A brute force attack is a method used to obtain private user information such as usernames, passwords, passphrases, or Personal Identification Numbers (PINs). These attacks are typically carried out using a script or bot to ‘guess’ the desired information until a correct entry is confirmed.
These attacks can be used by criminals trying to access data that is otherwise protected by credentials. While you might think a password keeps your information safe, research has shown that any eight-character password can be cracked in less than five minutes
A brute force attack can also be a useful way for IT specialists to test the security of their networks. Indeed, one of the measures of a system’s encryption strength is how long it would take for an attacker to be successful in a brute force attempt.
Because brute force certainly isn’t the most sophisticated form of attack, various measures can help block these types of threats. In this post, we explore brute force attacks in more detail, including some examples, and then reveal how you can protect against them.
An introduction to brute force attacks
Brute force attacks are often referred to as brute force cracking. Indeed, brute force – in this case computational power – is used to try to crack a code. Rather than using a complex algorithm, a brute force attack uses a script or bot to submit guesses until it hits on a combination that works.
There are plenty of tools easily available to help hackers launch brute force attempts. But even writing a script from scratch wouldn’t be too much of a stretch for someone comfortable with code. While these attacks are easy to execute, depending on the length and nature of the password and the computational power used, they could take days, weeks, or even years to be successful.
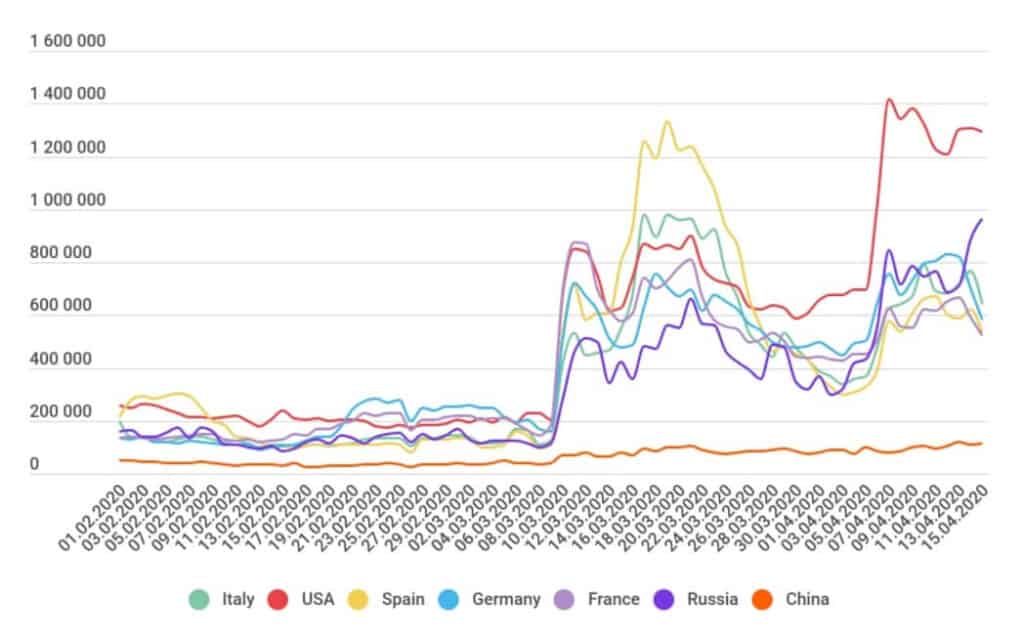
Although brute force attacks have been around at least since they were first documented in 1977, they became particularly prevalent in 2020, when cybercriminals began taking advantage of the increase in the number of remote workers.
An April 2020 report from Kaspersky found that the number of brute force attacks on Remote Desktop Protocols (RDPs) increased 400 percent in March and April.
Before we look at how to spot and prevent brute force attacks, we should note some other terms you may come across related to this topic.
Hybrid brute force attacks
A brute force attack uses a systematic approach to guessing that doesn’t use outside logic. Similar attacks include a dictionary attack, which might use a list of words from a dictionary to crack the code. Other attacks may start with commonly used, weak passwords.
These are sometimes described as brute force attacks. However, because they use some logic to decide which iterations may be the most likely first, they are more accurately referred to as hybrid brute force attacks.
Reverse brute force attack
A reverse brute force attack involves using a common password or group of passwords against multiple possible usernames. This doesn’t target a single user but might be used to try to gain access to a particular network.
The best protection against this type of attack is to use strong passwords, or from an administrator’s point of view, require that strong passwords are used.
Credential stuffing
Credential stuffing is a unique form of brute force attack that uses breached username and password pairs. If a username/password pairing is known, an attacker can use it to attempt to gain access to multiple sites. Once in a user’s account, they have full control over that account and access to any of the details it holds.
Precautions like two-factor authentication and security questions can help prevent damage by these kinds of attacks. However, the best protection is for users to never use the same password for multiple accounts.
The goal of a brute force attack
Once a hacker makes a successful login attempt, what’s next? Here are some of the possibilities:
- Stealing or exposing users’ personal information found inside online accounts
- Harvesting sets of credentials for sale to third parties
- Posing as account owners to spread fake content or phishing links
- Stealing system resources for use in other activities
- Defacement of a website through gaining access to admin credentials
- Spreading malware or spam content or redirecting domains to malicious content
As mentioned, brute force attacks can also be used to test for vulnerabilities in the system, so are not always malicious.
Examples of brute force attacks
Brute force attacks take place all the time and there are many high-profile examples to speak of. We likely don’t even know about many bygone and ongoing attacks, but here are a few that have come to light in recent years:
- Cisco VPNs: Bad actors targeted Cisco Adaptive Security Appliance (ASA) SSL VPNs with brute force attacks lasting five months in 2023. The attacks aimed to guess login credentials in order to gain access to the VPN appliances, after which they accessed victims’ networks. More than 11 organizations were reported to have been affected in the attacks.
- Canadian Revenue Agency (CRA): In August 2020, a credential stuffing attack resulted in the hacking of more than 11,000 accounts for the CRA and other government-related services.
- Arkansas county: In 2023, threat actors attempted to brute force their way into Arkansas county’s computer systems. Officials said the attack ended after more than 64,000 login attempts were made.
- Dunkin’ Donuts: The popular coffee franchise has been ordered to pay hundreds of thousands of dollars in response to a 2015 incident where credential stuffing and brute force attacks were used to steal money through the chain’s mobile app and website.
- Alibaba: A massive 2016 brute force attack on the popular ecommerce site affected millions of accounts.
- Magento: In March, 2018, Magento had to warn users that up to 1,000 admin panels had been compromised as a result of brute force attacks.
- Northern Irish Parliament: Also in March, 2018, the accounts of several members of the Northern Irish Parliament were accessed by brute force attackers.
- Westminster Parliament: An earlier attack hit Westminster Parliament in 2017 where up to 90 email accounts were compromised.
- Firefox: It was revealed early in 2018 that Firefox’s ‘master password’ feature can be easily brute-force attacked. This meant that over the previous nine years, many users’ credentials may have been exposed.
Even though brute force attacks are often used by criminals, they can help to test systems. What’s more, they can offer a backup option for password recovery if other methods have been exhausted.
How to spot a brute force attack
It’s not uncommon to get an email from a service provider telling you that someone logged into your account from a random location. When this happens, it is possible you have been the victim of a brute force attack. In this case, it’s advisable to change your password immediately.
You might even want to change your password for sensitive accounts on a regular basis, just in case you have become a victim of an undetected or unreported brute force attack.
If you’re a network administrator, it’s important for the security of your website and your users to look out for signs of a brute force attack, especially a successful one. Although a bunch of unsuccessful logins could well be from a forgetful user, chances are the site is under attack. Here are some signs to watch for:
- Multiple failed login attempts from the same IP address. Although, this could be a result of a proxy server being used by a large organization.
- Login attempts with multiple usernames from the same IP address. Again, this could simply be from a large organization.
- Multiple login attempts for a single username coming from different IP addresses. This could also be a single person using a proxy.
- An unusual pattern of failed login attempts, for example, following a sequential alphabetical or numerical pattern.
- An abnormal amount of bandwidth being used after a successful login attempt. This could signal an attack designed to steal resources.
From a user standpoint, it can be very difficult to know if your account has been breached by a brute force attack. If you do receive a notification after your account has been breached, your best course of action is to check your account for any changes not made by you and change your password immediately.
Related: What to do if your account or email has been hacked
How to prevent a brute force attack
Brute force attacks can be easy to detect simply because of the large number of login attempts. You’d think that thwarting an attack would be as simple as blocking the IP address that the login attempts are coming from.
Unfortunately, it’s not that straightforward as hackers can use tools that pass attempts through open proxy servers so that they come from different IP addresses.
Still, depending on whether you are a user or an administrator, you can prevent a successful brute force attack by following our tips. We’ll go into more detail on each one below.
Here’s how to prevent a brute force attack:
- Utilizing or requiring strong passwords
- Allowing a limited number of login attempts
- Employing the use of CAPTCHAs
- Setting time delays between attempts
- Asking security questions
- Enabling or requiring two-factor authentication
- Using multiple login URLs
- Tricking the attack software
Since most measures must be implemented by an administrator, this section will focus on items from that perspective. Users should still take note of areas where they can help to strengthen the system, such as by utilizing strong passwords and taking advantage of any optional security features.
1. Strong passwords
If you’re a network administrator, you can help prevent successful brute force attacks by requiring that users input strong passwords. A complex password is less effective than a long password. Ideally, passwords should be lengthy and random.
From a user perspective, a strong password is imperative. Using a common password or a simple word from a dictionary will make it far easier for a brute force attack tool to land on the right one. Coming up with a solid password can be difficult, but here are a few tips:
- Longer passwords are better as it will take a sequential tool longer to run through the iterations.
- Using a combination of upper and lower case letters, numbers, and special characters will make a password stronger.
- Never using the same password for different accounts will make you less vulnerable to certain types of attack.
Of course, coming up with and remembering strong passwords can be difficult, but there are tools to help you. These include password generators and password strenght testing tools, and password management applications such as LastPass, KeePass, Dashlane, and Sticky Password.
2. Limited number of login attempts
One common defense against a brute force attack is to simply limit the number of login attempts to a logical number, perhaps somewhere between five and 10. If you do this, just remember to provide some sort of recovery method for genuine users to pursue in case they become locked out.
For example, you might offer a recovery option by which their password can be changed through email verification. Or you could provide a support contact number or email to reach in case of a lockout.
You might also consider putting a time limit on the block. Since many brute force attacks will happen in a short space of time, a temporary lockout may be all that’s needed. You could set the lockout time to an hour or two to minimize the negative impact on the overall user experience.
Bear in mind that this is far from a failsafe option and comes with many potential problems. One of the issues with this measure is that some brute force tools not only switch up the password each time but also try a different username for each attempt. If the attempts are for different accounts, a single account won’t be locked.
Restricting the number of attempts for each IP address would make logical sense, but as mentioned above, different IP addresses can be used for each attempt, in which case this measure wouldn’t be effective. An alternative would be to block on a browser or device basis using cookies.
Another issue with this tactic is that lockouts can be used to harvest real usernames in a username guessing attempt where only real usernames deliver a lockout message. Further, a lockout could actually be used strategically to block out users to prevent them accessing accounts.
With all of these potential issues considered, a limited login attempt strategy should only be used in appropriate circumstances.
3. CAPTCHAs
CAPTCHAs (Completely Automated Public Turing tests to tell Computers and Humans Apart) have been around for more than twenty years. They can be used to determine whether or not a login attempt is being made by a human. Some CAPTCHAs simply request the user retype some distorted text, check a box, or answer a simple mathematical question.
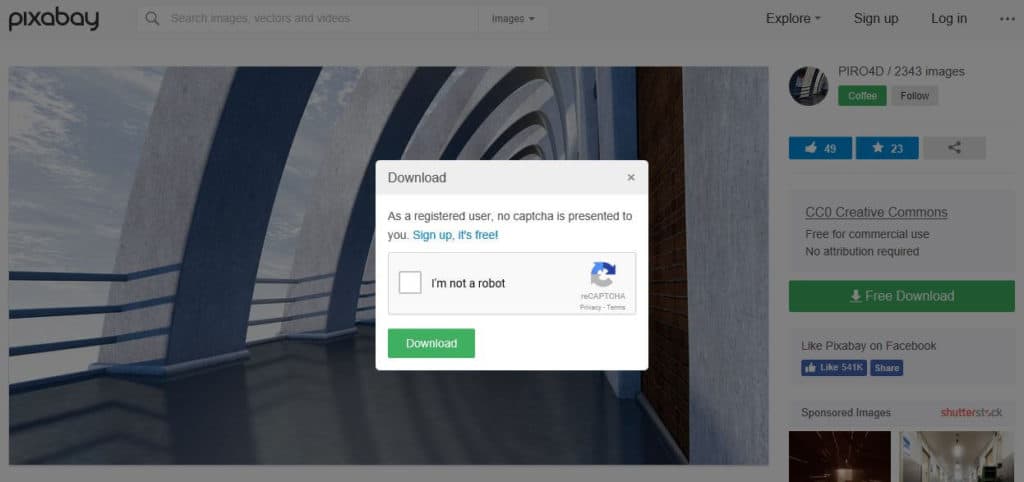
Others are a little more sophisticated and request that users identify objects in images.
Unsurprisingly, the simplicity of CAPTCHAs means that they are not that difficult to bypass. Still, they might at least present a hurdle for would-be attackers. CAPTCHAs can be used in combination with other tactics on this list, such as requiring a CAPTCHA after a certain number of failed login attempts.
4. Time delays
Implementing a time delay of a few seconds between login attempts sounds rudimentary but could actually be very effective. Some brute force attacks are based on a large number of attempts in a short amount of time in the hopes of quickly striking the right combination.
A short delay between attempts could seriously slow down an attack to the point where it’s not worth the effort. On the other hand, the delay might be barely noticeable to the average user.
This tactic won’t work for all attacks as some are designed to be deliberately slow.
5. Security questions
While many users bemoan the use of security questions, their utilization can be even more of a pain for brute force attackers. Even in targeted attacks involving personal information for a specific user, it could be difficult to get past security questions.
To make for a better user experience, you could only request security answers after a specific number of failed login attempts or each time a new device is used for login. Or, if you’ve detected an attack taking place, this might be a good time to request that all users answer a security question when logging in.
6. Two-factor authentication
Depending on the nature of your service, you might not want to deteriorate the user experience by enforcing a two-factor authentication rule. However, it’s nice to be able to provide this feature as an option for more security-conscious users.
You could choose to offer a simple two-step process, for example, credentials followed by an email, or you could let the user decide between different options, including credentials, social media, email, SMS, and more.
Note that there are two different forms of this type of authentication which are often confused or simply bundled together. Two-step verification (2SV) typically involves a verification code or link, often sent through SMS or email. For example, Amazon gives users the option to use 2SV in the form of a one-time password (OTP) for all login attempts.
Two-factor authentication (2FA) uses a different form of verification as the second factor. This could involve something like a keycard or fob, or a biometric method of identification such as a fingerprint or retina scan.
7. Unique login URLs
Because there aren’t really any concrete options for blocking brute force attempts, it’s wise to implement multiple defense strategies. Some of these could simply involve diversionary tactics. One such method is to provide different URLs for users to log in from. In this case, each user would either have a unique login URL or use a URL shared with a set of other users.
This method would be especially helpful in preventing attacks used to harvest usernames as each URL would provide a limited amount of information. This isn’t a first-class method by any means, but it could slow down an attack.
8. Trick the system
Another possible diversionary tactic is to switch things up in order to confuse the attacker (or rather the software being used). For example, some bots are trained to recognize errors, but you could use redirects to different failure pages for simultaneous failed login attempts. This would mean that the attacker would at least need to step things up with more sophisticated software.
Other options include allowing access to an account, but then requesting a password on a new page, or even granting access to an account with very limited capabilities.
Alternatively, you could use a reverse method and embed a failed login error in the code of the webpage. Even with a successful login attempt, a bot could be tricked into delivering this as a failed try. This form of obfuscation is often used to make it more difficult for an automated attack tool to understand whether a brute force attack has failed or succeeded.
This tactic might be enough to throw off the average person who is simply looking for a weak system to penetrate. But these tricks could probably be circumvented by a determined attacker and may require a lot of upfront effort.
The bottom line for protecting against brute force attacks
As you can see, there are many options for helping to prevent a successful attack. Because the nature of a brute force attack will vary on a case-by-case basis, there isn’t really a blanket method for prevention. As such, it might be best to consider using a combination of several strategies to create a solid line of defense.
Related:



