Secure Shell Origins
SSH (Secure Shell) is a widely used technology for securing communication between systems over untrusted networks. It enables encrypted connections that protect data in transit, making it a fundamental tool for maintaining confidentiality and integrity when accessing remote resources.
SSH can be understood as both a protocol and an application. As a protocol, it defines the rules for establishing secure, encrypted communication between devices. As an application, it provides the software that allows users to connect to and manage remote systems, commonly for tasks such as server administration and secure file transfers. This dual role makes SSH a flexible and widely adopted tool across different environments.
This guide introduces the fundamentals of SSH, including its key features, common use cases, and how it can be used to strengthen network security. Whether you’re new to networking or have experience in IT, understanding SSH is essential for maintaining secure communication channels.
Here is our list of the best SSH tools:
- ZOC EDITOR’S CHOICE This small utility for macOS and Windows provides the option to store connection settings and open multiple sessions that you can switch between in a tabbed interface. The tool includes a secure file trader service as well.
- JuiceSSH Runs on Android, great for accessing remote sessions while on the move.
- Termius Free SSH client for iOS with E2E encryption for secure remote sessions.
- SecPanel Free lightweight client for Linux Gnome environments, great for file transfers.
- SolarWinds Solar-PuTTY Terminal emulator with SSH, allows for tabbed multiple instances.
Secure Shell Origins
SSH was originally developed for Unix systems as a secure replacement for older remote access protocols such as Telnet. In Unix environments, a shell acts as a command-line interface that interprets and executes user commands. Early examples include the Bourne shell (“sh”), followed by others like the Korn shell (ksh), Almquist shell (ash), and Debian Almquist shell (dash).
These naming conventions influenced the term “Secure Shell,” reflecting its role as a protected version of traditional shell access. SSH was designed to address the security weaknesses of earlier protocols by introducing encryption and stronger authentication, making it an essential tool for system administrators and network professionals.
Today, SSH is used for a wide range of tasks, including secure remote access, server administration, file transfers, and protected communication between networked devices.
SSH Development
Secure Shell creates a command line environment with those commands executed on a remote computer, rather than on the computer that you are sitting at. This is a very similar operating procedure to FTP, the File Transfer Protocol.
As the SSH commands are executed on a remote computer, the user has to log into that remote device in order to fully use the Secure Shell. SSH was designed as a secure replacement of rsh and rlogin, which were standard Unix systems for remote access that had no security measures. Encryption of the connection was an integral part of SSH from its inception.
The original developer of SSH, Tatu Ylönen, set up a company, called SSH Communications Security in 1995. The standard was originally distributed as freeware, but the company gradually moved over to a commercial model and charged for a software implementation of the protocol. However, the framework for the protocol was already in circulation and so the developers of OpenBSD (a flavor of Unix) went back to a free version of SSH and created their own fork of it. At the same time, the Internet Engineering Task Force commissioned a protocol to be developed that codified and then adapted the original definition of SSH.
Thanks to the two parallel efforts to create free versions of SSH, there are now three types of the system. The original version is known as SSH1. The IETF protocol is referred to as SSH2. Anyone can use the IETF protocol, which is available for free, as a template to develop their own implementation of SSH. SSH1 and SSH2 are also sometimes written as SSH-1 and SSH-2.
The version of SSH that was created by the OpenBSD developers is known as OpenSSH. This is the basis for many SSH GUI programs that run in Windows-like environments. OpenSSH is now built into Windows as of Windows 10 version 1709. SSH is also now built into the operating systems of all Linux flavors, Mac OS, FreeBSD, NetBSD, OpenBSD, Solaris, and OpenVMS Unix.
SSH Communications Security now offers a paid-for SSH client, called SSH Tectia and hasn’t allowed access to its code since 1996. The SSH1 system, which is still in circulation dates back to 1995 and it hasn’t evolved since then. If you are offered a choice of SSH versions, you should opt for SSH2 or OpenSSH.
Uses for SSH
The primary use for SSH is as a safe way to connect to a remote server. This capability of SSH is actually becoming more important in the world of IT in recent years thanks to the rapid use of Cloud server space rental.
SSH2 and OpenSSH include secure file transfer utilities. The transfer of files across the internet has become a major purpose of the use of long-distance connections and so the lack of any security procedures in the widely-implemented FTP file transfer protocol makes the SSH file transfer system really important. The two types of secure transfer systems that you can use with SSH are SFTP, which stands for “SSH File Transfer Protocol” and SCP, which stands for “Secure Copy.”
Both SFTP and SCP will serve you well when you need to protect your server from attack and prevent snoopers from reading the contents of your files while they are in transit. Both of these utilities require user authentication and both encrypt data in transit. The security services are provided by SSH.
If you manage a WAN and need to log into remote servers and transfer files to and from them, then you will use SSH, SFTP, and SCP regularly. The difference between SCP and SFTP is that the first is just a copy command that can copy a file to or from a remote location. With SFTP, you also get a command language that enabled you to rename, create, move, or delete files on the remote server and also create and delete directories. You don’t get those abilities with SCP. However, as the basic SSH command language includes all of these functions, you could quite easily work well with a combination of SSH and SCP available to you.
VPNs are popular for getting past regional restrictions on websites. Regional restrictions are particularly prevalent on video streaming websites and they prevent people from getting access from overseas. Unfortunately, many governments oppose the use of VPNs and try to block them. You can protect your VPN traffic with SSH. In short, SSH offers a good way to protect any type of transaction that you want to perform over the internet.
How to Get SSH
SSH is probably built into your operating system. To check, open a terminal window and type ssh at the prompt. This is not the right way to use the utility because you are supposed to add parameters to the command. However, if SSH is available to you, the result of the command will be a response showing the structure of the command.
If you don’t have SSH on your Unix, Mac OS, or Linux system, you could install OpenSSH, which is now available for just about any operating system. If you want to install it on Windows, you also need to install Cygwin to emulate Unix on your computer. This includes SCP and SFTP. However, the interface is not so user-friendly and there are much better SSH servers available today.
The best SSH tools
There are a lot of very good SSH interfaces available on the market right now. These apps are a lot easier to use than the command line utility. So, if you don’t want to have to go to the command line to use SSH, or you just don’t have SSH in your operating system, you will find that one of these easy-to-use SSH systems will be the answer.
Our methodology for selecting SSH tools
We reviewed the market for Secure Shell (SSH) systems and analyzed the options based on the following criteria:
- A lightweight program with a small footprint
- Easy to set up connections
- Option to store connection settings for rapid reconnection
- A secure terminal emulator
- Nice to have a secure file transfer system included
- A free trial, a demo for a no-cost assessment opportunity or a free tool
- An SSH system that costs nothing or a tool that provides value for money
Here is our list of the best SSH tools:
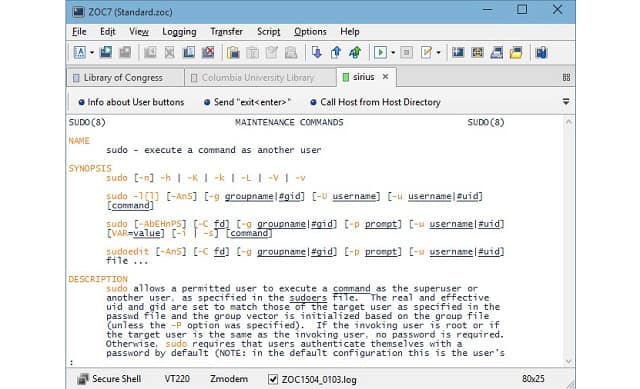
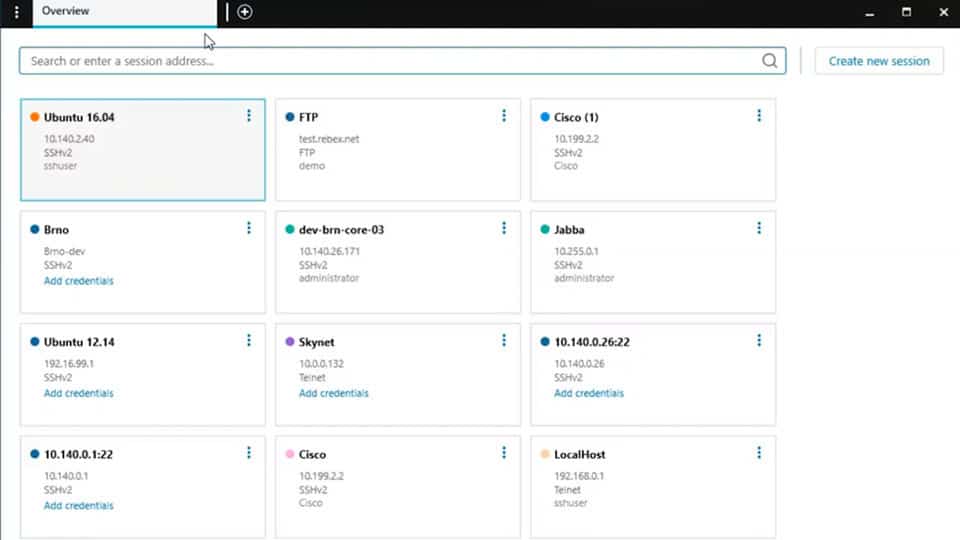
1. ZOC
ZOC is an option for you if you want to access remote computers securely with SSH from a Mac. The tool will run on Windows as well as on Mac OS. The tabbed interface enables you to access several open sessions and the Options screen gives you options over which terminal emulation standard you can use. ZOC is able to implement the TN3270, TN5250, VT220, Xterm, VT220, Wyse, and QNX terminal emulation standards.
Key Features:
- Choice of terminal emulator
- SSH security
- Secure file transfer options
- Store credentials for fast connections
- Tabbed interface
Why do we recommend it?
ZOC is an SSH client that provides a remote access terminal emulator. It will run on Windows and macOS. The system has its own scripting language, which should enable you to create task automation across sites and so this secure connection tool has a lot of possibilities.
The utility offers a choice of file transfer utilities, which include SCP, FTP, SFTP, FTPS, Zmodem, Xmodem, Ymodem, and Kermit. The system is easy to install and use.
Who is it recommended for?
ZOC Terminal isn’t free but it doesn’t cost much and you get a perpetual license for your money. The tool doesn’t have an end-user app feel to it, so this is going to appeal most to technicians. Any administrator who likes to write helpful little scripts will love this tool.
Pros:
- Operates on both Windows and Mac, giving admins more options to how they work
- Features a full-fledged terminal and text editor
- Supports multiple file transfer protocols, making it more flexible than PuTTY
- Includes an SSH key generator
- Can use strong AES-256 encryption
Cons:
- Is less user-friendly than competing tools
- Businesses must pay for licensing, similar tools are completely free
ZOC is sold on a lifetime license and you can assess the package with a 30-day free trial.
EDITOR'S CHOICE
ZOC is our top pick for an SSH client because it is very easy to install and use and it provides all of the functions you need to securely connect the built-in terminal emulator and file transfer utilities to remote computers. The system isn’t free, but it has a low price and gives you a lifetime license. Use SCP or FTPS, or SFTP for file transfers, store connection settings and open up multiple sessions in the multi-tabbed interface.
OS: Windows and macOS
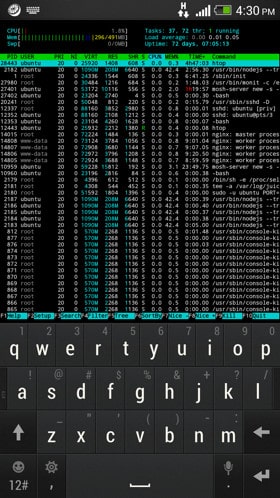
2. JuiceSSH
This SSH facility runs on Android devices, so you can securely access remote computers as you travel around. This is a great tool for checking in with your work computer or your computer at home. The ability to securely access other computers gives you the opportunity to greatly expand your use of mobile devices with limited storage. This is also a good facility for BYOD policies and companies. This is because the SSH involvement imposes user authentication and the encryption used on connections makes up for the security weaknesses of external wifi systems.
Key Features:
- Runs on Android
- Powerful SSH-protected terminal emulator
- Set up a secure link to an office computer
- Provides connection statistics
Why do we recommend it?
JuiceSSH is a free SSH utility for Android mobile devices. The system provides a secure terminal emulator for accessing your work or home computer. There is also a file transfer utility, but this works on a synching mechanism rather than SFTP. However, all of the services are protected by AES-256 encryption.
Related: Ultimate Guide to BYOD
JuiceSSH is particularly good for protecting all activities on your Android device, even those that execute automatically in the background. This feature was built specifically with Cloud syncing in mind, so you can access files on cloud servers and even work on copies offline when you are in areas that have no internet service.
Who is it recommended for?
The most likely market for this product is for personal use. There is a possibility to use the system for fleet devices in a corporation but there are much more sophisticated mobile device management systems that provide container-based application and content delivery as well as tracking, locking, and wiping.
Pros:
- Uses color accents to highlight key connection information
- Supports cloud sync, great for mobile offline file access
- Completely free
- The app provides its own password-protected screen lock
Cons:
- While the product attempts to bring SSH to mobile, the interface makes it hard to view connections and make change
- Better to use in a pinch rather than over the long term
You can download and install JuiceSSH for free from Google Play.
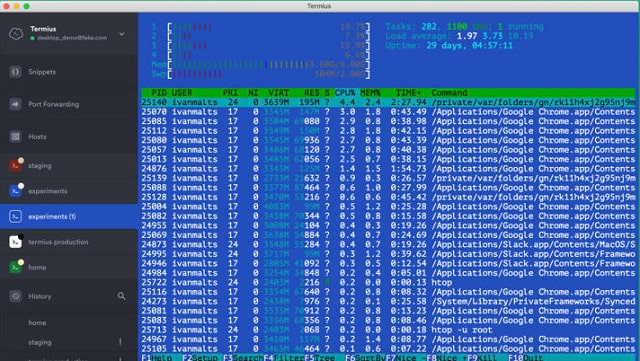
3. Termius
If you want an SSH client for iOS, probably your best option would be Termius. This isn’t the only SSH client system available for iOS and probably not the best — Prompt 2 probably has that distinction. However, Termius is one of the very few SSH clients that you can use for free. This utility allows you to connect to your home computer or work even over public wifi networks because it includes full connection encryption and user authentication before you can access the remote computer.
Key Features:
- Runs on desktops and mobile devices
- Secure connection options
- Paid version includes SFTP
Why do we recommend it?
Termius is an SSH tool for workstations and mobile devices with versions for Windows, macOS, Linux, iOS, and Android. This is a paid tool but you can get the secure terminal with an SFTP implementation for free. This is a more sophisticated tool than JuiceSSH and it is more likely to appeal to corporations.
The SSH client can connect to any other operating system. Termius also includes Mosh, which is an alternative secure connection system for iOS devices. Termius will cover syncing functions to cloud servers and it also includes an SFTP implementation to cover your file transfers. Termius is available for Windows, Linux, Mac OS, and Android. You can use the app for free on one device. That version doesn’t include SFTP or secure syncing, though. The paid version is very cheap and is paid for on a monthly subscription. That plan allows you to run the app on as many devices as you like, and it includes all of the Termius features.
Who is it recommended for?
The free edition of the tool is aimed at individuals and there are three paid plans for businesses. The key feature of Termius is a secure vault, which is an encrypted cloud drive for each subscribing user. Higher plans provide shared vaults, which allows roaming employees to be included in collaborative document development.
Pros:
- One of the only tools that support SSH access on iOS
- Provides full connection encryption, making it safe to use over public networks
- Supports files transfer via SFTP
Cons:
- Free version is limited to a single device
- Can quickly become a memory hog
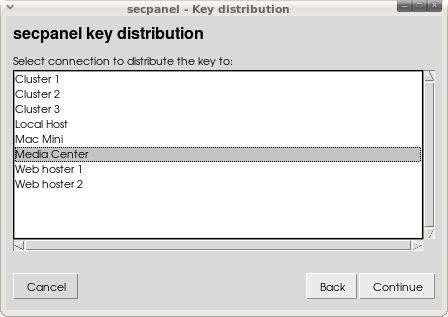
4. SecPanel
SecPanel is a free SSH client for Linux Gnome environments. This tool offers a GUI interface that makes accessing a remote computer a much easier experience than using the Linux command line free tool. SecPanel doesn’t implement SSH; it is a front-end to access the native SSH version that is built into the Linux operating system. It uses the free OpenSSH system.
Key Features:
- Runs on Linux Gnome environments
- Low on memory usage
- No-nonsense interface
Why do we recommend it?
SecPanel is a free GUI-based SSH client for Linux. This system can store connection settings to enable you to connect by just selecting an option from a list of your saved links. This is an easy-to-use and straightforward tool that gives you a secure remote terminal. You also get secure file transfer protocols.
The SecPanel interface is uncomplicated and it doesn’t have the multiple connection tabbed format that other SSH utilities offer. However, the benefit of this is that the program has a very small footprint and doesn’t use much memory or CPU.
The SecPannel interface also gives you access to SCP and SFTP to give you secure file transfer capabilities.
Who is it recommended for?
This is a good tool for system administrators who works on Linux. The tool doesn’t have many frills, which indicates that it isn’t really intended for end users. Its feature-free nature gives it a small footprint, which is another attribute that busy administrators will appreciate a lot more than users would.
Pros:
- Incredibly lightweight, uses minimal resources
- Good for those looking for the bare minimum in terms of features and design
- Offers secure file transfer via both SCP and SFTP
Cons:
- Specifically for Linux Gnome, not available for Windows
- Doesn’t support multiple connection tabs
- Fairly limited when compared to more refined tools
5. SolarWinds Solar-PuTTY
SolarWinds Solar-PuTTY is a great terminal emulator and a good choice for those who need to gain access to remote computers regularly and need SSH security protection. The tool is a product of SolarWinds, which is one of the world’s leading producers of system administration tools.
Key Features:
- You can set up buttons for connections
- Session recovery
- Multiple open sessions
Why do we recommend it?
SolarWinds Solar-PuTTY is an adaptation of the famous PuTTY utility – a fact that SolarWinds makes no effort to hide. You can set up session parameters and then they appear in a menu. Click on one of the buttons in the menu to get connected. This software runs on Windows and Windows Server.
The terminal emulator window allows you to connect multiple sessions in the same interface. The console is tabbed, so you can switch from one session to another by clicking on a tab for each. The application is able to maintain connections to several different remote computers simultaneously.
The tool includes implementations of SCP and SFTP, so you can use it to transfer files to remote computers as well as access them. The attractive presentation of the application is easy on the eye and will help you automate your administration tasks by supporting script transfer and execution.
Who is it recommended for?
This is another free tool that is designed for use by system administrators but this time, for those who work on a Windows computer. The tool gives you an SSH-based system for a secure terminal emulator plus SCP and SFTP for file transfers. A tabbed interface lets you switch between open sessions.
Pros:
- Completely free
- Integrates with SCP and SFTP giving it more functionality than PuTTY
- Offers secure credential storage for fast repeat access
- Can color-code multiple sessions to help organize multiple simultaneous connections
- Can automatically reconnect if the connection is interrupted
Cons:
- Like PuTTY, this tool is designed for technical professionals and requires basic networking knowledge before use
The Solar-PuTTY application installs on Windows environments and you can get it for free.
SSH Commands
The commands available in SSH are very similar to the standard Unix commands. In fact, in most cases, they are exactly the same. If you are unfamiliar with working at the command line, you are more likely to access SSH through a Windows-like console. Most graphical interfaces for SSH offer point-and-click interpretations of the standard commands. However, SSH is available as a command-line utility and even on Windows computers; you will need to use these Unix-like commands within the SSH environment. It is useful to have a list of SSH commands in order to get greater control over the tasks that you can perform on a remote computer with SSH.
SSH Command Cheat Sheet
ls: list files and folders in the current directory. Use ls -al to see attributes as well
cd: change directory. Use cd ~ to get to your home directory, cd – to go to the previous directory, cd .. to go to the parent directory
pwd: show the present directory name with its full path
touch: create a file, with the new filename as a parameter, e.g. touch afile.txt
rm: delete a file, e.g. rm afile.txt. Use a wildcard to delete several files at once, limited to deleting all matching files in the current directory, e.g. rm *.txt. You can delete files in a different directory as long as you have permissions for that folder, e.g. rm /usr/bigbob/note.txt. You can also use a wildcard to remove many files in a remote directory.
rm -rf: delete a directory and all of its contents, e.g. rm thatdir
mv: rename or move a file to a different directory. By default, the source and target names should be in the current directory, but either could be in a different directory, e.g. mv afile.txt bfile.txt or mv /usr/bigbob/afile.txt /user/alicef/afile.txt
mkdir: create a new directory. The name of the new directory is given as a parameter, e.g. mkdir docs
cp: copy a file from filename1 to filename2 with a directory path optionally added to the front of either or both filename, e.g. cp afile.txt ../afolder/bfile.txt. The wildcard * can be used, but the second parameter should be a directory and not a new file name, e.g. cp *.txt archivedir
cp -R: copy all of the contents of a directory to another directory, e.g. cp -R firstdir otherdir
wc: word count reports on the number of words, lines, and characters in a file. Use the option -w to just get a count of words, -l for the number of lines, or -c for just a character count, e.g. wc afile.txt or wc -l afile.txt
cat: dump the contents of a file, with the file name as the parameter options, e.g. cat afile.txt. Include -n to put a sequence number on the front of each line, e.g. cat -n afile.txt. It is also possible to get the contents of one file after another shown on the screen, e.g. cat afile.txt bfile.txt
cat >: create a file and write to it. After the command, press Return and start typing. Everything you write will be saved to the new file, including carriage returns, until you press CTRL-D, e.g. cat > afile.txt
more: cat with a pause in it. The contents will be shown one screenful at a time. Press the spacebar to get the next section of the file; press q to exit before the end of the file, e.g. more afile.txt
head: show the first 20 lines of a file. The number of lines can be specified by an option, e.g. head afile.txt or head -50 afile.txt. Be careful to only use the command on files that contain plain text
tail: show the last 20 lines of a file or the number of lines specified in an option, e.g. tail afile.txt or tail -50 afile.txt. Use tail -f to get a live view of new files added to a file, e.g. tail -f afile.txt
du: disk usage. Use -sh to get the total disk usage of the current directory. Try -sh * to get the disk space used by each element in the directory, e.g. du or du -sh *.
file: names the file type. Can be used with a wildcard to get a list of all files in the current directory, e.g. file afile.txt or file *.
history: list the last 50 commands executed from that account. Use the -c option to clear the history, e.g. history -c
find: list all instances of files or directory that match given criteria, e.g. find / -name “afile” finds all files on the computer with the name “afile,” find * -d lists all directory names on the computer.
last: shows recent logins to the computer with the username of each access. Use a number option to specify how many logins to show, add the -a option to see the hostname of each login, e.g. last -10 or last -10 -a
w: show all users currently logged in and where they logged in from.
netstat: shows all current network connections. Use -an option to see the source and destination ports or -rn to see the routing table of the IPs connected to the server, e.g. netstat -an or netstat -rn
top: shows live system processes. While the display is current, use Shift-M to order by memory usage or Shift-P to order by CPU usage.
ps: process status. This shows currently-running processes and their process identifiers (PIDs). Use option U to list all live processes for a given user, e.g. ps U bigbob. Use aux option to see all system processes, optionally in a hierarchy if the – forest option is added, e.g. ps aux or ps aux – forest.
kill: stop a system process. You can add a “signal,” to make the order stronger. There are several options for this parameter, but the strongest is 9. You need to give the PID of the process that you want to kill and you can get that by running ps or top, e.g. kill 492 or kill -9 492, where 492 is the PID of the process that you want to terminate.
grep: identifies a text string in a file or files, e.g. grep aword /usr/bigbob/*.txt. Use -v option to show all lines in a file that don’t contain the pattern, e.g. grep aword afile.txt.
vi: a very well known text editor that was originally written for Unix. Entering the command opens up an environment that includes its own command language.
nano: a simple editor with its own environment.
pico: another text editor.
SSH Troubleshooting
As with any networking facility, SSH doesn’t always work out of the box. There are settings on other equipment and software running on your network that can interfere with the performance of SSH or even block it. So, you may need to troubleshoot connection failures and delays.
The clarity of information that you get from error messages greatly assists in getting to the root cause of the problem. However, some applications are not built to assist end-users and subsequently, their developers don’t think it’s a valid use of their time to add clarity to error reporting. Unfortunately, SSH is one such application.
The most generalized error message that you are likely to face with SSH is “Connection Refused.” Faced with this blank wall, you are going to have to investigate all of the settings of your network and the server that you are trying to connect to in order to get SSH working.
The SSH client should report back with a more meaningful error message. However, the software you use might not be the most comprehensive implementation of the protocol.
Below is a list of the most common errors and their solutions. If you get the “Connection Refused” message, you need to assume that your client is reporting this general error message because the developers didn’t implement more precise error messages. In that case, test to see if the error is caused by one of these more specific problems. Here are the error messages that you are most likely to encounter:
- Access Denied
- Authentication Refused
- Warning: Remote host identification has changed
- Port 22: Connection refused
- Network error: Software caused connection abort
- Network error: Connection reset by peer
- Network error: Connection timed out
The first three errors relate to your account on the server that you are trying to connect to. The first solution to the problem of “Access Denied” or “Authentication Refused” is to make sure you didn’t make spelling mistakes when entering the username and password. Other reasons for these authentication errors relate to the account. The system administrator might have canceled your account, or changed the password for you. So, if you are sure that you haven’t made a typo, contact the administrator of the remote server to check on the status of your account.
“Remote host identification has changed” refers to the SSL security certificate of the server. Note that the message doesn’t say that the certificate is invalid. If you run the remote host, you will know whether the certificate has been changed. If you are trying to connect to someone else’s computer, check with the administrator if the host has a new security certificate. If it does, just accept the error message and allow connections to continue. It is worth verifying the certificate change rather than just accepting the warning blindly because this message is there to alert you to a possible “man in the middle” attack.
The remaining four error messages in the above list all relate to some point of failure between the SSH app on your computer and the remote server, which means that you need to look at every hardware and software element that provides the connection.
“Port 22: Connection refused” is a catch-all error message that expands only slightly on the straight-forward “Connection Refused” message that some clients display. Basically, you are going to have to check everything in order to find the cause of this error.
The three “Network error” messages give you more to work on. In all of these cases either your computer or the remote host timed out and closed the connection, or there was an interruption in the internet service. If the connection dropped because of errors on the line, then there isn’t much you can do about the problem other than just reconnect.
A timeout is more likely to be caused by inactivity on the connection. Look for a “keepalive” option in your SSH interface to prevent this problem from occurring. The message “Write failed: broken pipe” is also a timeout issue. The good news about these errors is that they don’t signify a serious problem. You just need to connect again.
For the “connection refused” problems check for errors in the following areas:
IP address conflict: run arping, arp -a, or arp-scan to search for duplicate addresses.
Firewall block: list SSH as a permitted application in your firewall policy and/or allow traffic to port 22.
Server unavailable: check that the remote host is actually live either by connecting to it through a different application or by contacting the server administrator.
Server port error: the SSH daemon on the server may be experiencing problems; try to connect to port 22 on the server through the SSH server connectivity test site.
SSH port error: use netstat to make sure that sshd is functioning and listening on port 22. If it is listening on any other port, kill the process and check the port settings in your SSH interface.
SSH daemon error: if the daemon isn’t working, shut down your SSH application and open it again. If the SSH daemon still isn’t running, reinstall your SSH applications.
If none of the above quick solutions work, you need to examine whether just the traffic from your SSH application is being blocked or whether there is a general network error. This could either be on your own network or on the internet connection from your computer to the server that you want to contact.
SSH FAQs
Do I have to install an application in order to use SSH?
You need to have an SSH program on your computer and it isn’t automatically available with all operating systems. However, it is built into Windows 10, all Linux flavors, Mac OS, FreeBSD, NetBSD, OpenBSD, Solaris, and OpenVMS Unix. If you don’t want to use an application with a GUI front end, you could install OpenSSH instead. This is a free protocol, which is actually the SSH implementation that is built into those operating systems. You can interact with its program elements from your own custom programs.
Is SSH only available for Unix?
No. There are implementations listed in this guide that work with Windows, Linux, Mac OS, iOS, and Android. The Original OpenSSH was written for OpenBSD Unix, but there is also a Portable version that will run on Windows, Linux, and Mac OS.
Is SSH a program?
No. SSH is a protocol, which means a set of guidelines. It can be implemented by individuals as long as they follow the rules laid out in the protocol when they write the program. Most implementations create a suite of programs, each of which fulfills a function of the protocol. When you run an SSH application on your computer, a check of running processes will show you several SSH programs running.
Where can I get the SSH2 definition?
The specifications for SSH2 are available for free from the Internet Engineering Taskforce websites. You will find a collection of documents at that site that relate to the SSH2 protocol. However, the key document is RFC 4251.
Which port does SSH use?
SSH has been assigned TCP port 22.
Is there a UDP SSH?
There is no UDP equivalent because SSH needs the session establishment procedures of TCP.
Can’t specify a drive with SCP
If you need to put a drive identifier at the beginning of a file path (e.g. “C:\”) you will run into trouble with SCP because the colon is a special character for that utility. So, you need to switch to that drive before running the scp command. If you need to specify a different directory to the one you are in, use relative file paths rather than an absolute path originating with the drive letter.
Can I use port forwarding with SSH connections?
You need to make sure that the SSH daemon is active on the remote server in order to run SSH port forwarding. You also need to check that your SSH implementation allows you to specify a non-standard port on startup. This will be in the form of a -D command-line option, which allows you to tag a port number onto the destination address, separated by a colon. This will force the connection to switch to a non-standard port when connecting to the remote computer.
Can I protect email transmissions with SSH?
You can establish a link with your correspondent’s email server on SSH and then pipe the email messages down it. However, your mail’s text will still be unencrypted while at rest on the server and the fetch phase from the email client will not be covered by your SSH connection. It is better to choose an email provider that includes end-to-end encryption.
Can I protect POP and IMAP fetches with SSH?
You can wrap email fetches from the mail server to the mail client on your computer if the mail server is running an SSH implementation – this is not standard with most email providers. which is also referred to as ‘tunneling.’ This method also will not protect your incoming emails when they are resident on the email server. In addition, it will not cover the journey of your incoming emails from the senders to your email server.
Can I wrap unprotected applications with SSH?
If the remote server can implement a pause function, such as sleep(), you can start up an SSH tunnel at the command line without entering the SSH command environment. You can then set your second application running through the same local port that you specified in the SSH launch command.
The sleep option gives you time to type in the second command before the initial connection times out for inactivity. In order to control which local port the encryption will run through, you should use the -L option on the SSH command. This option allows you to specify both the local port and the remote port in the format <local port>:<destination IP address>:<remote port>.
How do I stop the connection from timing out?
You can keep an SSH connection open through a “keep alive” command. In OpenSSH this is implemented in the config file of either the server or the client. On the server, you should enable ClientAliveInterval in the file called sshd_config or on the client, enable ServerAliveInterval in the ssh_config file.
How do I get meaningful error messages out of SSH?
Use the verbose mode. This is the -v option that you add to the command. So, for the client, use ssh -v and for the server, run sshd -v. For SSH2 use -d2.
I get the error message “Connection refused”
The SSH daemon on the server you are trying to connect to isn’t running. Another possibility is that it isn’t listening on the standard port, or it isn’t listening on the port you specified for the connection.
I get error message “Compression level must be from 1 (fast) to 9 (slow, best)“
Go to your config file and set CompressionLevel to a number from 1 to 9.
SCP won’t copy a file to the remote host with the same name
Don’t forget to put a colon (“:”) on the end of the line if you want to preserve the file name when sending it:
scp fname.log server.remotehost.com:SCP wildcard characters don’t work
SCP expands out wildcards on the local machine before sending the command, so you won’t be able to use wildcards to refer to groups of files on the remote computer without escaping them. Escaping the wildcard prevents its interpretation locally.
For example:
scp server.remotehost.com:\*.log .SCP won’t reference remote host environment variables
SCP interprets environment variables locally before sending the command to the remote computer. Put the entire contents of the command in single quotes but leave the target outside of the quotes:
scp ‘server.remotehost.com:$MAIL’ .Using SSH
Once you have chosen an SSH implementation, you will need to become familiar with the way that interface works. Many SSH application producers build in a few extras to give their product a distinction in the marketplace. You may find that it is these extra features that make you grow dependent on that one SSH interface and lose interest in continuing your search through all the available products.
Look out for free applications and free trials of paid SSH servers so that you can try out a few options before you settle on one specific server. Do you have a favorite SSH application? Leave a message in the Comments section below to share your experiences.
See also:
Best PuTTy alternatives for SSH clients
SFTP commands cheat sheet
How to hide your OpenVPN traffic with an SSH tunnel
Image: Security binary code from Pixabay. Public Domain.