Ethical hacking is the process of attempting to penetrate computer systems and networks with the intention of locating weaknesses and vulnerabilities (real and potential) that could be exploited by malicious hackers. Any information uncovered is then used to improve the system’s security and plug loopholes. Sound interesting? Then an online ethical hacking course is for you.
Ethical hacking is sometimes referred to as penetration testing, intrusion testing, or red teaming. There are many types of hackers, and ethical hackers are usually referred to as white hat hackers. This skill is in high demand and a white hat hacking course can jumpstart your cybersecurity career.
A quick search will yield a ton of results for an ethical hacking course online, but they aren’t all worth your time. We reveal more about our favorite courses below, but if you’re in a rush, here are our top picks.
The best ethical hacking courses:
- StationX – The Complete Ethical Hacking Course Bundle
- Udemy – Learn Ethical Hacking From Scratch
- Cybrary – The Art of Exploitation
- Offensive Security – Metasploit Unleashed
- Coursera – Cryptography
- Introduction to Ethical Hacking and Cyber Security
- StationX: The Complete Python for Hacking and Cyber Security Bundle
- Cybrary: Intro to Python
- Cybrary: Developing Ethical Hacking Tools with Python
- CyberTraining 365: Ethical Hacking with Python
- Udemy: Python 3 For Offensive PenTest: A Complete Practical Course
- Udemy: Python Network Programming | Network Apps & Hacking Tools
- Mindsmapped: Python for Ethical Hacking
Tips for choosing an ethical hacking course
We’ve included a range of course types in our list, but here are some things to think about when deciding on which one to try first:
- Don’t go in over your head. Some courses assume a certain level of background knowledge, while others are targeted at complete beginners. Choose a course that’s at the right level for you.
- Consider minimum requirements. Bear in mind that you’ll need specific software to follow some courses, so be prepared to gather some resources if needed.
- Look for special offers. Paid courses are often of higher quality, but they can get pricey. However, many companies run special offers so you end up paying very little for a superior-quality course.
- Watch out for scammers. Unethical hackers prey on amateurs, so be careful you don’t sign up with unethical hackers who promise to teach you the ropes.
Best ethical hacking courses online
Here is our list of the best ethical hacking courses to learn hacking from scratch:
1. StationX – The Complete Ethical Hacking Course Bundle (Paid – Beginner)
StationX’s The Complete Ethical Hacking Course Bundle is our top choice for the best ethical hacking course and is really the gold standard for white hat hacker training. This comprehensive course was developed with beginners in mind and contains everything you need to know about ethical hacking and how to secure systems against attacks.
It starts with basic terminology and shows you how to install the required software, and how to set up a penetration testing lab. Aside from ethical hacking and penetration testing, you’ll also learn about hacking and testing for websites and networks, social engineering, and using Android for testing computer system security.
Your instructor throughout is computer scientist and ethical hacker Zaid Al Quraishi.
Cost:
This bundle usually costs $500 but Comparitech readers save 87% and benefit from five courses for just $65.
Courses in bundle:
- Ethical hacking from scratch
- Website hacking from scratch
- Network hacking from scratch
- Social engineering from scratch
- Hacking using Android
Requirements:
- Basic IT skills
- Wireless adapter
2. Udemy – Learn Ethical Hacking From Scratch (Paid – Beginner)
This is a very comprehensive ethical hacking course for absolute beginners with no previous knowledge of hacking or penetration testing. It focuses on the practical side of penetration testing but doesn’t neglect the theory, for example, how devices interact inside a network.
You will first learn how to set up a testing lab on your own machine, and how to install the Kali Linux operating system. Don’t worry if you’re not familiar with Linux; you will quickly learn the basic commands you need to interact with the Kali Linux terminal.
Cost:
Approximately $130, although Udemy offers regular specials so we’ve seen the price as low as $29.99.
TIP: This course is included as part of the StationX Ethical Hacking bundle.
Covers:
- Network penetration testing
- Gaining access
- Post exploitation
- Web application penetration testing
Duration:
- 15.5 hours of on-demand video (about 135 videos)
Requirements:
- Basic IT skills
- Wireless adapter
More: Udemy provides an easily navigable portal to a wide range of ethical hacking courses, free and paid. Running a search on “ethical hacking” returns over 800 matches, more than 40 of them free. Some suggestions to get started:
- Start Kali Linux, Ethical Hacking and Penetration Testing! (Free – Beginner) – Offers a complete tutorial on how to install VirtualBox, including on Windows 8.1, and run Kali Linux in any environment. Learn how to create a virtual environment and the basics of the Linux terminal. All you need is a fast internet connection. (4 hours)
- Kali Linux tutorial for beginners (Paid – Beginner) – Focuses on configuring the Kali Linux operating system to build up Linux targets from scratch to hack. No previous knowledge of Linux required. You will need to have a basic understanding of networking concepts and of ethical hacking concepts such as port scanning, vulnerability scanning, and so on. (5.5 hours)
3. Cybrary – The Art of Exploitation (Free – Intermediate)
Buffer Overflow occurs when a program, while writing data to a buffer, overruns the buffer’s boundary and overwrites adjacent memory locations, creating a potential security vulnerability. In this ethical hacking course, you will write a Python script and use it to hack a system affected with Buffer Overflow.
Covers:
- Vulnerability and exploit
- Buffer overflow
Duration:
- 3 hours of on-demand video
Requirements:
- Prior coding experience
More: Cybrary courses are totally free and cover a wide range of subjects, but you must pay if you want a certificate of completion, or to access the assessments and exams (approximately $99 per month). The website is well organized with an option to select ethical hacking courses suitable for a specific career path, for example, penetration tester or network engineer, and even create your own syllabus.
You can search for courses by skill type, level, or certification. When you sign up, you will be directed to your dashboard, which displays the courses you’ve completed or are busy with, your certifications, and even posts you’ve published to the Cybrary community. This site is ideal if you want to build up a portfolio of knowledge, keep track of your progress, and ultimately choose one or more certifications.
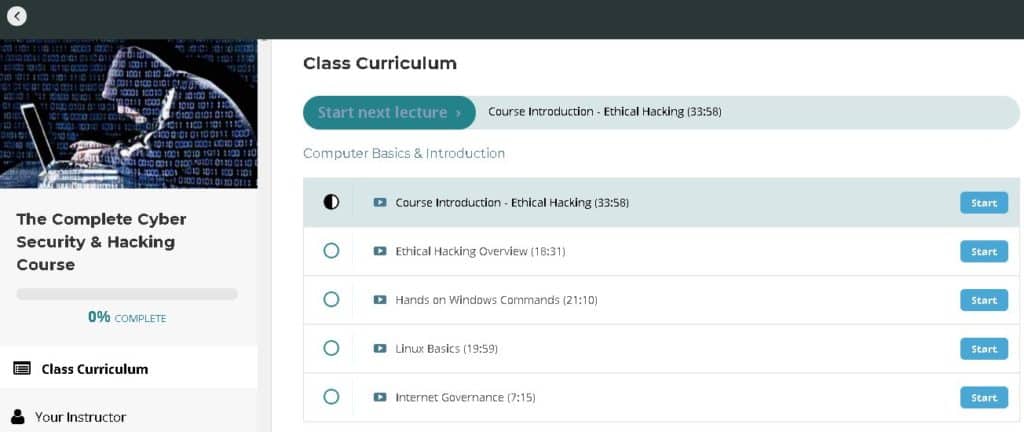
4. EH Academy – The Complete Cyber Security & Hacking Course (Free – Beginner to Intermediate)
This ethical hacking course covers the basics of white hat hacking including a detailed video on how to set up a lab. You’ll also get an introduction to Nmap and Metasploit tools and learn basic Windows and Linux commands. A nice touch is that below each video you can comment or post questions to the instructor or other students.
Covers:
- Computer basics and introduction
- Setting up your lab
- Information gathering
- System hacking
- Web server (site) hacking
Duration:
- 1.5 days
Requirements:
- Reliable internet connection
More: For the advanced hacker, EH Academy offers a wide range of specialized ethical hacking courses, most of them paid (ranging from $50 to $200). Examples are Using Python For Offensive Penetration Testing, Advanced Mobile Application Penetration Testing, iOS Application Penetration Testing Training, Metasploit training for Penetration Testing & Ethical Hacking, and VoIP Hacking & Penetration Testing Training.
5. Offensive Security – Metasploit Unleashed (Free – Intermediate to Advanced)
The in-depth Metasploit Unleashed ethical hacking course is provided for by Offensive Security. The organization’s goal in providing the course is to increase awareness for children in East Africa who are underprivileged. The course assumes you understand some fundamentals, for example, command-line interface commands, and scripts.
Covers:
- Everything you need to know to get started with Metasploit
- Hands-on practice from information gathering to writing a simple fuzzer
Duration:
- Self-paced
Requirements:
- Reliable internet connection
- A virtual machine (aka Hypervisor) to host your labs
- Minimum 10 gigabytes of storage space
- Sufficient RAM (check under Requirements in the Introduction section to calculate how much you will need)
- The bare-minimum requirement for VMware Player is a 400 MHz or faster processor (500MHz recommended)
- Kali Linux (download under Requirements in the Introduction section)
- A vulnerable VMware virtual machine to scan and attack (download “Metasploitable” under Requirements in the Introduction section)
6. Coursera – Cryptography (Free – Intermediate)
By the end of this ethical hacking course, provided by the University of Maryland through Coursera, you’ll have a firm grasp of cryptographic primitives in wide use today. You’ll also learn how to combine these to develop modern protocols for secure communication.
Covers:
- Foundations and practical applications of modern cryptography
Duration:
- 7 weeks
Requirements:
- Some experience covering discrete mathematics and basic probability
- Prior exposure to algorithms will be helpful
- Familiarity with programming in a C-like language
- Mathematical maturity
More: MOOCs (Massive Open Online Courses) are free online college-level classes open to everyone. They are apparently “more popular than cheese.” They don’t count towards degree credits but will be appreciated by future employers as degree-level training.
The method of instruction is usually video but instructors’ brains can be picked on virtual forums and during chat sessions. There are various types of assessments, from peer assessment to formal exams, depending on the course. Some of the courses have fixed schedules and most take between six to eight weeks to complete.
7. Introduction to Ethical Hacking and Cyber Security
This free course offered by Mindsmapped is a four-part program. Aimed at beginners, it comprises 35 lectures in total and should take around five hours to complete.
The fours modules are:
- Introduction to Cyber Security and Ethical Hacking (2 lectures)
- Deep-Dive into Ethical Hacking (3 lectures)
- Penetration Testing (6 lectures)
- Ethical Hacking (24 lectures)
You’ll learn the basics of ethical hacking including exactly what it is and its different phases. The course also delves into virtualization and penetration testing, including practical applications of all topics.
If you’re keen to learn more, you can check out several additional ethical hacking courses offered by Mindsmapped:
8. StationX: The Complete Python for Hacking and Cyber Security Bundle
StationX offers a bundle of three courses designed to help complete Python beginners become advanced users with extensive cybersecurity knowledge. It includes 36 hours of on-demand video lectures.
Courses strike the perfect balance between the theoretical and practical components of hacking with Python. What’s more, they stick to the point, so you don’t get bogged down in unnecessary details that could be overwhelming, especially for beginners.
You’ll learn by example, writing your own hacking and security programs, modeling problems, and designing and implementing the corresponding solutions.
The courses included in the bundle are:
- Learn Python and Ethical Hacking From Scratch
- Python for Beginners: Learn Python Programming (Python 3)
- Cyber Security – Python and Web Applications
If you’re looking to start a career in cybersecurity or simply want to learn more about hacking with Python, this bundle could be a great fit. What’s more, StationX has a ton of other great courses and bundles available. You can even take advantage of its VIP Membership and get access to all courses for a low annual fee.
9. Cybrary: Intro to Python
If you’re a high-level learner who just wants to learn the bare minimum, this one might be for you. Instructor Joe Perry keeps things simple in this course that’s geared toward non-coders. In it, you’ll learn the “must-know” aspects of Python rather than delving into its specifics.
Intro to Python contains around 10 hours of material covering basic concepts up to advanced scripts. Designed to prepare people who are considering a career in penetration testing and cybersecurity, it focuses on teaching the commands and functions most critical to the industry.
This course includes two modules:
- Just the Basics
- Data Types and Logic
Once you’re finished, if you’re looking to expand your knowledge, Cybrary has plenty more courses to choose from, many of which are free. You’ll have to create an account to access any of the courses, and once you’re enrolled, you’ll be offered the Insider Pro package. This costs $99 per month (or $83 per month when billed annually) and gives you access to more courses, a career pathway guide, and a mentor. It comes with a seven-day free trial.
10. Cybrary: Developing Ethical Hacking Tools with Python
Another popular offering on Cybrary is Developing Ethical Hacking Tools with Python. This course includes just over an hour’s worth of videos so is quick to complete, but packed with useful information. For example, it teaches you how to combine multiple Python libraries and automate information gathering. You’ll even learn how to code a keylogger and write a ZIP password bruteforcer.
Here are the modules included in this course:
- Introduction
- Automating Information Gathering
- Writing a Keylogger in Python
- ZIP Password Bruteforcing in Python
- Going Forward
This is considered an intermediate level course so some background knowledge in Python is needed. It might be a good idea to take the Intro to Python course followed by this one.
11. CyberTraining 365: Ethical Hacking with Python
Ethical Hacking with Python is a comprehensive course containing just under eight hours of video tutorials. During this program, you’ll learn Python fundamentals including simple coding using variables, statements, and dictionaries.
You’ll also have access to ethical hacking tutorials such as “Buffer overflow and exploit writing with Python” and “Syn Flood attack with Scapy.” The curriculum includes 23 lessons ranging from three to 36 minutes in length. Here are a few lesson examples:
- Python File Handling
- Ping Sweep with Scapy
- Object-Oriented Programming in Python
- Forensics Investigation with Python
The course is suitable for complete beginners, but it does become fairly complex and could teach experienced programmers a thing or two. Each lesson includes an exam, enabling you to identify gaps in your knowledge.
CyberTraining 365 offers a free five-day trial, so if you’re quick, you might be able to take this course for free. Once your trial is up, you’ll pay $9 for the first month and $59 per month after that. You can get discounts if you sign up for a six-month or annual term. If you’re only interested in this course, it’s also available on Udemy for $19.99.
12. Udemy: Python 3 For Offensive PenTest: A Complete Practical Course
Udemy’s popular Python 3 For Offensive PenTest course is for more advanced users. It covers in-depth topics related to ethical hacking and penetration testing but includes some real-world examples to help you see things from a practical perspective.
The cost of this course is $99.99. The total length of all videos is around five hours; this includes 58 lectures split into seven modules:
- Quick Intro
- Python 3 / Windows 10 / Kali 2: Gaining Access – Your First Persistent Shell
- Python 3 / Windows 10 / Kali 2: Advanced Scriptable Shell
- Python 3 / Windows 10 / Kali 2: Catch Me If You Can!
- Python 3: How Malware Abuse Cryptography? Python Answers
- Python 3 / Windows 10 / Kali 2: Passwords Hacking
- Windows 7 & 10 Privilege Escalation – Weak Service Permission
One notable thing about this course is it’s regularly updated so you can be assured lessons deal with the most current information and program versions. What’s more, the course instructor, Hussam Khrais, is prompt in responses to student queries and will even make updates to the course upon request. Udemy courses come with a certificate of completion.
As mentioned, this isn’t considered a beginner’s program and prerequisites include beginner-level Python (or another scripting language) and intermediate-level knowledge of ethical hacking and penetration testing.
13. Udemy: Python Network Programming | Network Apps & Hacking Tools
This is another (somewhat pricier) course offered by Udemy, targeted at beginners. The course is new to the platform but is already proving a hit, having attracted thousands of students and racking up some great reviews. It takes things slowly and explains everything you need to know about setting up your environment and getting started with Python 3.
You’ll also learn about the basics of networking, including internet architecture and Python TCP connections. Practical lessons include setting up more than 15 Python 3 code application tools and networking applications, creating a man-in-the-middle Python 3 tool, and building a data scraping tool.
The course consists of 26 lectures (about six hours of videos) split into four modules:
- Introduction To This Python 3 Course
- Setting Up Your Environment
- Getting Started With Python 3 Networking
- Python 3 Network Hacking
It’s fairly pricey at $199.99 but Udemy does offer regular discounts so watch out for those.
Udemy offers many other cybersecurity-related courses, including more on the topic of hacking with Python. Here are a couple of others you may want to check out:
- Introduction To Python For Ethical Hacking
- Offensive Python | Mastering Ethical Hacking Using Python
- Cyber Security – Python and Web Applications
14. MindsMapped: Python for Ethical Hacking
This free offering from MindsMapped is a two-part program. The course instructor is the founder of HackerSploit, a cybersecurity consultancy firm.
The two main modules are titled:
- Python for Ethical Hacking (13 lectures)
- Python for Ethical Hacking (Advanced) (3 lectures)
The first caters to beginners and starts with an introduction to Python, progressing to the creation of a brute force password checker. The second part of the course moves on to more advanced topics including creating TCP servers and understanding sockets.
The whole program can be completed in around three hours. After that, if you’re eager for more, Mindsmapped offers several other ethical hacking courses including:
Use ChatGPT to learn ethical hacking
The last couple years have seen a huge shift in how people can access free education. Countless YouTube videos and articles have popped up that explain how anybody can leverage ChatGPT to learn new skills.
ChatGPT is an AI platform that anybody can use for free. A free account allows you to access the ChatGPT 3.5 algorithm, which has been trained on information from the internet up to the end of 2022. ChatGPT is an extremely knowledgeable resource packed with useful information about cybersecurity and ethical hacking (as well as countless other skills).
ChatGPT can provide you with information, explanations, and guidance on various aspects of ethical hacking, including concepts, tools, techniques, and best practices.
Below, we have included some ways that ChatGPT can help you learn ethical hacking:
- Ethical hacking concepts: ChatGPT can explain the concepts of white hat hacking, such as penetration testing, vulnerability assessment, and ethical responsibilities.
- Tool recommendations: ChatGPT can suggest and describe tools that are commonly used by ethical hackers. this includes network scanners, vulnerability scanners, and password-cracking tools.
- Methodologies: ChatGPT can help you learn ethical hacking methods and provide insights into how ethical hackers think and approach their targets.
- Best practices: ChatGPT can offer guidance on ethical hacking best practices, including how to conduct ethical tests responsibly and without breaking the law.
- Legal and ethical considerations: ChatGPT knows legal and ethical considerations of hacking, including the importance of obtaining proper authorization and respecting privacy laws.
- Vulnerability exploitation: ChatGPT can provide explanations and examples of common vulnerabilities, such as SQL injection and cross-site scripting (XSS), and how ethical hackers (and criminals) can exploit them.
- Resources and learning methods: ChatGPT can suggest additional online courses, books, websites, and forums where you can gain more knowledge about ethical hacking. It can also direct you to resources like OWASP Top 10 to learn more about the risks associated with web development (such as insecure design, misconfiguration, authentication failures, and broken access control).
Is ethical hacking legal?
Yes. In 2015, the Librarian of Congress issued a number of exemptions to the 1998 Digital Millennium Copyright Act which effectively allow white hat hackers to hack software in the name of research and on condition they disclose any vulnerabilities they might find. This controversial topic is increasingly relevant as more everyday items, including vehicles, contain computers.
An ethical hacker must abide by the following (informal) guidelines:
- Get express (written, preferably) permission to attempt to penetrate an organization’s system.
- Be respectful of all the company’s rules and policies.
- Notify the company of all weaknesses and vulnerabilities found.
- Leave the system in the way it was found, that is do not create any weaknesses that could be exploited at a later date.
- Keep a written record of what is done on the system.
- Do not violate the laws of a country by, for example, doing something that breaches copyrights, intellectual property, privacy laws, and so on.
Why take an ethical hacking course?
An organization may hire an ethical hacker to attempt to hack their computer system within certain restrictions set by the company and country law. A company may also train a staff member to perform this role in-house. Sometimes ethical hackers are simply self-proclaimed “geeks” who hack on their own time, but not destructively. These kinds of hackers do it “for the fun of it” and, if they’re bounty hunters, even get paid if they find a loophole in an organization’s system.
If you decide to undergo white hat hacker training, you’ll be in excellent company. For instance, a little-known fact about Sir Timothy John Berners-Lee, best known as the inventor of the World Wide Web, is that he was a hacker in his early years. According to Investopedia, “As a student at Oxford University, Berners-Lee was banned from using the university computers after he and a friend were caught hacking to gain access to restricted areas.”
One of the most notorious white hat hackers in recent times is Kevin Mitnick, described once by the US Department of Justice, as “the most wanted computer criminal in United States history.” After serving time for unlawful hacking, he reformed and became a paid ethical hacking consultant for numerous Fortune 500 companies, as well as for the FBI.
As a career, ethical hacking can be quite lucrative. According to InfoSec Institute, salaries for certified ethical hackers in 2021 ranged from $45,000 to $129,000 USD. An Indeed survey from the same year found that ethical hacking salaries ranged from approximately $57,787 per year for an IT security specialist to $105,973 per year for a firewall engineer.
The Exabeam 2018 Cyber Security Professionals Salary and Job Report found that 23.7 percent of security professionals surveyed had a CEH certification (more on that below).
Why do ethical hackers prefer Python?
Python is a popular choice among ethical hackers, and for good reasons. Here’s why it’s so liked:
- Easy and powerful: Python is known for being user-friendly. This makes it a top pick for beginners and pros alike. It’s simple to learn but can do a lot of heavy lifting in cybersecurity tasks.
- Flexible and intuitive: With Python, you can bend and twist it to do various tasks. This flexibility is super handy for ethical hackers who need to write different types of programs quickly and efficiently.
- Great for scripting: Ethical hackers often need to write small programs (scripts) to automate tasks or solve problems. Python is perfect for this.
- Strong community support: Imagine having a big group of friends you can ask for help anytime. That’s what the Python community is like. With loads of resources, forums, and documentation, help is always available if you get stuck or need advice.
- Versatile for many careers: Python isn’t just great for hacking. It’s a skill that opens doors in many fields, like web development, big data, game development, AI, and smart device tech.
In short, Python equips ethical hackers with a versatile and effective tool, making it a vital skill in their arsenal.
Ethical hacking course certification
The most widely recognized ethical hacking credential is the Certified Ethical Hacker (CEH) credential from EC-Council. You don’t have to sign up for their course before taking the exam, but all self-study students have to go through a formal eligibility process. You could take one or more of the courses listed above and go for the accreditation separately.
The EC-Council also offers the Certified Network Defense Architect (CNDA) credential. To be eligible for the course, you need to first obtain CEH certification from EC-Council and must be employed by a government or military agency, or be a contract employee of the US government.
The essential skills to becoming a master hacker
Unless you specialize in a particular area, for example, mobile or forensics, a formal one-size-fits-all course typically touches on the following subject matter:
- Buffer overflows, cryptography, denial of service, enumeration, firewalls, exploitation, fingerprinting, foot printing, hacker types, hacking mobile platforms, hacking web applications, hacking web servers, penetration testing, reconnaissance, scanning networks, session hijacking, sniffing, social engineering, sql injection, system hacking, tcp/ip hijacking, hacking tools, trojans and backdoors, viruses and worms, and wireless hacking.
Succinctly summed up by OCCUPYTHEWEB, to get started, here’s what you really need to master:
- Basic computer skills (not just MS Word but using the command line, editing the registry, and setting up a network
- Networking skills (for example, understanding routers and switches, internet protocols, and advanced TCP/IP)
- Linux skills (these are non-negotiable)
- Hacker tools (for example, Wireshark, TcpDump, and Kali Linux)
- Virtualization
- Security concepts and technologies (such as SSL, IDS, and firewalls)
- Wireless technologies
- Scripting (for example, Perl, BASH, and Windows PowerShell)
- Database skills (starting with SQL)
- Web programming and applications (how hackers target them)
- Digital forensics
- Cryptography (encryption)
- Reverse engineering
Other ethical hacking resources
Formal ethical hacking courses are ideal for on-the-job training in a specific niche. Alternatively, many hackers advocate self-learning. The advantage of this is that you get to discover your field of particular interest. Below are some other free resources, tutorials, hands-on challenges, and articles on ethical hacking.
- Exploit Exercises – As the name suggests, see if you can spot code vulnerabilities in a series of advanced hacking challenges.
- Vuln Hub – This site offers a really fun way to practice your skills in hands-on workshops, for example, download a custom VM and then try to obtain root level access.
- YouTube – Perfect for the lazy ethical hacker; all you need is popcorn. Simply search “ethical hacking course.”
- Tutorials Point – The Ethical Hacking Tutorial provides a good overview for beginners.
- Open Security Training – The Hacking Techniques and Intrusion Detection course is under a Creative Commons License so you can use it to train employees in-house. All the materials are supplied; just add an instructor. The course creator is available for on-site training.
To enhance your learning experience, you might consider joining an ethical hacking forum or paying an ethical hacker to share their knowledge and experience with you. If you’re interested in a particular tool or platform, most hacking software vendors provide in-depth tutorials for their applications.
Happy hacking and stay legal!
FAQs about ethical hacking
How does ethical hacking differ from malicious hacking?
In the world of hacking, there are two main paths: ethical hacking and malicious hacking. Think of them as two characters in a video game, each with goals and rules.
- Ethical Hacking: Ethical hackers are given permission to test the security of websites and systems, almost like a special pass, to find and report problems. These hackers follow the rules, only searching for weaknesses they’re allowed to. They aim to find these weak spots before the bad guys do so they can be fixed and make the digital world safer.
- Malicious Hacking: On the flip side, malicious hackers are the villains. They hack into systems without permission to steal information or cause damage. Their actions can lead to severe problems, like stealing sensitive data or causing systems to crash.
- The Key Difference – Permission: The most important difference between ethical and malicious hackers is permission. Ethical hackers have the green light to test systems and are actually helping improve security. Malicious hackers, however, are breaking the law by entering digital spaces that’re not allowed.
Choosing to be an ethical hacker means staying on the right side of the law and using your skills to make the internet a safer place for everyone.
See also: