘ether[0] & 1 = 0 and ip[16] >= 224’
Tcpdump output format
The record format used to write network packets to files has become a standard that has been adopted by many newer packet sniffers and traffic analyzers.
The standard is not straightforward and is adapted for each protocol. However, those applications that have adopted the format also account for these variations. The format is called pcap, which is the name of the packet capture process used by tcpdump. Files in this format usually have the .pcap extension.
Tcpdump for Windows
There is an adaptation of tcpdump that runs on Windows. This is called WinDump and it relies on WinPcap for packet capture in the same way that tcpdump uses the pcap function of libpcap. WinPcap is actually owned by Riverbed Technology. This same company is the primary funder of Wireshark, which is probably the most famous and widely-used packet sniffer in the world. There is a wireless version of WinPcap, which is called AirPcap. You can download WinDump, WinPcap, and AirPcap for free from the WinPcap website.
Using packet sniffers
The tcpdump command line utility is useful for those who are familiar with the Unix and Linux operating systems and enjoy writing shell scripts. Those who are not so experienced at putting together commands with regular expressions at the command line will find it difficult to use this program.
You have other options because there are many packet sniffers available, such as Wireshark, which was mentioned above. You can find out more about alternatives to tcpdump in this review of packet sniffers.
Do you have a favorite packet sniffer? Are you a fan of tcpdump, or do you prefer more user-friendly alternatives? Leave a message in the Comments section below and share your experiences.
tcpdump FAQs
What is the difference between Wireshark and tcpdump?
Both Wireshark and tcpdump capture packets. On that level, both of these tools are the same. However, Wireshark has a DUI interface that includes packet analysis functions. Tcpdump is a command line utility. It has fewer features and it is harder to use.
How do I kill a tcpdump process?
Usually, entering Control-C will stop the tcpdump process. If that doesn’t work, find the process id of the tcpdump process with the ps -aux command, then type in kill -9 followed by the process ID and hit return.
Where are tcpdump files stored?
Unless you specify a directory and file name where tcpdump records should be stored, the file will be written to the directory that you were in when you ran tcpdump. You can specify where tcpdump should store captured packets with sudo tcpdump -i 1 -w followed by the path and filename.
Image: tcpdump packet capture by Linux Screenshots via Flickr. Licensed under CC BY 2.0



