Network security is a top priority for businesses and individuals alike. Cyberattacks, including viruses and malware, are constantly evolving, making it crucial to have proactive measures in place to detect and mitigate threats before they cause significant damage. One of the most effective ways to identify and eliminate malicious software from your network is by performing a thorough network virus scan.
A network virus scan involves using specialized antivirus or network security software to scan your network for known viruses, malware, ransomware, and other types of malicious code. This process helps detect infected devices, vulnerable entry points, and unauthorized activity within your network. Regular virus scanning not only helps protect your devices and data but also plays a key role in preventing data breaches, service disruptions, and reputational damage.
This guide will walk you through the process of performing a network virus scan, from selecting the right antivirus solution to configuring scan schedules and interpreting scan results. We will cover both manual and automated scanning methods, offer best practices for ensuring a thorough scan, and provide tips for responding to detected threats. By the end of this guide, you will have the knowledge to conduct regular, effective virus scans on your network, safeguarding your organization or personal network from evolving cyber threats and ensuring the integrity of your digital environment.
What is a ‘network virus’ and how is it different from a normal virus?
A network virus is a type of malware that can replicate itself across multiple computers through network packets. Network viruses are different from traditional viruses because they don’t rely on files in order to spread but self-replicate across hosts and spread through executable code or a document.
For most viruses, administrators can deploy an antivirus solution that runs manual or automated scans to detect when a device is compromised. Once a virus is detected the user can quarantine the files and remediate the outbreak. Unfortunately, the process is a little more complex when dealing with a network virus.
As network viruses spread through network packets, traditional antivirus solutions can’t detect them. Such viruses are very difficult to get rid of and commonly re-infect devices. The side effects of a successful attack range from poor network performance to data theft, compromised device performance, and downtime.
From a network administrator’s perspective, Network viruses require a different type of security strategy than traditional viruses. To detect a network virus a network administrator needs to scan network traffic with a packet sniffer or intrusion detection tool to detect malicious packets and other suspicious activities.
Here is our list of the best packet-sniffing software:
- Site24x7 EDITOR’S CHOICE This is a cloud-based platform for comprehensive network monitoring and traffic flow analysis. It provides detailed insights into bandwidth usage, device health, security, traffic patterns, and more. Start a 30-day free trial.
- Paessler PRTG Network Monitor This system scans networks and provides a network inventory and map as well as a packet sniffer. Available for installation on Windows Server or as a cloud SaaS package.
- ManageEngine NetFlow Analyzer This package runs on Windows Server or Linux and it collects packets for protocol analysis by looking at the port information in packet headers.
Here is our list of the best intrusion detection systems:
- ManageEngine Log360 (FREE TRIAL) This SIEM System can take feeds from the network as well as from endpoints and that enables it to look for anomalous activity on all parts of your IT system. Available for Windows Server.Download a 30-day free trial.
- CrowdStrike Falcon This hybrid tool operates as an AV on devices and centralizes activity monitoring in a cloud-based unit. The endpoint unit runs on Windows, macOS, and Linux.
- SolarWinds Security Event Manager This is a log messages collector, consolidator, and analyzer that includes pre-written searches for security threats.
How to scan for malicious traffic with a packet sniffer (Wireshark)
Wireshark is a packet sniffing tool available for Windows, macOS, and Linux that you can use to scan your network for malicious traffic. With Wireshark you can sniff traffic to identify infected files, helping you to find the root cause of a virus outbreak. Before running a capture you can select the type of interface you want to monitor.
To start capturing packets in your network, double click on the Wi-Fi option under the Capture heading. The software will start to collect packets in real-time displaying information such as Time, Source, Destination, Protocol, and other Info. You can stop capturing packets by pressing the red Stop icon in the top left corner of the screen.
Filtering Packets
To make sense of the information you capture, you’ll want to use packet filtering. Packet filters limit the output information based on the type of filter you apply. You can apply filters by using the filter box/search bar at the top of the screen.
Filtering packets are useful for identifying malicious packets as you can search for packets coming to and from an IP address or filter all traffic by a certain type. For example, to see packets coming to or from an IP address you can use the following filter (Change the IP address for the one of the IP address you want to filter IP packets coming from ):
ip.src == 192.788.53.1
Alternatively, if you want to filter packets that are going to an IP address you can use the following filter:
ip.dst == 192.788.53.1
You can also combine the two filters together if you want to view traffic traveling to and from the IP address with the following command:
ip.src == 192.788.53.1 or ip.dst == 192.788.53.1
If you want to filter by packet type then you can do so by entering the type of packets you want to filter into the filter bar (the example below uses DNS, but you could use another packet type such as DHCP, ICMP, or TCP):
dns
Filtering IP addresses in this manner allows you to monitor the conversations taking place between particular machines, so if you suspect that a computer is infected, you can take a closer look at its traffic. It’s a good idea to regularly inspect hosts generating the greatest traffic volume, as this can indicate the host is infected with malware and is attempting to spread it to other machines.
Another key issue to look out for is if traffic is sent to and from unusual locations or if a host starts to send an unusually high amount of traffic. The only way to identify this abnormal activity is to take a baseline capture of your normal network activity so you can see anomalous behavior more clearly.
For an in-depth tutorial on Wireshark see our How to use the Wireshark Network Protocol Analyzer post.
Why scan for malware and malicious traffic with a packet sniffer?
Running a standard virus scan with an antivirus will enable you to detect malicious entities like viruses and malware that have infected your device. The traffic that enters your network is a key entry point to your network, and monitoring that entry point will enable you to respond quickly when a threat breaches your defenses.
Packet sniffers are an important tool because many antiviruses struggle to detect network viruses that replicate across multiple hosts. Tools like Wireshark and Snort give you the ability to pinpoint strange connections across your network so that you can investigate and address any underlying threat.
By combining continuous packet sniffing with traditional antivirus virus scanning you can protect your network more comprehensively, and defend against a broader range of threats. In other words, combining the two significantly reduces your exposure to online threats.
Using an IDS to detect malware
An Intrusion Detection System (IDS) is a type of software that can detect attempts to break into your network. IDS tools can detect intrusion attempts, like malware, viruses, trojans, or worms, and notify you when an attack takes place. Examples of IDS solutions you can use to monitor for threats include Snort and Nmap.
IDS’s are useful because they can detect the early signs of a cyber attack. For example, before launching an attack on a network, many hackers will run a port scan to look for vulnerabilities. With a tool like Snort, you can detect port scanning, which gives you a heads up before any damage is done to your network.
IDS solutions use signature-based and anomaly-based detection methods to detect attacks. A signature-based IDS searches for malicious patterns in traffic based on known attacks and an anomaly-based IDS uses machine learning to detect abnormal behavior and flag it up to the user.
Out of the two methods, anomaly-based IDS solutions are more effective at scanning networks for unknown viruses and malware. Signature-based tools need to be regularly updated to stay effective and struggle against unknown zero-day attacks.
Packet sniffer or IDS for detecting malware?
Both packet sniffers and IDSs are useful for detecting malicious activity taking place on the network and are very similar. The key difference between the two is that an IDS is a packet sniffer with anomaly detection, which can identify malicious traffic patterns and send alerts to notify the user.
For example, with Snort, you can create traffic rules to detect malicious code. In contrast, packet sniffing tools like Wireshark don’t have an alerts function and you have to identify suspicious activity manually by collecting and filtering packets.
While IDS’s are superior at automating threat detection and response, packet sniffers remain useful for identifying and investigating malicious traffic patterns. In short, both Wireshark and Snort are viable solutions for detecting malicious traffic and protecting your network against attackers.
Our methodology for selecting a network virus scanning tool
We reviewed the market for network protection systems and tested tools based on the following criteria:
- A choice of deep packet inspection tools and SIEM systems
- Options for on-premises hosting and cloud-based services
- Facilities that provide automated scanning for threat detection
- The possibility to use the tool for manual threat analysis
- Nice to have a package that can also perform network monitoring functions
- A free trial that allows the software to be assessed before paying
- Value for money from a price that offers a bargain with respect to the number of services that the tool provides
The Best packet sniffing software
If you want to search for other packet-sniffing tools to monitor your network, then there are plenty of tools to choose from. We’ve listed some of the top free and paid alternatives to Wireshark below:
1. Site24x7 (FREE TRIAL)
Site24x7 is a cloud-based network performance monitoring tool that provides complete visibility into your environments to help you make data-driven decisions. With this tool, you view device availability and performance, detailed network traffic insights, WAN performance metrics, and more.
Key Features:
- AI-powered monitoring.
- Monitors multiple networks through the same console.
- Detects traffic anomalies and security issues.
- Real-time alerts.
- Custom report generation.
Why do we recommend it?
Site24x7 monitors every aspect of your vast network to provide detailed insights on devices, traffic patters, network performance, and more. With such insights, you can proactively address issues in your network and plan for optimal performance. It is cloud-based and hence there are no downloads and setup hassles. Its AI models can help with decision-making.
Who is it recommended for?
Site24x7 is a good choice for MSPs managing multiple client networks. It is also a good choice for IT teams that have to manage vast or hybrid networks.
Pros:
- A single tool for monitoring everything in your network.
- Clear and flexible pricing model.
- Easy setup.
- Real-time alerts.
- AI-powered insights.
Cons:
- No on-premises deployment
You can register for the 30-day free trial.
EDITOR'S CHOICE
Site24x7 is the top pick for detecting security vulnerabilities in your network. This tool comes with extensive capabilities to monitor every aspect of your network, including devices, traffic, WAN, and more. What we love about this tool is that it takes information from these multiple sources and analyzes it to provide detailed insights about the security issues in your organization. Moreover, it is simple to set up and easy to use. We also love its AI-based insights and extensive reports that present all the analyzed information in an easy-to-understand format. Due to these reasons, we highly recommend Site24x7 to keep your networks safe.
Download: 30-day FREE Trial
Official Site: https://www.site24x7.com/network-performance-monitoring.html
OS: Cloud-based
2. Paessler PRTG Network Monitor
Paessler PRTG Network Monitor is a free network monitoring tool that you can use to monitor IP, UDP, and TCP traffic. With the packet sniffer sensor you can monitor IRC, AIM, Citrix, FTP, P2P, DHCP, DNS, ICMP, SNMP, IMAP, POP3, SMTP, NetBIOS, RDP, SSH, VNC, HTTP, HTTPS, and more. It is available for Windows and Mac.
Key Features:
- Network discovery
- Packet sniffer
- Network inventory and mapping
- Protocol analysis
Why do we recommend it?
Paessler PRTG Network Monitor is able to monitor networks, servers, and applications. The buyer decides which of the monitoring tools in the package, called sensors, should be activated. This system includes a packet sniffer function and a protocol analyzer. It also has a customizable system of alerts.
Who is it recommended for?
This package will appeal to a wide audience because it is offered as a software package for Windows Server and as a SaaS cloud platform. The system is priced according to the number of sensors that the buyer activates and it is free to use for only 100 sensors.
Pros:
- Can be used to detect unusual traffic
- Continuous network device scans
- Network updates that will spot rogue devices
- Options for on-premises or cloud deployment
Cons:
- Not a security monitoring system
You can download the software for free.
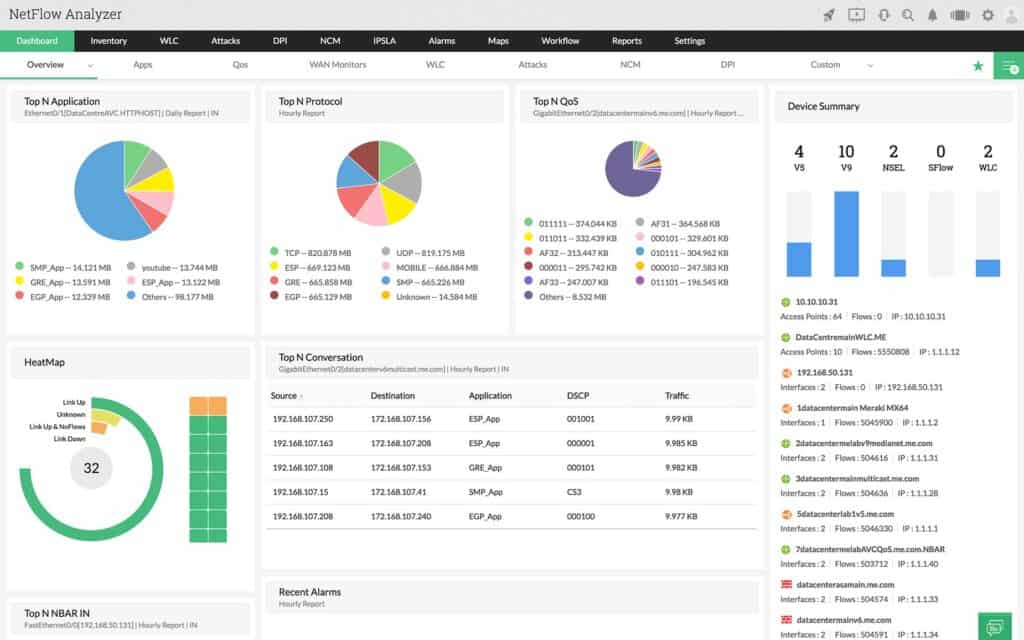
3. ManageEngine NetFlow Analyzer
ManageEngine NetFlow Analyzer is a paid packet collection tool you can use to monitor network bandwidth consumption. With ManageEngine NetFlow Analyzer you can monitor interface bandwidth and traffic patterns in real-time. Through the Advanced Security Analytics Module, you can view all security events alongside an anomaly count. It is available on Windows and Linux. You can download the free trial.
Key Features:
- Traffic analyzer
- Flow protocols
- Packet inspection
Why do we recommend it?
ManageEngine NetFlow Traffic Analyzer is a packet tracker and traffic assessor that focuses on preventing switches and routers from getting overloaded. The tool can also detect anomalies in traffic, such as surges in unusual traffic to specific endpoints and ports. You can set up the service to alert for anomalous activity.
Who is it recommended for?
This system is available for on-premises installation on Windows Server and Linux. It is also offered as a SaaS platform. The service will detect excessive traffic per protocol, source, or destination. It can also be used for capacity planning. The system is suitable for mid-sized and large companies.
Pros:
- Identifies excessive traffic per protocol
- Reads packet headers
- Prevents network device overloading
Cons:
- No remediation mechanisms
See our related post on the Best Packet Sniffer.
The Best Intrusion Detection Systems
You can read more about IDS services and how they work in Intrusion Detection Systems Explained: Best IDS Software Tools Reviewed. If you haven’t got time to read that report, here is a quick rundown of the three best intrusion detection systems.
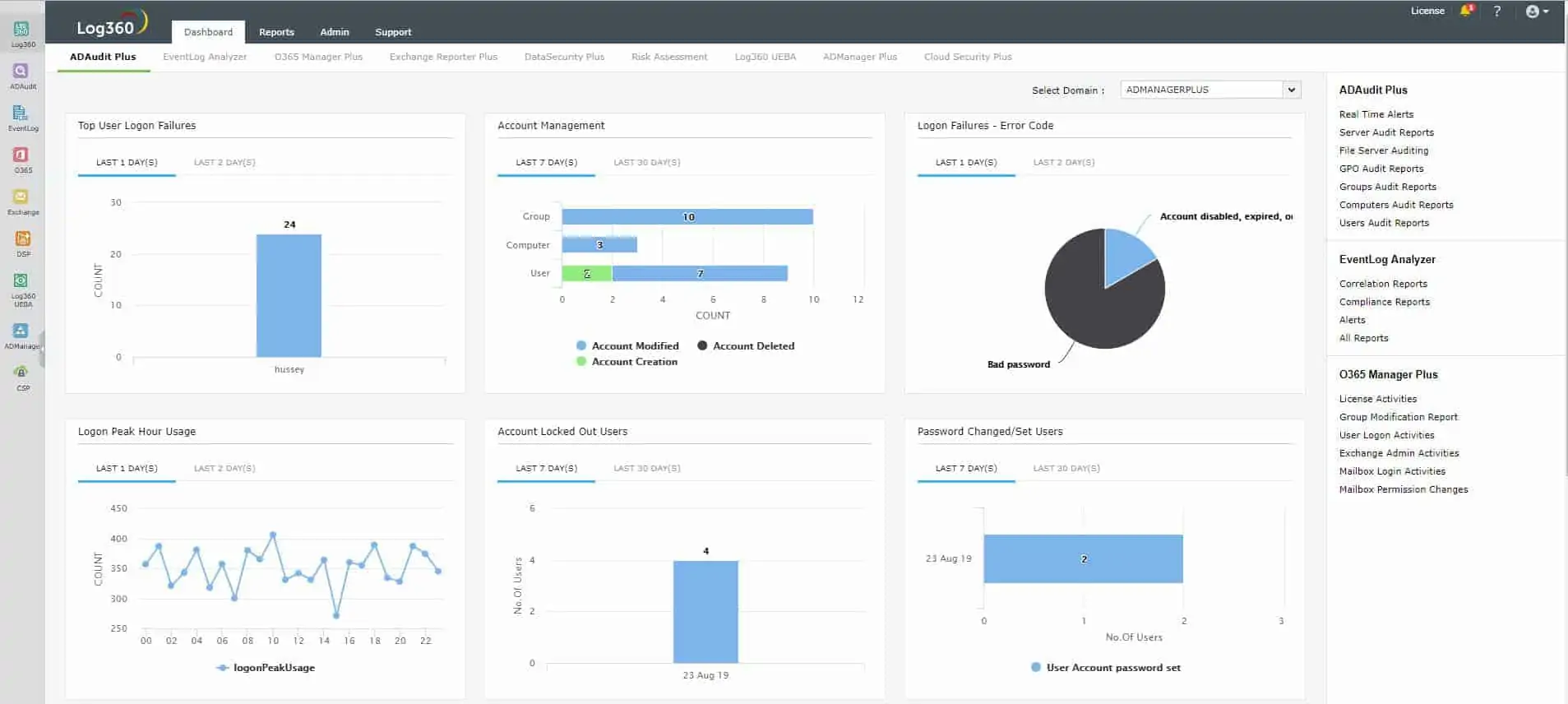
1. ManageEngine Log360 (FREE TRIAL)
ManageEngine Log360 is megapack of ManageEngine tools. It includes Active Directory analysis and protection measures, a log manager, and a SIEM. The tool is also able to track user account activity for insider threat and account takeover detection. The intrusion detection service is found within the SIEM tool.
Key Features:
- Log analysis
- Threat hunting
- Log management
Why do we recommend it?
ManageEngine Log360 is able to take system activity data from all of the devices on your system. That includes network equipment as well as endpoints. The tool searches the pooled log data for threats and can spot unusual activity that could be caused by malware or intruders. The package also provides measures to identify and block insider threats and account takeovers.
Who is it recommended for?
This is a very large pack of tools that provides Active Directory security measures and specialized units for protecting email systems and Microsoft 365. The core of the package is its log manager and SIEM tool and the entire package is particularly suitable for companies that need to prove compliance with PCI DSS, GDPR, FISMA, HIPAA, SOX, and GLBA.
Pros:
- Threat scanning based on system-wide activity data
- User behavior analytics for insider threat detection
- Compliance management
Cons:
- This is a very large package and you might not need all of its modules
This package is available for Windows Server. Most of the components of the package are also available individually, so you can look at the ManageEngine list of modules to see whether you would rather buy some of the elements instead of the whole pack. You can examine ManageEngine Log360 with a 30-day free trial.
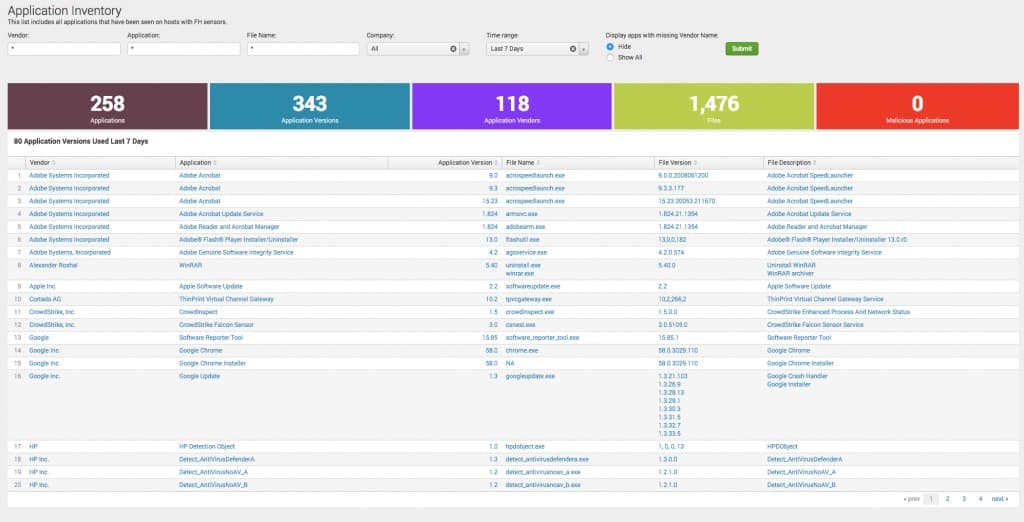
2. CrowdStrike Falcon
CrowdStrike Falcon is a cloud-based platform of security tools that work off reports sent up to the cloud server from the one site-based product in the family, Falcon Prevent. The Falcon Prevent service is an endpoint protection system that operates an antimalware and intrusion detection service by looking for anomalous behavior. All malicious activity comes in from the network and so the reports from this tool also give you an insight into network viruses.
Key Features:
- Hybrid solution
- Endpoint protection
- Cloud-based coordination
Why do we recommend it?
CrowdStrike Falcon is a multi-level protection system with a next-generation antivirus installed on every endpoint and a centralized cloud controller that searches uploaded activity reports for threats. The system is easy to expand by just installing the endpoint unit, called Falcon Prevent, on a new endpoint.
Who is it recommended for?
This package is highly-regarded and it has a strong client list among the largest companies in the world. The Falcon Prevent unit is a little pricey and that puts the service out of the reach of small businesses. Mid-sized businesses might also find the cost a little high.
Pros:
- An endpoint unit that can continue to operate when isolated from the network
- Company-wide private threat intelligence
- Early warning for endpoint hardening
Cons:
- A little pricey
CrowdStrike offers Falcon Prevent on a 15-day free trial.
3. SolarWinds Security Event Manager
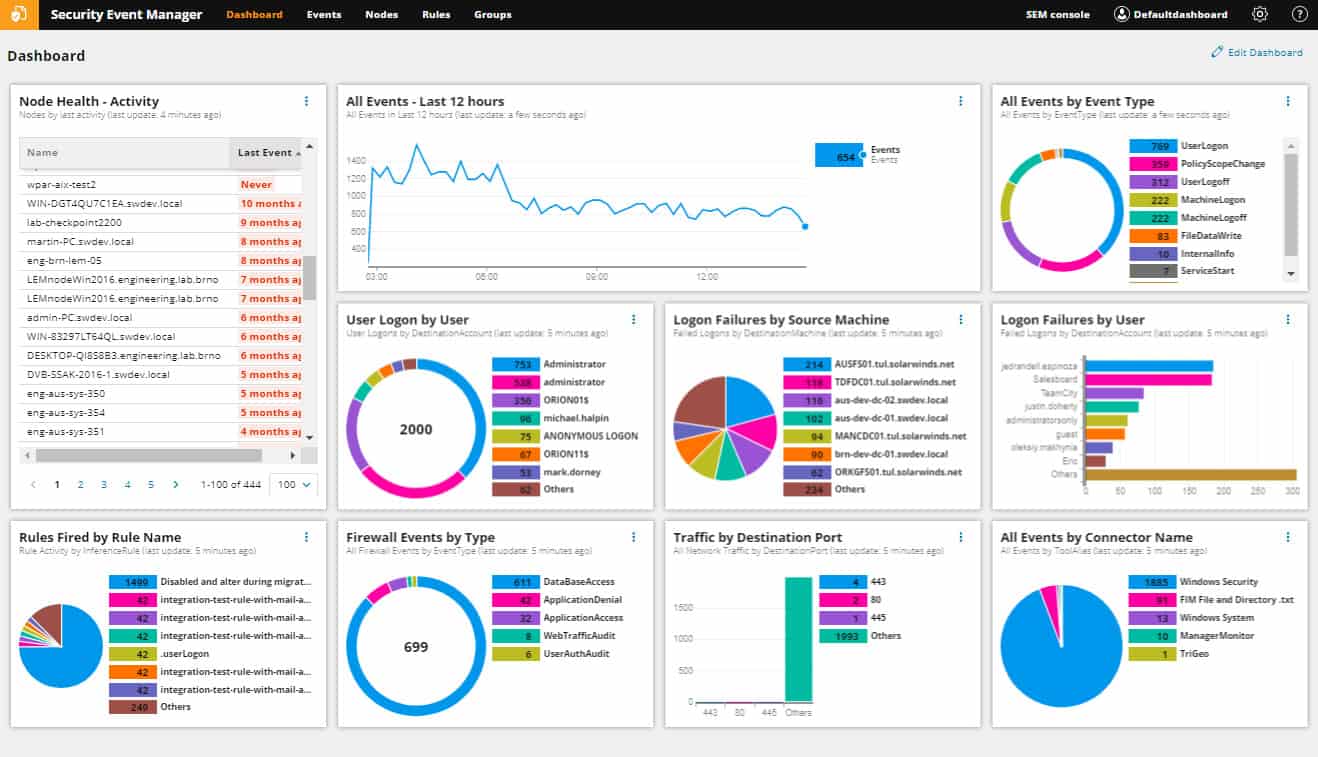
SolarWinds Security Event Manager (SEM) is a host-based intrusion detection system but you can easily give it network-based intrusion detection capabilities by feeding it the network security monitoring output of Snort. This is an on-premises package that runs on Windows Server. It will process log messages generated by Unix, Linux, and macOS computers as well as Windows.
Key Features:
- Log management
- Threat hunting
- Log analyzer
Why do we recommend it?
SolarWinds Security Event Manager provides log management and security scanning. This system scans logs for threats and also provides a data viewer with tools for manual analysis. The data gatherer includes network traffic reports and the system will alert if it identifies viruses or human threats.
Who is it recommended for?
This package is suitable for large businesses with complicated systems. The tool collects data from operating systems, software packages, network devices, and firewalls. It can implement automated remediation actions to shut down threats. So, it provides a full security service against manual and automated threats.
Pros:
- Consolidates and files log messages
- Data viewer with tools for analysis
- Implements automated threat-hunting
Cons:
- No cloud version
Try the tool on a 30-day free trial.
Network virus scanning best practices
Scanning for traditional and network viruses is vital for protecting your infrastructure and preventing malware outbreaks. Being aware of the risks and proactively scanning will give you the best chance of defending yourself against the next generation of online threats. However, there are some best practices you’ll want to bear in mind:
1. Backup your files!
Backing up your files regularly is disaster recovery 101, both for protection against viruses and other issues like system failures or natural disasters. Regularly backing up your files periodically will ensure that your data is protected even if you encounter a persistent virus.
2. Turn off your internet connection
If you find out a device is compromised, one of the first things you should do is turn off your internet. Cutting off the device will stop the compromised system from communicating with external entities so that you can contain the problem and work on restoring the system more effectively.
3. Schedule Regular Scans
Scheduling regular scans is essential for making sure that you continually discover new threats. One-off scans can be good for diagnosing current problems but you’ll miss any security events that take place after you stop scanning. Regularly scanning up will ensure your devices are secure.
4. Make Sure to Follow Up!
Once you’ve run a scan, you’ll need to make sure that you’ve done everything needed to eradicate the threat. Many scanning tools will generate reports that give you information on how to deal with infected files, so following these instructions is a good way to make sure that you implement the necessary changes to protect your system.
Perform a network virus scan to protect important endpoints
While antivirus solutions can’t protect you against every online threat they play an important part in securing your endpoints against some of the most common threats online. Network scanning is a simple way to minimize your exposure to online threats.
Remember to schedule regular scans to make sure that you stay up to date on security risks. Should you find that a system is compromised, cut off the internet, and quarantine the offending software so that you have time to remediate the issue. You also want to make sure that the virus isn’t hiding in your backup files before rebooting the system.
Network Virus Scan FAQs
What is a network virus?
By definition, a “network virus” is a type of fileless malware that moves from computer to computer without saving files on any device but going straight into the operating system. Without a file to scan for, these systems are very difficult to detect because they can only be spotted as network packets and running processes. However, often, when people refer to a “network virus scan” they actually mean a scan that reaches across the network to scan each connected device.
How do you scan a network for a virus?
Scanning network traffic for viruses rather than scanning each endpoint connected to the network involves examining packets that travel around the network. The best security software category for this job is a network-based intrusion detection system (NIDS). This scans packets for known contents that indicate anomalous behavior. NIDS services can spot unauthorized user activity as well as network-bound viruses.