Perfect wireless security is a fallacy – it simply does not exist.
The best you can hope for is security that is good enough, or at least better than an alternative target.
While the chances of interesting an attacker are high, the possibility that interest will be converted into action depends almost entirely on how hard it is for the attacker to breach your defenses.
Fortunately, there is much you can do with your router to ensure that an attacker does not see your wireless network as so-called “low hanging fruit,” ripe for the picking.
And it all starts with the device’s configuration panel.
Securing your wireless router – typical user
While the general principles behind securing any wireless router are much the same, the specifics can often vary between brands and models so I won’t be able to handhold you through any changes you may need to make, or tell you precisely which settings you need to alter.
But I can point you in the right direction (if your router has an advanced configuration page, chances are you’ll need to visit it while reading this guide).
Login credentials
Firstly, you will want to login to your router. You probably received the username and password for the device from the manufacturer, retailer or your ISP, depending on where it came from. Or it may be written on the bottom of the router itself.
Depending upon what your login credentials are, you’ve probably just spotted the first security issue – many routers ship with the same default username (‘admin’ is common) and password (‘admin’ and ‘password’ are often used) so find out how to change that and do so as quickly as possible, picking a new username along with a long password. If you struggle to come up with passwords, use our password generator. In general, it’s a good idea to store all of your various passwords in a password manager. Two of the best options are Dashlane and StickyPassword.
Firmware
Windows update available? Do it.
Antivirus update ready for download? Do it.
Generally speaking, whenever you have the option to update something, do it!
And the same goes for your router’s firmware.
Typically, by the time you receive your router from your ISP, local shop or wherever else, the software it originally shipped with will already be out of date. And vulnerable, be it a Belkin router, higher end Cisco model or any other brand.
Fortunately, most manufacturers are responsible and issue firmware updates to tackle vulnerabilities as and when they are discovered. So, instead of just updating the firmware on the day you unpack your router like everyone else, be different and check back for updates on a regular basis, say every month or so. But do make sure you only download firmware updates from the manufacturer’s official website – fake updates hosted on rogue websites are not as uncommon as you may think.
Encryption
Your router probably gives you the option of employing several different types of encryption. While you don’t need to understand how each of them works, you do need to realise that they are not all created equal.
Some, such as WEP, suck. In fact, WEP sucks so bad that it isn’t really any better than having no encryption at all. And WPA, well, that’s barely an improvement.
WPA2 isn’t so bad though so make sure that’s what you use for your wi-fi connections.
Automatic updates
This is where you need to exercise some discretion – do you want your router to automatically check for updates (normally, as mentioned above, this is a good thing) or would you prefer to know when your device is communicating with its manufacturer?
A few years back, leaving automatic updates on would be the correct answer, but in this Internet of Things age in which TVs call home and share viewing details, including the names of files on attached USB drives, I’m not so sure.
You must decide what’s best for you.
Restrict other outbound traffic
As above really – if you have devices that want to phone home you should perhaps be asking why. Then make a decision on whether to restrict that ability on a case-by-case basis.
Restrict inbound traffic
Hopefully you can already imagine why letting all incoming traffic feel welcome is a bad idea. If, for whatever reason, you need to let some in, be selective.
Sure, some services may require port forwarding (I seem to recall having to forward multiple ports when connecting two Xboxes to my network) but you want to avoid it if possible.
If you really must engage in port forwarding then try and use uncommon ports and try and learn a bit about what you are doing before you begin.
Turn off WPS (WiFi Protected Setup)
An interesting feature that provides quick and convenient security in theory, but is susceptible to brute force attacks in practice.
Leave it switched off.
Disable unused services
Telnet? Switch it off.
SMB (Samba file shares)? Switch it off.
uPnP? Don’t think, just switch that thing off.
Unless of course you need them, in which case there’s a fair chance you already understand what you are doing or are well prepared to find out, long before you switch them on.
Except for uPnP which always stays off, got it? (If you’re wondering why, this Arron Finnon video will tell you all you need to know, but do watch out for the occasional swearing).
Check port 32764 for vulnerability
You know how your house has a back door? You wouldn’t leave it open all the time, would you?
I thought not, and that’s why you need to check whether port 32764 is vulnerable because, if it is, the back door to your router is wide open, a neon welcome sign is flashing above it and no-one even knows.
So, what to do? Easy, go to ShieldsUP – don’t worry, it’s not a Trekkie site – and follow the simple instructions.
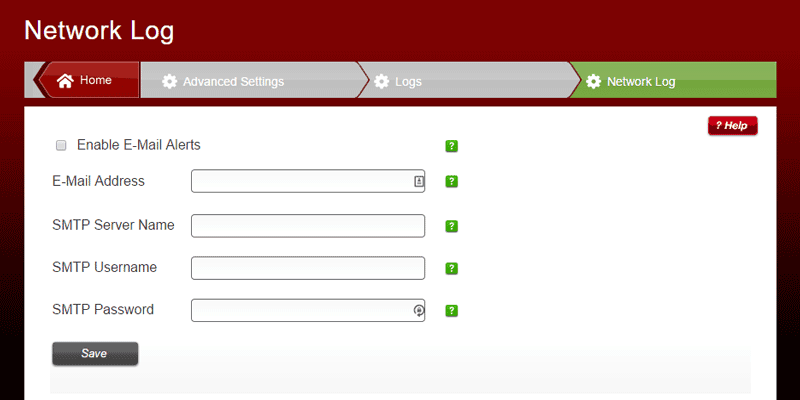
Enable logging
Most routers can log just about everything from the moment they are first switched on but sometimes that ability is not switched on by default.
Check that, and switch it on if necessary.
Read your logs from time to time!
Now your router is recording everything you’ll want to check those logs from time to time.
You’ll be looking for suspicious activity, such as unknown devices connecting to your network, connections on days/times when there shouldn’t be any and anything else that looks out of the ordinary.
You can check your logs manually through the router’s control panel or you can typically have them emailed to you on a schedule you define.
Log out when you’ve finished
Changed your login credentials? Excellent.
Now remember to log out when you are done or else you’ll be leaving an authenticated session running on your router and that’s not a good thing.
Securing your wireless router – concerned user
Once you’ve worked through the basics of router security you will almost certainly be more secure than the majority of your neighbours – but you may want to go further.
And why not, you can never have too much of a good thing, can you?
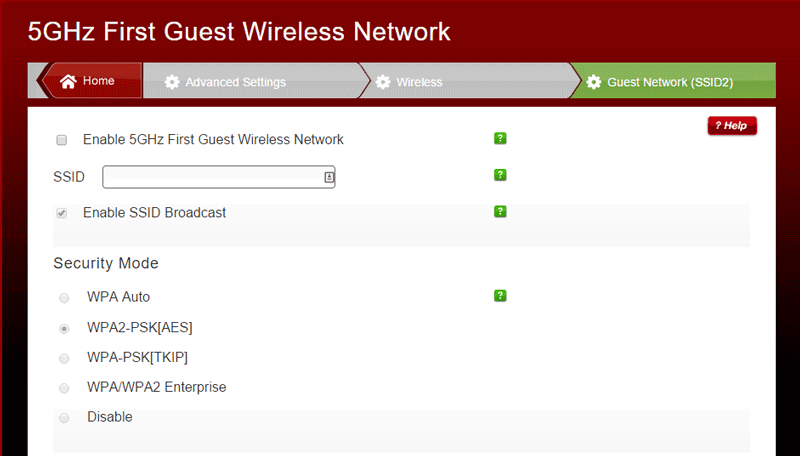
To guest or not to guest, that is the question
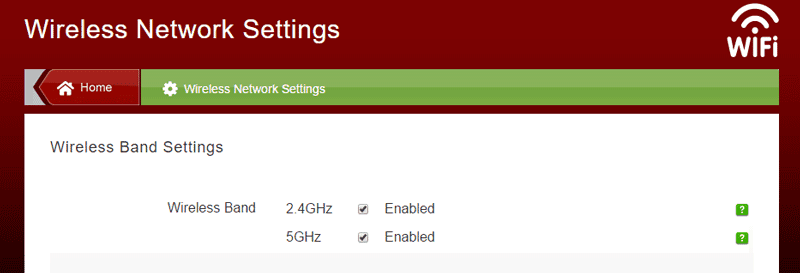
Most modern routers tend to offer 2G and 5G connections, secured by a password hopefully of your choosing.
Many also offer the ability to set up additional connections for ‘guests’ which you can choose to leave unprotected (bad idea) or configure as you see fit.
Personally I would never set up a guest network but if you must, the same rules apply – WPA2 encryption and a suitably long password.
And, whatever you do, do not allow it to have access to your own local network but, instead, restrict it to internet access instead.
Thou shall’t not connect USB storage
Some routers sport a USB port to allow easy sharing of external drives across your network.
That sounds great in theory but if you don’t know what you are doing, could be a catastrophic move that exposes everything on the drive to the internet.
If in doubt, don’t plug it in.
192.168.0.1 is for suckers
Got a router? Know its IP address?
Chances are, its something like 192.168.0.1 or 192.168.0.254.
Lucky guess, eh?
Nope, routers all tend to come with a similar range of IP addresses and any attacker worth their salt knows that.
That’s why it’s a good idea to change yours to something atypical that may just thwart an attacker that has gained access to your local network.
Sorry, SSID isn’t home right now
When you connected to your router for the first time did you notice how it had a unique name?
In days gone by, those names tended to quite handy to a hacker who could use them – in some cases – to determine your router’s password.
If you are using a modern router you can probably leave the SSID alone, but changing it may be wise on an older device.
Or you could just change it anyway – I’ve seen a lot of routers given the name of ‘GCHQ surveillance van’ in the vicinity of my own router. It always makes me chuckle while probably worrying a neighbour or two. It’s a bit childish though, don’t you think?
Return of the MAC, and no-one else
Theoretically sound, practically worthless, MAC address filtering allows you to create a ‘white list’ of devices that have permission to connect to your router.
Doesn’t work but I’ve heard the placebo effect is appreciated by some users so feel free to play around with this is you have time to kill.
Wrapping up
Hopefully this article has given you some ideas of how you can secure your router and wireless network while also debunking a couple of old practices that are now, or never were, worth your time.
Even if you implement all the good points, your network won’t be 100% secure, but as long as someone else’s is easier to break into, that will probably do, unless you are being specifically targeted.
In either event, look beyond your router as it is just one piece in the larger jigsaw puzzle we call security.
If you want to protect your computer you should also be thinking about your firewall, antivirus software, password choices, VPNs and much more besides.
Related: Best VPNs for DD-WRT routers


It’s really important to be concerned with your router. SO many bad things can happen if we are not aware. Thanks for this great post.