The “bring your own device” concept has been around since 2004, so it is not exactly a new trend. However, the significance of BYOD has increased exponentially in recent years, made more cogent by the increase in the use of freelance specialists and the market saturation of mobile devices, such as tablets and smartphones.
Although the cost benefits of encouraging employees and visitors to supply the equipment they need for work are clear, the security risks of allowing access to corporate resources from private devices discourages many businesses from adopting the policy.
Here is our list of the best BYOD solutions & software:
- ManageEngine Mobile Device Manager Plus (EDITOR’S CHOICE) This suite of mobile security services includes application, device, and email management functions as well as device management. Available for both on-premises installation or as a cloud service. Get a 30-day free trial.
- Omnissa Workspace ONE UEM A cloud-based endpoint management package that manages both workstations, mobile devices, and IoT.
- BlackBerry UEM A package of endpoint management services that includes BYOD management and the control of company-owned devices. Download onto Windows Server or access the SaaS version.
- Citrix XenMobile Mobile device management from one of the major virtualization providers.
- N-able N-sight A remote monitoring and management tool that includes the ability to monitor, manage, and secure smartphones and tablets.
- Cisco Meraki A unified endpoint management system that can be tailored to just cover mobile devices.
- Microsoft Intune A cloud-based unified endpoint management system that will implement a BYOD policy.
- SOTI MobiControl Covers IoT devices as well as phones, tablets, and laptops. Runs on Windows.
- Miradore Mobile Device Management A cloud-based mobile device manager available in free and paid versions.
- Jamf Now A mobile device manager for iOS devices that is free for up to three devices.
- BeachheadSecure A cloud-based unified endpoint management service that includes support for iOS and Android device management.
Despite the cost savings of BYOD, businesses in developed economies have a lower rate of BYOD than those in developing countries. North American and European businesses tend to be more risk-averse than businesses in Brazil, India, and the Middle East because they are more likely to be the targets of cyberattacks.
Thus, in countries such as Russia, Brazil, and the UAE, 75 percent of workers were using their own personal devices at work by 2013, whereas in the more developed nations, that rate was only 44 percent.
Knowledge is power, so in this guide, you will learn more about BYOD. You will discover the risks that you can face when you allow employees and visitors to connect to your network with their own equipment, and you will find out how to protect your business against those threats. Once you have a solid understanding of the risks and the strategies that mitigate those problems, you will have more confidence to decide whether to reap the benefits of a BYOD policy.
Benefits of BYOD solutions & management software
Although there are many risks involved in BYOD, companies are starting to implement this policy, so there must be benefits that you could reap by following the trend.
The main financial benefit of BYOD is that it cuts out the cost of buying equipment. The cost of reassigning laptops and personal devices also has to be taken into account.
So, the cost savings are greater for companies that expect to have a high turnover of staff or depend on a lot of temporary staff.
Start-up businesses can reduce the amount of capital needed for equipment by encouraging employees and collaborators to bring in their own equipment. If you don’t own the equipment that your workers use, you don’t have any responsibility for replacing outmoded models with the latest technology. You do, however, need to take responsibility for the firmware and potential security risks of those devices and that task requires the technical assistance of specialized software.
Businesses that frequently organize events on the company site would also benefit from the policy because making a network available to visitors would aid collaboration. If you want to show potential clients around your premises, you want to be welcoming and allow them to connect to your network, but you also need to show that your company has tight security, so managed BYOD is a lot more preferable than a free-for-all.
BYOD physical security risks
You have two categories of challenges when you begin a BYOD policy:
- Employees bringing their own personal devices into the office
- Employees out in the field who want to attach to the network from their remote location
Of these two access models, the remote access scenario presents more risk to the company because there is a problem of physical security in addition to the complications of device data integrity.
Sales teams are particularly proficient in using smartphones to make quick calculations, write down reminders, and store contact details. They will probably already be using their own device for company business if you haven’t provided them with one from the company.
However, meetings often over-run and salesmen can be in a rush to pack up and move on. They get distracted on the metro and rush off at the last minute at their stops. Those devices often get left behind.
A mislaid, lost, or stolen laptop, smartphone, or tablet can seriously disrupt a sales effort just because of loss of the information that is stored on it. If that device also has access to the company network, the thief may quickly sell it to a hacker and then your network and company data has been compromised. This is particularly the case when busy people don’t bother to lock their devices with a passcode.
The physical risks of BYOD may be the major factor that discourages you from allowing employees to use their own devices for company activities. However, as has already been pointed out, they probably are already using their own devices to store their work information, and as they are out in the field, there is little that you can do to stop this habit.
Solutions to BYOD physical security risks
If you can’t stop remote employees from using their own devices, the only option is to embrace the practice and control access to information.
Getting that sales contact information backed up off the mobile device and onto the company CRM system is a priority. Not only does a lost phone lose those sales lead details, but a salesman that gets hired by your competition takes all of that stored data with him. You want to provide online apps that encourage remote employees to store all potentially profitable information on your servers and not on their own devices. So, if they walk, they lose access to all the intelligence that you paid them to gather.
Mobile device management (MDM) systems can track the location of all devices used for the company, no matter who owns them, so BYOD devices can be located as well. You need a system that allows you to lock mobile devices remotely, or wipe all device data should the designated users lose sight of them.
Remote wiping is a common solution for company-owned devices but may prove controversial with BYOD owners. If a survey of employees proves that they would be unwilling to allow all data from their phones to be wiped, there are other strategies that you can employ to ensure your company’s system is not compromised.
BYOD Malware risk
Whether your employees connect to your network within the office or from a remote location, you run the risk of malware spreading from their own devices onto the system.
The malware risks that you face fall into three categories:
- Email risks
- Internet risks
- Wifi risks
When the workers are out in the field, or when they are off the clock, they have every right to take their own laptop, smartphone, or tablet wherever they want and do what they like with it.
Email risks
There are many entry points to a device for a virus. One of the main methods that Trojans use to spread is through email attachments. PDF formats, Word documents, and video in particular pose risks. You are no doubt aware of those risks and have policies in place on your corporate email system to block these forms of attachments. However, those rules don’t apply when the owners of devices access their own email in their own time.
Internet risks
Other virus risks come from “cross-site scripting” (XSS) where hacker code is injected into web pages and downloads onto the device when the page is loaded into the browser. Again, you can block XSS on your own network, but not on the devices of your employees.
Some employees might like to download files with the BitTorrent protocol in their spare time. This is another virus access point.
WiFi risks
Employees are likely to take their devices out with them to restaurants and bars, or to hotels on vacation. They may connect to WiFi hotspots, a popular avenue for hacker intrusion. There is actually an international ring of hackers that specializes in infecting mobile devices while in hotels. The hacker group is called Darkhotel and they infect devices indiscriminately, not just the laptops of national security officials and ambassadors. Any employee with BYOD access to the company network is valuable to Darkhotel, and any company will do.
These hackers operate a form of attack called an “advanced persistent threat“. They will gain access to the company network and gradually break passwords to get into databases and file stores, enabling them to riffle through your product designs, your purchase orders, your sales contacts, and your employee data. No matter how small or mundane your business is, the information contained in your system is valuable to identity thieves. A Chinese hacker group operates a cybercrime infrastructure called the terracotta VPN that provides cover for hackers by running connections through the networks of unsuspecting companies.
These factors may be the major reason that you want to prevent employees from accessing your company network with their own, possibly virus-ridden devices. However, there are solutions to all of these problems.
Solutions to BYOD malware risks
You can’t tell employees what they can and can’t download on their phones. However, you can tell them that they are not authorized to access the network. Your mobile device management system should be able to gain access to the device periodically and sweep it for viruses and keyloggers. If any malware is detected, the system should quarantine the device until it has been cleaned. Jailbreaking is another threat to your company network because it allows access to the underlying kernel of the phone and bypasses the operating system to operate beneath virus protection. You need a system that detects jailbreaking and bans those phones from accessing the network.
You may need the permission of the user to perform a virus clean or restore kernel access restrictions. In fact, it would be better to provide a guide on how the device owner can use company tools to clean the detected viruses off their own phone.
Your network would be better protected if you could control the security policy of the entirety of every device that connects to it. There are two ways to deal with virus protection and communication privacy. You can offer all employees connecting to the network with their own devices free virus protection and VPNs to secure all of their connections at all times, or you can use a method known as containerization.
Containerization and MAM
With containerization, you supply applications through a company portal, possibly in the form of a secure browser. Access to the company network can only be achieved through that portal. You make a VPN available for that app so all communications between the device and the company network will be protected. However, all of the user’s other activities will not be protected.
Mobile application management (MAM) systems take care of these portals. This is similar to virtualization—dumb terminals use the processing power of another computer—and is also the same method that cloud-based apps employ. Containerization keeps company communication and personal use of a mobile device separate. MAM ensures all of the work performed on a mobile device is actually resident on an on-premises server, which can be monitored and controlled.
One more system is available to help you cut down on virus risk. This is mobile email management or MEM. These systems give secure access to the company email system over encrypted connections. Storage only occurs on the company’s own protected mail server. MEMs enforce company policy on emails, such as blocks on downloading attachments.
BYOD Confidentiality risks
All of the factors explained in the physical risk section of this guide also apply to the risk of disclosure of company information.
There are three main types of confidentiality risk:
- Screen visibility risk
- Device loss risk
- Employee action risk
The likelihood of employees using their own device to access the company network through wifi hotspots is very high. People enjoy the status of being needed for their job even out of office hours and will answer calls from work, even if they occur in the middle of the night. Similarly, they will pick up alerts from the network and check in on information even when they are on vacation or out to dinner.
Accessing the company network over the internet gives essential, on-call staff such as IT support specialists the ability to do their jobs around the clock. However, if they access the internet from a restaurant or hotel WiFi system, they run the risk of exposing all of the data that is passed back and forth to a man-in-the-middle attack (MITM).
Screen visibility risk
Employees who can access company information at home might be more likely to leave their laptops running with the screen active while they walk off to the kitchen to make a visitor a cup of coffee. Without needing to enter commands, that visitor would be able to read the open document or take a snapshot of it with his own mobile device. That visitor does not need to be an international industrial spy. However, a neighbor with heavy car loan payments might be interested in selling embarrassing or innovative information to the press.
Device loss risk
The loss of devices is not just an inconvenience in terms of hardware, but it also breaches confidentiality if sensitive company data is stored on it. If your business has operations in Europe, the advent of the General Data Protection Regulation, which is in effect as of May 2018, makes the protection of personal data a critical business need. That information may pertain to employees, customers, or even market research, and if anyone can prove that you have not taken sufficient steps to protect that data, they can sue you and your company will be heavily fined.
Employee action risk
Cash-strapped or disgruntled employees will find it a lot easier to copy over or print files containing sensitive information from home than they would in the office, where their actions could be observed. So, distributing files to be stored on employee-owned devices presents a confidentiality risk. With many employees given access to the same information, identifying the source of an information leak would be difficult.
The loss of confidentiality may discourage you from implementing BYOD. However, many of the risks listed above already exist on your private office network, so you need to address the problems of virus intrusion, internet security, and disclosure by employees anyway. The systems that you need to implement in order to prevent information leakage on employee-owned personal devices will actually strengthen your corporate data confidentiality.
BYOD Solutions for confidentiality risks
If you make business applications available from an application server, using MAM, you can also demand that files be stored remotely and not allow storage of corporate documents and data on employee-owned devices. A number of different security tactics for company data are available through mobile content management (MCM) systems.
If you choose to allow documents to be transferred to the device, then MCM systems can track versions of documents, stamping them, so the source of a leak can be traced to a specific copy of a document. These MCM systems can also disable the text copy functions of apps running on mobile devices and make it impossible to print, copy, or email documents.
Man-in-the-middle theft of information can be prevented by applying a VPN to all official communications. The problem of an employee leaving a document open on a device when they temporarily walk away can be solved by enforcing screensaver locks. The problem of theft or loss of devices is taken care of by the automatic lock and location tracking methods of MDM systems.
MEM systems ensure that your employees’ official emails are protected from snoopers in transmission and at rest on the email server.
There is no technical solution to disgruntled or desperate employees showing company data to third parties. However, making the original document impossible to move goes a long way to blocking anyone having any proof of controversial information. Also, the ability to withdraw the individual’s access to the network effectively ends the risk, particularly if you only allow the central storage of data.
Alternatives to BYOD Management
One easy alternative to the BYOD solution is to ban employee-owned personal devices from connecting to the network. This would be an unpopular move. Surveys report that the hardware cost savings of letting employees use their own devices at work is not the biggest benefit of BYOD. In fact, it doesn’t even make it into the top three.
A 2016 survey by LinkedIn’s Information Security Group and Crowd Research Partners discovered that companies rated increased employee mobility as the main reason they chose to implement a BYOD policy (63 percent), employee satisfaction and increased productivity were the next two top reasons that companies implemented BYOD, with 56 percent and 55 percent ratings, respectively.
If you have considered the risks of BYOD and decided that they outweigh the benefits, then there are some other strategies that you could consider.
Personally owned, company-enabled (POCE)
The POCE acronym is actually just an alternative phrase for BYOD. However, it highlights a successful BYOD strategy. Very fundamental BYOD involves giving the wifi password to employees so they can access the internet at work without having to use their personal phone plan’s data allowance. However, such a strategy would be foolish. The “company enabled” part of this name shows the way.
You need to manage all mobile devices whether owned by the company or owned by the employee. With company-owned equipment, you can take control of the device entirely and ban the user from loading any apps onto it other than those installed by the systems administrator. With BYOD systems, you need to set up a portal that cordons off part of the phone for business use during work hours. The user only accesses the company network through that portal and the rest of the phone is available to the user.
Corporate-owned, personally enabled (COPE)
As the name suggests, in this scenario, the device is owned by the company, but the employee is also allowed to use it for personal reasons. However, the company ultimately owns the phone and has rights over it. This enables you to lock or wipe the phone in emergency situations. The user may lose any personal information stored on the phone, but that situation should be explained at the point of issuance. By this strategy, the company retains the rights over the phone and all data stored on it, even if that information was saved by the user.
Choose your own device (CYOD)
This is a variation on company-owned devices that uses a little marketing savvy to get employees onboard with the idea of using mobile devices for productivity gains. The company will buy devices in bulk and gain special discounts for doing so. Instead of buying all of one model, the IT department buys a range of devices. Each employee is then able to select a device rather than being allocated a model.
This policy can even be presented in the form of a catalogue, which feels like a purchase process and wins the enthusiasm of the employee. Whether the phone should be available for personal calls and internet access is a matter for company policy. However, thanks to automated mobile device management systems, the administration of mobile devices is not made more complicated just because the models controlled by the system are diverse.
In some cases, MDM systems are dedicated to one operating system. In these instances, the specialization usually focuses on iOS devices. However, the exact model of the device is not important even in these environments.
Company-owned mobile devices
If you have decided against the BYOD policy, that doesn’t mean that you can’t involve mobile devices in your IT strategy. A number of industry-specific devices could be used in your service delivery. Barcode scanners and point-of-sales devices fall into this category. Smartphones and tablets can also be used as sales devices. You can restrict the apps that can be loaded onto a device and make it part of a store display or a piece of sales demonstration equipment. This is called “kiosk” mode. In these cases, the user would need to use a separate phone for personal calls and messages.
Enterprise Mobility Management
In earlier sections, you discovered mobile device management (MDM), mobile application management (MAM), mobile content management (MCM), and mobile email management (MEM). You can buy software to implement any one of these solutions or get a bundle of all of them, in which case you need to look for an enterprise mobility management system (EMM).
The good news is that these systems are so comprehensive that you no longer need to worry about employing mobile devices in your business. Whether those mobile devices are owned by the company or owned by employees makes little difference. MDM systems can cope with all scenarios.
The software industry has taken note of the higher risks of including mobile devices in a company network. The possibility of BYOD has created some innovations in the mobile management software market that have raced ahead of traditional network management systems.
Enterprise mobility management systems have become so impressive that you will wish you could have the same level of control for your physical office network and all of its attached devices. You can. If you want EMM for all of your network, then you need to look for unified endpoint management (UEM) systems. They are out there and usually provided by the same vendors that produce EMM systems.
The best BYOD solutions & management software
Comparitech has a special feature on mobile device management systems. However, if you don’t have time to hop over to that other article, here are summaries of today’s recommended top ten MDM systems.
Our methodology for selecting BYOD tools
We reviewed the market for BYOD solutions and analyzed tools based on the following criteria:
- Device risk assessment
- Mobile content management
- Security measures to protect company data from theft
- User authentication
- Options for managing IoT devices
- A free trial or a demo package that enables assessment without paying
- Value for money from a comprehensive service that enables users to connect their own devices to the company network
With these selection criteria in mind, we picked some great mobile device management systems that will enable you to allow user-owned devices onto your network safely.
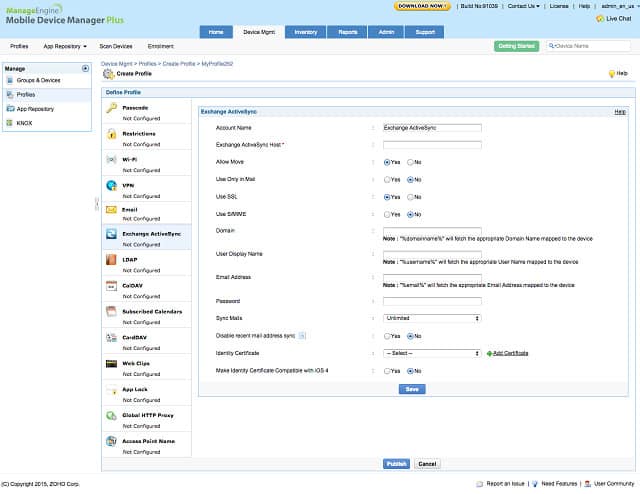
1. ManageEngine Mobile Device Manager Plus (FREE TRIAL)
ManageEngine produces a range of infrastructure management software and the Mobile Device Manager Plus system fits well with the company’s other network and server monitoring packages. You can buy this MDM system as a software package to install in your offices or subscribe to a cloud service.
Key Features:
- Comprehensive Security Scans: Ensures mobile devices are free from vulnerabilities and malware.
- Broad OS Support: Offers robust management capabilities for both Android and iOS platforms.
- Application Protection: Shields corporate applications from unauthorized access and data breaches.
Why do we recommend it?
ManageEngine Mobile Device Manager Plus provides all of the tools that you need to manage user-owned mobile devices and fleet devices. This includes mobile content management, which ensures that the owners of iOS and Android devices accessing your data can’t save copies or forward it to unauthorized recipients.
As well as an MDM, this suite includes mobile application management, mobile content management, and mobile email management, so it is the complete EMM package. The management options include services for BYOD, which starts with an enrollment app to get a device included in the network. If you have company-owned devices, you can configure them in bulk or individually.
Policies can be defined for different groups of devices, making it easy to set separate configuration options for BYOD and company-owned devices. Remote access to all devices is facilitated through the system dashboard. It enables you to view the screen of a device, explore the file system, and run programs to fix problems. You can lock or wipe lost devices remotely. The console is able to locate all devices. The system will periodically test each device, search for malware, and detect jailbreaking.
ManageEngine’s Mobile Device Manager Plus is specifically tailored for personal devices, which makes it ideal for BYOD oversight, but it can be integrated into a wider unified endpoint management strategy. The system is free to use to manage up to 25 devices and it is also available as a cloud service.
Who is it recommended for?
All of the features in the ManageEngine package allow companies to control access to company resources and data. It manages user-owned devices as well as company devices. So, this is a good option for businesses that want to allow BYOD but also need to protect data from theft or unintentional disclosure.
Pros:
- Unified Endpoint Management: Integrates mobile devices into a holistic security framework, covering both personal and company-owned devices.
- Application Access Control: Regulates access to critical applications, maintaining data integrity and security.
- Proactive Threat Detection: Monitors for unauthorized OS interactions and sensitive data access attempts, enhancing device security.
Cons:
- Limited IoT Integration: Lacks management support for IoT devices, potentially leaving a gap in device coverage.
All communication between the device and the network is encrypted, and a fully encrypted email management system is also available. The system is free if you only need to manage up to 25 devices and there is a 30-day free trial for the paid plans.
EDITOR'S CHOICE
ManageEngine Mobile Device Manager Plus is our top pick for a BYOD solution because this system can manage your corporate devices and user-owned laptops, phones, and tablets in a single console. The service offers a range of on-boarding measures, including a self-enrollment option that allows users to connect to your office wireless system. You can also allow users to access your corporate data and apps by providing a portal. This is a single app that provides a locker of apps that you can populate from your central administrator dashboard. Add apps to the locker and also choose to suspend access with just a few clicks. Corporate systems are containerized on the user-owned device, so there isn’t any danger of shadow file copies or other memory leaks leaving corporate data on the device. While allowing secure BYOD usage, this package also has extensive services you managing corporate fleet devices. Those utilities include tracking, remote locking, and wiping.
Download: Access a 30-day FREE Trial
Official Site: https://www.manageengine.com/
2. Omnissa Workspace ONE UEM
Omnissa is a leader in virtualization and the cloud-based Workspace ONE UEM platform includes mobile application management that mimics virtual terminal methodologies. The onboarding of BYOD is carried out by an enrollment app that you make available to the device owner. If you also have company-owned devices on the network, the system enables you to treat these two ownership groups differently through customizable policies. You can check all phones for malware and jailbreaking and quarantining suspicious devices.
Key Features:
- Versatile Cloud Deployment: Operates entirely from the cloud, offering scalable and flexible management capabilities.
- Advanced Virtualization Techniques: Leverages virtualization for efficient application and resource management across devices.
- Secure VPN Connectivity: Integrates proprietary VPN technology to ensure secure connections for mobile and remote devices.
Why do we recommend it?
The Omnissa Workspace ONE UEM system enables users to hop from device to device and they can be desktops or mobile devices and includes both company-owned equipment and user-owned devices. The system has special protection measures for dealing with BYOD that ensure appropriate access without risk.
All communications between the network and the device are encrypted and the more expensive plans include a proprietary VPN, which is called Workspace ONE Tunnel. For user-owned devices, that encryption can be applied just to the apps that access the network. Access control processes use two-factor authentication can include biometric checks. A secure email system is also available with Workspace One .
Remote access to all devices will enable you to troubleshoot and diagnose problems. This facility gives you screen view and the ability to execute programs. Remote control functions all give you the ability to lock or wipe phones and the location of all active devices is tracked live on a map. The option to monitor and limit the use of corporate cell phone service plans comes with the more expensive Workspace One packages.
You provide an app catalog, which can be tailored for groups of devices. The system checks automatically for installed apps that are not on a whitelist.
Who is it recommended for?
Workspace ONE includes a plan to manage desktops, one to manage mobile devices, and one to manage both. The system is cloud-based, so you don’t need to worry whether you have the right operating system to run the package. One problem with this tool is that it can’t manage devices running Linux.
Pros:
- Robust Access Controls: Features comprehensive access controls, including two-factor and biometric verification, to secure device and data access.
- Direct Device Troubleshooting: Allows technicians to access devices remotely for diagnostics and problem resolution.
- Streamlined Device Onboarding: Simplifies the onboarding process for both company-owned and personal devices with customizable policies.
Cons:
- Lack of On-Premises Solution: Does not offer an option for self-hosting, which may be a limitation for organizations with specific compliance requirements.
The Workspace ONE package is available in three service levels and you can get a 30-day free trial.
3. BlackBerry UEM
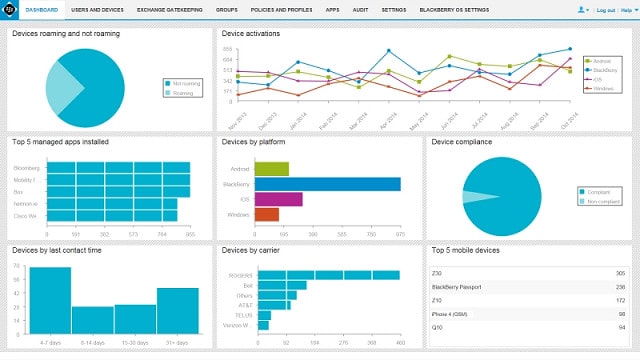 BlackBerry UEM monitors and manages workstations, mobile devices, wifi-enabled equipment, and wearable technology. You can download and install software or opt to use the management system as a cloud-based service.
BlackBerry UEM monitors and manages workstations, mobile devices, wifi-enabled equipment, and wearable technology. You can download and install software or opt to use the management system as a cloud-based service.
Key Features:
- Comprehensive Device Support: Monitors a wide range of devices including BYOD, IoT, and wearable technology.
- Flexible Deployment Options: Available as both a downloadable software and a cloud-based service.
- Integrated Desktop Management: Seamlessly combines mobile device management with traditional desktop oversight.
Why do we recommend it?
BlackBerry UEM provides security for communications between company endpoints wherever they are. The package also provides a containerized delivery system for corporate apps on user-owned devices. This method simultaneously secures company data on all mobile devices. The package also includes tracking, locking, and wiping functions for company-owned devices.
You can configure your own devices en masse, or make secure apps available for user-owned devices. The question of whether users would let you wipe their phones in case of loss is not an issue with the BlackBerry system because it does not include that capability, nor does it include a device location utility. You will be able to access devices remotely, however, and the functions you can perform on all managed devices include locking in case of theft.
Who is it recommended for?
BlackBerry is famous for the security that it offers for its own mobile devices and now applies that security system to third-party equipment, which includes on-premises, company-owned computers. The security system simultaneously offers a method to safely include BYOD on a company network even if they are not actually in the company offices.
Pros:
- Remote Device Management: Enables administrators to access and manage devices remotely, enhancing operational flexibility.
- Enhanced Device Security: Offers device locking capabilities to secure devices in case of theft or loss.
- Efficient Application Distribution: Facilitates the management and distribution of mobile applications, streamlining corporate app usage.
Cons:
- Limited Recovery Features: Lacks the ability to track or wipe devices, potentially limiting response options in case of lost or stolen devices.
Secure email and messaging capabilities are available as an optional extra as is a CRM package. The cheaper package consists of MDM and a basic MAM. To get more comprehensive mobile application management and mobile content management you need to sign up for one of the more expensive plans — there are five different service levels. All of the mobility plans can be assessed with a free trial.
4. Citrix XenMobile
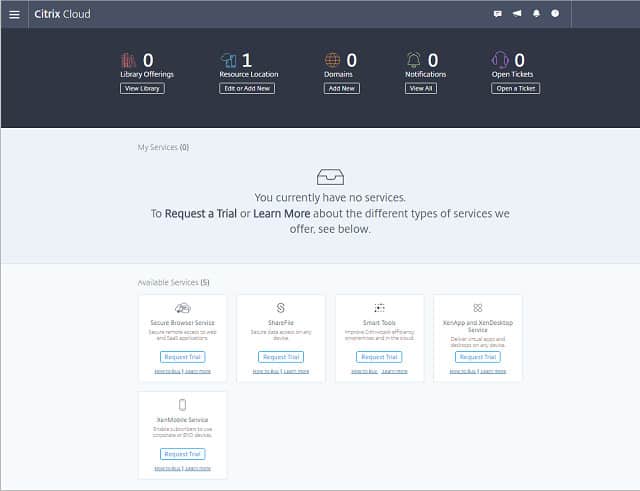
Key Features:
- Advanced Mobile App Management: Offers extensive management of mobile applications, ensuring secure and efficient use.
- Comprehensive Content Management: Enables secure mobile access and sharing of corporate content, safeguarding sensitive data.
- Innovative Virtualized Delivery: Utilizes virtualization technology to provide a seamless user experience across devices.
Why do we recommend it?
Citrix Xen Mobile is very similar to the Omnissa Workspace ONE UEM because it relies on a virtual desktop strategy. This provides a virtual account for each user on a server. Users can then hop from device to device and get uninterrupted service from the applications that they use.
Citrix includes proprietary email, messaging, collaboration, and file-sharing utilities in XenMobile. Include any other app through a technique, called “Wrapping.” This applies a layer of encryption to all communications for that app between the device and the server. If you develop your own in-house apps, they can be made available securely to the mobile devices on your system with the addition of just one line of code.
Citrix has a special procedure for dealing with user-owned devices. This is called a “MAM first” policy. The security of the software applications made available to user-owned devices substitutes for the protection extended to company-owned devices by the MDM system. Nothing is loaded onto the device other than a network login app. Once the owner logs out of that portal, there is no corporate property on the device. This is a great solution to the thorny issue of wiping lost phones. Users can access their account from any device, so they can start a project on their desktop computer and then continue accessing that work from their mobile device when they leave the office.
Who is it recommended for?
This package is part of the Citrix Endpoint Management platform. It doesn’t just take care of BYOD but enables workers to use any device, whether on-premises or out of the office. The users log into a portal, which is based on containerization. The platform doesn’t interact with Linux devices.
Pros:
- Seamless Virtual Machine Access: Allows users to interact with virtual machines via mobile devices, extending the workplace environment.
- No Corporate Data on Personal Devices: Ensures corporate assets remain off user devices, minimizing data breach risks.
- Containerized User Access: Provides a secure, containerized portal for user access, maintaining data integrity across devices.
Cons:
- Preference for VMs Over Containers: Despite leveraging virtual machines for application delivery, the approach raises questions about not opting for container technology.
This is a very sophisticated solution that supports flexible working practices and you can get a taste of it with a free trial.
5. N-able N-sight

N-able N-sight is a SaaS system that provides remote monitoring and management software plus the server to run it on and storage space for RMM-related files. The system includes special procedures for monitoring personal mobile devices and it is ideal for managing a BYOD policy.
Key Features:
- Comprehensive Remote Management: Enables full monitoring and management of devices remotely, ensuring operational efficiency.
- Dedicated Mobile Device Management: Provides robust management tools for mobile devices, supporting BYOD initiatives.
- Efficient Bulk Onboarding: Streamlines the process of integrating new devices into the network, saving time and resources.
- Secure Application Access: Offers a secure portal for accessing company applications from any device, enhancing data security.
Why do we recommend it?
The N-able N-sight remote monitoring and management platform includes a mobile device management (MDM) module. This is able to track, locate, lock, and wipe devices and those devices can be user-owned or company fleet devices. The tool will manage devices running Windows and iOS but not Android.
N-able N-sight enables system managers to onboard devices rapidly. As this is a remote system, those individual devices don’t have to be in one place. So, groups of mobile devices delivered to different sites can all be given a corporate-approved configuration by one central IT department.
User-owned devices can be integrated into the corporate system by loading a portal to company services on them. This access can easily be blocked should the phone be lost or stolen. So, there are two levels of treatment available for mobile devices used for company activities – company-owned devices that can be completely controlled, tracked, and locked or wiped remotely, or user-owned devices that can be given access to company resources, while allowing their normal recreational use by the owner.
Another way to manage access from BYOD devices in the corporate realm is to grant and control access from mobile phones to the office WiFi network. It is possible to create separate WiFi APs for BYOD equipment and company-owned devices, allowing the network manager to vary access rights according to the needs of different user types. For example, guests can be allowed access to a WiFi system to enable them to contact their own base services while in the building, without needing to give them access to the full network and its resources.
Who is it recommended for?
The N-able platform was designed for use by managed service providers because it has a multi-tenant architecture to keep the data of MSP clients separate. However, IT departments could also use the system. Companies that need to manage devices that run Android would need to look elsewhere.
Pros:
- Versatile Device Policies: Supports distinct management procedures for both company-owned and personal devices.
- Streamlined Device Integration: Facilitates easy setup and standardization of devices joining the corporate network.
Cons:
- Limited Compliance Tools: Lacks built-in compliance reporting features, which may require supplemental solutions.
- Restricted Mobile OS Support: Mobile device management does not extend to Android devices, potentially limiting its applicability.
The mobile device management functions can control individual devices running iOS, Android, and Windows Mobile. The dashboard for N-able N-sight is resident in the cloud and it can be accessed from through any standard browser or a mobile app. You can get a 30-day free trial.
6. Cisco Meraki
Cisco Meraki is a unified endpoint management system that monitors all of your office equipment as well as mobile devices. However, you can structure your service so that it only monitors mobile devices. It works with Windows, macOS, Windows Phone, iOS, Android, Chrome OS and Samsung Knox operating systems.
Key Features:
- Extensive Endpoint Coverage: Monitors a wide array of devices, including mobile and office equipment, across various operating systems.
- Simplified BYOD Enrollment: Enables easy self-enrollment for user-owned devices, facilitating BYOD policies.
- Integrated Corporate Services Portal: Provides a centralized portal for accessing corporate services, enhancing user experience.
Why do we recommend it?
Cisco Meraki takes a Zero Trust Access (ZTA) approach to user access management, which easily extends to user-owned devices. The service checks each device as it connects to the corporate network and blocks those that have security issues. From that point, connection security and application access rights management take over.
BYOD inclusion starts with an enrollment process performed by the device owner. Company-owned devices can also be added to the system and configured in bulk. Configuration options can be managed by groups, allowing you to set different policies for groups of users or types of devices.
Meraki has a great device tracking feature that shows the current location of all equipment on a map. Lost devices can be locked or wiped. Meraki is able to monitor call and data plan usage. It is possible to limit corporate account usage for devices that show excessive consumption or those that have been lost or stolen.
Who is it recommended for?
This service packages together application and data access control that is allocated to a user, regardless of device. Like many of the other UEMs on this list, it can’t interact with the Linux operating system. However, iOS and Android mobile and laptops running Windows, Chrome OS, or macOS can be managed.
Pros:
- Application and Data Segregation: Efficiently containerizes applications and content, securing corporate data.
- Comprehensive Device Management: Offers robust features for both personal and company-owned devices, including tracking and remote wipe.
- Effective Resource Monitoring: Tracks and manages call and data plan usage to prevent excessive consumption.
Cons:
- Biased Feature Set: Delivers more comprehensive functionalities for company-owned devices than for personal devices, potentially limiting BYOD flexibility.
The mobile application management and mobile content management functions of Meraki are combined in a system called Backpack. The administrator bundles together software applications and data storage and then makes that package available to a group of users. Different application bundles cater to different work roles.
7. Microsoft Intune
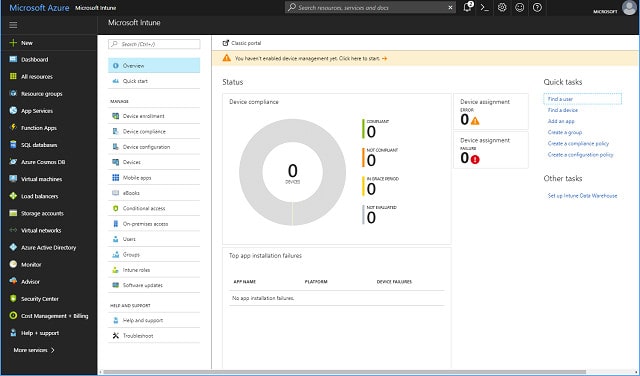
Key Features:
- Cloud-Based Flexibility: Offers a cloud-based solution for managing both computers and mobile devices across multiple OS platforms.
- Comprehensive Device Management: Provides the tools to manage both company-owned and personal devices with ease.
- Versatile Policy Implementation: Enables granular control over devices with customizable policy options for enhanced security.
Why do we recommend it?
Microsoft Intune combines connection security with access to Microsoft SaaS services. This is a Zero Trust Access solution that blocks connections if they don’t come from an authorized user. There are three levels of service for this package and that basic system just adds connection security to Microsoft 365 access.
User-owned devices can be treated differently to company-owned equipment. An enrollment package allows users to enlist their devices. Within Intune, policy options give you control of the whole phone or just deliver secure apps to a device. The latter is probably a more palatable option for BYOD.
Security features include location of lost or stolen devices (only for iOS), remote locking, and phone wiping. There is no remote access function with Intune, which may make this system preferable for BYOD scenarios. However, it is possible to scan all mobile devices for unauthorized apps and malware. In the case of app-only access, these functions would not be relevant, leaving responsibility for the rest of the device to the owner.
Who is it recommended for?
If you use Microsoft 365 for your company’s productivity suite, your users can access that SaaS package from any device, including their own. Focusing BYOD on one application suite that is delivered from the cloud certainly makes BYOD management very easy. Your users’ devices can be running any operating system, including Linux.
Pros:
- Flexible Management Options: Allows the choice between managing the entire device or simply deploying secure apps, catering to BYOD preferences.
- Simplified User Enrollment: Facilitates easy self-enrollment for personal devices, streamlining the BYOD integration process.
- Pre-Connection Security Checks: Ensures devices are scanned for security risks before connecting, maintaining a secure network environment.
Cons:
- Limited Higher Security in Basic Plan: The basic Intune plan offers essential functions, with more advanced security features and application management reserved for the higher-tier E3 and E5 plans.
Intune is the lower level of a three-level service. The higher plans are called E3 and E5. These two packages have stronger security features than Intune and better application delivery systems. Mobile content management and secure email are only available with E3 and E5.
Microsoft offers a 90-day free trial for Intune, E3, and E5.
8. SOTI MobiControl
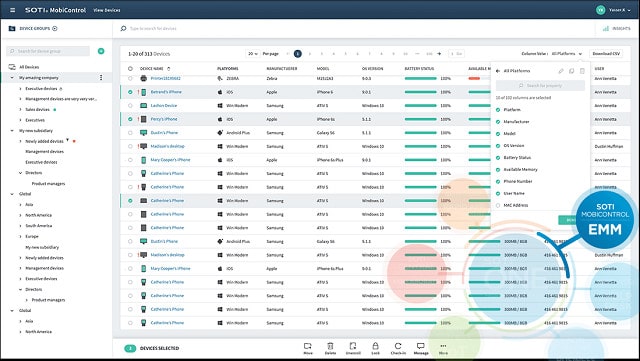
Key Features:
- Flexible Enrollment Options: Supports multiple enrollment methods for device management, offering versatility in device integration.
- Scalable Distributed Architecture: Features a distributed system architecture for effective management of devices across locations.
- On-Premises Solution: Delivers a self-hosted platform, giving companies control over their mobile device management infrastructure.
Why do we recommend it?
SOTI MobiControl just focuses on mobile devices – it isn’t a UEM like many of the packages on this list. It is an Enterprise Mobility Management (EMM) package. It is able to manage IoT devices as well as mobile devices. The availability of apps on a device can be blocked, according to physical location.
MobiControl can manage the entire mobile device or restrict network access to specific apps, leaving the user-owned device available for out-of-office private use. Although you can configure devices centrally and bulk configure company-owned devices by group, there is a self-enrollment package that allows users to enroll phones themselves.
The client software available with SOTI includes a secure browser. This is the access method for BYOD scenarios, delivering apps to devices not owned by the company. File storage is kept off the device, making the risk of loss less critical. The mobile content management module of MobiControl is called SOTI hub and keeps all files on a central server. All file access is logged.
The management dashboard includes remote lock and wipe functions. The central administrator can remotely access managed devices, which gives a view of the screen and the ability to execute programs in order to fix problems.
Who is it recommended for?
SOTI MobiControl offers a self-service onboarding system that works for both corporate-owned devices and BYOD. Content is held on a central server and users get a view of it rather than transferring data over. So, this is a good package for businesses that need to comply with data protection standards.
Pros:
- IoT Device Inclusion: Extends management capabilities to include IoT devices and specialized industry equipment, broadening device coverage.
- Dynamic Application Control: Allows for location-based app accessibility, enhancing security and user experience.
- Centralized Content Management: Utilizes SOTI Hub for secure, centralized file storage and access, maintaining data integrity and compliance.
Cons:
- Focus on Corporate Assets: Primarily designed for managing company-owned mobile assets, which may limit its flexibility for BYOD scenarios.
Start using MobiControl before you pay for it. The software can be downloaded directly from the SOTI website and you get a 30-day free trial.
9. Miradore Mobile Device Management
Miradore Mobile Device Management package is a cloud-based service. There are three service levels and the lowest of these is free of charge. The paid versions are Premium and Premium for Partners. The minimum order quantity for the Premium plan is ten devices. The price per device reduces for larger fleets but the price for ten devices is $3.30 per device if paid monthly or $2.75 per month if paid annually.
The Free package doesn’t include BYOD management, you need the Premium edition for that. The Premium version, which includes MAM and MCM, is still cheaper than most of the other services on this list. Miradore is not one of the major players in the infrastructure management software market, but its service competes very favorably with the leaders of the industry. Miradore is able to manage mobile devices running Windows, iOS, and Android.
Key Features:
- Broad Device Coverage: Manages both mobile devices and laptops, supporting iOS, Android, Windows, and macOS.
- Secure Containerization: Offers containerized delivery of corporate data and applications on personal devices.
- Accessible Free Plan: Provides a no-cost option for basic mobile device management needs.
Why do we recommend it?
Miradore Mobile Device Management offers controls for mobiles and laptops running iOS, Android, Windows, and macOS. This tool provides BYOD only for devices running Android. The system creates a secure vault on the user-owned device, which it interfaces to the corporate system. This on-device unit can be remotely blocked by a central administrator.
All plans include end-to-end encryption. Remote control functions allow you to locate all equipment, lock or wipe a lost device, reset passwords, and bypass any hardware password set by the user.
Miradore uses enrollment-based configuration, which is fine for BYOD. However, you can’t bulk configure a fleet of company-owned devices. The software includes secure email apps and wifi protection. A VPN service is only available for iOS devices.
Who is it recommended for?
The Miradore solution is similar to a containerization service except that the “container” is installed on the device rather than delivering services and then being destroyed at the end of each session. This is an alternative strategy for businesses that aren’t satisfied with standard containerization.
Pros:
- Versatile Management Options: Equips businesses with the tools to manage both in-house and BYOD scenarios effectively.
- Remote Access and Control: Features comprehensive remote control functions, including device locking, wiping, and password resets.
- Data Integrity: Ensures corporate data is securely accessed without being stored on personal devices, safeguarding information.
Cons:
- Limited Desktop Management: Focuses primarily on mobile and laptop management, overlooking desktop integration.
The Premium plan includes mobile application management. In a BYOD environment, you would need the “containerization” solution, which isolates the apps on a device that are allowed to access the company network. This is also only available with the Premium plan. Other special features reserved for the Premium plan include data and cell plan usage monitoring and web content filtering.
The free plan includes standard report formats, and you can customize reports with the two paid packages. As you would expect, a number of features are available only to paying customers, such as live support.
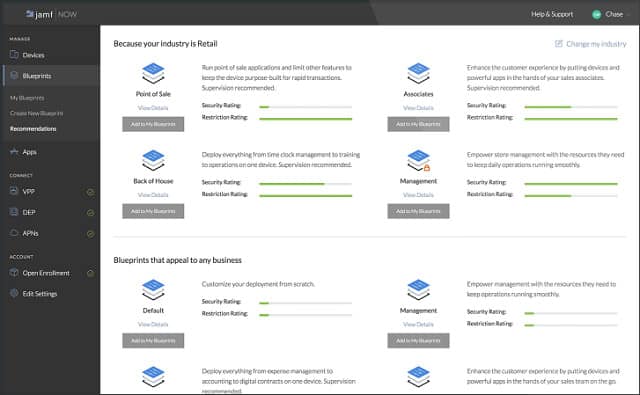
10. Jamf Now
Jamf Now is a cloud-based service that only controls iOS devices. The service is priced per device and the first three devices are free.
Key Features:
- Cost-Efficient Management: Manages up to three iOS devices for free, offering a cost-effective solution for small setups.
- Simple Web-Based Enrollment: Facilitates device enrollment through a user-friendly web interface, streamlining the process.
- Enhanced Connection Security: Implements robust security measures to protect devices and their connections.
Why do we recommend it?
Jamf Now provides mobile device management for iOS devices and it includes procedures for BYOD inclusion. The service is an orchestration system for some of the app delivery systems that are provided by Apple. These include the Apple Business Manager and the Automated MDM Enrollment service.
The enrollment process is very well designed. Send a link to a web page containing all of the sign up details necessary to include a device in the network to the device owner. Completion of the enrollment triggers and automatic configuration procedure that installs an encryption client on the device.
If you have company-owned devices as well, create a “blueprint” configuration and then apply that to group a group of devices. You can create several blueprints for your entire network.
Managed devices send out alerts to warn of jailbreaking or unauthorized software. Get an inventory of the spare storage capacity, installed apps, and the serial number of each of the devices on your network.
Allocate a passcode to each device. Two-factor authentication is available. Procedures for lost phones include lock and wipe options. A phone marked as lost will signal you its location.
Who is it recommended for?
Jamf aims for the SMB market. The company offers Jamf Now for free to manage three devices. Businesses that need to manage more devices still get those first three for free. The Jamf Now service will also manage devices running macOS and that includes desktop Macs.
Pros:
- Dual Management Capability: Efficiently manages both company-owned and personal iOS devices, enhancing organizational control.
- Comprehensive Device Security: Offers extensive security controls including alerting for jailbreaking and unauthorized software installation.
- Effective OS and App Management: Provides OS patch management and keeps an inventory of installed apps and device storage.
Cons:
- iOS Exclusive: Limited to managing iOS devices, excluding Android and other operating systems from its service offering.
Jamf Now relies on the Apple Volume Purchasing Program for mobile application management. A version control utility lets you check on the operating systems of your managed devices and roll out updates when they become available.
11. BeachheadSecure
SimplySecure is a cloud-based service that can manage iOS and Android mobile devices as well as portable storage. The system can manage desktops and laptops, giving you unified endpoint management. You may only purchase an annual subscription directly from the SimplySecure website. It is possible to get a monthly rate, but only through resellers. The service is charged at a different price per unit for desktops and laptops, mobile devices, and USB storage.
Key Features:
- Versatile Cloud Platform: Provides comprehensive management for a variety of devices including iOS, Android, desktops, laptops, and USB storage from a single cloud-based service.
- Unified Endpoint Management: Enables the management of all types of devices, offering a cohesive approach to endpoint security.
- Advanced Device Recovery Features: Offers device tracking and remote wiping capabilities to protect against loss or theft.
Why do we recommend it?
Beachhead Secure for Phones and Tablets is a division of the BeechheadSecure cloud platform for UEM. This system covers devices running iOS and Android. The key element of the service is device encryption, which can be applied to user-owned devices. You can combine the plan with modules for endpoints and USB devices.
The service includes device tracking, and lost devices can be wiped remotely. The utility to reset passcodes centrally works as a lock in cases of theft.
Encryption protects communications between each device and the company network. Data stored on the device can also be encrypted.
Who is it recommended for?
This system isn’t as sophisticated as the other tools on this list. It relies extensively on imposing encryption but it requires the permission of the device’s owner and it is a little more invasive than the virtualized desktop or container delivery models implemented by the other tools on this list.
Pros:
- Strong Encryption Measures: Ensures secure communication and data protection on devices with robust encryption capabilities.
- Peripheral Management: Extends security measures to include peripheral devices, broadening its protective scope.
- Flexible Subscription Options: Offers annual subscriptions directly, with monthly options available through resellers, providing purchasing flexibility.
Cons:
- Focused on Corporate Assets: Primarily designed for managing corporate-owned assets, which may limit its appeal for BYOD scenarios.
Optional coverage for USB storage devices is pretty unique and a great boon for small companies that employ portable storage as a space saver for mobile staff. SimplySecure is a straightforward UEM system suitable for small businesses with no in-house systems administrators.
To BYOD or not to BYOD
MDM systems can greatly increase your control over mobile devices used for your business whether you own those devices or your employees do.
A complete enterprise mobility management solution not only replicates the security measures on your private network, but takes it a step further.
Mobile devices can enhance the competitive edge of any company. If you don’t want to risk BYOD, then try one of the other deployment models outlined in this guide. CYOD is a particularly clever strategy that gives employees a feeling of being valued: “The company is buying me a phone!” If you want to introduce mobile devices into your work practices, you will be watching your employees walk out of the door with the equipment that you paid for. Making them feel that you bought the phones for them boosts morale, getting you extra productivity benefits out of the purchase.
Providing mobile equipment for employees is a risky business and keeping track of issuance is important. In a famous example, Coca Cola lost a large amount of mobile devices to one employee who was a serial loser. Each loss took network access and stored company data with it. Allowing BYOD solves the problem of lost hardware along with all of the data on it.
The industry has come a long way since the Coca Cola laptop heist, and you can thank your MDM system for saving you a lot of money. It keeps track of your property wherever it goes and because it gives you the confidence to allow employees to connect their own devices to the network, saving you the cost of buying equipment.
Notice the MDM systems listed in this guide manage both company-owned equipment and employee-owned mobile devices. That gives you an opportunity to get the best out of a mobile strategy by employing a hybrid approach. The tracking of company-owned devices gives you a fallback position and should allow you the confidence to lay down strict ground rules. Staff who refuse the terms of connecting to the network with their own approved devices can be issued a company device.
The CYOD strategy can also be integrated into an employee incentive scheme. A better phone or tablet could be offered to those who win points for improved productivity or success on company-approved training courses.
The bottom line is that mobile devices have become a useful tool both as an incentive for improved performance and as a bare, straightforward productivity gain.
Update your system monitoring software to include enterprise mobility management and reap the productivity gains and cost savings of BYOD.
Bring Your Own Device FAQs
Can you enforce strong passwords in a BYOD environment?
It is possible to enforce strong passwords for access to any of your systems by any device, including user-owned devices in a BYOD environment. Authentication procedures can be managed universally and include a range of security measures, including strong password requirements, password rotation requirements, and 2FA methods.
How do you prepare for teleworking in a BYOD strategy?
Teleworking and BYOD on-site require very similar strategies, so it makes sense to merge the two processes that allow access. Create a portal that will allow access to business resources through a browser or app. That will give access from user-owned devices whether in the office or at a remote location without having to control the entire device.
Can I stop jailbroken devices from entering my network?
Mobile device management (MDM) systems can detect when a device has been jailbroken during the onboarding phase. In these instances, the MDM software just doesn’t load access software on the device. MDM systems that install an agent onto the device keep a constant check on the device and either prevent sideloading and jailbreaking or block access to corporate apps on the device.
Further reading
Comparitech Networking Guides
The ultimate guide to mobile device management (MDM)
Top server management & monitoring tools
How to build your own cloud storage server at a fraction of the cost
The best free NetFlow analyzers and collectors for Windows
The best free network vulnerability scanners and how to use them
The best packet sniffers and network analyzers
Best free bandwidth monitoring software and tools to analyze network traffic usage












Wow…this is one detailed and informative article that was totally worth the read. BYOD is on the rise and every company should read this article to understand the concept better, take the necessary precautions and hire a managed IT service provider to do the rest for you. Thanks for sharing this article up here!
This is like a complete guide for BYOD. I didn’t read the whole thing, but whatever I read, I could connect to it. Thanks for sharing such an informative post.
Excellent read, and a lot of that info has helped me with my business case. Thanks.
Typo: “There are three main types o confidentiality risk”
of
Thanks for spotting that one. I have corrected the error.
Cheers,
Stephen