Did you know that one in 20 Americans has had their identity stolen at some point? It’s scary enough losing access to your online accounts but if an attacker is able to get your Social Security Number, things can get complicated very quickly. After all, getting a new SSN isn’t easy, and while you wait to be processed, someone could be taking out loans, opening new bank accounts, and using your health insurance.
The good news is that you don’t just have to let this happen. Below, we’ll reveal how you can freeze your Social Security Number in the event of a breach. What’s more, you’ll learn how to find out if someone else is using your SSN, and how to protect yourself against this kind of identity theft in the future.
Why is your SSN so important?
Originally created as part FDR’s New Deal as a way to track individual Americans’ Social Security accounts, the nine-digit Social Security Number eventually became a standard personal identifier used for a wide variety of purposes.
As all Americans receive this number shortly after birth, or upon becoming a naturalized citizen, the wide use of the number out of the SSA makes a certain kind of sense. Before SSNs, there was no easy way to track all Americans beyond legal names and physical address. Yet that method, as we all know, is a bit troublesome. Names are not exactly unique, and people change addresses all the time.
The problem is that social security numbers are supposed to be kept secret, yet all sorts of organizations request them, including employers, credit card companies, and government agencies. Sooner or later, a large-scale breach was going to happen, and it did: in 2017, Equifax had more than 147 million SSNs stolen, leading to an FTC settlement of around $500 million.
How to see if someone is using your Social Security Number
The easiest way to keep tabs on your SSN is to sign up for a free my Social Security account. This allows you to view annual statements that break down your retirement benefits, Medicare credits, taxes paid, and earnings record. There’s also a phone number to call if you notice any errors.

Next, request a free credit report from the FTC-approved AnnualCreditReport.com. This will show you any open lines of credit and accounts that have been opened in your name. If there are any you don’t recognize, look over your bank statements to see if there are any unusual charges.
What to do if your SSN has been stolen
As someone who has had his data stolen in a number of local and national data breaches, I can empathize with the feeling that comes immediately after knowing you’re a victim. It can be a numbing, scary experience, full of unknowns and unanswered questions. Thankfully, many organizations, such as banks, are readily monitoring your accounts for suspicious activity. For me, the only time my stolen data was actually utilized (stolen credit card information), my bank called me up and asked me if I was currently using my card somewhere halfway across the country (I wasn’t). They quickly shut it down and issued me a new card and contacted local police on my behalf.
For stolen SSNs, that’s a bit more difficult. Unless you’ve actually witnessed the theft firsthand, chances are you won’t find out about your stolen SSN until the damage has already been done. At that point, you’re working to minimize or put a stop to any further damage, reduce the overall impact on your life, and recover from the loss you’ve suffered as a result. The moment you discover that you’re a victim, you’ll want to take the following steps:
1. Check your credit report
This is no different than our earlier stated advice but is a necessary step once you know or suspect that your SSN has been stolen. This may be an important step immediately following a data breach that has impacted you, or if you discover a keylogger on your computer.
2. Contact any companies where fraud is occurring
Someone actively stealing your SSN is generally intent on using it for monetary gain. This either means selling it to someone who can use it to get a job or using the information themselves. This typically involves creating a credit card account, which may show up on your credit report. If you see accounts open that you know or suspect you did not open yourself, contact those crediting companies and explain to them the situation. They may not take immediate action beyond shutting down or suspending the suspicious accounts, but this will start the process.
3. Place a fraud alert on your credit report
If, after checking your credit report, you do find that there is suspicious activity, make sure you have had a fraud alert placed on your report. This will be a boon to you, as any credit inquiries will see the fraud alert and recognize that any irregular credit activity, including falling credit scores, may not be your fault.
4. Contact the FTC and IRS
You’ll want to head over the IRS website and IdentityTheft.gov, the FTC’s official website for reporting identity theft. These sites will walk you through the process of explaining what happened, and include going through the recovery process. You can also call the FTC at 1-877-438-4338.
5. Obtain records of your checking and banking accounts
This may be time-consuming, but you’ll want to go back through your accounts to see if you can identify where the first hints of suspicious activity began.
6. Submit a report to the Social Security Administration
If your SSN has been stolen, this is an important step. By submitting a report here, or calling the SSA at 1-800-269-0271, the SSA may be able to help track how your number is being used, and by whom. The organization may also allow you to apply for a new number if the damage is particularly extensive. Keep in mind: if you do get a new number, you will have to start building your credit history from scratch.
7. Contact your local police
This may seem like a strange step, but it’s a potential helpful option. At this point, your goal is to create a paper trail to prove that you were actively trying to solve the problem. This can go a long way to helping expedite the complaint and add proof to any courts or legal authorities that you need a new SSN or need assistance.
8. File a complaint with the FBI’s Internet Crime Complaint Center
As with contacting the local police, SSA, and FTC, filing a report with the FBI’s Internet Crime Complaint Center, this is all about creating a solid paper trail. This is a useful step if you’re fairly certain that your SSN was stolen via an online method, and not due to stolen physical documents. The FBI will likely forward this complaint to the FTC. However, if multiple complaints connect, it may otherwise help your case.
How do thieves steal Social Security Numbers?
Identity thieves can get their hands on your SSN in lots of different ways. Here’s an non-exhaustive rundown of a few, and what you can do to prevent them:
- Data breaches: The main way hackers obtain SSNs. Unfortunately, there’s nothing you can really do about this aside from deleting old accounts or avoiding services that require a Social Security Number.
- Phishing sites: These are designed to look like legitimate websites except they steal your login credentials and potentially all kinds of other information. The best way to protect yourself is to read up on common phishing scams, stop clicking links in emails, and be skeptical of every unsolicited message
- Keyloggers: A type of malware that sends whatever you type to an attacker. By the time you discover you have a keylogger, you may have already given away your SSN. We recommend running malware scans regularly and avoiding shady websites as much as possible to lower your chance of infection
- Stolen wallets: This one’s simple: if you lose your wallet and it has your SSN card inside, whoever finds it has all the information they need.
- Picking through your trash: Less common nowadays, but still a threat. We recommend shredding anything with your name, SSN, address, or date of birth before throwing it away
How to keep your Social Security Number secure
The best way to keep your SSN private is by proactively monitoring your credit reports for suspicious activity and limiting the number of organizations that you give it to. You can try offering services an Individual Taxpayer Identification Number instead, or just refuse to do business with companies that haven’t adopted the SSA’s recommendation of using alternative identifiers.
Another great way to stay safe is to delete yourself from sites that aggregate personal information such as SSNs, home addresses, and phone numbers. Unfortunately, there are dozens of these, and they reacquire old data all the time. We recommend using an automated service like Incogni instead: this sends removal requests to 100+ data brokers on your behalf and checks back regularly to make sure that once your information has been taken down, it stays down.
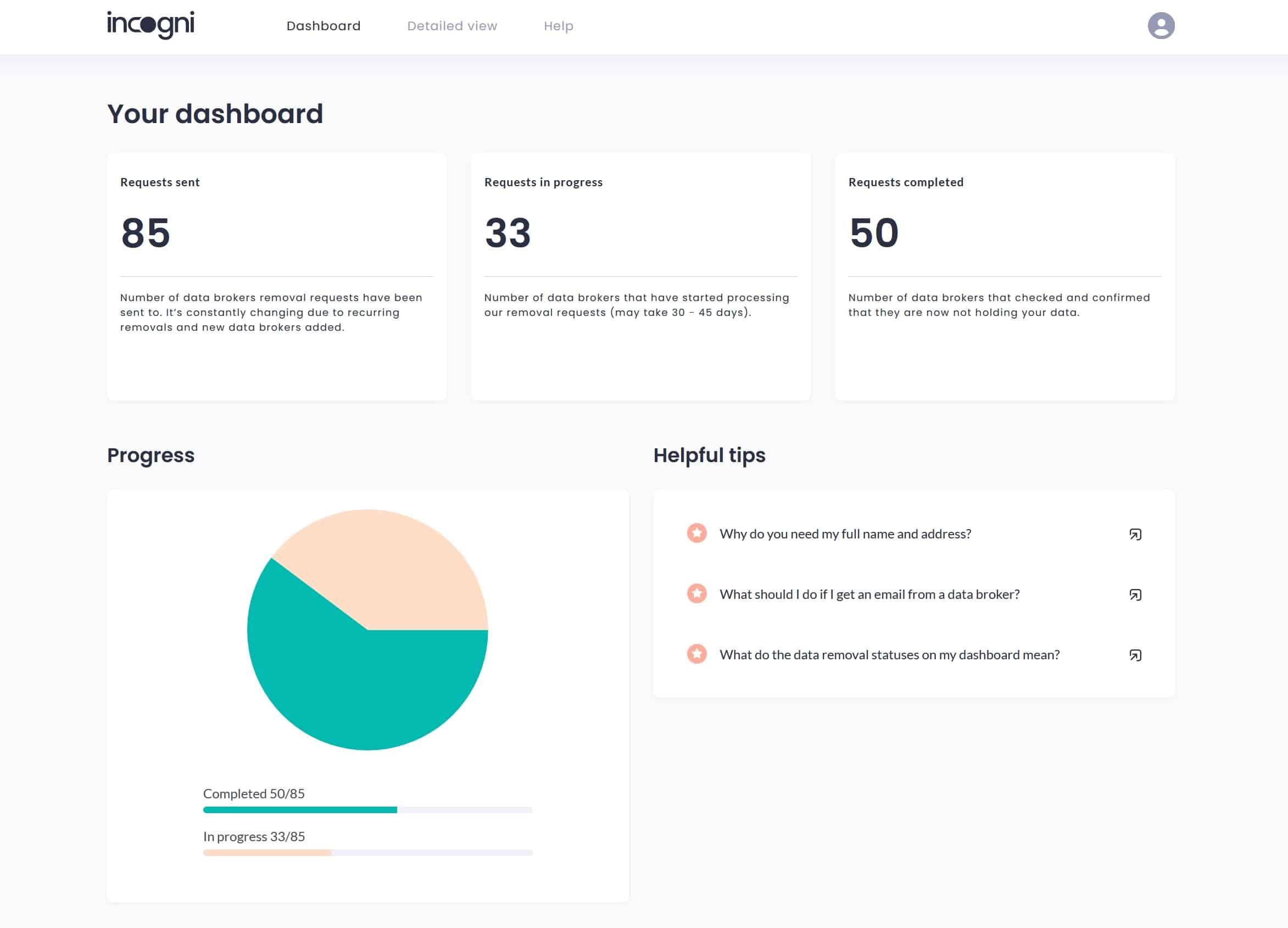
Incogni’s dashboard offers a clean and intuitive way to keep track of removal requests
Users can track the progress of their takedown requests using Incogni’s dashboard but it’s a very hands-off service, with no action required on your part. Best of all, it’s currently available at 50 percent off, with plans starting at just $6.49 USD per month.
A special note on ‘familiar fraud’
There’s a special class of identity theft known as “familiar fraud”. We call it a special class, but it’s unfortunately far too common. Familiar fraud occurs when the person committing the identity theft knows the victim. in 2018, Forbes reported that 15 percent of identity theft victims knew the person who stole their identity, more than double the number from the year prior.
Why is familiar ID fraud, such as child ID theft and elderly ID theft, so common? For the most part, because it’s far too easy. Family members may target related children because they will be able to get away with that ID theft for years before it’s ever discovered. A 10-year-old child whose Social Security Number is stolen and used to create credit card accounts likely won’t discover he or she is a victim until well until their 20s when it really starts to matter.
Meanwhile, some people may choose to take advantage of elderly family members or friends for similar reasons. The ID theft is likely to go undiscovered for a long time, and many elderly people may simply pay the associated bills, often assuming that they’re related to other expenses such as healthcare spending.
We strongly suggest checking credit scores of your children and elderly family members regularly.You can request this information from Experian through their Fraud Center. Additionally, you can add fraud alert or even a credit freeze. Education is important too: we’ve created a guide to keeping your kids safe online and a state-by-state list of establishments offering cybersecurity training for older adults.


