Your internet activities are transmitted through many routers and switches en route to their destination. Those packets are susceptible to collection and analysis at each of those points through a process called packet sniffing. This article explains what packet sniffing is and some practical advice on how to avoid it.
See also: Best Packet Sniffers & Best Network Analyzers
There are many forms of networking and the most common of all is TCP/IP. That acronym stands for Transmission Control Protocol over Internet Protocol which simply means the network sends TCP packets to destination computers using IP addresses. The critical part of this description is the word packets.
Contrary to what our eyes tell us, things like web pages and emails do not travel across the internet whole. They are disassembled at the sending end into small data packets and reassembled at the receiving end back into their original format. While those data packets are traveling across the internet, they are susceptible to eavesdropping and even modification. This technique is colloquially called packet sniffing and it is carried out by ISPs, governments, ad companies, and bad guys alike. In this article we look at ways to protect yourself from packet sniffing.
What is packet sniffing?
In order to understand how packet sniffing occurs, it’s helpful to understand how internet routing works. Web pages and emails are not sent through the internet intact as one document.
Rather, the sending side (your computer) breaks them down into many little data packets. These packets are addressed to an IP address at the receiving end which usually has an obligation to acknowledge receipt of every packet it receives. In order to support that, each packet contains the sending and receiving IP address as well as a lot of other information.
These packets do not get passed from the sender to the receiver in one fell swoop. Rather, each packet traverses the internet en-route to its destination by passing through a number of traffic control devices such as routers and switches. Each time a packet passes through one of these traffic control devices, it is susceptible to capture and analysis.
A note about routing and convergence
The routers’ role in this process is literally to route traffic to its destination. The routers of the internet have some idea of where the destination IP address is, or at least they know where to send the packet if they’re not directly connected to the destination.
This technique is called convergence because packets from all over the world converge on their destination by virtue of routing. Consider a large destination such as Facebook. It has traffic coming to it from all across the globe. As those packets get nearer to the actual Facebook servers, the disparate traffic converges into a very busy section of the internet. The routers at those locations need to be very robust and secure.
An easier comparison may be to consider a highway that has hundreds of off-ramps into various towns. All of the traffic that is destined for the town of Quahog will take the Quahog exit off the highway. That is a form of convergence in that these cars are just individual cars that don’t appear to have anything in common until they all start exiting at Quahog.
If an observer wanted to examine all the cars going to that town, it makes the most sense to sit at the Quahog highway exit since 100% of the cars taking that exit are the cars of interest. It makes less sense to sit elsewhere on the highway and examine cars because only a portion of those are destined for Quahog.
The NSA’s PRISM surveillance program uses this technique; the NSA packet sniffers “park” at the routers closest to big internet providers like Google and Facebook in order to collect as much traffic destined for those sites as possible.
Who packet sniffs?
Anyone who has access to a router can perform packet collection and subsequent analysis. Since internet users generally have no idea how their traffic is being routed, it’s not really possible to know who may be observing that traffic. However, history has shown the following actors have been involved in packet sniffing for various reasons over the years.
A note about routers
Most of us probably think about the wi-fi router in our houses when we hear the word router. That’s entirely correct. The consumer-grade router in your house does the same job as the big commercial routers on the internet. Your home router is responsible for accepting traffic from the various internet-connected devices in your home and routing them out to the internet. It is also responsible for accepting response traffic from the internet and routing it back to the specific device that requested it. The only real difference is that internet routers do that for millions of devices, whereas your home router would not be up to such a monumental task.
Government agencies
United States
The Snowden papers revealed a massive surveillance apparatus, named PRISM, that the United States Government had been deploying in secret for years. In particular, the National Security Agency (NSA) has been passively collecting internet traffic destined for large internet sites such as Facebook, Google, and others. The NSA has large-scale analysis tools such as XKeyscore which allow it to search through the collected packets at a later date.
United Kingdom
The United Kingdom has a similar passive collection surveillance system named Tempora. The UK is uniquely positioned in that most of its internet traffic arrives at the UK via undersea fibre optic cables. This provides a single point of entry and egress to and from the UK and the Tempora collection devices operate at these locations.
Another dozen or so countries are also known to conduct mass internet surveillance. All internet surveillance would require some form of packet collection and analysis.
Businesses
Internet surveillance is not limited to governments. Industrial espionage has been a thing for decades and there’s no doubt that some corporations employ techniques to determine what their competitors are doing.
Business espionage agents generally do not have the luxury of government warrants to demand access to internal networks and routers in order to collect packets. Therefore, most internet-based industrial level espionage likely relies on tried and true methods such as phishing to gain access to internal networks. Once entry is gained to the target network, the collection and analysis of data packets can contribute a wealth of knowledge.
Advertisers
Ad agencies are notoriously unscrupulous, especially internet ad agencies. Agencies like this are typically paid in one of two ways: either the number of ads they show (Cost Per Thousand – CPM) or by the number of ad clicks the ads garner (Pay Per Click – PPC).
In either case, the more impressions an ad gets, the higher those numbers. Advertisers can use packet sniffing to either surveil users to gauge their market tastes, or – even worse – to inject ads into incoming packets as they go by,
Comcast was discovered to be sniffing packets on its network in order to determine the optimal place to inject ads into arbitrary web pages that its users were viewing.
Aside from the ethical issues of modifying content that neither belongs to Comcast, nor resides on its network, it doesn’t take much imagination to speculate on other things that can be injected into packets on the way by.
Internet ads are known to contain malware in many cases. When an actor such as an advertiser can take over the traffic destined for your computer and insert arbitrary content, much of which is know to be malware, that circumvents many protections you can put in place yourself. While Comcast was injecting ads via javascript, an attacker can just as easily inject javascript that silently steals your credentials.
Bad guys
Bad guys are always up to no good. Many of them are skilled and are able to use a wide variety of methods to steal information from you. Phishing remains the number one method by which bad guys get access to information such as logins and financial data.
But, phishing isn’t just after one type of information. A normal citizen may be phished for their credit card information that the bad guy can then sell for a profit. In contrast, a systems administrator at a bank may be phished for their login credentials. The bad guy can then hide on the bank’s internal network, sniff packets, and collects financial data on all of the bank’s customers. Many insidious and deeply penetrating attacks start with a simple phishing email.
Another very common vector for smaller scale bad guys is to set up a fake wireless access point at public places such as coffee shops, and collect the data packets of unsuspecting people who have unwittingly connected to it.
Malware can contain packet sniffers that monitor users’ online activity, sending data back to a hacker’s command-and-control center. The VPNFilter Malware, which infected half a million wireless routers in over 50 countries, included a packet sniffer in its third stage. VPNFilter intercepts data packets containing login credentials and sends them to the hackers over the Tor network.
Why is it bad for me?
Having your traffic watched is bad for a few broad reasons, and hundreds of smaller reasons.
Personal information
Consider how much personal business you conduct online. Most of us do our banking, set up medical appointments, write emails with personal details, and carry on long-term chats with our friends and family online. How much of that information would you like to become public, or at least, to be read by other people?
It’s easy to imagine bad guys stealing your credit card numbers, but what about more subtle information? Would your insurance company like to know you’ve recently had an angiogram? Would your soon-to-be new employer like to know you’ve just scheduled an appointment at a family clinic? Would your bank like to know you’ve recently lost your job? The reason we call a class of information “personal information” is because it is personal, and it is for us to control the distribution of that knowledge.
Yes, you do have something to hide
There’s a group of people who take the stance that they don’t care if they are surveilled over the internet because “I have nothing to hide.” Quite frankly, this shows a fundamental misunderstanding of the problem. Packet sniffing is conducted by bad guys attempting to do harm as much as it is by law enforcement agencies. Since there is no way to configure a data packet to allow law enforcement to read it, but not the bad guys, there is no other conclusion than we do all, indeed, have something to hide.
Business information
Businesses generally conduct themselves with a veil of secrecy over their upcoming endeavors. A business that is in negotiation to purchase a competitor, or to build a new location at a strategic location, could suddenly become very disadvantaged if that information were to fall into the wrong hands.
In the case of real estate, a business generally has a “go, no-go” point when a large investment is made. If sensitive information were leaked after that point it’s possible for a business to lose large amounts of money. This can lead to job loss, and in smaller regions, real economic impact. One of the ways information like this is leaked is through industrial espionage, which can include packet sniffing insecure emails and messages.
How to protect yourself against packet sniffing
In order to understand how to protect yourself against packet sniffing, it is important to know what your traffic looks like in different scenarios. I’ll focus on the web but the same principles apply for any internet communication such as email and messaging. Using plain unencrypted HTTP is the worse possible security posture. Using HTTPS (SSL encrypted sessions) offers more protection, but not quite as much protection as a VPN can provide.
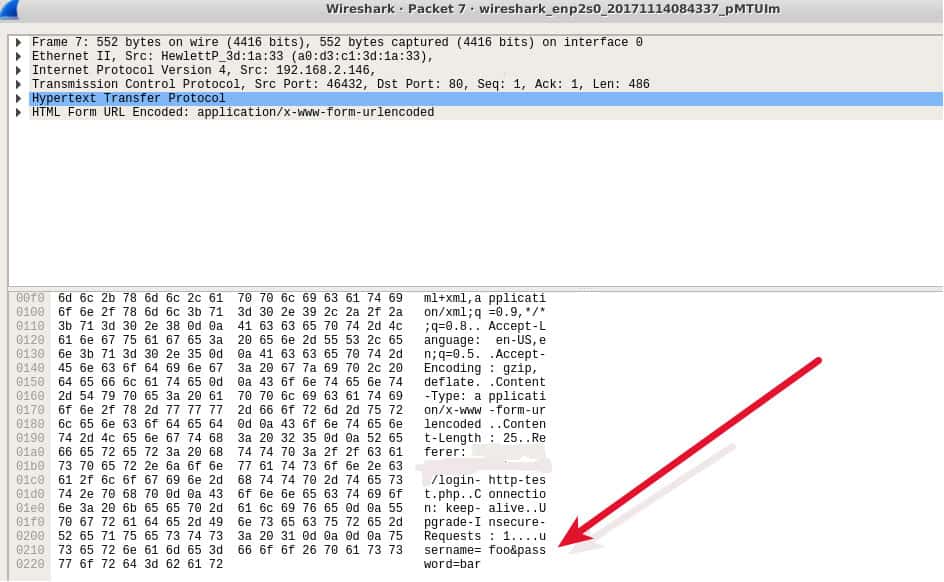
First, let’s start with a login form on an unencrypted website only using HTTP. I think it is fairly common knowledge by now that if you’re entering data into a website that does not display HTTPS and/or a lock in its address bar, that this is not secure. Most mainstream browsers now prevent users accessing non-HTTPS sites. This has forced the majority of sites to adopt HTTPS. Nevertheless, outliers exist.
I created a mock login page and logged in with the username foo and the password bar. This screenshot shows the Wireshark capture of that login. An observer can easily see my username and password and use it later to log in to my account.
Next, I visited the Comparitech website, which forces users to HTTPS. I typed comparitech.com into my browser to start this off. The first thing to happen is that my system did an unencrypted DNS lookup to get the IP address of comparitech.com.
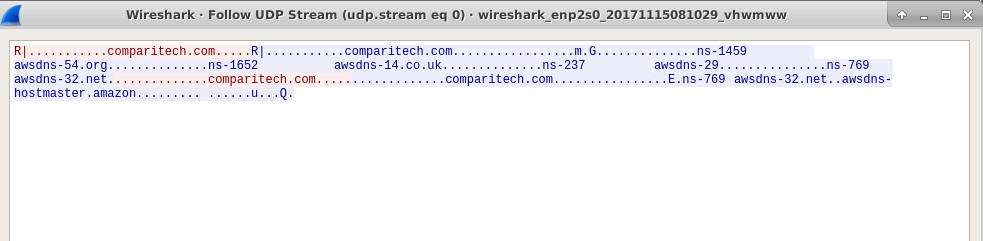
This information tells any observer that I am about to visit the Comparitech website.
My browser then attempted to connect to comparitech.com. We can see the website will not allow unencrypted HTTP connections so it sends headers back to my browser that instruct it to retry using HTTPS:
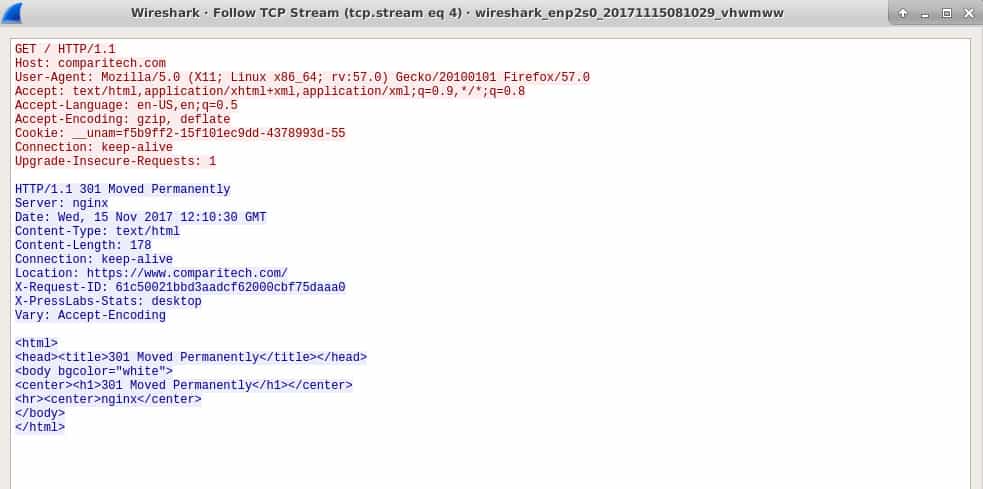
My browser does so and from then on my session is encrypted. This process is a little better than plain HTTP because my subsequent login to the site, as well as all my other activities on the site, are now encrypted.
But, this process has still provided an observer with the information that I visited the Comparitech website. This is called meta data and it is the crux of how most of the government surveillance programs justify their spying. These programs attempt to state that metadata is not valuable, but that’s clearly not true. Knowing where people go online is of great value.
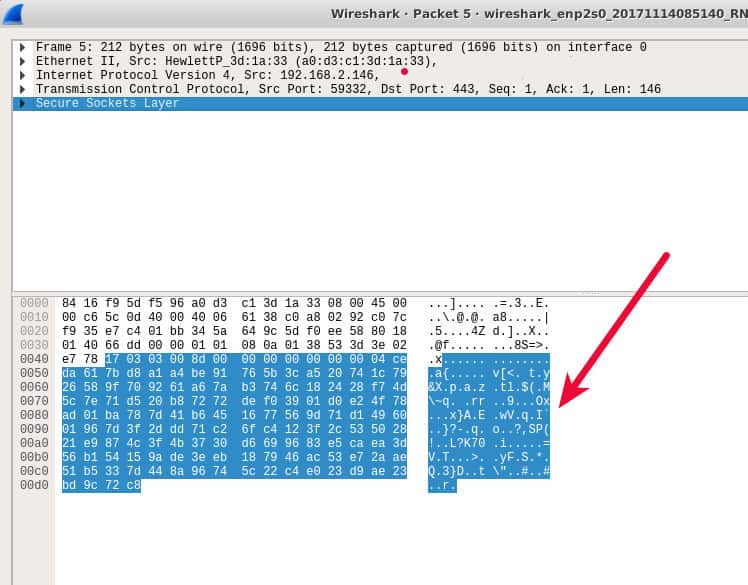
This is a screenshot of what an observer can see of my activities on the site using HTTPS. It’s mostly encrypted gibberish.
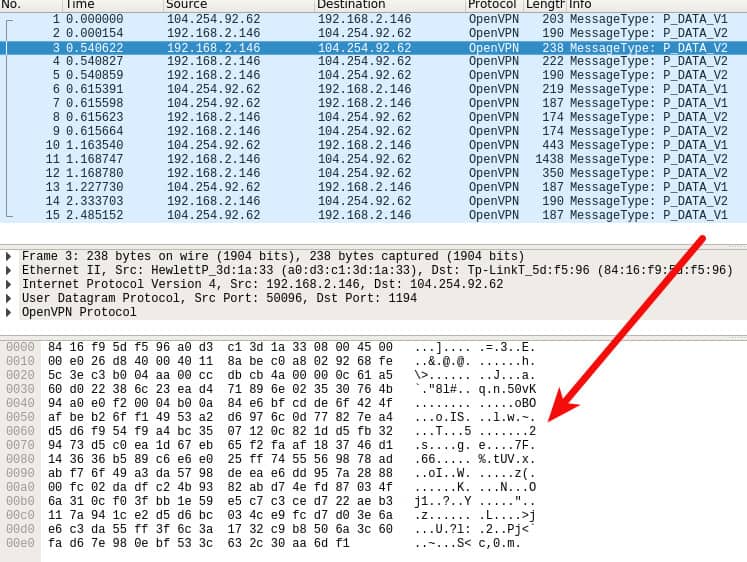
Finally, I captured some packets when my VPN was running. In this case, everything is encrypted. The only thing an observer can get from observing my traffic is a bunch of encrypted OpenVPN packets destined for an OpenVPN server.
My traffic is encrypted in bulk on my computer before it is sent through the VPN and it is not decrypted until it arrives at the VPN server. The VPN server then peels off the encryption layer it added on the sending end, and then sends the traffic on to its destination on my behalf.
Note that I am also routing my DNS through my VPN so even my DNS queries are encrypted and invisible to an observer.
Based on these example packet captures, the rules for protecting yourself from packet sniffing are:
Use a VPN all the time
The packet captures above show that VPN connections provide the most complete protection. Your traffic is completely encrypted and, if you ensure your DNS queries also go through your VPN, your destinations cannot be derived.
The only party that can see your traffic is your VPN provider since they need to remove the VPN encryption in order to see where the traffic should go. You’ll need to have some level of trust in your VPN provider to ensure they do not do things like log your traffic.
Providers like NordVPN adhere to strict no-logs policies that have been verified via multiple third-party audits. They also provide currently uncrackable encryption to keep your data safe from packet sniffers.
You can increase your level of anonymity and privacy by using Tor with a VPN. NordVPN provides one-click access to the Tor network, which does away with the need to download and install the Tor browser.
TRY THE TOP VPN RISK-FREE
NordVPN is offering a fully-featured risk-free 30-day trial if you sign up at this page. You can use the VPN rated #1 by Comparitech with no restrictions for a month.
There are no hidden terms—just contact support within 30 days if you decide NordVPN isn't right for you and you'll get a full refund. Start your NordVPN trial here.
Always use HTTPS when available
If you’re visiting one of the few sites that still use HTTP, see if it will accept an HTTPS connection by simply tying https:// in the browser bar before the site address. Many websites have SSL certificates in place, but the website maintainer isn’t actively forcing visitors to use it. Better still, turn on your browser’s HTTPS-only mode. The Electronic Frontier Foundation provide instructions on how to do it.
It’s worth noting that you should continue to use HTTPS even if you’re using a VPN. This is because an HTTPS encrypted payload can only be decrypted by the destination web server or by your own browser. A VPN provider will have to decrypt the VPN encryption it added to the packet, but it won’t be able to decrypt the HTTPS packet itself which means your VPN provider would only be able to collect the metadata.
Never send form data using HTTP
If you’re in a situation where you’re simply unable to use a VPN or HTTPS, then you should avoid sending data to a website at all. Specifically, this means do not fill in any form boxes or click any form buttons on a website. Forms send data from your computer to the web server and the most common places we see this is in login forms, contact forms, and other pages that collect information from you.
Any time you send data to a website using unencrypted HTTP, that data is clearly visible to an observer. The first screenshot in this section illustrates how easy it is to see my username and password in an HTTP packet; any information you send over HTTP will be equally visible.