The shift toward hybrid working means that more people than ever are using their own devices for work. This is a trend that’s likely to continue. But what are the risks of a Bring Your Own Device (BYOD) policy and how can they be mitigated? We find out.
BYOD security risks
Loosely defined BYOD policies pose serious security risks. According to Microsoft’s 2023 Digital Defense Report, between eighty and ninety percent of the previous year’s ransomware attacks originated from unmanaged devices. These devices are typically lacking in the security measures needed for a workplace environment – making them an easy target for attackers.
Unfortunately, relatively few companies stipulate what’s required from people using their own devices for work. One survey of a 100 European organizations found that 49% of them had no formal Bring-Your-Own-Device (BYOD) policy in place.
Getting started – Who, What, When, and Where?
Every organization has its own approach to BYOD and will need to implement custom protection in line. How is BYOD practiced in your workplace? What devices are being used, and by Whom, When, and Where?
Mulling over these considerations – Who, What, When, and Where – is the first step in formulating rules that can help balance the risks of BYOD against the benefits for both your organization and your employees.
The benefits are substantial. These include more satisfied employees, lower hardware costs, and increased mobility and productivity for remote workers. In its heyday, BYOD was smart, practical, cost-effective, trendy, and super employee-friendly. IT departments were saving money. Employees loved working with tools they knew without the need to micromanage their digital lives.
It’s not that the wheels then fell off, but as cyber attacks increasingly made headline news, a curious ambivalence towards BYOD set in that is still ongoing today. Organizations realized they had to start weighing up security costs against the value BYOD brought to the company’s financial bottom line.
- Interested in BYOD implementation? See our ultimate guide to BYOD
What are the risks of BYOD?
Besides the technical challenges, security and privacy are the primary BYOD risks. Technical challenges include connecting to wi-fi, accessing network resources like shared files or printers, and addressing device compatibility issues.
Security and privacy are risks faced by both organizations and employees in different ways. Organizations tend to be more concerned about the security of corporate data (and how user behavior threatens it). Employees are more concerned about the privacy and confidentiality of their personal data (and what rights their employers have to access it).
Security risks
- Local exposure – Loss of control and visibility of the enterprise data which is being transmitted, stored, and processed on a personal device. One of the inherent downsides to BYOD.
- Data leakage – Potential data leakage or disclosure of enterprise data from an unsecured device.
- Data loss – Physical loss or theft of a device (and thereby loss or compromise of sensitive data).
- Public exposure – Susceptibility to man-in-the-middle attacks and eavesdropping at public wi-fi hotspots often used by remote workers. Connecting to personal area networks, e.g. using Bluetooth, poses similar security risks.
- Insecure usage – Unacceptable use of a BYOD by a third party, e.g. friends or family at home
- Malicious apps – Devices with compromised integrity. An example is applications with different levels of trust installed on the same device. For instance, allowing push notifications or enabling location-based services. A malicious application may be able to sniff, modify, or steal inter-application messages thereby compromising trusted applications on the device. In addition, even apps from official app stores may be compromised.
- Rogue apps – By gaining root access to mobile devices, there’s a risk that users (aka “rogue employees”) can bypass security restrictions. In some cases, they may install rogue apps.
- Cross contamination – Just one of the (many) risks of having personal and corporate information housed on the same device. Corporate data may be accidentally deleted.
- OS-specific security customization – “Jailbreaking”, “root”, and “unlock” are three popular procedures that users may execute on personal devices to remove vendors’ configuration restrictions. This makes them more vulnerable to insecure applications. They may be able to access device sensors (e.g. microphone, camera) or sensitive data stored on the device without restrictions.
- Insider attacks – Vulnerability to insider attacks which are difficult to prevent since they occur in the local area network (LAN) of an organization using a valid user profile
Privacy issues
Because BYODs access company servers and networks, companies can legally access them. Initially, employee concerns around privacy were Big Brother-type ones. These concerns included whether companies would have the ability, and right, to snoop into private correspondence and curtail the way they used the internet privately, e.g. accessing social media sites.
But experts pretty much agree, employers aren’t all that interested in what employees are doing in their spare time. They’re more interested in whether what they are doing can in any way compromise the company’s security. It’s pretty clear that there’s a fine line when it comes to how deeply organizations can, should and need to delve into personal data.
Consider the following:
- Litigation – Employees mobile devices may be subject to discovery request in the context of a litigation involving an organization.
- Personal data loss – A company’s BYOD security may rely on software that doesn’t make a distinction between personal and corporate data. So, if there’s a perceived security breach, everything on the device – personal and corporate – may automatically be deleted (called remote wipe). This is a bit tough if you didn’t back up the videos of the birth of your first child.
- Big Brother – While not intentionally doing so, a company’s IT department will most certainly be able to track an employee’s physical location at all times and be aware of their online activity.
Security and data privacy stakes are arguably highest in the healthcare industry. That’s because patient data is a particularly lucrative targets for cybercriminals. Data at risk includes medical histories, insurance and financial data, and personally identifying information.
BYOD security technologies roundup
Here’s what you need to know about some of the potential weapons in your arsenal.
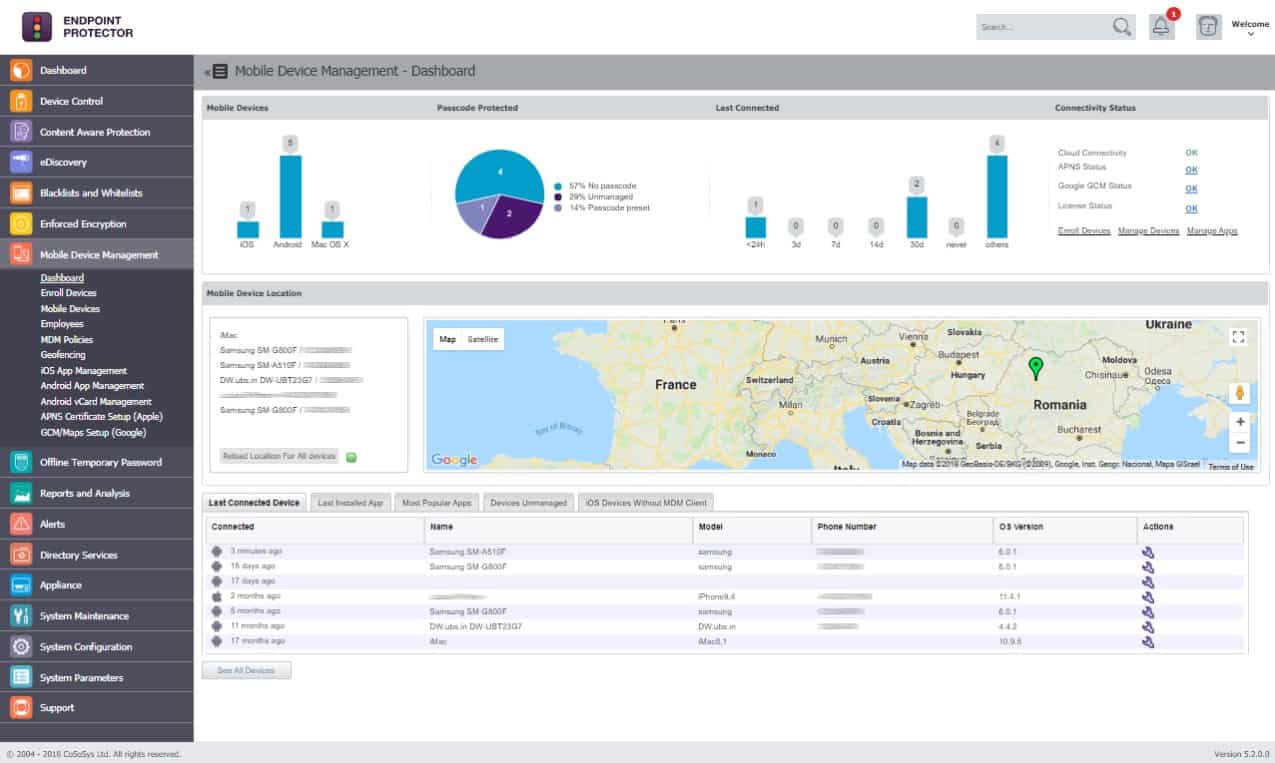
Mobile Device Management (MDM)
Mobile Device Management (MDM) is usually the first port of call for BYOD security. But, remember that BYOD is an ownership model. MDM – and Mobile Application Management (MAM) – are simply types of software companies can buy and use to help secure BYOD.
Organizations can easily implement a 3rd party MDM system. It can do things like remotely wipe all the data from a phone, or locate a phone if it has gone missing. MDM is also great at data segregation. Sharing work and personal contacts in the same address book, for example, creates a high risk of data leakage.
It is lamentably easy to incorrectly select a personal contact as a recipient and accidentally post sensitive company information. Bear in mind that MDM works best in conjunction with Network Access Control (NAC) software (see Next Gen Network Access Control (NAC) below.)
Enterprise Mobility Management (EMM)
EMM is similar to MDM. The main difference is that MDM manages all the features of the device while EMM manages the entire device.
BYOD 1
MDM systems managed devices in the BYOD 1 era. Over time, IT gurus identified real problem with BYODs and changed their strategy. The problem was the disparate risk posed to employees and organizations by having corporate and personal data on the same phone. Employees balked at the threat to their privacy and organizations worried about security breaches of corporate data.
BYOD 2
Enter BYOD 2 and Mobile Application Management (MAM). MAM managed applications rather than entire devices. Employees could feel their personal data was private and they had control over their devices (heck, they paid for them, didn’t they?) For their part, organizations now needed only to worry about the control, management and security of enterprise data and applications, rather than personal content.
Mobile Application Management (MAM)
But does MAM work? One issue is that it’s difficult for MAM to manage apps from official app stores. To solve this issue, MAM vendors attempted to “wrap” regular off-the-shelf apps with their own layer of security, encryption, and control.
The problem is that in order for an IT department to “wrap” an iOS or Android app, they have to get the app’s original package files from whoever wrote the app. But most app developers really don’t like to give these files away.
Alternatively, MAM vendors wrote their own secure versions of the apps users wanted to download. This defeated the object somewhat. After all, one of the benefits of BYOD is the freedom to use one’s device in the way one is accustomed to using it. This was one of the driving forces behind the trend to BYOD.
Companies like IBM who issued free Blackberrys soon realized that employees preferred, and were more comfortable with, their personal iOS and Android devices.
Virtual Hosted Desktop (VHD) Containerization
VHD creates a complete desktop image that includes the operating system, all applications, and settings. Any machine can access the desktop, with processing and storage taking place on a central server. An example is Office 365.
For remote workers, the main problem with this model was less than ideal performance. It only worked for basic office applications like word processing, spreadsheets, and basic messaging.
VHD containerization places native applications inside a safe zone on a device. It effectively isolates and protects them from certain functions, such as wireless network connections, USB ports, or device cameras. The main problem with VHD containerization is the security issues inherent in client-side storage.
Next Gen Network Access Control (NAC)
In the old days, Windows servers easily controlled static user machines and were very restrictive. Today, controlling network access is more complicated because of having to deal with wireless BYODs using different operating systems.
Modern NAC software – called Next Gen NAC – authenticates users, implements security applications (e.g. firewall and antivirus) and restricts the availability of network resources to endpoint devices in compliance with a defined security policy, specifically for mobile.
NAC is a real stickler for rules and can perform risk assessments based on the Who, What, When and Where attributes of both the user and device. Administrators can create and automatically enforce strict granular access policies.
For instance, a user / device combination that is perfectly legitimate during regular work hours may not automatically receive access to parts of the system after hours. Incidentally, in the industry, it’s often referred to as Role Based Access Control (RBAC).
Next Gen NAC requires that the network recognizes the identity of a user. It only allows them access to the resources that are necessary by applying strict user role rules.
In short, NAC controls the users that access certain types of data. It works best in concert with MDM, which enables organizations to monitor, manage, secure, and apply security policies on employee devices.
Data Loss Prevention (DLP)
DLP is a strategy for making sure that end users do not send potentially sensitive or critical information outside the corporate network. As information is created, DLP tools can apply a use policy for it, whether it is a file, email, or application.
For instance, it could identify content containing a social security number or credit card information. This type of data is called personally identifiable information (PII).
For an example of how a DLP tool will manage the use of sensitive data, we can look at Endpoint Protector by CoSoSys. This includes a data discovery tool that identifies stores of sensitive data, such as PII and company assets, such as working practices or product designs.
Endpoint Protector allows the system administrator to set up different security rules for different user accounts, account groups, or company departments. This provides access to certain types of data to be closely monitored or even restricted, enforcing policies per data type rather than by file location.
The data protection services in Endpoint Protector watch over USB ports, email systems, chat apps, printers, and cloud file storage systems to ensure that sensitive data is not disclosed. CoSoSys lets you access a free demo of Endpoint Protector.
BOYD solution checklist
There are a number of measures organizations can take to mitigate BYOD risks:
- A comprehensive strategy is the best approach, albeit taking cognizance of your organization’s Who, What, When, and Where BYOD usage. Comprehensive should include pairing solutions that work best when implemented in tandem, like MDM and NAC.
- In addition, solutions should include practical rules that aren’t intrusive or petty. For instance, if your DLP tool identifies an outgoing email that contains the word “confidential” it may be overkill to wipe a user’s message outright. Instead, flag it for a follow-up investigation. (See Remote wipe below.)
Remote wipe
Remote wipe is the facility to remotely delete data from a device. This includes overwriting stored data to prevent forensic recovery, and returning the device to its original factory settings so any data is inaccessible to anyone, ever.
Widely reported on the internet at the time with some amusement was an incident involving Mimecast CEO Peter Bauer’s daughter. While playing with her father’s smartphone on their vacation, she entered several incorrect passwords. This resulted in the phone’s remote wipe feature activating, deleting all of the photos he had taken on the trip.
Although a remote wipe feature is a useful security measure to protect data on a lost or stolen device, using it can result in an employee’s data being unnecessarily erased. The solution: organizations need to create a security balance between personal and work usage of BYOD devices. When alerted to a potential security breach, rather than automatically wiping a device’s data, security administrators could physically confirm it was lost or stolen. All it takes is a phone call.
Risk profiling
Organizations need to understand their own requirements for data protection. This is especially true in regulated environments where there may be compliance requirements, and compile a risk profile. For instance, international deployment and compliance requirements are two scenarios where BYOD risk levels are particularly high.
Staying up-to-date
Update operating systems, browsers and other applications frequently with the latest security patches. The Panama Papers debacle was one of the largest data leaks in history, caused, say security experts, by vulnerabilities in outdated software.
Another aspect of staying up-to-date is ensuring that the devices of employees leaving the company are suitably wiped of corporate data. If they aren’t, the risk of any data being breached can continue well into the future.
What happens, for instance, if an ex-employee sells their device? And did we mention the havoc disgruntled employees could cause with access to company secrets and intellectual property? Sensitive corporate data fetches a premium price on the Dark Web.
Isolating data
It’s a good idea to limit access to enterprise data according to the nature of an employee’s job role. This is where Next Gen NAC comes in. Smarter data provisioning ensures minimum necessary access to sensitive data. In addition, segregation and VPNs can prevent sensitive data from being leaked via dodgy public wireless hotspots after hours.
Device tracing
Don’t underestimate the value of the good old-fashioned key and padlock security strategy. Coca-Cola suffered several data breaches when an employee stole many laptops over the course of several years. Coca-Cola didn’t even notice the laptops had been stolen.
The solution is for companies to implement a strict device tracking policy. This way they always know the whereabouts of all company devices whether in use or not. Another good practice is implementing a surveillance system that can monitor all devices entering and leaving company premises. Include visitors’ devices in the surveillance system.
Putting it all together
ManageEngine Mobile Device Manager (MDM) is an example of commercially available systems that implement BYOD. This service installs a portal on the user-owned devices that provides a list of authorized applications that the user is allowed to access.
This is a containerized system so corporate data doesn’t touch the operating system of the device. The administrator can place controls over what the user can do with the data. For example, the app can block emailing or printing of data.
App delivery is protected by VPNs. This service includes an authentication step, so lost or stolen devices don’t result in strangers getting access to corporate resources. The security feature of the MDM isn’t able to wipe the mobile device. However, the administrator is able to suspend access to the portal, so the device just ends up with an icon that leads to nothing if it is stolen.
Mobile Device Management Plus has many more features for fleet devices. The package is available in three editions: Free, Standard, and Professional. BYOD capabilities are included in all three editions. The free service is limited to managing 25 devices. The system is available as a cloud-based SaaS package or as a software package for Windows Server. You can assess either version with a 30-day free trial.
Curtailing the rogue employee
The rogue employee is a unique creature in the urban jungle. Or at least s/he believes they are. This is the person who is not obliged to follow society’s rules as the rest of us are. For instance, this person may believe they drive better when under the influence of alcohol. In the workplace, they are likely to have a similar scant disregard for policies and rules.
TechRepublic way back in 2013 reported that forty-one percent of US mobile business users had used unsanctioned services to share or sync files. Eighty-seven percent admitted they were aware that their company had a document sharing policy that prohibited this practice.
Data breaches at their lowest level are due to human error. One of the solutions is regular, intensive security training for all roles, from CEO to tea maker. Which brings us to security awareness.
Security awareness training
Also reported by TechRepublic was the story about the security team at a non-profit organization that found out several teams using Dropbox without IT authorization had recently been hacked.
The team, very sensibly, contacted Dropbox. They told the CSR over the phone that they wanted to know more about how their organization had been using the platform. The phone rep volunteered more data than they had expected, telling them: “We have a list of 1600 user names and their email addresses. Would you like that list?”
The cloud-storage vendor was clearly most interested in upselling them the enterprise version, and was willing to share a customer list without even authenticating the person who called. The rep was enrolled on a security awareness training course after this incident … we hope.
If it isn’t written down, it doesn’t exist
According to an AMANET survey, a whopping forty-five percent of employers track content, keystrokes, and time spent at the keyboard. However, to put this into perspective, eighty-three percent of organizations inform workers that the company is monitoring content, keystrokes and time spent at the keyboard.
Eight-four percent let employees know the company reviews computer activity, while seventy-one percent alert employees to e-mail monitoring.
When it comes to BYOD, companies need to develop acceptable use policies and procedures that clearly communicate boundaries. They should explicitly describe the consequences of policy violations.
BYOD requires mutual trust between an organization and its employees – data security on the one hand, and the protection of personal information on the other. But this is of little consequence when a data breach leads to litigation.
Enterprises must institute a formal registration and provisioning process for employee-owned devices before allowing access to any enterprise resources. Employees need to acknowledge they understand the rules of the game.
What should be included:
- Acceptable use, including social media access
- Security procedures (like password updates and encryption) and incident response guidelines
- Financial terms of use (reimbursements, if any)
- Rules covering device and data loss
- What monitoring may take place
- What devices are allowed or not allowed
What’s preventing BYOD adoption – security or ambivalence?
How prevalent is BYOD really?
BYOD first became popular in 2009. However, it didn’t really embed itself in workplace culture to the degree some had predicted. The global pandemic that arrived in 2019 changed all this, affecting a sea-change in how people worked and their attitude toward being in the office.
A 2023 study [PDF] by Cisco, which looked at companies in eight countries, found that BYOD was a “global phenomenon,” with strong evidence of “employees everywhere using own devices for work.” The research found that eighty-nine percent of surveyed IT departments enabled BYOD in some form.
BYOD is a lucrative market, but for whom?
GlobeNewswire reported that the BYOD market was valued close to $30 Billion in 2014, and projected to grow by fifteen percent between 2015 and 2022. Research by Mordor Intelligence claims the BOYD market in 2023 was worth $98.45 Billion, with plenty of growth forecast for the future.
At the time of writing, the US has the largest BYOD market, but this is expected to shift to the Asia-Pacific region in the coming years. You’ll likely already be familiar with the companies profiting from BOYD. These include:
- VMware Inc.
- IBM Corporation
- Oracle Corporation
- Citrix Systems Inc.
- MobileIron Inc.(Ivanti.)
- SAP SE
- Cisco Systems Inc.
- Hewlett-Packard Company
- Verizon Communicatiomns
BYOD alternatives
Choose your own device (CYOD)
CYOD is an increasingly popular option with larger organizations. Unlike BYOD where the user can use any device, organizations have to approve the use of CYOD. Pre-configured devices should provide all the applications necessary for employee productivity.
By deciding which devices its employees can choose from, a company knows exactly what each device’s security provisions are. The company also knows which version of what software each device is running. It can be sure all its own apps and software are compatible and consistent across the company.
Corporately-owned, personally-enabled (COPE)
With the COPE model, companies pay for their employees’ smartphones. The business retains ownership of the devices. Just as they could on a personal device, employees can send personal emails and access social media, etc. The downside is that controls can prevent corporate data from being available on company-issued devices outside of set parameters. This can defeat the object for remote workers.
How do the big guys do it?
For many smaller companies, BYOD seems to be the elephant in the room. What the big guys have in common is a plan, and an eye on the bottom line.
A few Fortune 500 companies – Gannett, NCR Corporation, The Western Union Company and Western Digital – shared their BYOD policies with Network World. They said they made sure to put secure access procedures in place prior to allowing mobile devices onto their LANs.
Their top BYOD security practices were:
- BYOD users have to install corporate-approved anti-virus software
- IT administrators must also be able to access employee BYODs for security reasons. Reasons included conducting remote wipes (called “poison pill” technology) of lost or stolen devices, or to scan for security threats.
- Some companies require employees to use PIN locks on their devices.
- Most companies require users to load their mobile device management (MDM) application onto mobile phones, tablets, and phablets.
- A few companies, like NCR, prohibit use of personal email accounts for business purposes.
- NCR also prohibits the storage of business material or information on internet or cloud sites unless expressly authorized.
Google has a tiered access approach which factors in device state, device attributes, group permissions, and the required level of trust for a particular employee role.
There are four tiers:
- Untrusted – No Google data or corporate services (in general).
- Basic Access – Services with limited Confidential and Need-To-Know data exposure (e.g. campus maps and bus schedules) and HR data for the requesting user.
- Privileged Access – Services with Confidential but not Need-To-Know data (e.g. bug tracking) and HR data with manager level access.
- Highly Privileged Access – Access to all corporate services, including those that contain Confidential or Need-To-Know data.
This approach, explains Google, challenges the traditional security assumptions that private or “internal” IP addresses represent a “more trusted” device than those coming from the internet.
It enables granularly enforced access and gives a precise way of expressing risk thresholds. Users have the flexibility to use a range of devices, and choose less secure configurations for their convenience (such as a longer screen unlock time or removing the PIN completely).
They can also opt into different levels of enterprise management. A user’s level of access to enterprise services will depend on the device, its current state and configuration, and their user authentication.
IBM
At IBM, proper use guidelines exclude a multitude of services employees regularly use on their own devices, but do offer in-house developed alternatives. Regular services include Dropbox, email forwarding, voice-activated personal assistant Siri, and public file transfer programs like Apple’s iCloud.
The problem is, if IBM (or any other company) is going to strip these devices of the very things that attracted users to begin with, chances are, those devices will stop being used for work at all.
Colgate-Palmolive
When Colgate-Palmolive instituted its BYOD program, the company estimated it would save $1 million a year. That’s the cost of license fees it would have had to pay BlackBerry maker Research in Motion if the devices were under corporate ownership.
The bottom line – Who, What, When, and Where?
The trick to dealing with the threats inherent in remote working and BYOD is to have a network which is contextually aware. A context-aware network is one which can identify the source and nature of traffic – by location, type of device, and behavior, e.g. whether it is usual or suspicious.
By identifying potential threats, the system can make an intelligent decision as to how to respond. For example, it might not allow access to a device that is not in the same geographical location as another device belonging to the same user. Or, it might allow limited access to a user logging in over public wi-fi. It may also restrict access to certain files or parts of the company network.
Some things to bear in mind:
- It’s difficult to revoke BYOD privileges in the workplace
- It’s no good throwing the baby out with the bathwater by restricting BYOD to the extent it no longer has the value intended
The lesson: put BYOD into perspective in terms of its value with regards to employee satisfaction versus the security risks. If you decide it’s worth it, configure practical rules to make it work.



Thank you for your article. I would like to add that the vulnerabilities you are describing can also be found outside the corporate environment. Bad actors have applied the same model on private victims by enabling various MDM/EMM solutions on private devices (not for enterprise purposes) without the victims’ consent or knowledge that their phones are being managed.
In some cases, malicious MDM solutions allow attackers, with previous physical access to the devices, to remotely control all aspects of the phones. This includes creating hidden users on the devices and installing fake system apps, such as Google Play Services, which enable the sideloading of all user applications. The malicious MDM allows total remote access, control, and management of all aspects of the digital life of the victims.
From my own experience, the compromised devices included a Samsung S21+5G and a OnePlus Nord 10. Despite several factory resets and security measures, the malicious MDM persisted, leveraging hidden user profiles and unauthorized apps to maintain control. Here are some specific examples and analysis from my devices:
Persistent Unauthorized Apps and Services:
On my Samsung S21+5G, unexpected apps like com.hicloud.android.clone were present, and persistent Knox-related services were found on my OnePlus Nord 10, indicating unauthorized MDM configurations.
Creation of Hidden User Profiles:
The malicious MDM created hidden user profiles on the devices. For example, apps I uninstalled under my user profile were still present under hidden guest users. This allowed the attackers to re-establish control and maintain their malicious activities even after factory resets.
Simulated Wearable Interactions:
Despite not owning any wearable devices, my devices had persistent wearable-related services active. For instance, logs showed activities such as com.google.android.gms.wearable.DATA_CHANGED and com.google.android.gms.wearable.MESSAGE_RECEIVED, indicating that the MDM was simulating wearable interactions to maintain its presence and functionality.
Data Synchronization and Monitoring:
The MDM enabled extensive data synchronization and monitoring. On my OnePlus device, activities such as FitRecordingBroker, DataUpdateListenerCacheService, and FitnessSyncAdapterService were running, despite no physical wearables being used. This indicates unauthorized data collection and synchronization facilitated by the MDM.
Google Accounts Exploitation:
Multiple Google accounts were involved in unauthorized sync activities for Google Fit and other services. For instance, logs showed active fitness services and queried packages, suggesting the MDM leveraged these accounts for extensive data monitoring and synchronization.
Notification Manipulation:
Enterprise and BYOD Configurations:
Logs showed entries related to enterprise license policies, enterprise MDM services, and BYOD configurations (com.google.android.apps.work.clouddpc.CONFIRM_PROVISION_AS_BYOD). This indicates that the MDM was set up to manage the device as if it were part of an enterprise environment, possibly to evade detection by leveraging legitimate enterprise features.
Samsung-Specific MDM Services:
Detailed logs from my Samsung device included services like com.sec.enterprise.mdm.services.simpin and com.sec.enterprise.knox.cloudmdm.smdms, showing that the MDM was deeply integrated into the device’s operating system, using Samsung’s enterprise management capabilities to maintain control.
These malicious actions not only compromised the security of my devices but also aimed to access sensitive data, including financial information. The attackers used sophisticated methods to maintain control and evade detection, illustrating the severe risks of unauthorized MDM solutions on personal devices.
These attacks highlight the need for enhanced security measures even on personal devices, as the traditional boundaries of BYOD vulnerabilities have expanded beyond the corporate realm