Businesses are slowly waking up to the threat that phishing poses, with many introducing mandatory training in recent years. However, research shows that cybercriminals are increasingly targeting CEOs and executives instead of frontline staff. After all, with nearly half of all such attacks succeeding, there’s clearly value in going after the bigger fish (hence the terms “whaling” and “whale phishing”).
One of the biggest problems is that every whaling attack is personally-tailored to fit the target. Unlike traditional phishing, it usually doesn’t involve tricking you into clicking on a malicious link or downloading malware. Instead, criminals use information they’ve gathered elsewhere to gain your trust before stealing data, transferring funds, or locking down your systems. In addition to reputational damage, impacted businesses often suffer huge financial losses, sometimes even having to cease operations entirely.
Types of whaling attacks
At its heart, whaling is identical to spear-phishing; the only difference is that the target tends to be someone with more access and decision-making power. While this means that attackers must first work harder to convince the victim that they’re genuine, the potential rewards are significantly greater.
Here are a few of the most common ways criminals gain your trust:
- Following up urgent emails with a phone call: Executives often drop their guard when speaking on the phone, especially if the caller references a previous email and implies that there’s an urgent issue that needs their input. However, thanks to the advent of AI-powered voice-cloning and number spoofing, it’s harder than ever to tell if the person on the other line is who they claim to be
- Impersonating collegues or business partners: Plenty of companies list their partners’ names online. Attackers often create fake email addresses and try to get that person’s subordinates to help compromise the organization without realizing that they’re speaking to an imposter.
- Providing detailed information about the company: Sophisticated attacks often come after long periods of data-gathering. This allows criminals to know exactly who to target, what their duties are, and what access they have. However, mentioning confidential information doesn’t guarantee their authenticity as it may well have come from publicly-available sources or even previous successful phishing campaigns
- Sending malware to company addresses: Infected USB sticks may turn up at the office, employees’ homes, or even outside in the parking lot. These are often designed to create a backdoor into your device or network that can be used to harvest even more information
- Social engineering: Criminals frequently pose as potential business interests, suppliers, or peers to try and get close to their targets. This may be done via social media, LinkedIn, or anywhere senior exectives can be spoken with informally
Telltale signs of a whale phishing attack
Your standard phishing email is usually fairly easy to spot, with typos and suspicious links out there in plain view. In contrast, whale phishing is much more sophisticated. You’ll have to stop for a moment, read between the lines, and really think about what’s being asked of you. Here are few key characteristics that indicate the email you’ve received may not be legitimate:
- You’re urged to make a snap decision in order to avoid some form of major problem. This could be preventing fines, becoming compliant with local law, or ensuring everyone is paid on time.
- The victim is asked to transfer funds or send data (particularly payroll information) in a manner that’s different from the norm. Often, this is a “one time thing”, specifically to avoid the consequences alluded to earlier
- The employee or supplier contacts you from a new email address or phone number, or asks you questions that they should already know the answers to
- You’re asked to enter information on a newly-created website, or to update your data on “the new system”
How to protect yourself from a whaling attack
First of all, it’s important to remember that no system is 100 percent secure. A determined team of attackers will eventually be able to compromise just about any organization. That said, you can make yourself a much less appealing target and protect your business by implementing a robust data-protection policy. This may include:
- Ensuring no single employee has full access to all of a company’s resources
- Requiring monetary or data transfers to be signed off on by multiple people
- Periodic cybersecurity training and compliance tests with a specific focus on phishing-recognition
- Preventing employees from sharing certain information about their role and duties online
- Implenting screening tools to check for malicious links, external emails, and signs of social engineering
- Requiring multi-factor authentication on company devices
- Having strict password-creation rules and requiring these to be changed regularly
- Banning the use of private email and social media on company systems
- Using data-removal services to limit the amount of information that attackers can find about the target online
Shield yourself from whaling with Incogni
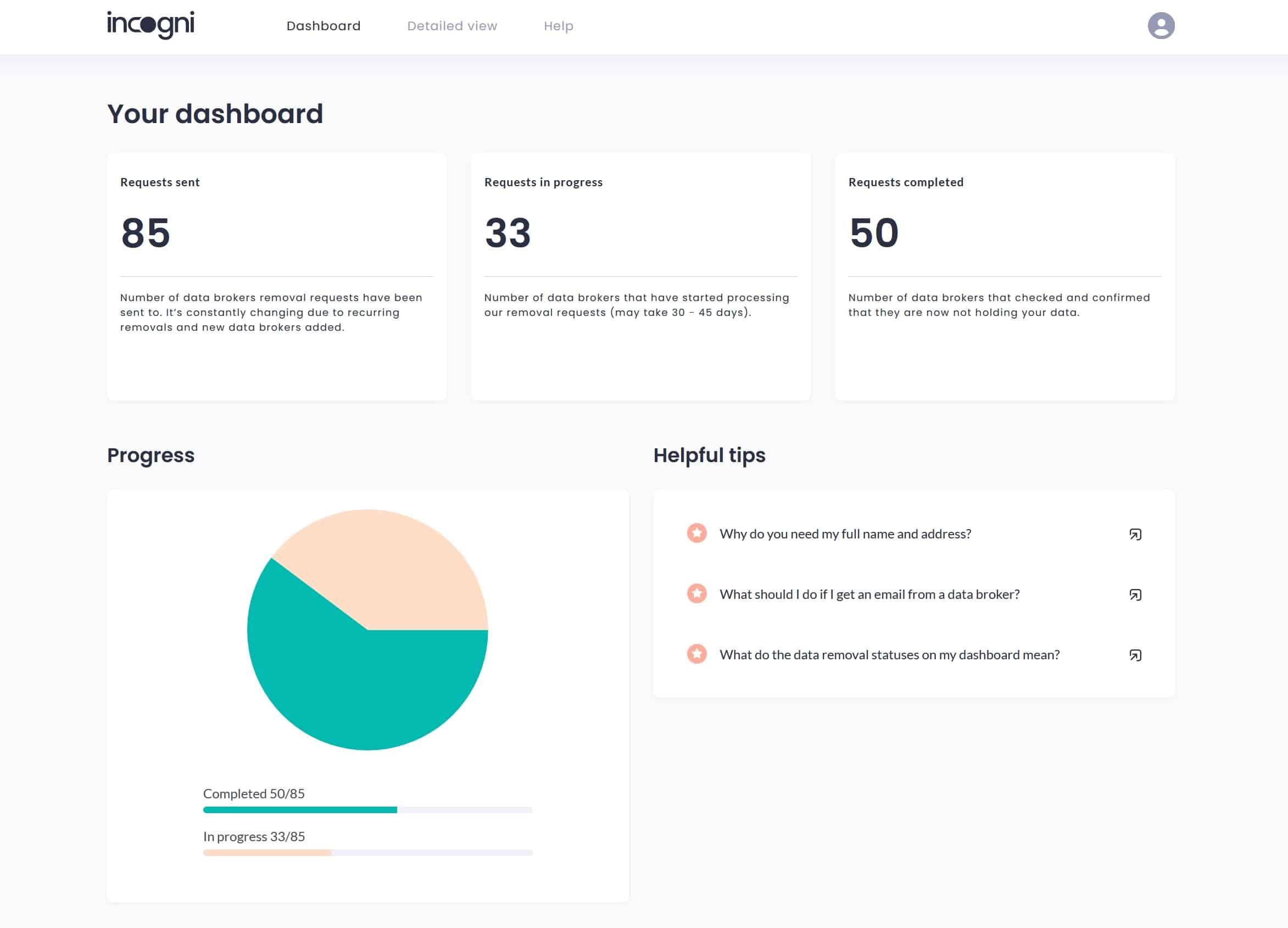
Scrubbing your Facebook of sensitive information is easy. What’s harder is getting yourself removed from the multitude of people-search and data-aggregation sites. Incogni simplifies this process, automatically sending removal requests to over 100 data brokers to ensure that information such as your Social Security number, home address, and phone number are never publicly-available. Better still, Incogni checks in regularly, preventing your data from being reacquired.
Once you’ve signed up, Incogni gets to work right away. Users can monitor the process of takedown requests, but there’s nothing further you need to do. The service claims to save the average user more than 300 hours of effort, and with a CEO’s time already in very high demand, that truly is invaluable.
Incogni is currently offering a 50 percent discount on one-year plans, allowing you to keep your data off the market for as little as $5.79 USD per month.
Examples of business whaling attacks
Just visiting the wrong web page is enough to get malware onto a company’s network through a high-level user account. You could set up a site covering a subject of interest to the target that downloads spyware automatically. An example of whaling used to facilitate such a fileless malware attack is Operation Cobalt Kitty, which was launched against an Asian corporation in 2017.
Next, you could create a copy of the target company’s website so it is possible to send legitimate-looking emails. Imagine you wanted to pose as Barry Hartnell, CEO of Magimeg Corp. Let’s say that Magimeg Corp’s website has the domain magimeg.com. The scammer buys the domain magimegcorp.com and sets up an email account for barryhartnell@magimegcorp.com. They can then send out instructions to the CFO to transfer funds to an account in the Cayman Islands.
Such scams are more likely to succeed if the locations and the actions in your messages make sense. That’s why attackers frequently learn he victim’s schedule and what activities that person regularly performs ahead of time.
In this example, if Barry Hartnell was sitting in his office when you sent the email, the scam would collapse as soon as the CFO walked down the corridor to ask Barry for confirmation. However, if Barry Hartnell was actually in the Cayman Islands at the time to carry out a takeover of a local company, the request for a transfer of funds would make perfect sense.
A whaling attack might not be as simple as wiring money. Executives could send instructions to buy products, with payments going to an attacker’s account. Alternatively, the HR director could ask the IT department to set up a user account with system privileges for the (fictional) new network administrator who will be working from home.
High-profile whaling attacks
Corporations that have been stung by any type of hacker attack often don’t want this info out there. So, it is very difficult to get a full picture of the prevalence of whaling. We do, however, have plenty of major incidents on record. Here are just a few:
- Hackers got employees at Ubiquiti Networks to transfer $46 million
- Belgian bank Crelan was conned into transferring more than 70 million Euros
- An Australian hedge fund closed following an $8 million whaling incident
- Cinema chain Pathé sends almost a million euros to scammers
- HR employee from Snapchat inadvertently sends attackers payroll info