Imagine your computer’s operating system as a complex ecosystem, teeming with programs and applications that function like various interconnected departments within a large organization. Sandboxing is a cybersecurity technique that creates isolated environments within this system, separating these programs and restricting their ability to interact directly with each other. This controlled environment minimizes disruptions and safeguards the overall stability of the system.
Think of traditional sandboxes at the playground. Sand seems to have a mind of its own, clinging to clothes and shoes and spreading everywhere. Programs on your computer can be just as unpredictable, interacting with various parts of your system storage, memory, and even the central processing unit. This interaction can lead to conflicts between programs, hindering overall system performance or creating vulnerabilities that malicious software can exploit, similar to a security breach within a company.
While resource sharing allows your computer to multitask efficiently, it also introduces potential risks. A poorly coded program can malfunction on its own or cause other programs to crash, much like a software bug disrupting critical operations within an organization. On the other hand, malicious software actively seeks to exploit these connections to cause harm, acting like a cybercriminal attempting to infiltrate a secure network.
Sandboxing helps mitigate the consequences of both accidental errors and intentional attacks. It acts like a digital security measure, confining each program’s operations within its designated zone and preventing it from reaching unauthorized areas of your system, like a robust access control system protecting sensitive data within an organization.
What is Sandboxing?
In technical terms, sandboxing is a security mechanism isolating a program or app, limiting access to your computer’s resources and sensitive data. It operates like a virtual container, where the program can run but with controlled permissions and limitations. Here’s the key idea:
- Isolation: The sandboxed program is kept separate from your core operating system, files, and other critical software.
- Restricted Access: The program can only interact with what it needs to function, preventing it from making unauthorized changes or accessing confidential information.
Browser Sandboxing: The Frontline of Web Security
Web browsers are your gateway to the vast online world – but they’re also prime targets for cyber attacks. That’s why browser sandboxing is so crucial. Here’s the state of sandboxing in major browsers:
- Chrome & Chromium-Based Leaders: Google Chrome pioneered browser sandboxing. Chromium, its open-source base, means browsers like Opera and Brave inherit this strong security feature.
- Microsoft Edge: Built-In Protection: Edge, Microsoft’s successor to Internet Explorer, automatically sandboxes website processes for enhanced security.
- Firefox: Evolving Security: Mozilla Firefox offers selective sandboxing. While not as comprehensive as full-browser sandboxing, it still adds a valuable layer of protection.
- Apple Safari: Process Isolation: Safari runs websites in separate processes, a form of sandboxing that limits the impact of a single compromised site on the entire browser.
- Legacy & Obscure Browsers: Caution Required: Sandboxing isn’t universal. Less common browsers may lack it altogether. For the highest security, stick with mainstream browsers that actively prioritize sandboxing.
Why Browser Sandboxing Matters:
- Damage Control: Sandboxing prevents malicious code on a single website from hijacking your entire browser or computer by isolating browser processes.
- Everyday Protection: Sandboxing works silently in the background, protecting you from known and emerging online threats.
If You Want Extra Security: While browser sandboxing is powerful, dedicated third-party sandboxing solutions (covered in the next section) offer advanced control and customization for high-risk scenarios.
Manual sandboxing
While browsers are a very important weakness in any operating system, by no means are they the only weakness. Any application has the potential to be malicious and therefore the security posture of any computer can be strengthened by the use of sandboxing. Manual sandboxing is the process of purposely configuring your system to sandbox an application that might otherwise have full access to your system.
Virtual machines
Desktop virtualization has come a long way in recent years and it is now fairly easy to install and use virtual machines. A virtual machine is as it sounds: a “machine” that is not real. It is really just a piece of software.
The most common use of a virtual machine is to install a copy of your operating system into it and run that virtual machine on your desktop as if it was another physical machine. This type of separation provides a great deal of security because programs can only access resources inside the virtual machine.
If a piece of malware were to take hold and infect your system, it would only be able to infect the virtual machine, which limits the amount of damage it can do. It’s even possible to run alternative operating systems within a virtual machine such as running a Linux distribution in a virtual machine on a Windows PC.
There are many virtualization applications, each aimed at a specific type of use case. The most popular and mature desktop virtualization applications that normal users can typically handle are VirtualBox, VMware, and Parallels.
Background: A virtualization consists of two main parts. The term host refers to the actual physical computer that runs the virtualization software. The term guest refers to the operating system running within the virtualization application.
VirtualBox
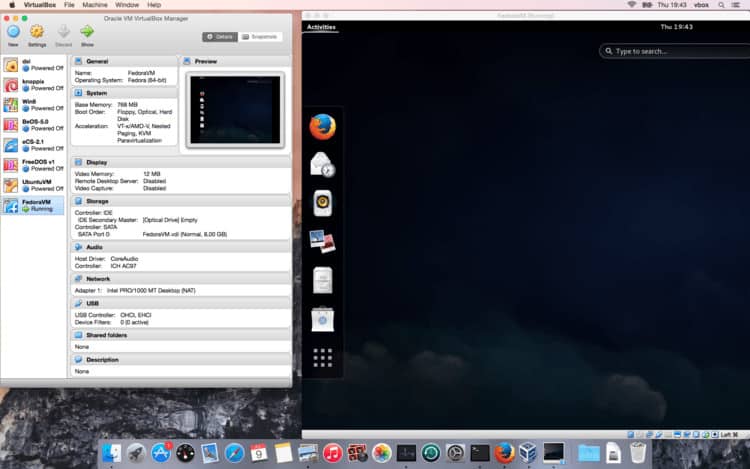
VirtualBox is owned by Oracle and has clients for every major operating system. After installing VirtualBox, you can create a virtual machine by using the New button. You’ll need to provide the operating system installation media because VirtualBox does not come with that. Linux distributions are easily found on the internet. A good list is the website distrowatch and for proprietary operating systems like Windows you will need to have your installation CD handy.
VMware
VMware Fusion 13 Pro provides local desktop virtualization, but at a cost of $199. It allows users to run multiple operating systems from a host. Fusion Pro is designed for Mac-users to run Windows and Linux applications. Workstation 17 Pro also costs $199 and is design for those with a Windows or Linux PC. It supports a range of guest operating systems including Unix, Linux, BSD, and Windows.
Parallels
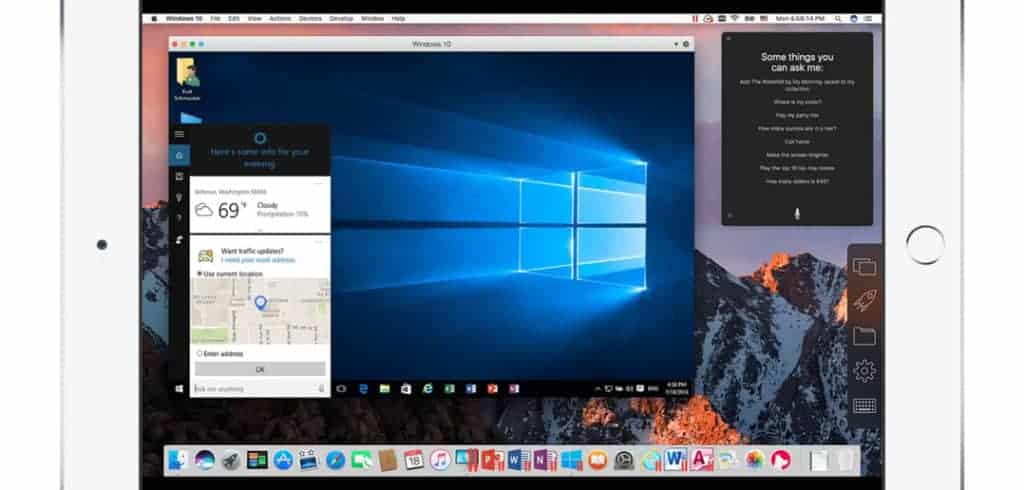
Parallels is very similar to VirtualBox with the notable exception that it only runs on macOS and is specifically built to run Windows in the virtual machine. If you’re looking for that combination — running Windows on your macOS desktop — then Parallels may be the best solution for you. Parallels is not free. However, there is a 30-day free trial.
ToolWiz Time Freeze
From a simplicity standpoint, ToolWiz Time Freeze is a go-to option for those who don’t want to fiddle around with settings.
This free sandboxing app works by creating a virtual environment of your entire operating system. Instead of sandboxing individual programs, it effectively sandboxes your entire Windows operating system by “freezing” it in place, then running everything on the virtual system. Time Freeze does all of this rather seamlessly.
Once you do a system reset, any changes made while Time Freeze was active will automatically erase. Because your operating system is frozen to any changes, it remains intact. The downside to this is that you’ll need to remember when you have Time Freeze active if you make any changes to your system that you want to keep. Time Freeze allows you to keep select files and folders “unfrozen” as it were, to ensure anything you want to keep remains there after you reset your system.
Qubes OS
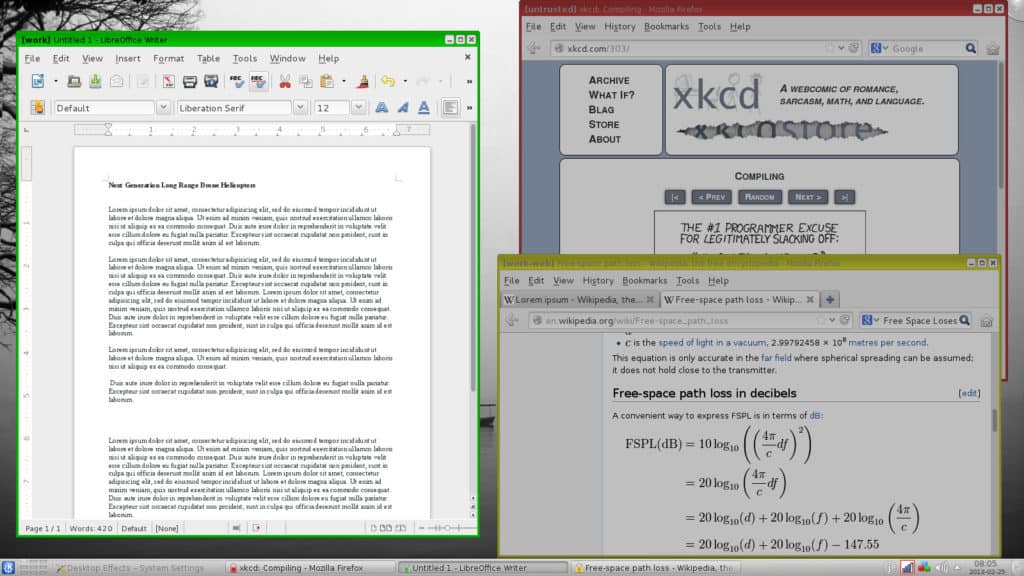
QubesOS (pronounces “Cubes”) deserves a special mention for virtualization. Qubes uses the Xen hypervisor instead of VirtualBox. It launches several guest operating systems and each one is separate from the other. This allows the sandboxing of individual applications, each within its own virtual machine, rather than just sandboxing the entire guest operating system.
QubesOS’ distinctive difference is that Xen is its own operating system; no “host” operating system runs underneath it. I’ve written more about Qubes and other anonymity-focused Linux distributions here.
Sandboxie
As of June 2020, Sandboxie is no longer being supported by its creator. You can still download/install versions of the program, but we recommend you do so with caution. Unsupported apps are particularly vulnerable to attack. Because of the popularity of the program, Sophos released the source code for the app onto Github.
Sandboxie’s motto is Trust No Program. It runs solely on Windows and claims to separate running programs from the underlying operating system. The Sandboxie control panel is used to nominate specific programs to run in a sandbox. The most common programs that present the largest threats, such as browsers and email programs, are listed as configuration options by default, and other applications can be added as needed.
The data inside Sandboxie is destroyed when a sandbox is closed, but it is possible to configure Sandboxie to leave important data unaltered. Folders containing emails and web browser bookmarks are examples of data that can survive a sandbox deletion.
SHADE Sandbox
SHADE Sandbox is designed for home users and has a straightforward drag and drop interface for virtualizing applications. For example, users can place their browser in the sandbox and protect their machine from anything harmful brought in from the internet. A one-year license for Windows costs $20.
Types of issues non-sandboxed programs can cause
Programs that don’t run in a sandbox can wreak havoc on your system. Here are a few problems they can cause.
Programs crashing into each other
In the early days of computing, the CPU handed out resources on a first-come-first-served basis. This worked well when our computers were not doing much, but these days much more complex methods of resource allocation are used.
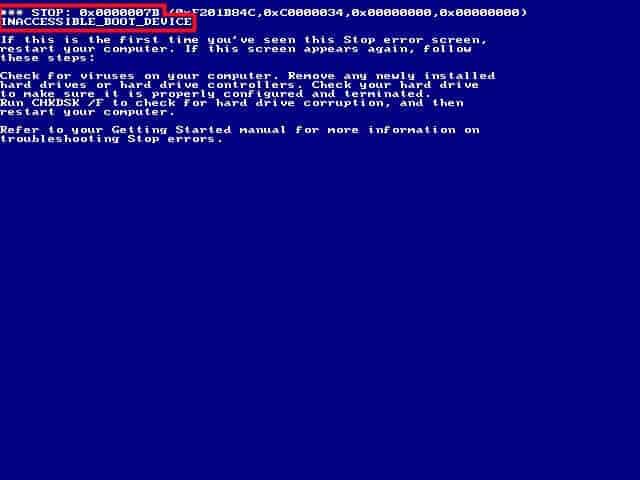
CPUs fiercely defend the boundaries of the resources they’ve allocated and, if a program attempts to access a resource that has not been specifically designated to it, the program or other programs can crash.
Running a program in a sandbox allows the system to pre-allocate resources such as memory and disk space in advance of the program requesting anything. This ensures that those resources are ready for the program whenever it needs it, and also ensures that no other programs can use those resources.
Programs with different dependencies
Every program has numerous versions of itself. Very few programs are perfect in every way upon their initial launch, which is why we’re constantly subjected to the never-ending upgrade cycle.
Our devices are forever telling us that updates need to be applied or new versions of our programs are available. It’s important to allow these updates to take place as soon as possible because many of these updates are related to security or performance issues. Putting off upgrades usually renders your device less secure and running in a state that is less than ideal.
Underneath the main applications that we use and interact with every day are a set of helper programs. These programs exist to help the main application run properly. We humans are seldom aware of these programs, but the main program could not function without them. These helper programs are called dependencies in developer parlance. Just like any other program, these dependencies constantly update and change, which is where things can get tricky.
If a main program makes use of a particular function that the dependency supplies, but the dependency is upgraded and suddenly does not have that function any more, then the main application will collapse. The main application doesn’t get the expected result from that dependency. In many cases, the dependency error is so unexpected that the main application will just crash unceremoniously. The main application developer probably isn’t warned in advance about changes to the dependency, so it can be difficult to account for such a situation and handle it gracefully.
Most programmers do their best to ensure backward compatibility, which means that even if a newer version of their application doesn’t have a function it had in the past, it will still handle requests for that function gracefully so that other applications depending on it will not crash.
However, some very notable exceptions such as Java and Python are known for being very difficult to work with during an upgrade. In the Linux world, the well-known phrase “dependency hell” refers to the problems inherent with big system updates. In some cases, dependency programs have their own dependencies, and it’s not unheard of to end up in an upgrade situation where it’s not possible to satisfy all the dependencies.
For example, if my Puppy Vet Tracker program needs version 2.0 of some dependent program, but my Daily Star Wars Quote program needs version 1.0 of the same dependent program, then it’s not possible to satisfy that requirement for both programs.
Developers frequently run into this type of issue, and sandboxing is one way to address it. Creating a sandbox and installing my Puppy Vet Tracker into it would allow the dependent program to be upgraded to version 2.0. The main computer system would remain with version 1 of the dependent program, and therefore I can still get my daily Star Wars quote. Win-win.
Malicious programs
Consider a situation in which an application shares your computer with all the other running programs. Some of the programs running on your computer may contain sensitive information. Perhaps you have legal documents, budget spreadsheets, or a password manager open, and those applications are storing some data in memory.
Malicious programs exist that probe around the areas of the computer assigned to other programs to see what they can find. In recent years, resource allocation has become better so it is harder for a program to access data that is not in areas specifically assigned to it, but hacking techniques such as trying to read beyond the memory assigned to the program can work.
The trick to successful exfiltration of data (the removal of data from your system) has always relied on fooling the computer user into installing malware. This is usually done with social engineering or phishing tactics and can result in wholesale compromise of a system where every file can be stolen.
Sandboxing programs can provide a very strong defense against malicious programs. When a program is sandboxed properly, it can only access the memory and disk space assigned to it. Therefore, opening sensitive documents in a sandbox will usually prevent the malicious program’s ability to access them because the document isn’t in the same memory space as the malicious program.
Having said that, there is a very concerted effort by hackers to penetrate in, and out, of sandboxes. This is called escaping the virtual environment and is considered to be such a serious type of attack that Microsoft recently paid a $105,000 bounty to a white-hat hacking team that demonstrated it was possible using the Edge Browser.



My head is pulsating