 Like all network proxies, a transparent proxy intercepts and redirects data in transit, typically through the internet. In plainest terms, transparent proxies do not modify the data that pass through them. But what really sets transparent proxies apart is that clients—end user devices used by you and me—don’t need to configure or even be aware of the proxy in order for it to work. Transparent proxies are sometimes called inline, intercepting, reverse, invisible, or forced proxies.
Like all network proxies, a transparent proxy intercepts and redirects data in transit, typically through the internet. In plainest terms, transparent proxies do not modify the data that pass through them. But what really sets transparent proxies apart is that clients—end user devices used by you and me—don’t need to configure or even be aware of the proxy in order for it to work. Transparent proxies are sometimes called inline, intercepting, reverse, invisible, or forced proxies.
If you’re a frequent internet user, you probably interact with transparent proxies all the time without realizing it. Chances are, your internet service provider uses transparent proxies whenever you want to access popular websites, videos, and news articles. Instead of sending and receiving a video from Netflix’s server across the country every time someone wants to watch it, your local ISP will “cache” a copy of the video on its own servers. When you go to watch the video, the transparent proxy will redirect you to the cached version of the video, saving upstream bandwidth. As an end user, you get higher-quality video with less buffering, but otherwise the experience is indistinguishable from a direct connection to Netflix.
Transparent proxies are integral to content delivery networks, or CDNs, that perform caching on a large scale. But that’s just one of many applications. In this article, we’ll discuss in more detail how transparent proxies work, how they are used, their pros and cons, and how to detect and bypass them.
How transparent proxies work
To the end user, a transparent proxy is basically malware. It intercepts internet traffic and redirects it to another destination without the end user’s consent. This essentially describes a man-in-the-middle (MITM) attack. However, transparent proxies are not always malicious.
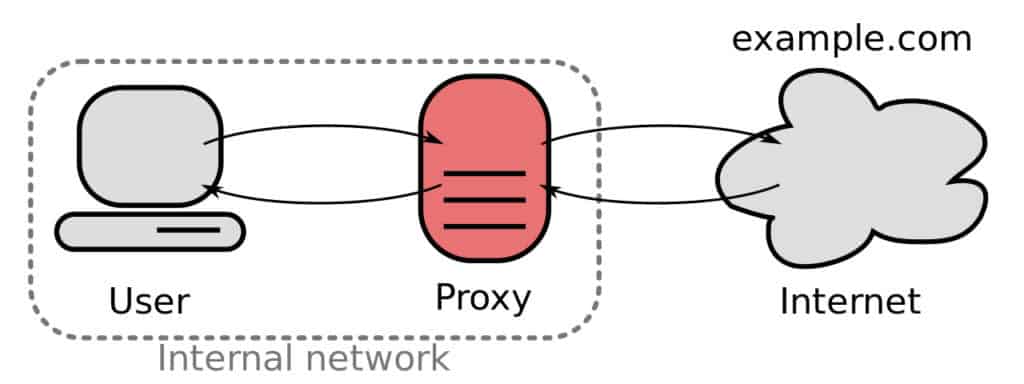
Transparent proxies usually sit between users and the web. When a user sends a request to connect to, say, a website, it is first redirected to the proxy server. Redirection is usually handled by a firewall on the same host as the proxy server, such as iptables on Linux.
The proxy server receives the request and then asks the redirector–the firewall–for the original destination of the connection. It can then decide whether to allow the connection to go through to the original destination, block the connection, or redirect the connection.
Squid is the most popular software used to set up transparent proxies.
How transparent proxies are used
Transparent proxies do not require any configuration on the client side, so users don’t need to download any apps or make any configuration changes on their end to use them. Instead, configuration is left to the service provider, which has greater control over how users interact with their services. This makes transparent proxies useful for situations in which the quantity and types of clients on the network are unknown.
Caching
We briefly described proxy caching in the introduction. Whenever a user connects to a website to, say, watch a video, a copy of the video is stored in a cache on the proxy’s host server. The proxy redirects future requests for that video to the cached version, and the user never knows the difference. Similar methods are used in large-scale content delivery networks (CDNs).
Proxy caching saves the ISP upstream bandwidth that would have been used to stream the video all the way from the source upon each request, and the user’s video buffers more quickly.
Filtering
Filtering proxies are used to restrict access to resources on the network. If that network is the internet, then filtering proxies can be used for censorship. An office building’s proxy could disregard requests to Facebook and YouTube in order to keep employees on task. Schools and libraries often employ filtering proxies to prevent users from accessing inappropriate content. Nation-states can use filtering proxies to monitor and censor content that they deem inappropriate or offensive.
Gateway
Have you ever connected to a public wifi hotspot that required you to agree to the provider’s terms of service, log in with your email, or watch an ad before it would allow access to the internet? Chances are, that network was using a gateway proxy. Transparent proxies can modify or block traffic based on certain rules, selectively restricting access to the internet. In this example, the proxy redirects users to a login page.
DDoS protection
Proxy DDoS protection, or “remote” DDoS protection, is a technique that uses a transparent proxy to prevent distributed denial-of-service (DDoS) attacks from crippling networks. A DDoS attack involves flooding a server with junk requests, often from a botnet that includes multiple devices. When a DDoS attack hits the proxy server, it prevents the flood of packets from hitting the main server. Users who can’t connect through the proxy due to congestion from the attack are simply redirected to another transparent proxy. A server can have as many backup transparent proxies as necessary to fend off junk requests and keep the site up and running for legitimate users.
Traffic Monitoring
ISPs and network administrators have many ways of monitoring traffic, and a transparent proxy is one of them. It can be used to monitor traffic such as requests and connection statistics on a network. Of course, this could be done for nefarious reasons. For example, the operator of a public wifi network could use the transparent proxy to steal the data and credentials of users.
Authentication
Transparent proxies are sometimes used by Internet providers as well as public wifi hotspots to authenticate users on a network. Chances are you’ve attempted to connect to a public wifi network only to find that you have to authenticate and agree to the terms of service. Failing to do so means that the network remains restricted and you won’t be able to browse.
How to detect if you’re behind a transparent proxy
A simple way to check whether or not you’re behind a transparent proxy is to attempt to connect to a server you know does not exist. If there’s no proxy, you’ll see a typical error message in your browser. Chrome says, “This site can’t be reached,” because the IP address cannot be found.
If you are behind a proxy, the error might be different or you might be redirected to another page, such as a search page.
If that doesn’t give you a straightforward result, a few websites have proxy detection services with varying reliability, like this one.
If you visit an HTTPS-encrypted website and click on the lock icon, your browser will give you some basic information about the site’s SSL certificate. If the certificate is issued to your ISP and not the website owner, that could be a sign that you’re behind a transparent proxy.
VPNs and HTTPS vs transparent proxies
In a standard, non-encrypted connection, internet traffic can be monitored and filtered by a transparent proxy. The data contained therein can be cached on the proxy server for later use.
HTTPS
Websites that use HTTPS secure browser traffic between the server and client with SSL encryption. The encryption scrambles the data before leaving the device, making it indecipherable to anyone who intercepts it. However, DNS traffic is typically not encrypted and tells the proxy server where the encrypted HTTPS traffic is going. The actual contents of network traffic may not be visible, so the data can’t be cached, but the proxy can at least see where it’s going. (Note: This is why transparent proxies are often incompatible with encrypted DNS, or DNSSEC.)
Transparent proxy software like Squid can handle HTTPS traffic in a few different ways, but generally the proxy can still monitor the destination of data in transit through some means. In some cases, network administrators set up HTTPS interception on transparent proxies. The proxy server acts as a man-in-the-middle with its own HTTPS certificate authority. In this scenario, HTTPS traffic is intercepted and decrypted at the proxy server instead of the destination website. The data can then be cached, filtered, or inspected before being re-encrypted and sent on to the destination.
VPN
If you’re behind a transparent proxy and you want to bypass it altogether, then use a VPN. A good VPN encrypts all traffic leaving your device, including DNS and HTTP/S traffic. Without knowing the contents or destination of your data, the transparent proxy cannot take action and will simply forward it to the destination unmodified (unless it explicitly blocks traffic to the VPN server). Note that a VPN will make the proxy cache inaccessible, which can make things slower for the end user.






