It’s always a satisfying feeling when you find that free wi-fi connection at a hotel, airport, or café. The temptation to hit connect is irresistible – what’s not to like about saving your mobile data? Complimentary internet, somehow, just feels better than the paid version.
However, public wi-fi doesn’t come without its potential downsides. While these hotspots are often safe, there is a chance that people with malicious intent (such as wanting to steal your data) are logged on to some networks. After all, they are available to anyone with a Wi-Fi-enabled device.
As alarming as this might sound, it doesn’t mean you have to avoid connecting to public wi-fi networks. If you take the proper precautions, you can enjoy a worry-free wi-fi experience.
How to use public Wi-Fi securely
In order to keep yourself safe and secure on a public Wi-Fi network, we recommend the following tips:
1. Distinguish between secured and unsecured networks
Generally speaking, there are two types of public wi-fi networks. A completely open network allows you to log on without any authentication details. All you have to do is simply click connect, and your smartphone or laptop will do the rest. We advise that you refrain from using this option, or only log on as a last resort and for a short period of time.
The other type of public wi-fi network requires you to sign up and enter details, such as a phone number and a valid email address. You might also have to create a username and password before the system grants you access. These could be either a large-scale Wi-Fi network provided by your cellular company or one at your local coffee shop, where the range is significantly less. Both are considered public Wi-Fi systems.
Such networks are considered far more secure as your personal details are saved. Would-be hackers aren’t usually in the business of giving away such details, so it’s a safe bet that they’ll leave these networks alone.
If you’re sitting in a coffee shop or cafe, ask the barista which Wi-Fi network to connect to. They’ll be aware of the official ones – put in place either by the mall or the shop itself – and will guide you accordingly.
Related: Airport wireless network – not as safe as you think.
2. Keep sensitive information at bay
If you’re using a public Wi-Fi network, it’s a good idea to avoid engaging in activities like internet banking, online shopping, or any other activity that might expose financial data.
It’s not a good idea to be filling out a webform with your bank account details, credit card information, or social security number while connected to a public wi-fi network.
If there’s a compelling need to transfer funds or take advantage of a flash sale, the prudent approach is to turn on your mobile data for this specific transaction. It’ll only take seconds and will keep your information secure.
Also, check out our guide: How to Safely Access Online Banking.
3. Turn off wi-fi when not in use
If you’re not using the internet but are in range of a public network, we advise you to simply turn off wi-fi. It’ll just take a few seconds and add an extra layer of security. After all, just enabling the option allows people to notice your presence and possibly snoop around. If you wish to reconnect to the internet, just switch wi-fi back on.
For Windows users, just click on the wireless icon in the system tray and turn it off. For Mac OS, find the wi-fi icon on the menu bar (that’s on the top right-hand corner of your screen) and switch it off. Both Android and iOS users will find the option to turn off wi-fi in the settings menu.
Related: Do VPNs work without Wifi?
4. Turn off sharing
In some cases, it’s possible to share files and printers, and turn on remote logins from other computers logged on to the same network. This setting is okay for networks you trust, like those at home and in the office, but should be avoided when connected to public wi-fi.
For Windows PC users, go to Control Panel > Network and Internet > Network and Sharing Center. Once you’re there, click Change advanced sharing settings. Turn off both network discovery and file and printer sharing.
For mac OS Sequoia, simply go to System Settings… -> General -> Sharing and turn off all of the switches. Earlier versions of macOS may be a bit different, but are similar.
5. Use a VPN
Short for Virtual Private Network, a VPN encrypts all the internet traffic going to and from your device. This effectively secures open wi-fi connections and makes it almost impossible for hackers to snoop on your activity.
A VPN is also an excellent choice for accessing restricted content such as that from US Netflix, Hulu, and BBC iPlayer. It works by tunneling the traffic via an intermediary server so that it appears you’re somewhere other than your current location.
We highly recommend NordVPN, but there are many other high-performance alternatives. Some even come with automatic wi-fi protection, so you know you’ll be secure every time you connect to a hotspot. You can find out more in our article about the best VPNs for public WiFi.
TRY THE TOP VPN RISK-FREE
NordVPN is offering a fully-featured risk-free 30-day trial if you sign up at this page. You can use the VPN rated #1 for public wifi with no restrictions for a month.
There are no hidden terms—just contact support within 30 days if you decide NordVPN isn't right for you and you'll get a full refund. Start your NordVPN trial here.
6. Stick to secure websites
Hyper Text Transfer Protocol (HTTPS) is an encrypted protocol through which your browser sends data to the website you’re currently visiting. Popular sites like Facebook and Gmail use the HTTPS protocol as it significantly reduces the chances of your private data being exposed.
To identify an HTTPS secured site, just look for the padlock icon in the browser next to your website address. Not all sites have this option, so don’t assume your browsing is encrypted by default.
To help matters, we recommend you install the “HTTPS Everywhere” browser plugin. This plugin forces you to connect to the secure version of a site, if available. Although, bear in mind that if there’s no HTTPS site, you’ll simply go to the unsecure version.
If you’re still wary of a site’s security credentials, we recommend you read through our guide of how to recognize secure sites.
7. Enable your firewall
The basic firewall present in your Windows or Mac operating system might not have the advanced, robust features that paid antivirus solutions offer, but it’s still a handy tool to ward off attacks.
For the uninitiated, a firewall is the first line of defense against hackers and acts as a barrier between trusted and untrusted networks. It’ll monitor all traffic and decide whether to accept or reject based on specific security parameters.
To enable your firewall in Windows, just go to the security settings. These are found in Control Panel > System and Security > Windows Defender Firewall (It may just say “Firewall”).
For macOS, go to System Settings… -> Network -> Firewall. Toggle the Firewall switch to the “On” position.
8. Keep your software updated
Most programs we use aren’t static in any way – developers are constantly tuning the code and patching up security vulnerabilities.
As a general rule of thumb, when your antivirus pings you to install a software update, you should follow the prompt and update. At the same time, you should do this over your home or office internet connection, not an unsecured public one.
9. Follow smart browsing principles
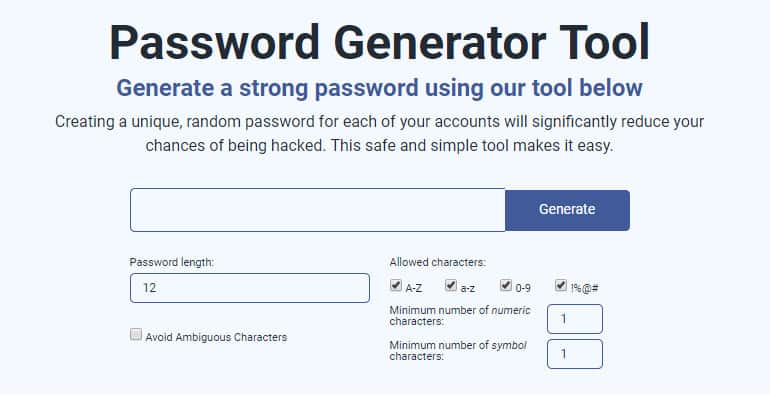
Other than all the practical tips outlined above, there are more steps for deterrence that you can apply too. Deploying strong passwords with a combination of uppercase, lowercase, and numerals is definitely recommended. If you’re stuck for options, you can use our password generator.
Use a password manager. This allows you to use secure and unique passwords without the need to remember each and every password. Many password managers will not only create and store your passwords, but they will also warn you when you attempt to reuse a password or if your password has been exposed in a data breach.
Enable two-factor authentication whenever you can – this is particularly important for social media, email, and banking. If you’re connected to a public wi-fi network, then don’t forget to log out of all your sites before you leave. Also, tell your device to “forget the network” – this prevents it from logging on to it automatically in the future.
Common dangers of public wi-fi
If you follow the steps above, then you should be able to stay safe while using public wi-fi. However, it’s good to know what you’re up against. In this section, we’ll take you through some of the methods hackers deploy to steal your data.
1. Man-in-the-middle attacks
Hackers use this technique to intercept communications between two entities, such as your device and the server it’s connected to. The flow of data is interrupted by the snooping hacker, allowing them to eavesdrop on your personal information and steal things like bank account information and credit card details.
Man-in-the-Middle (MITM) attacks are particularly prevalent on public wi-fi networks. Hackers set up rogue wi-fi networks with seemingly innocuous names such as ‘FreePublicWifi’ in a bid to lure users. Once you’re connected, the hacker will have direct access to your browsing session and all the data contained within. They might even be able to view your stored cookies, or bite-sized packets of data that store things like login information.
The effectiveness of MITM attacks was showcased by 7-year-old ethical hacker, Betsy Davis, who successfully infiltrated a public wi-fi network in under 11 minutes. A survey carried out as part of the demonstration revealed that 59 percent of British internet users frequently connect to public hotspots, with 19 percent of them using public wi-fi for sensitive transactions like personal banking.
One way to identify a rogue connection as opposed to a legitimate one is to check for authentication/login procedures. Trustworthy networks will usually ask for some personal details and for you to agree to a ‘terms of service’ before granting you internet access. If a network allows you to log in immediately without the need to punch in any data, that’s usually a red flag, and the network should be avoided.
2. Packet sniffing
A packet sniffer is robust software that’s used by system administrators to monitor network traffic. With its help, an administrator ensures a smooth flow of traffic by removing all bottlenecks on the network.
But there’s a downside. An intruder with malicious intent could infiltrate the software and use it to analyze all the traffic in the network. The purpose is the same: to steal personal information such as passwords, user IDs, and credit card information. However, intruders can remain invisible while they steal this data, so packet sniffing is generally viewed as a dangerous attack to quell.
There are three ways to carry out a packet sniffing attack. The first one is referred to as wireless sniffing, and involves a hacker gaining control of the system after forcing their way through the network. Some companies unwittingly make this process easier by forgetting to change the default admin settings on their routers.
Another way is for an employee of the firm who has access to the internal LAN to abuse his privileges to capture traffic. The last method involves the use of spoofing techniques by hackers outside the target network. Such techniques break through the firewall and make it possible to steal information.
3. DNS spoofing
DNS servers help manage the flow of internet traffic to and from your device. For example, when you enter ‘facebook.com’ on your browser, it first contacts its DNS server. The server then responds with an IP addresses that your device can use to connect to Facebook. It’s basically helping convert human-readable domain names to computer-readable ones.
DNS servers can turn malicious if a hacker gains access and changes some of the information. The server could be instructed to redirect common domain name requests such as ‘google.com’ to a site that the hacker owns and controls. In this case, you become a victim of a phishing attack (see below).
Such types of hacking attempts can be devastating on public networks. A hacker only needs to infiltrate one computer in order to disrupt the dozens of devices that are connected at any given time.
4. Phishing scams
Phishing attempts are used by hackers to obtain sensitive personal information such as your bank account details or credit card information, often for the purpose of stealing money. They’re usually disguised as links within official-sounding emails or other modes of communication, prompting users to hand over details.
In 2015, Australian comedian Casey Talbot was robbed of over US$10,000 from his personal bank account while connected to public wi-fi in Sydney airport.
Hackers first infiltrated the network and then proceeded to target his particular device via a malicious email. Mr. Talbot fell for the trap and handed over his information. The money was cleaned out immediately.
As a general rule of thumb, we reiterate that you should avoid any sort of financial activity over public wi-fi.
















i like this vpn