PGP (Pretty Good Privacy) encryption has become a mainstay of internet privacy and security for one main reason: it allows you to send a coded message to someone without having to share the code beforehand. There’s a lot more to it, but this is the fundamental aspect that has made it so useful.
Let’s say you needed to send a sensitive message to a friend without anyone else discovering its contents. One of the best solutions would be to alter it with a secret code that only you and the friend know, so that if anyone intercepts the message, they can’t read the contents.
Systems like this work fine in many different types of encryption, but there is one major flaw: How can you send a coded message to someone if you haven’t already had a chance to share the code with them?
If you haven’t shared the code beforehand and use it to encrypt your message, then your friend will have no way to decipher the coded message when they receive it. If you send the code alongside the coded message, then anyone that intercepts the message can access the contents just as easily as the recipient.
It’s a conundrum that PGP has managed to solve with something called public-key encryption (don’t worry, we’ll cover what this is later), which allows its users to send secure and encrypted messages to people that they’ve never met, or communicated with, before.
What else does PGP encryption do?
PGP’s core function is to enable its users to send secure messages without needing a prior introduction, but that’s not all it does. It also allows recipients to verify whether a message is authentic or if it has been tampered with. It does this by using something called digital signatures, which we will cover later in the article.
On top of this, PGP can be used to encrypt other things besides email. You can use it to encrypt your hard drive, instant messages, files and more. While these are all important features, this article will mainly focus on using PGP encryption for email, PGP’s most widespread use.
Why is PGP important?
You may not be aware, but email isn’t a very secure way to communicate. When your email leaves your account and gets sent across the internet, it transits through networks that are beyond your control. It can be intercepted and tampered with, all without you or the recipient’s knowledge.
If you need to send something valuable or sensitive, normal email just isn’t suitable. Your personal messages can be snatched by hackers who might use it to commit identity fraud, while important government messages can fall into the hands of spies. A person’s stalker could even be reading everything that goes through their inbox.
These dangers are part of why PGP was invented — to bring some semblance of privacy and security to the Wild West that is email communication. It stands for Pretty Good Privacy, which may not inspire a whole lot of confidence for something that people rely on to keep their communications secure.
Despite the name – which was inspired by a radio program’s fictional shop called Ralph’s Pretty Good Grocery – PGP is a form of encryption that does not have any publicly known ways of being broken. This means that as long as it is properly implemented you can be confident in the security, privacy and integrity of your messages and files.
The history of PGP
PGP is an encryption program that was created by Phil Zimmerman back in the internet dark-age of 1991. Zimmerman, who was a staunch anti-nuclear activist, initially created the program so that like-minded individuals could communicate and store files more securely. The first encryption algorithm was called “BassOmatic,” named by Zimmerman after a Saturday Night Live sketch.
Zimmerman released PGP for free via FTP, making it the first form of public-key cryptography with widespread availability. It spread quickly over Usenet, particularly among peace and other political activists. From these roots, its usage grew outwards to those who wanted more privacy and security for their communications.
After PGP encryption spread outside of the US, the United States Customs Service (USCS) started an investigation into Zimmerman. This was because PGP was then classified as high-strength cryptography. At the time, this type of cryptography was deemed a form of munition and required a license to be exported.
Once PGP made its way overseas, the USCS became concerned with its creator for initiating its international distribution. Thankfully for Zimmerman, after several years of investigation and some imaginative legal maneuvering, no charges ended up being laid.
Over the years, new versions of PGP have continually been released to improve its security and its usability. Some of these changes included restructuring the certificate system, implementing new symmetric and asymmetric algorithms and developing a new proxy-based architecture.
Along the road, there were a number of acquisitions which ended up with Symantec Corporation — now itself part of Broadcom — purchasing PGP Corporation and most of its original assets for $300 million (GBP £229.7 million). They now own the trademark to PGP and use it in their products.
See also:
Famous codes and ciphers through history
Encryption Resources: A Big List of Tools and Guides
OpenPGP
The early days of PGP were plagued with patent disagreements based on its use of the RSA encryption algorithm. In order for PGP’s development to continue without these licensing issues, the team behind it set about creating a non-proprietary standard that could be used openly and freely.
In 1997, they approached the Internet Engineering Task Force (IETF) with a proposal to develop the standard and name it OpenPGP. The proposal was accepted and OpenPGP became an Internet Standard. This enabled anyone to implement OpenPGP into their software.
OpenPGP is actively being developed under the RFC 4880 specification. This standard sets out the encryption algorithms, formats, composition and other features that programs must use to be OpenPGP-compliant.
Which programs use OpenPGP?
PGP encryption is used in a number of proprietary programs. Thanks to the development of the OpenPGP standard, it’s also available in a number of free implementations.
The most prominent of these is Gpg4win, which is a free suite of encryption tools for Windows. PGP encryption can be used on Mac OS with a program such as GPG Suite, Android with K-9 Mail and iOS with Canary Mail. More OpenPGP-compliant options can be found on the OpenPGP website.
How does PGP encryption work?
First, let’s cover the key concepts, then we’ll go into an example to give you a more concrete understanding. PGP encryption relies on several major elements that you will need to get your head around in order to understand how it works. The most important ones are symmetric-key cryptography, public-key cryptography, digital signatures and the web of trust.
Symmetric-key cryptography
Symmetric-key cryptography involves using the same key to both encrypt and decrypt data. In PGP, a random, one-off key is generated, which is known as the session key. The session key encrypts the message, which is the bulk of the data that needs to be sent.
This type of encryption is relatively efficient, but it has a problem. How do you share the session key with your recipient? If you send it alongside your email, then anyone who intercepts the message can access the contents just as easily as your recipient. Without the key, your recipient will only see the ciphertext.
Public-key cryptography
PGP solves this problem with public-key cryptography, also known as asymmetric cryptography. In this kind of encryption there are two keys: a public key and a private one.
Each user has one of each. The public key of your potential correspondent can be found by searching through key servers or by asking the person directly. Public keys are used by the sender to encrypt data, but they cannot decrypt it.
Once data has been encrypted with the recipient’s public key, it can only be decrypted by their private key. This is why public keys are freely handed out, but private keys need to be guarded carefully. If your private key is compromised by an attacker, it enables them to access all of your PGP encrypted emails.
In PGP, public-key encryption isn’t used to encrypt the message, just the one-off session key that was generated to encrypt it. Why? Because public-key encryption is simply too inefficient. It would take too long and use a larger amount of computational resources.
Since the body of the message usually contains the bulk of the data, PGP uses the more economical symmetric-key encryption for this. It reserves the lumbering public-key encryption for the session key, making the whole process more efficient.
In this way, the message gets encrypted through more practical means, while public-key encryption is used to securely deliver the session key to your recipient. Since only their private key can decrypt the session key, and the session key is needed to decrypt the message, the contents are secure from attackers.
Digital signatures
Our written signatures are frequently used to verify that we are who we say we are. They are far from foolproof, but they are still a useful way of preventing fraud. Digital signatures are similar, using public-key cryptography to authenticate that the data comes from the source it claims to and that it has not been tampered with.
The process makes digital signatures essentially impossible to forge unless the private key has been compromised. Digital signatures can be used alongside PGP’s message encryption or separately. It all depends on what you are sending and why.
If the message is sensitive and shouldn’t be read by anyone but the recipient, you need to use encryption. If the message must be delivered intact and without alteration, then a digital signature will need to be used. If both are important, you should use them together.
Digital signatures work by using an algorithm to combine the sender’s private key with the data that they are authenticating. The plaintext of your message is fed through a hash function, which is an algorithm that transforms inputs into a fixed-size block of data, called a message digest.
The message digest is then encrypted with the sender’s private key. This encrypted message digest is what is known as the digital signature. In PGP encryption, the digital signature is sent alongside the message body (which can either be encrypted or in plaintext).
Verifying digital signatures
When someone receives a digitally signed email, they can check its authenticity and integrity by using the public key of the sender. The whole process is generally done by the recipient’s PGP software, but we will lay out the rough steps to give you an idea of what’s actually happening.
First, a hash function is used on the message that was received. This gives the message digest of the email in its current form.
The next step is to calculate the original message digest from the digital signature that was sent. The sender’s public key is to decrypt the digital signature. This gives the message digest exactly as it was when it was signed by the sender.
To determine whether the message is authentic and hasn’t been tampered with, all the recipient’s program has to do is compare the message digest from the email they received against the message digest that they derived from the digital signature.
If the message had been altered by even one character or punctuation mark, then the message digests will be completely different. If the message digests don’t line up, then the recipient will know that there is a problem with the message.
If the two message digests are not identical, there are three likely culprits:
- The public key used to decrypt the digital signature was not linked to the private key that was used to encrypt it. This means that the sender may not be who they say they are.
- The digital signature may be fake.
- The message has been changed since it was signed.
If you receive a digitally signed message and the digests don’t line up, you should be skeptical. It may be an innocent mistake because the wrong public key has accidentally been used, but it could also be a fraudulent message or one that has been tampered with.
The web of trust
How do you know that a public key actually belongs to the person who says it does? Couldn’t someone just post up their own public key and claim that they’re the Pope in an attempt to access all of his incoming PGP-encrypted emails (assuming he’s tech savvy enough to use PGP)?
Thankfully, this was all thought of ahead of time and solutions were put in place. Otherwise, something so simple would completely undermine the whole system. To prevent this kind of activity, the web of trust was developed.
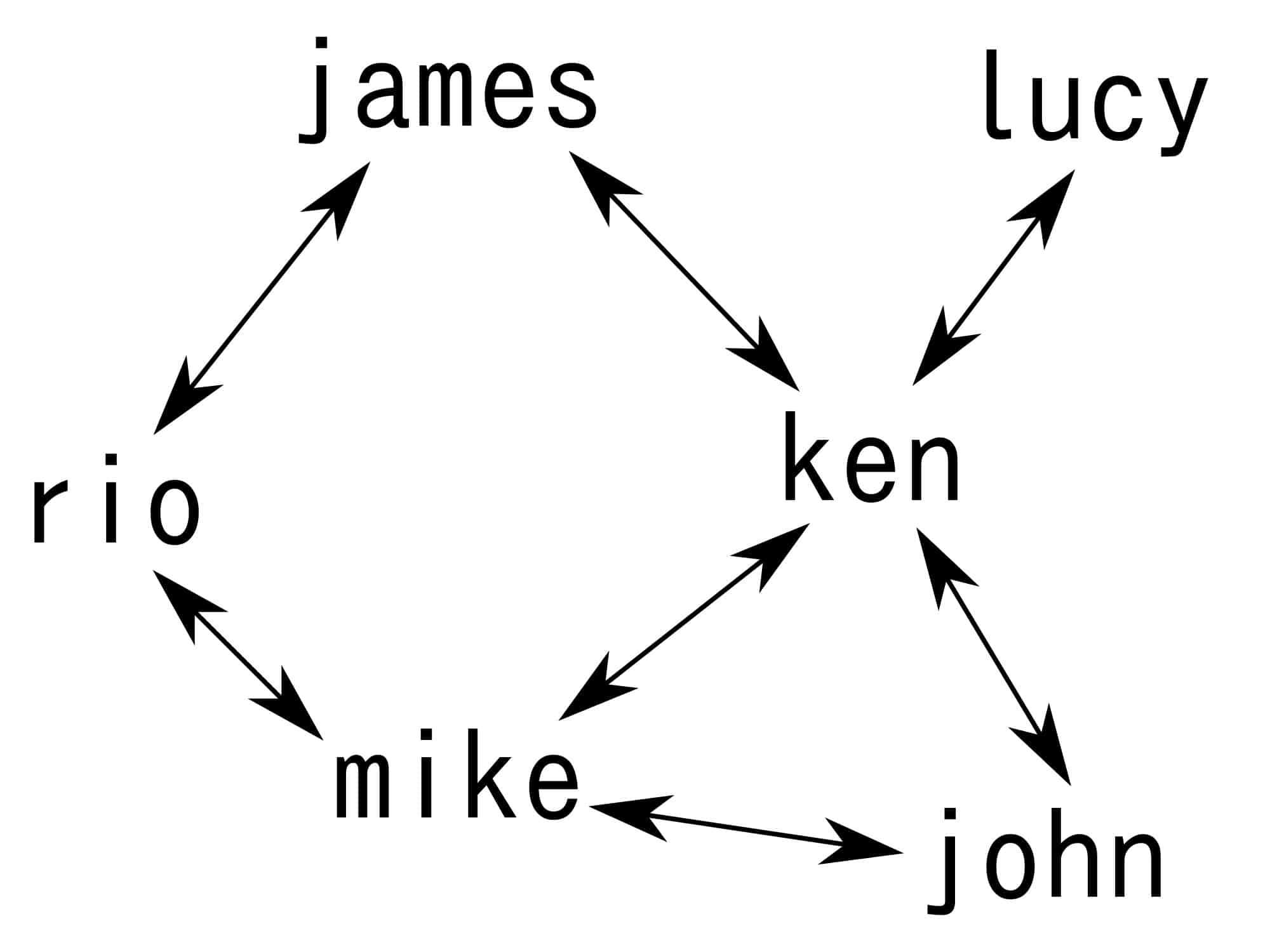
The web of trust grew as a way of vetting that each PGP public key and user ID are really connected to the person or organization that they are said to represent. The web of a trust connects the real life entity with the public key by using a third party to sign the user’s PGP digital certificate. The best part? It does it all without a central authority that can collapse or be corrupted.
A digital certificate contains the user’s identifying information, their public key and one or more digital signatures. If you know a PGP user personally, you can confirm that their public key is linked to their actual identity. You can put your trust in them and digitally sign their certificate, which shows that at least one person vouches for their identity. They can also do the same for you.
If both of you meet one new PGP user each and digitally sign their certificates to verify their identities, you start to build a small network, where the four of you can trust the links between the public keys and identities, based on the trust each person has in others that they are linked to.
Over time, this builds an interconnected web of trust, with lots of people vouching for each other with digital signatures that verify their ownership of a public key.
Sometimes it can be difficult for new users to find someone to sign their certificates and verify the relationship between themselves and their public key. It can be particularly challenging if they don’t know other PGP users in real life.
This has been partially solved by key-signing parties, which are real-life meetups where users can assess whether keys belong to the person saying it does. If everything checks out with their identification, they digitally sign the person’s certificate when they get home.
There are different levels of trust, including full and partial. Those that have many digital signatures on their certificates that represent full trust are seen as much more dependable than those with only a couple of partial-trust signatures.
The web of trust allows users to assess for themselves whether they trust the digital certificate of a potential correspondent. If the message they want to send is extremely sensitive, they might decide that the risk is too great to send it to someone who only has partial trust.
Certificate authorities
PGP digital certificates aren’t the only way that identities can be linked to their public keys. X.509 certificates can also be used. This is a common certificate standard that is also used for other purposes. The main difference between PGP certificates and X.509 certificates is that PGP certificates can be signed by anyone, while an X.509 certificate must be signed by what is known as a certificate authority.
PGP certificates can be signed by certificate authorities as well, but X.509 certificates can only be signed by certificate authorities or their representatives. X.509 certificates also carry a range of the owner’s identifying information alongside the public key, but they also have a start and an expiry date.
In contrast to PGP certificates, which a user can make themselves, X.509 certificates are only available by applying to a certificate authority. These certificates also only have a single digital signature from the issuer, as opposed to the many signatures that a PGP certificate can have from other users.
Encrypting Attachments
PGP can also be used to encrypt your attachments. There are a couple of ways to do this, but it will depend on your implementation. In general, the best way method is with PGP/MIME, which will encrypt the attachments and message body together. This prevents the leaking of metadata that occurs if each segment is encrypted separately.
PGP encryption in action
Let’s put all of this together in an example to show how these elements work in relation to each other. To make things more interesting, let’s say you’re a whistleblower from a totalitarian country who has uncovered an extreme case of corruption.
You want to get the message out to journalists, but you are terrified for your own safety. What if the government finds out that you were the one who leaked the information and they send people after you?
You eventually decide that releasing the information to the public is the right thing to do, but you want to do it in a way that protects you as much as possible. You search online and find a journalist who is renowned for this kind of work and always protects their sources.
You don’t want to just call them or email them normally, it’s too risky. You’ve heard about PGP before and decide to try using it to protect your message. You download a program like Gpg4win and configure it with an OpenPGP-compliant email.
Once everything is in order, you seek out the journalist’s public key. You find it on their website or by searching a key-server. Their public key has numerous full-trust signatures on the digital certificate, so you know it’s legitimate.
You import the journalist’s public key, then use your OpenPGP-compliant email to begin. You type out the message:
Dear Susan Peterson,
I have some information about a huge corruption scandal in The United States of Mozambabwe. Let me know if you are interested and I will send you more details.
Adding your digital signature
If you are worried about the email being tampered with, you can add your digital signature. A hash function turns the plaintext into a message digest, which is encrypted with your private key. The digital signature will be sent to the journalist alongside the message.
Encrypting the message
When this is finished, PGP compresses the plaintext. Not only does this make the process more efficient, but it also helps to make it more resistant to cryptanalysis.
Once the file is compressed, PGP creates the one-off session key. This session key is used to efficiently encrypt the plaintext with symmetric-key cryptography, turning the body of the message into ciphertext. The session key is then encrypted using the journalist’s public key. This public-key encryption is more resource-hungry, but it allows you to securely send the session key to the journalist.
The ciphertext, the encrypted session-key and the digital signature are then sent to the journalist. When the journalist receives the message, it will look something like this:
wcBMA97wCTWE/j6yAQf9EIv17btMUCL8BwIn4bAf/gE3GVdPmpfIQLSpOa1yN9d8
KI9K8xs9MAEF7fgl94/nXg0h9e1KcTjgi81ULMRMkDjIoYd33TQTMqXnRQu4b5mU
hOKn+BGJ2LNeWI/tLLCXHfN27x3RkDHZR7q8UupnukVlArCt+1ck+Fph0xE9G3UG
JF5KmQWm9n+1fWMzynj9vy4CBERtOgc5ktVNJOek4Mr+14vz9NykbBwgJthpDaFK
HtRgVimokTCxVckIc3aLK9dXPUBCh9D3GpUw6ruEn17/PWvveAnLDmbsfpGxizlF
uC8OWRgaKSdgZhZBqyFS0Wb6B39gWgoK9xh4/Ma90dLADAEbDAN6eRqvhYhADWW+
fLkFU3q8If0CYZY1tIeXLa46IxqiQaBPQfOQ7MfG5gAWAV5AHdd6ehWMKfy1Yoye
K3ikc18BZMRCLMmEilI+pDrIpcii5LJSTxpzjkX4eGaq1/gyJIEbpkXRLr5OSKmN
m/pS1ylm5XvapQCpDo7DAAFZ13QpLmGf54gMZOTFYGZzg7EMcShL5nZ4y16GJ2DK
qlpLCcVluNzJDEBnlYaVEGzrHJNgpNldNDjYn2NN780iJuronSwzyMP7NPTm0A==
=iO3pDecrypting the message
The journalist uses their private key to decrypt the session key. The session key then decrypts the body of the message, returning it back to its original form:
Dear Susan Peterson,
I have some information about a huge corruption scandal in The United States of Mozambabwe. Let me know if you are interested and I will send you more details.
Verifying the digital signature
If the journalist is skeptical about the integrity of the message or believes that it may not have been sent by you, they can verify the digital signature. They run the message they received through a hash function, which gives them the message digest of the email they received.
The journalist then uses your public key and your digital signature to give them the message digest as it was when you sent the message. If the two message digests are identical, then they know that the message is authentic. From this point, you and the journalist will be able to communicate backwards and forwards with PGP to discuss the details of the corruption scandal.
How secure is PGP encryption?
As far as its security goes, current versions of PGP are essentially airtight, as long as they are used correctly. There are some theoretical vulnerabilities to older versions, but current versions aren’t publicly known to have any means of being broken with contemporary technology and the latest cryptanalysis techniques. The likelihood of anyone having a secret means of breaking PGP is also negligible, so it’s pretty safe to use PGP with confidence, as long as you use it properly.
As PGP has been developed, more encryption algorithms have been added to bolster its security. Whenever any slight vulnerabilities have been discovered, they have been quickly patched by the developers. The biggest worry is not in PGP encryption itself being broken, as it would be impractically difficult for any criminal or nation state to do so.
Instead, it’s far more likely for an attacker to use other means to uncover your communications. This could include using a keylogger to figure out your private key, or ransacking your house to see if your private key has been written down somewhere.
Despite this, there have been some vulnerabilities in various implementations of OpenPGP. At the start of 2018, a weakness was found that could be used to show the plaintext of emails that had been encrypted.
Dubbed EFAIL, it involves attackers first intercepting a target’s encrypted email and altering it to cause the final recipient’s email client to send the message to the attacker once it has been decrypted.
The attacker doesn’t actually decrypt the email themselves and this technique doesn’t involve breaking PGP encryption. Despite this, PGP users need to be aware and take appropriate measures to mitigate the risks.
Anyone using PGP should change the settings in their email client to prevent the automatic loading of external images and other content. They should also turn off JavaScript and HTML when viewing encrypted emails. With these measures in place, PGP encryption is still safe to use.
What are the limitations of PGP encryption?
While PGP encryption is an important tool in the security arsenal, as with every other defense, it’s far from perfect.
Usability
One of its major downsides is that it’s not exactly user-friendly, especially compared with most of the apps that we spend our day-to-day lives on.
This presents challenges to those who want to protect their emails, but lack a high-degree of technical literacy. It may be one of those things that they just have to learn in order to keep their communications safe. Otherwise, encrypted messaging apps like Signal might be better suited to their needs.
There have also been many different versions of PGP over the years, each with new algorithms and features. Because of this, older versions of PGP won’t be able to open messages that have been encrypted by newer systems. Even with the correct key, it still won’t work, because they use different algorithms.
This means that it is important to make sure that both the sender and the recipient are aware of which version and settings are being used, so that they can settle on a system that mutually works for them.
PGP is not anonymous by default
PGP users need to be aware that it doesn’t encrypt every aspect of their emails. It encrypts the body text, but anyone who intercepts PGP emails will still be able to see the subject line and message details, as well as information about both the sender and the receiver.
While the message itself may be private, the interaction is not anonymous. Users need to consider this when evaluating whether it is the right tool for the job. To start with, they should avoid putting anything overly specific in the subject line.
Considering our example from above, the whistleblower would still need to consider the risks associated with PGP. If the corruption scandal caused huge government outrage, it’s not unrealistic to imagine government agents hacking into the emails of the journalist.
If they were to find only one interaction with a citizen of the United States of Mozambabwe, it wouldn’t take any Sherlock-style skills for them to deduct that this person is probably the whistleblower. The agents don’t need to be able to access the message contents to have a high degree of confidence, or at least enough to bring that person in for interrogation.
PGP encryption is an integral part of high-security communication
The nuts and bolts behind PGP encryption are a little complicated, but it’s an important aspect of secure email. Those who use it need to understand how it works, at least in a broad sense. Otherwise they may make incorrect presumptions or use it improperly, endangering their message contents and perhaps even their lives.
As a quick recap, PGP encryption leverages a range of techniques to provide secure and private email communications. These include compression, public-key encryption, symmetric encryption, digital signatures, and the web of trust.
Together, these allow its users to send encrypted messages in an efficient manner. It also let’s them check whether a message is authentic and has not been altered. The OpenPGP standard was formed so that everyone could use it for free, helping to make it the most widespread form of email encryption. While PGP encryption isn’t perfect, as long as you are aware of its limitations, it’s one of the safer ways that you can communicate online.
Now, you may be wondering how to use PGP? We’ve got you covered in our tutorial on how to encrypt email.
Backlit keyboard by Colin licensed under CC0