
Remote Access Trojans (RATs) are a type of malware threat that lets a hacker take control of your computer. The spying activities that the hacker may carry out once that RAT is installed vary from exploring your files system, watching activities on the screen, and harvesting login credentials.
The hacker might also be using your internet address as a front for illegal activities, impersonating you, and attacking other computers. Viruses downloaded through RAT will infect other computers, while also causing damage to your system by erasing or encryption essential software. RATs should not be confused with Remote Administration Tools which share the same acronym.
Remote Access Trojans (RATs) are a significant cybersecurity threat, targeting both individuals and organizations by giving attackers unauthorized access to systems. For IT professionals, network administrators, and security teams, managing and protecting against these threats is a critical concern. This software is specifically designed to identify, track, and eliminate RATs from infected systems, providing a crucial layer of defense against cyber intrusions.
The primary roles involved in using or purchasing RAT detection and removal tools are cybersecurity professionals, IT support teams, and incident response teams. These professionals face the common pain points of detecting and mitigating covert attacks that often remain hidden for extended periods. RATs can bypass traditional security measures, making it difficult for businesses to safeguard sensitive data and systems.
As organizations become more digital and remote work increases, the potential for RAT infections grows, posing even greater risks. These security tools help address such challenges by providing real-time monitoring, remote access alerts, and the ability to terminate malicious connections. By detecting unauthorized access and eliminating RATs, businesses can prevent data breaches, safeguard user privacy, and minimize operational disruptions caused by these stealthy threats.
Remote Access Trojans (RAT) software can address the following problems in your organization
- No alerts or notifications when there’s any unauthorized activity in your network.
- Unable to trace how a RAT entered the network.
- Delayed detection of remote access, resulting in late mitigation and higher damages.
- Slow system performance due to hidden malware.
- No centralzied tool for scanning and isolating compromised devices.
Effective RAT detection and mitigation helps organizations ensure the security and integrity of their digital environments.
Here is our list of the best intrusion detection tools for RAT software, scanners & detection tools:
- SolarWinds Security Event Manager EDITOR’S CHOICE Goes beyond RAT detection with automated remediation tasks that help you block RAT activities and review suspicious behavior on your entire network.
- Snort Industry stalwart in NIDS first launched by Cisco.
- OSSEC Open-source HIDS gaining a following for data gathering capabilities.
- Zeek Free network-based intrusion detection system for Unix, Linux, and Mac OS.
- Suricata Monitors IP, TLS, TCP, and UDP protocol activity.
- Sagan Not a standalone intrusion detection system, good for automating scripts.
- Security Onion Open-source amalgamation of other open-source tools on this list.
- AIDE Specializes in rootkit detection and file signature comparisons.
- OpenWIPS-NG Preferred for wireless packet sniffing.
- Samhain Great for setting alerts, but no real troubleshooting capabilities.
- Fail2ban Scans log files and bans IPs that show malicious activity.
If you need to know more, explore our vendor highlight section just below, or skip to our detailed vendor reviews.
Highlights of the Best Intrusion Detection Tools for RATs, Scanners & Malware Detection
Top Feature
Real-time event correlation, log-driven threat detection with automated response options
Price
From $1,789
Target Market
SOCs, IT teams, audit teams needing malware indicators from log data
Free Trial Length
30-day free trialAdditional Benefits:
Features:
Top Feature
Signature and anomaly-based network intrusion detection
Price
Free; Rule packs available — $29.99/year for personal use, $399/year per sensor for business use
Target Market
Skilled security technicians
Free Trial Length
Free tool; no trial period for the paid rule sets
Read more ▼
Top Feature
Log-based intrusion detection for hosts
Price
OSSEC: Free; OSSEC+: Free; Atomic OSSEC: $55/year per endpoint
Target Market
Cybersecurity professionals and system administrators with technical expertise
Free Trial Length
OSSEC and OSSEC+ are free; no trial for Atomic OSSEC
Read more ▼
Top Feature
Application-layer threat detection with anomaly and signature analysis
Price
Free
Target Market
Researchers and security professionals on Unix-based systems
Free Trial Length
Not applicable (free tool)
Read more ▼
Top Feature
Application-layer visibility with packet reassembly
Price
Free
Target Market
Businesses of all sizes
Free Trial Length
Free tool
Read more ▼
Top Feature
Automated log-based threat remediation
Price
Free
Target Market
Tech-savvy teams needing low-cost IDS/IPS
Free Trial Length
Free tool
Read more ▼
Top Feature
Open-source IDS combining Suricata, Zeek, and Elastic Stack
Price
Free
Target Market
Security professionals and SOC teams seeking an open-source, scalable threat detection platform
Free Trial Length
Free and open-source
Read more ▼
Top Feature
File integrity monitoring for Linux and Unix systems
Price
Free
Target Market
Technical users on Linux/Unix platforms
Free Trial Length
Free tool
Read more ▼
Top Feature
Real-time wireless intrusion prevention with automated countermeasures
Price
Free
Target Market
Skilled cybersecurity professionals managing Wi-Fi networks
Free Trial Length
Free tool
Read more ▼
Top Feature
Stealth file integrity monitoring using cryptographic checksums
Price
Free
Target Market
Unix/Linux admins building custom IDS solutions
Free Trial Length
No trial; open-source and free
Read more ▼
Top Feature
Automatic IP banning for brute-force attack prevention
Price
Free
Target Market
Best for users on Unix, Linux, or macOS seeking a lightweight, free intrusion prevention system
Free Trial Length
Free open-source tool
Read more ▼
Key points to consider before selecting RAT detection tools
When selecting RAT detection tools, it’s important to consider the following key points to ensure effective protection against these covert threats:
1. Detection Capabilities
Ensure the tool offers comprehensive RAT detection features, including real-time scanning for known and unknown RATs, as well as the ability to identify suspicious network activities, unusual processes, or unauthorized remote access.
2. Ease of Deployment
Look for a tool that is simple to install and configure, with minimal disruption to existing systems. A user-friendly interface and straightforward setup process will ensure faster deployment across your network.
3. Compatibility
Ensure the tool is compatible with your existing IT infrastructure, operating systems, and security measures. The tool should be able to seamlessly integrate with other cybersecurity solutions and support various platforms, including Windows, macOS, and Linux.
4. Customizable Alerts and Reporting
Choose a RAT detection tool that offers customizable alerts for unusual activity and detailed reporting. This allows IT teams to respond quickly and investigate any incidents in-depth, ensuring timely resolution.
5. Performance Impact
Consider the tool’s system resource usage. A good RAT detection tool should run quietly in the background without significantly impacting system performance or user experience.
6. Cost and Licensing
Evaluate the cost-effectiveness of the tool based on the size of your network and the scope of protection required. Some tools may offer flexible licensing models based on the number of endpoints, while others may be priced per user or device.
7. Support and Updates
Verify that the RAT detection tool is supported by a reliable vendor, offering timely updates to address emerging threats. Regular software updates and customer support are critical to keeping your system protected from new RAT variants.
By considering these factors, businesses can select the most effective RAT detection tool to safeguard their networks and data from unauthorized access and cyber threats.
How to calculate ROI for Remote Access Trojan detection software
Calculating the ROI (Return on Investment) for Remote Access Trojan (RAT) detection software involves measuring the benefits gained from the software compared to its costs. Here’s how to calculate it:
Identify the Costs
Consider the following cost categories:
- Initial purchase cost: The upfront price of the RAT detection software.
- Subscription/maintenance costs: Any recurring fees for updates, support, or software maintenance.
- Training costs: The time and money spent on training staff to use the software effectively.
- Deployment costs: Resources needed to install and configure the software across the network.
Estimate the Benefits
You probably already have an idea of how the RAT detection system will improve your business – you will have been triggered into the acquisition process by some realization of a threat. However, many find quantifying the benefits difficult. Start by addressing the following benefits and estimate a value for each of these achievements.
- Prevention of Data Breaches: Estimate potential losses from a RAT-induced breach, including legal fees, customer compensation, and reputational damage. Subtract the cost of the software.
- Time Savings: Consider the time saved by security teams in identifying and mitigating RAT threats compared to manually responding to incidents. Multiply by the hourly rate of staff involved in incident response.
- Reduced Downtime: Calculate the value of downtime prevented by detecting RATs early, including lost productivity, business disruptions, and potential revenue loss.
- Improved Compliance: If the software helps in meeting regulatory compliance (e.g., GDPR, HIPAA), consider the cost savings from avoiding fines.
Calculate ROI
Use the following formula to calculate the ROI:
Where:
- Total Benefits = Total value of data breach prevention, time savings, reduced downtime, and improved compliance.
- Total Costs = Initial purchase, subscription, training, and deployment costs.
Example:
If the RAT detection software costs $5,000 for the year, and it helps prevent a potential data breach worth $50,000, saves 200 hours of IT staff time ($100/hour), and reduces 10 hours of downtime ($1,000), then:
- Total Benefits = $50,000 (breach prevention) + $20,000 (time savings) + $1,000 (downtime reduction) = $71,000
- Total Costs = $5,000 (software cost)
This means that for every dollar spent on the software, $13.20 is saved or generated in benefits, yielding a 1,320% ROI.
This approach helps quantify the value of investing in RAT detection software, showing how it offsets costs by preventing costly security incidents and operational inefficiencies.
RAT software tools and APTs
RATs are tools that are usually used in a stealth type of hacker attack, which is called an Advanced Persistent Threat, or APT. This type of intrusion is not focused on damaging information or raiding computers quickly for data.
Instead, APTs consist of regular visits to your network that can last for years. RATs can also be used to reroute traffic through your company network to mask illegal activities.
Did You Know…
Some hacker groups, predominantly in China, have even created a hacker network that runs through the corporate networks of the world and they rent out access to this cybercrime highway to other hackers. This is called the “terracotta VPN” and it is facilitated by RATs.
Early invasions
RATs have quietly been around for more than a decade. The technology was discovered to have played a part in the extensive looting of US technology by Chinese hackers back in 2003. The Pentagon launched an investigation, called Titan Rain, which discovered data theft from US defense contractors, with development and classified testing data being transferred to locations in China.
You may recall the US East Coast power grid shutdowns of 2003 and 2008. These were also traced back to China and were also facilitated by RATs. In short, a hacker who can get a RAT onto a system can activate all of the software that the users of those computers have at their disposal.
Hybrid warfare
A hacker with a RAT can command power stations, telephone networks, nuclear facilities, or gas pipelines. RATs not only represent a corporate network security risk, but they can also enable belligerent nations to cripple an enemy country.
The original users of RATs for industrial espionage and sabotage were Chinese hackers. Over the years, Russia has come to appreciate the power of RATs and has integrated them into its military arsenal. APTs are now officially part of the Russian offense strategy that is known as “hybrid warfare.”
When Russia seized territory from Georgia in 2008 it employed DDoS attacks to block internet services and APTs using RATs to gather intelligence, control, and disrupt Georgian military hardware and essential utilities. Russia’s use of RATs to destabilize Ukraine and the Baltic States continues to this day.
Russia employs semi-official hacker groups, such as APT28. Another hacker group, known as APT15 is regularly used by the Chinese government. The names of these groups explain their main strategy, the “advanced persistent threat,” which is facilitated by RATs.
The rise in trade tariff tensions in 2018 has seen a new spurt in Chinese hacker activity, particularly the semi-military APT15 group. The troubles between the USA and North Korea that have been rumbling on since 2015 have also caused a rise in RAT-assisted APT activity originating in North Korea.
So, while threat actors & hackers around the world use RATs to spy on companies and steal their data and money, the RAT problem has now become an issue of national security for many countries, particularly the USA. We have included some examples of RAT tools below.
Defense against Remote Access Trojan software
Antivirus systems don’t do very well against RATs. Often the infection of a computer or network goes undetected for years. The obfuscation methods used by parallel programs to cloak the RAT procedures make them very difficult to spot. Persistence modules that use rootkit techniques mean that RATs are very difficult to get rid of. Sometimes, the only solution to rid your computer of a RAT is to wipe out all of your software and reinstall the operating system.
RAT prevention systems are rare because the RAT software can only be identified once it is operating on your system. The best way to manage the RAT problem is to use an intrusion detection system. Comparitech has a guide on intrusion detection systems, which gives you a full explanation of how these systems work and a rundown of recommended tools.
The best intrusion detection tools for RAT software, scanners & detection tools
Features Comparison Table
| Product/Features | SolarWinds Security Event Manager | Snort | OSSEC | Zeek | Suricata | Sagan | Security Onion | AIDE | OpenWIPS-NG | Samhain | Fail2ban |
|---|---|---|---|---|---|---|---|---|---|---|---|
| Network-Based IDS | Yes | Yes | No | Yes | Yes | Yes | Yes | No | Yes | No | No |
| Host-Based IDS | No | No | Yes | No | No | No | No | Yes | No | Yes | Yes |
| Real-Time Monitoring | Yes | Yes | Yes | Yes | Yes | Yes | Yes | No | Yes | Yes | Yes |
| Signature-Based Detection | Yes | Yes | Yes | No | Yes | Yes | Yes | No | Yes | Yes | No |
| Anomaly-Based Detection | Yes | No | Yes | Yes | Yes | No | Yes | Yes | No | Yes | No |
| Open Source | No | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Yes |
| Integration with Other Systems | Yes | Yes | Yes | Yes | Yes | Yes | Yes | No | No | No | Yes |
| Customizable Rules | Yes | Yes | Yes | Yes | Yes | Yes | Yes | No | No | No | Yes |
| Support and Community | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Yes |
1. SolarWinds Security Event Manager
Best for: Large organizations
Price: Starts at $3,292
Tested on: Windows Server, Cloud/SaaS (Hypervisor, AWS and MS Azure)

Intrusion detection systems are important tools for blocking software intrusion that can evade detection by antivirus software and firewall utilities. The SolarWinds Security Event Manager is a Host-based Intrusion Detection System. However, there is a section of the tool that works as a Network-based Intrusion Detection System. This is the Snort Log Analyzer. You can read more about Snort below, however, you should know here that it is a widely used packet sniffer. By employing Snort as a data collector to feed into the Snort Log Analyzer, you get both real-time and historic data analysis out of the Security Event Manager.
SolarWinds Security Event Manager’s key features
This is an on-premises software package and its most important features are:
- Log Management: Collects, categorizes, and reformats log messages.
- Log File Searches for Intrusion: SEM offers log file searches to detect and investigate intrusions or security incidents within the network.
- Live Data Monitoring for Anomalies: The tool provides live data-monitoring capabilities to identify anomalies and suspicious activities in real-time.
- Automated Remediation: SEM includes automated remediation features to respond to security threats and incidents automatically.
- Compliance: It is compliant with industry standards such as PCI DSS, HIPAA, and SOX, ensuring adherence to regulatory requirements.
Unique buying proposition
This package has the ability to process a large volume of log messages, converting them into a standard format. The conversion process, which is known as “consolidation,” enables logs from different sources, written in different formats, to be pooled for searching and storage.
Feature-in-focus: SolarWinds Security Event Manager’s forensic analysis
The Security Event Manager performs rapid analysis of log messages, looking for the common signs of a threat. The tool isn’t limited to looking for attacks coming from external locations, so it will be able to spot the activity of a RAT that is operating within the network. System activity records will show the communication between the RAT within the system and a controller or user accessing that software from outside the network.
Comparitech SupportScore
SolarWinds is a large organization with 2,000 employees. This is a good factor for our SupportScore formula, which favors large, stable, financially successful enterprises. The employee job satisfaction rating of the company is not so hot and brings down the total score.
Both the human Customer Support team and the pre-written digital documents, guidance, and help screens provided by SolarWinds get top marks. Thus, the SupportScore of SolarWinds is 8.9 out of 10.
Why do we recommend it?
SolarWinds Security Event Manager identifies suspicious activity whether it is human driven or software based. Like all forms of malware, RATs need to be spotted quickly and removed. This tool offers good value for money because it identifies and removes a range of threats, not just RATs.
This dual capability gives you a full Security Information and Event Management (SIEM) service. This means that you can watch Snort-captured events live and also examine cross-packet intrusion signatures identified through log file records.

The Security Event Manager goes beyond RAT detection because it includes automated remediation tasks that help you block RAT activities. The tool is compliant with a range of data security standards, including PCI DSS, HIPAA, SOX, and DISA STIG.
Who is it recommended for?
Although businesses of all sizes need cybersecurity protection, The SolarWinds Security Event Manager is aimed more at large enterprises. This is because it is a large software package that needs to be installed and maintained. Its pricing structure is also more interesting for large businesses that for small companies.
Pros:
- Targeted Threat Detection: SEM is designed specifically to detect and stop RATs, malware, worms, insider threats, and other security risks promptly.
- Integration with Tools like Snort: It supports integration with tools like Snort, allowing SEM to be part of a comprehensive security strategy leveraging multiple technologies.
- Pre-Configured Alerts and Rules: With over 700 pre-configured alerts, correlation rules, and detection templates, SEM provides instant insights and threat detection capabilities upon installation.
- Intelligent Threat Response: The tool offers easy-to-build threat response rules and uses intelligent reporting to reduce false positives, enhancing accuracy in threat detection and response.
- Built-In Reporting: SEM includes built-in reporting and dashboard features, reducing the need for multiple cybersecurity tools and providing centralized visibility into security posture.
Cons:
- Feature Density: Due to its feature-rich nature, SEM may require time and effort to fully explore and utilize all its capabilities effectively.

The SolarWinds Security Event Manager can be installed on Windows Server. The utility isn’t free to use, but you can get it on a 30-day free trial.
EDITOR'S CHOICE
SolarWinds Security Event Manager (SEM) is our top pick for a RAT detection system because it is a comprehensive event monitoring and analysis package that can spot both manual and automated anomalous behavior. When utilized for detecting Remote Access Trojans (RATs), SEM proves to be a valuable tool, particularly in environments where proactive, real-time detection is critical. SEM’s strength lies in its ability to centralize and correlate logs from various sources, allowing it to detect suspicious activity indicative of RATs. It can analyze event data from endpoints, firewalls, and other network devices, applying predefined and custom correlation rules. This provides visibility into unusual behaviors, such as unexpected remote logins, file transfers, or abnormal outbound traffic, which are common RAT indicators. The platform’s real-time alerting feature is key for RAT detection, allowing security teams to quickly respond to potential threats. SEM’s customizable dashboards provide clear, actionable insights, making it easier to track and respond to suspicious activity. The system’s automated responses, such as blocking IP addresses or isolating compromised devices, help mitigate the impact of RAT infections. SolarWinds SEM is a solid choice for organizations seeking to improve their RAT detection capabilities and overall network security posture.
OS: Windows Server
2. Snort
Best for: Skilled security technicians.
Price: Free; pay for packs of detection rules.

Snort is free to use and it is the industry leader in NIDS, which is a Network Intrusion Detection System.
Snort’s key features
Snort’s most important features are:
- Signature-Based Detection: Snort uses signature-based detection to identify known threats by comparing network traffic against a database of predefined signatures.
- Anomaly-Based Detection: Additionally, Snort can detect anomalies in network traffic by analyzing deviations from normal patterns.
- Packet Sniffer: It includes packet sniffing capabilities, allowing it to capture and analyze network packets in real-time for security analysis.
- Intrusion Detection Mode: Snort operates in intrusion detection mode, where it detects and alerts users about potential intrusions or security breaches within the network.
Unique buying proposition
Snort is a command line tool that was written for Unix but is also available for Linux and Windows. The lack of a decent graphical user interface makes Snort difficult to use and more suited to technicians. However, it is possible to feed Snort output into other tools for better presentation and further analysis.
Feature-in-focus: Snort’s intrusion prevention system (IPS)
Snort specializes in network activity scanning for threat detection, which makes it a network intrusion detection system (NIDS). However, the tool goes one step further and allows playbooks to be set up to define steps for automated responses. That makes the tool an intrusion prevention system (IPS).
Comparitech SupportScore
Snort is a free tool but it is owned by Cisco Systems. Our SupportScore formula examibes the producer rather than the product and divisions are regarded as sharing the SupportScoree of their parent companies. So, here we use the SupportScore calculated for Cisco Systems.
Cisco is one of the largest companies in the world. It has a large number of staff and is financially successful. These factors score well in the SupportScore results, which arrives at 9.6 out of 10.
Why do we recommend it?
Snort is both an open source system and a property of Cisco Systems. This combination creates a sweet spot that means you are getting a very widely-used network traffic analyzer that is supported by the world’s leading network device producer.
This system was created by Cisco Systems and it can be installed on Windows, Linux, and Unix. Snort can implement defense strategies, which makes it an intrusion prevention system. It has three modes:
- Sniffer mode – a live packet sniffer
- Packet logger – records data packets to a file
- Intrusion detection mode – includes an analysis module
The IDS mode of Snort applies “base policies” to the data. These are alert rules that provide intrusion detection. Policies can be acquired for free from the Snort website, sourced from the user community, or you can write your own. Suspicious events that Snort can highlight include stealth port scanning, buffer overflow attacks, CGI attacks, SMB probes, and OS fingerprinting. Snort is capable of both signature-based detection methods and anomaly-based systems.
The front-end of Snort isn’t very good and most users interface data from Snort to better consoles and analysis tools, such as Snorby, BASE, Squil, and Anaval.

Who is it recommended for?
Snort is a sophisticated tool for network specialists – it isn’t an out-of-the-box package. For this reason, although it is free to use, it isn’t a solution that small businesses that don’t have technicians on staff could use.
Snort is difficult to set up and requires training to use. So, it isn’t a tool for occasional use. Therefore, you would need to have strong technical skills and network administration or cybersecurity training before considering using this tool. The output is difficult to interpret but those with light programming skills can learn the Snort configuration language and forward results to a separate tool for data analysis.
Pros:
- Free and Open Source: Snort is completely free and open-source, allowing users to access its source code, customize rules, and contribute to the community’s rule sets and configurations.
- Widely Used and Supported: Snort is one of the most widely used IDS globally, with a large user base and extensive community support.
- Active Community: The active and vibrant Snort community provides resources, documentation, and support forums for users to seek assistance and share knowledge.
- Data Analysis: The tool provides data analysis features, enabling users to examine network traffic patterns, anomalies, and potential threats.
Cons:
- Complex Configuration: Snort’s extensive configuration options and rule syntax can be complex for novice users, requiring a learning curve to effectively deploy and manage.
- Learning Curve: Compared to products with dedicated support and extensive documentation, Snort may have a steeper learning curve, requiring users to invest time in learning its configuration and usage.
3. OSSEC
Best for: Scanning and interpreting log messages.
Price: OSSEC = Free; OSSEC+ = Free; Atomic OSSEC = $55 per endpoint per year.

OSSEC stands for Open Source HIDS Security. A HIDS is a Host Intrusion Detection System, which examines events on the computers in a network rather than trying to spot anomalies in the network traffic, which is what network intrusion detection systems do. OSSEC is the current HIDS leader and it can be installed on Unix, Linux, and macOS operating systems. Although it can’t run on Windows computers it can accept data from them. OSSEC examines event logs to look for RAT activities. This software is an open-source project.
OSSEC’s Security Event Manager’s key features
When we tested OSSEC we found the following key features:
- Log-Based Intrusion Detection (LIDs): Actively monitors and analyzes data from multiple log data points in real-time, allowing for the detection of security incidents and potential threats.
- Rootkit and Malware Detection: Conducts process and file-level analysis to detect malicious applications and rootkits, providing comprehensive protection against malware-based attacks.
- Adaptable Detection Rules: It offers adaptable detection rules, allowing users to customize and configure rulesets based on their specific security requirements and environments.
Unique buying proposition
OSSEC has been around for a long time and has been a well-supported project, so it is reliable and bug-free. The tool was created in 2004 and was adopted by a company called Third Brigade in 2008. That business was taken over by Trend Micro, who assumed responsibility for managing the project in 2009. That cybersecurity enterprise guided development until relinquishing control in 2018, so the tool has a long period of development under one of the leading cybersecurity firms.
Feature-in-focus: OSSEC’s OSSEC+
Atomicorp offers OSSEC+ for free. This is an enhancement of OSSEC with extra features, such as a GUI interface and Machine Learning for threat detection. The actual data processing mechanism within OSSEC+ is still the open source OSSEC. Confusing matters, Atomicorp offers another proprietary enhanced edition called Atomic OSSEC, which is not free to use.
Comparitech SupportScore
Assessing the support profile of OSSEC is difficult because there are actually three OSSECs. The original OSSEC is a community project that receives funds from Atomicorp but is kept separate; its developers and managers are unpaid volunteers. So, there isn’t a budget for user assistance with the OSSEC tool. OSSEC+ and Atomic OSSEC provide a different story. Those products are full supported.
This SupportScore assessment is only about the open source OSSEC – a tool that doesn’t make any money and doesn’t have a dedicated team working on it. The SupportScore for OSSEC is 3.6 out of 10. We didn’t assess Atomicorp.
Why do we recommend it?
Like Snort, OSSEC is a free, open source project that has been supported by a major corporation – Trend Micro in this case. Trend Micro is a leading anti-malware provider and OSSEC tried in well with that business’s strengths because it examines events on endpoints. Today, the project is run by Atomicorp, which produces its own paid-for version of OSSEC while still making the open source edition free to use.
This is a data-gathering tool, which doesn’t have a very user-friendly front-end. Generally, the front end for this system is supplied by other tools, such as Splunk, Kibana, or Graylog. The detection engine of OSSEC is based on policies, which are alert conditions that might arise in the data. You can acquire pre-written packages of policies from other OSSEC users who make their packages available for free on the OSSEC user community forum. You can also write your own policies.

Who is it recommended for?
Also like Snort, OSSEC is a tool for use by specialists. You need to be able to understand how cybersecurity tools work in order to get this package working effectively to identify threats and remove them automatically.
Administrators should assess their skills before choosing an OSSEC version. The open source OSSEC is difficult to use and doesn’t have a GUI. For those who just want to use OSSEC without in-depth training, OSSEC+ or Atomic OSSEC would be better. The core OSSEC will particularly interest those with programming skills because the package can be customized.
Pros:
- Free to Use: OSSEC is freely available for use, making it accessible to a wide range of users and organizations without the need for costly licensing fees.
- Cross-Platform Compatibility: OSSEC can be deployed on various operating systems, including Linux, Unix, and Mac, providing versatility and compatibility across different environments.
- Combination SIEM and HIDS: It can function as both a SIEM system and a HIDS, offering comprehensive security monitoring capabilities.
Cons:
- Dependency on Secondary Tools: OSSEC may require additional tools like Graylog and Kibana for in-depth analysis and visualization of security data, adding complexity to the setup and management process.
- Lack of Paid Support for Open-Source Version: The open-source version of OSSEC does not include paid support, which may be a limitation for organizations requiring dedicated technical support and assistance.
Get started with the installation using a shell script.
4. Zeek
Tested on: Unix, Linux, and MacOS
Best for: Scanning network traffic for threats.
Price: Free

Zeek is a very well-established network-based intrusion detection system. This free tool is better known by its old name: Bro. The tool changed its name to Zeek in 2018. Zeek is an open-source project that is supported financially by some very big names, including the Mozilla Foundation and the International Computer Science Institute.
Zeek’s key features
Zeek is highly respected by network administrators and security professionals. Its best features are:
- Application Layer Detection: Zeek specializes in application layer detection, providing insights into network traffic at a granular level.
- Anomaly-Driven and Signature-Based Searches: It employs both anomaly-driven and signature-based searches to detect known and unknown threats within network traffic.
- Advanced Threat Detection: The tool utilizes signature detection and anomalous behavior scanning techniques, enabling it to detect a wide range of threats.
Unique buying proposition
Zeek is a command line tool without a GUI app. The system was one of the first intrusion detection systems in the world. Specifically, it is a network intrusion detection system. The system is relatively easy to use but it is probably better to set up the tool to send output to a third-party tool for display and analysis.
Feature-in-focus: Zeek’s deployment options
Zeek is a software package that can be installed on Linux, Unix, or macOS. The source code is available and some have managed to compile the system to run it on Windows. The tool is often run in Docker. It can also be installed on a cloud virtual server, such as on an account from AWS or Azure.
Comparitech SupportScore
Zeek doesn’t have a corporate sponsor or a paid version. Instead, the founders of Zeek started up a consultancy to provide funds. That business is called Corelight, which advises clients on the selection, installation, and management of cybersecurity systems. So, Zeek makes a loss, which doesn’t score well in our SupportScore formula.
The project runs a Customer Support team and there is plenty of documentation and training options available. It is in the customer support and documentation categories that Zeek gets most of its SupportScore points. The overall SupportScore of Zeek is 4.2 out of 10.
Why do we recommend it?
Zeek is an excellent alternative to Snort. While not quite as highly respected as Snort, this tool is a close competitor. The Zeek system is easier to set up than Snort but it performs a competent scan of network traffic, looking for chains of activity that indicate malicious actions. The service will also identify manual intrusion.
Despite being a network-based system, Zeek doesn’t operate on live data. This is because packet analysis doesn’t spot many types of attacks that are implemented in stages, across packets, and from different sources. So, Zeek captures data packets and then stores them in files. This makes it an application-level NIDS.
The packet files are analyzed by the Zeek Event Engine. This is a semantic analyzer that looks for unusual patterns that break out of standard activity behavior. The detection techniques used by the analyzer are therefore anomaly-based. However, the analyzer also does a sweep for well-known malicious intruder behavior, so it deploys signature-based analysis as well.
Zeek runs on Unix, Linux, and MacOS. The system includes a scripting language that enables technicians to write their own capture routines and anomaly scans. This technical aspect might put many people off using the system. However, the monitor has a large following, so there is a big user community out there to advise newbies. A big problem with Zeek is that it doesn’t have its own front end, so it needs to be paired up with other interfaces. Kibana is probably the most regularly used interface for Zeek.

Who is it recommended for?
Zeek is a little easier to operate and understand than Snort because it applies automated searches on traffic that you can just treat as a black box. Nevertheless, the need to pair this system with a third-party front end means there is a learning curve involved just to get the system running. If you can hire a technician to set the service up for you, you would be able to operate Zeek without technical skills.
Pros:
- Free to Use: Zeek is freely available for use, making it accessible to security professionals and organizations without the need for expensive licensing fees.
- High Customizability: Zeek is highly customizable, catering to the needs of security professionals operating on Unix-based operating systems.
- Scripting Automation: Zeek supports automation through scripting, empowering administrators to automate various actions and responses based on detected threats or network events.
Cons:
- Limited Platform Support: Zeek is primarily available for Unix, Linux, and Mac platforms, limiting its compatibility with Windows-based environments.
- Specialized Usage: Due to its complexity and focus on advanced threat detection, Zeek is better suited for researchers, specialists, and security professionals who require in-depth network traffic analysis capabilities.
5. Suricata
Best for: Detecting intruder activity.
Price: Free

Suricata is a NIDS that can be installed on Windows, Linux, Mac OS, and Unix. This is a fee-based system that applies application layer analysis, so it will detect signatures that are spread across data packets. Suricata monitors IP, TLS, TCP, and UDP protocol activity and focuses on key network applications, such as FTP, HTTP, ICMP, and SMB. It can also examine TLS certificates and focus on HTTP requests and DNS calls. There is also a file extraction facility that enables the analysis of virus-infected files.
Suricata’s key features
Suricata is a command line system, written for Linux. Its important features are:
- Application Layer Analysis: Suricata specializes in application layer analysis, providing detailed visibility into the behavior of RATs and other network threats.
- Compatibility with Other Tools: Send data to SIEMs or to data visualization packages.
- Analyzes Network Traffic: Suricata thoroughly analyzes network traffic, including multiple protocols, to detect and respond to potential security threats.
Unique buying proposition
Suricata offers the opportunity to block intruders, not just identify them. The package works off a series of rules that not only detect threats but stop them. That remediation function is optional and users can instead choose to get the system to notify them of potential threats so that they can be assessed manually.
Feature-in-focus: Suricata’s Lua scripting option
Suricata has a ruleset definition syntax and an output format notation system based on JSON but these are not programmable languages, so the development team created a channel that enables Lua scripts to be run within the environment, directing and influencing actions, such as data analysis and file routing.
Comparitech SupportScore
Suricata is managed by the Open Information Security Forum and this is where we look in order to assess the SupportScore for the tool. The Suricata developers will support some aspects of the tool – these are called Tier 1 and Tier 2 supported items. The organization regards support requests as Beta testing, so it will adjust the code if a user discovers a problem. However, all of the stable code is not supported by the organization – users have to tuen to the user community for help.
There are a number of third-party consultancies that provide support for Suricata on contracts. However, in general, the users of this free tool get no support. Extensive online help and guides go a long way to make up for this absence and Suricata also offers training courses and conferences to explain how the system works. The overall SupportScore for Suricata is 3.7 out of 10.
Why do we recommend it?
Suricata is another free network traffic analyzer that implements system defense. The package runs on-premises and it can monitor internet traffic to and from cloud services as well as LAN activity. Suricata is able to block the malicious activities that it spots.

Suricata has a built-in scripting module that enables you to combine rules and get a more precise detection profile. This IDS uses both signature-based and anomaly-based detection methods. VRT rules files written for Snort can also be imported into Suricata because this intrusion detection system is compatible with the Snort platform. This also means that Snorby, BASE, Squil, and Anaval can serve as front ends to Suricata. However, the Suricata GUI is very sophisticated and includes graphical representations of data, so you might not need to use any other tool to view and analyze data.
Who is it recommended for?
Anyone can use Suricata. The system is easy to set up and use because it has a very good user interface and runs on all of the major operating systems. As Suricata is free to use, it is suitable for businesses of any size. The frontend isn’t the best you can get and if you have technical skills, you can feed data into other analysis tools. The Suricata system also includes a scripting language, which enables those who have technical skills to really expand the intrusion prevention features in this tool.
Pros:
- Application Layer Visibility: Suricata’s ability to collect data at the application layers provides unique visibility into the behavior of RATs and other malicious activities.
- Efficient Packet Reassembly: It efficiently analyzes and reassembles protocol packets, ensuring accurate analysis and detection of security incidents.
- Multi-Protocol Monitoring: Suricata can monitor multiple protocols and check the integrity of certificates in protocols like TLS, HTTP, and SSL, enhancing its coverage and threat detection capabilities.
Cons:
- Scripting Complexity: Users may find the built-in scripting capabilities of Suricata somewhat challenging to use, requiring a learning curve to leverage scripting for customizations and automation.
- Visualizations on Dashboard: Some users may find that Suricata could improve its live dashboard visualizations for better data representation and analysis.
6. Sagan
Best for: Log analysis.
Price: Free

Sagan is a free host-based intrusion detection system that can be installed on Unix, Linux, and Mac OS. You can’t run Sagan on Windows but you can feed Windows event logs into it. Data gathered by Snort, Suricata, or Bro can be imported into Sagan, which gives the data analytical tool of this utility a NIDS perspective as well as its native HIDS capabilities. Sagan is also compatible with other Snort-type systems, such as Snorby, BASE, Squil, and Anaval, which could all provide a front end for data analysis.
Sagan’s key features
Sagan was first created in 2010; its best features are:
- Geographic Location Tracking: Tracks events based on IP address source or destination data to identify anomalies in geographic locations.
- Threat Intelligence Integration: Queries custom blacklists, Bro Intel subscriptions, and Quadrant Information Security threat intelligence feeds.
- Alert Fatigue Reduction: Implements thresholds to reduce alert fatigue, alerting only after specific criteria have been met.
Unique buying proposition
Sagan has many functions that make it a good host-based intrusion detection system. Sagan is also able to analyze data collected by network-based intrusion detection systems. A NIDS collects traffic data through a packet sniffer. Sagan doesn’t have a packet sniffer, but it can read in traffic data collected by Snort, Bro, and Suricata — all of which are free to use. So you get a blend of both HIDS and NIDS security activities with Sagan.
Feature-in-focus: Sagan’s intrusion prevention system
The tool includes features that make it an intrusion prevention system (IPS). Once Sagan detects anomalous behavior, it can write to your firewall tables to ban specific IP addresses from the network either permanently or temporarily. This is a great assistant for network security because it implements IP bans automatically and keeps the system available for genuine users.
Comparitech SupportScore
Calculating the SupportScore for Sagan is difficult because this calculation relates to the company rather than its products. In 2011, the creator of Sagan founded Quadrant Information Security to manage the product but over the years, the business has transformed the tool into a commercial product suite, leaving the original open source tool still available for free on GitHub. The support treatment of the free and paid systems is completely different.
Open source Sagan gets no support at all and both assistance and documentation come from the user community. The paid suite of tools is fully underpinned by a professional Customer Support team. The SupportScore for Quadrant is 6.1 out of 10 but this relates to the support for the paid tools. The SupportScore for just the open source software would be much lower.
Why do we recommend it?
Sagan is a free log analysis tool that is good for malware and intrusion detection. This service can also centralize data gathered from many of the other tools on this list. Look upon Sagan as a free alternative to SolarWinds Security Event Manager.

Sagan is a log analysis tool and it needs to be used in conjunction with other data gathering systems in order to create a full intrusion detection system. The utility includes an IP locator, so you can trace the sources of suspicious activities to a location. It can also group together the activities of suspicious IP addresses to identify team or distributed attacks. The analysis module works with both signature and anomaly detection methodologies.
Sagan can automatically execute scripts to lock down the network when it detects specific events. It performs these prevention tasks through interaction with firewall tables. So, this is an intrusion prevention system.
Who is it recommended for?
If you have the money and you want to install a SIEM tool to spot RATs, you should really go for the SolarWinds tool. However, if you don’t want to pay anything and you are prepared to put in a little work, you should consider using Sagan. Creating rules to automatically shut down threats takes a bit of learning, but you will save a lot of money for the time that you invest.
Pros:
- Free Log Analysis Tool: Sagan is available as a free log analysis tool, making it accessible to organizations without additional costs.
- Compatibility with Open-Source Tools: It is compatible with other open-source tools like Zeek and Snort, allowing for integration and enhanced threat detection capabilities.
- Automated Threat Remediation: Sagan offers automated remediation of threats, helping to mitigate security risks and respond to incidents more efficiently.
Cons:
- Not Available for Windows: Sagan is not available for Windows operating systems, limiting its deployment options for organizations that primarily use Windows environments.
- Not a Standalone RAT Solution: While Sagan offers automated remediation, it is not a standalone solution specifically focused on RAT removal or prevention.
- Steep Learning Curve: New users may experience a steep learning curve when using Sagan, as it requires familiarity with log analysis concepts and configurations.
7. Security Onion
Best for: A bespoke SOC software suite.
Price: Free

Security Onion was developed by splicing together the code for Snort, Suricata, OSSEC, Bro, Snorby, Sguil, Squert, Kibana, ELSA, Xplico, and NetworkMiner, which are all open-source projects. This powerful tool is a free Linux-based NIDS that includes HIDS functionality. It was written to run specifically on Ubuntu.
Security Onion’s key features
This on-premises package is open source and free to use. Its best features are:
- Intrusion Detection: Incorporates intrusion detection capabilities to identify and alert on potential security threats within the network.
- Honeypots: Includes intrusion detection honeypots, which are decoy systems designed to lure attackers and gather information about their tactics and techniques.
- Log Management: Facilitates the collection, storage, and analysis of log data from various sources, aiding in the detection and investigation of security incidents.
Unique buying proposition
Security Onion provides a range of security services in one console. The package is enough for an entire Security Operations Center because it operates log collection and a SIEM as well as an intrusion detection system / intrusion prevention system. The package implements both host-based and network intrusion detection methods.
Feature-in-focus: Security Onion’s automated responses
Security Onion applies detection rules to identify potential threats. These can be extended to implement actions automatically to block sattacks. This strategy is implemented through a scripting language and SOAR connections to other security tools. Although these methods are powerful and flexible, they require in-depth technical knowledge to implement.
Comparitech SupportScore
Security Onion is the name of a company as well as a tool. The Security Onion business the open source Security Onion and has also developed a paid tool, called Security Onion Pro. The paid system is fully underpinned by a professional Customer Support team, while users of the open source option have to rely on community support.
Our SupportScore formula relates to the company and not its products. Therefore, it accounts for support for the paid tool as well as for the open source system. The SupportScore for Security Onion is 4.5 out of 10.
Why do we recommend it?
Security Onion was created to address the problem that we have flagged a number of times in the reviews above. The problem is that all of the systems on this list would work a little better if they are combined into a suite. Security Onion links together the best free intrusion detection systems so you don’t have to learn how best to fit these utilities together into an impressive intrusion prevention system to block RATs and other malicious activities.
Host-based analysis checks for file changes and network analysis is conducted by a packet sniffer, which can display passing data on a screen and also write to a file. The analysis engine of Security Onion is complicated because it combines the procedures of so many different tools. It includes device status monitoring as well as network traffic analysis.
There are both signature-based and anomaly-based alert rules included in this system. The interface of Kibana provides the dashboard for Security Onion and it includes graphs and charts to ease data analysis.

Who is it recommended for?
As it involves so many packages, Security Onion takes time to download and install. However, the setup process is guided and that makes this tool easy to use by anyone. The one problem that some businesses will face is that Security Onion only runs on Ubuntu Linux. So, if your enterprise only has Windows PCs, you will have to convert one of them to Linux to use security Onion.
Pros:
- Free and Open-Source: Being free and open-source, Security Onion provides cost-effective security monitoring and analysis capabilities.
- Network Visibility: Provides comprehensive visibility into network traffic, allowing for the monitoring and analysis of network activities.
- Host Visibility: Offers insight into host activities, enabling the detection and investigation of suspicious behavior on individual devices.
Cons:
- Availability Only for Linux: Security Onion is available only for Linux operating systems, which may limit its deployment options for organizations that primarily use other operating systems.
- Visualization through Kibana: It uses Kibana for visualization, which may require additional configuration and setup for customized visualizations.
- Complex Interface: The interface of Security Onion is considered fairly complicated, and some users may find it challenging to navigate or use.
8. AIDE
Tested on: Linux
Best for: File protection
Price: Free

AIDE stands for “Advanced Intrusion Detection Environment.” This is a free HIDS that runs on Mac OS, Unix, and Linux. This IDS focuses on rootkit detection and file signature comparisons.
AIDE’s key features
This tool was first created in 1999. Its most significant features are:
- Log Monitoring: AIDE monitors logs from various network systems and devices, analyzing entries for signs of unauthorized access, unusual behavior, or security incidents.
- File Integrity Monitoring (FIM): Tracks changes to critical system files and directories, alerting administrators to unauthorized modifications and potential security compromises.
- Intrusion Detection: Combines signature-based and anomaly-based techniques to identify known attack patterns and detect unusual activities, such as port scans or malware, indicating potential threats.
Unique buying proposition
AIDE is a long-running free tool. Those two attributes explain the appeal of the tool. It’s longevity shows that it works successfully and has been bug tested extensively through frequent use. The fact that the tool is free to use is very appealing for cash-strapped stratups and small businesses.
Feature-in-focus: AIUE’s file integrity monitor
This system scans an endpoint and discovers all files. The tool then calculates a checksum for each of those files. All of this data is stored in a database and then files are rechecked for changes. This is a very early file integrity monitor. The software was written for Unix and will also run on Linux and macOS.
Comparitech SupportScore
AIDE offers very few details on how to use the tool. It is explained in a single page on GitHub.io and gives the name of the current developer. So, the tool doesn’t get points for corporate structure, staff, system documentation, or a support team. AIDE gets a SupportScore of 0.5 out of 10.
Why do we recommend it?
As it is a free, open-source host-based intrusion detection system, AIDE competes with OSSEC, Suricata, and Samhain. This is worth a try. However, its command-line interface makes the AIDE utility difficult to use. If you have the time and the skills, you can forward AIDE data files and display them in another tool.

The data gathering module populates a database of characteristics that are gleaned from log files. This database is a system status snapshot and any changes in device configuration trigger alerts. Those changes can be canceled by reference to the database or the database can be updated to reflect authorized configuration alterations.
System activity checks are performed on-demand and not continuously, but it can be scheduled as a cron job. The rules base of AIDE uses both signature-based and anomaly-based monitoring methods.
Who is it recommended for?
AIDE isn’t available for Windows, so if you only have PCs, you won’t be able to use this tool. This is a system that will appeal to technical experts who like to tinker.
Pros:
- Free and Open-Source: Being free and open-source, AIDE provides cost-effective intrusion detection capabilities for security professionals and organizations.
- Lightweight Deployment: Its lightweight nature allows it to run efficiently in legacy environments, making it suitable for detecting RATs and other threats in such environments.
- SIEM Integration: Integrates with SIEM systems to centralize and correlate security events from multiple sources, enhancing visibility and analysis capabilities.
Cons:
- Availability Only for Linux and Unix: AIDE is available only for Linux and Unix operating systems, which may limit its deployment options for organizations that primarily use other operating systems.
- Not Beginner-Friendly: AIDE may not be as beginner-friendly as some other security tools, requiring a certain level of technical expertise and familiarity with command-line interfaces for effective usage.
9. OpenWIPS-NG
Best for: Scanning wireless networks.
Price: Free

OpenWIPS-NG comes from the developers of Aircrack-NG. In fact, it integrates Aircrack-NG as its wireless packet sniffer. Aircrack-NG is a well-known hacker tool, so this association may make you a little wary. WIPS stands for “Wireless Intrusion Prevention System” and it runs on Linux.
OpenWIPS-NG’s key features
This tool was first released in 2012. Its main features are:
- Sensors: “Dumb” devices that capture wireless traffic and send it to the server for analysis.
- Server: Aggregates data from all sensors, conducts thorough analysis, and initiates responses to detected attacks.
- Interface: Provides a user-friendly GUI for managing the server and displaying comprehensive information about threats on the wireless network(s).
Unique buying proposition
OpenWIPS-NG is fairly unique. It both sniffs packets and transmits them. This enables the tool to be an intrusion prevention system because it is able to send instructions to block a suspicious user. The tool can also be used by hackers.
Feature-in-focus: OpenWIPS-NG’s response automation
OpenWIPS-NG automates wireless threat responses by detecting attacks like rogue APs, deauth floods, or MAC spoofing and executing countermeasures such as jamming, deauthentication, or MAC blocking. Its server-driven architecture supports custom scripts, enabling real-time mitigation and integration with broader security systems for fast, hands-off wireless intrusion prevention.
Comparitech SupportScore
OpenWIPS-NG is not very user friendly and, as it is a free tool, does not generate an income for its creators. There is no budget for corporate functions and the managers of the open-source project haven’t created a professional user support team. There is very little system documentation available.
OpenWIPS-NG scores zero in many of the points categories of our formula. Thus, the tool gets a SupportScore of 0.5 out of 10.
Why do we recommend it?
OpenWIPS-NG is unique on this list because it operates on wireless networks. It can be used to extract packets and analyze them and also to inject traffic back into the wireless networks. A great feature of this tool is that it is free to use. However, don’t think that it will be able to crack transmission encryption, so you won’t be able to spy on WiFi users.

OpenWIPS-NG is a free utility that includes three elements:
- Sensor – the packet sniffer
- Server – data storage and analysis rule-base
- Interface – user-facing front end.
The sensor is also a transmitter, so it can implement intrusion prevention actions and cripple unwanted transmissions. The server performs analysis and also launches intervention policies to block detected intrusions. The interface module displays events and alerts to the systems administrator. This is also where settings can be tweaked and defensive actions can be adjusted or overridden.
Who is it recommended for?
Like its stablemate, Aircrack-NG, OpenWIPS-NG is good for hackers. However, the ability to respond to detected malicious activities makes it very useful. You would need to be a competent network engineer to use this tool.
Pros:
- Flexibility: Its flexibility allows security specialists to customize and tailor it to specific security needs and network environments.
- Lightweight CLI: The command-line interface is efficient and does not require heavy system resources, making it suitable for various devices and environments.
- Memorizable Syntax: The syntax is straightforward and easy to remember, reducing the learning curve for users.
Cons:
- Reliance on Other Tools: It relies on other tools to expand its functionality, which may require additional configurations or integrations.
- Not an All-in-One Solution: While powerful for WiFi network security, OpenWIPS-NG may not be ideal for users looking for a comprehensive, all-in-one security solution that includes other network security aspects.
10. Samhain
Best for: Detecting and killing rogue processes.
Price: Free

Samhain, produced by Samhain Design Labs in Germany, is a free host-based intrusion detection system that installs on Unix, Linux, and Mac OS. It uses agents running at different points on the network, which report back to a central analysis module. Each agent performs file integrity checking, log file monitoring, and port monitoring. The processes look for rootkit viruses, rogue SUIDs (user access rights), and hidden processes.
Samhain’s key features
This is a common line tool that can feed data through to the interface of your choice. Its important features are:
- Security: Baseline databases and configurations are stored securely on the server, preventing tampering by local intruders.
- Log Facilities: Offers a wide range of logging facilities including email, syslog, signed and tamper-resistant log files, SQL databases.
- Monitoring User Access Rights: Samhain can monitor user access rights to detect privilege escalation, which is a common behavior associated with RATs.
Unique buying proposition
Samhain provides a package of data processing services that can feed analysis through to other tools or be integrated into custom-built cybersecurity tools. The service doesn’t have a graphical user interface and you can choose to set up one of many data console systems that are available for free, such as Kibana. Samhain Labs provides a separate interface, called Beltane, for the consideration of its Samhain users.
Feature-in-focus: Samhain’s file integrity monitor
Samhain’s file integrity monitor enhances system security by computing cryptographic checksums (e.g., SHA-256) to detect unauthorized changes in files. It implements alerts via syslog, email, or custom scripts, and offers tamper-resistant features like signed databases and stealth operation. Samhain is ideal for centralized or standalone host monitoring.
Comparitech SupportScore
Samhain Labs has no corporate structure or employees, so it doesn’t get any points from the business assessment categories in our SupportScore calculation. The tool is very old and so not easy to use and the company doesn’t maintain a Customer Support team. There is some documentation for the product and we gave it full marks for that.
The overall SupportScore for Samhain Labs is 1.5 out of 10.
Why do we recommend it?
Samhain is a host-based intrusion detection system so it competes with other HIDS on this list. It is a free, open source project and so you can alter the code if you want to. Features that no other IDS on this tool has include the ability to mask its running processors and its strong protection of log files.
Network communication between agents and the console is protected by encryption. Connections for the delivery of log file data include authentication requirements, which prevent intruders from hijacking or replacing the monitoring process.
Samhain will highlight warning signs of intrusion but it doesn’t have any resolution processes. You will need to keep backups of your configuration files and user identities in order to take action to resolve the problems that the Samhain monitor reveals. Samhain keeps its processes hidden by stealth technology, called “steganography” in order to prevent intruders from manipulating or killing the IDS. Central log files and configuration backups are signed with a PGP key to prevent tampering by intruders.

Who is it recommended for?
Samhain can be used as a log management tool and it provides a log viewer. The system is useful to have if only for those services and it would be useful for businesses of any size. This is yet another tool that won’t run on Windows.
Samhain would work best as a component of a custom-built IDS or IPS. The tool dates back to times when technicians spent all of their time at the command line and liked the fact that software was difficult to use because it gave them job security. However, these days, system administrators and network managers have too much to do and need automated, easy-to-use tools that enhance productivity.
Pros:
- Free and Open-Source: Being free and open-source, Samhain offers security monitoring capabilities without additional costs.
- Flexibility: Provides modules for comprehensive monitoring tasks including integrity checks using cryptographic checksums, detection of rogue SUID executables, and centralized monitoring.
- Detection Capabilities: It can effectively detect rogue processes, intrusions, malicious connections, and privilege escalation, enhancing overall security posture.
Cons:
- No Paid Support Options: Samhain lacks paid support options, which may limit access to dedicated technical assistance and resources.
- Not Available for Windows: It is not available for Windows operating systems, restricting its deployment to Linux and Unix-based environments.
- Outdated Interface and Usability: The interface of Samhain feels outdated and may not be particularly user-friendly.
11. Fail2Ban
Best for: Blocking access to outsiders.
Price: Free
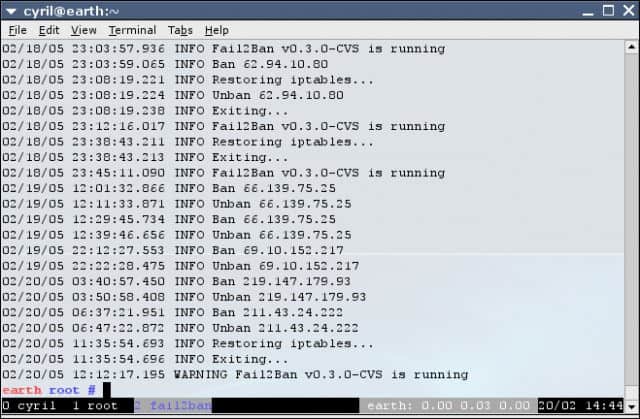
Fail2Ban is a free host-based intrusion prevention system that runs on Unix, Linux, and Mac OS X. The IDS analyses log files and imposes bans on IP addresses that display suspicious behavior. Automatic lockouts occur in Netfilter/IPtables or PF firewall rules and the hosts.deny table of TCP Wrapper. These blocks usually only last a few minutes, but that can be enough to disrupt a standard automated brute-force password-cracking scenario.
Fail2Ban’s key features
Fail2Ban was first released in 2004. Its best attributes are:
- Automatic IP Ban: Fail2Ban automatically bans attacking IP addresses, which is effective in stopping RAT Command and Control (C&C) servers.
- Combination IDS and HIDS: It acts as a combination IDS and HIDS, providing comprehensive security monitoring.
- Cybersecurity Controls: Protects against brute force attacks.
Unique buying proposition
Fail2Ban is a lightweight, real-time cybersecurity system that protects against brute-force attacks. It monitors log files and bans malicious IPs automatically. The software runs on Linux and uses regex-based filters for detecting suspicious behavior. It is able to secure SSH, web servers, and more without the complexity or cost of full-scale intrusion prevention systems.
Feature-in-focus: Fail2Ban’s detection system
Fail2Ban’s detection system monitors log files for predefined patterns of suspicious behavior, such as multiple failed login attempts. Using customizable regular expression (regex) filters, it identifies brute-force attacks and other threats in real time. Once triggered, it initiates automated actions like IP banning to mitigate potential security breaches quickly.
Comparitech SupportScore
Fail2Ban is an open source project, which has no income or corporate structure. The software is available from GitrHub and its project page includes some usage instructions. However, there are no other guides available. Neither is there a Customer Support team for Fail2Ban.
The SupportScore for Fail2Ban is 0.5 out of 10.
Why do we recommend it?
Fail2Ban is a host-based intrusion prevention system that scans application activity for suspicious activity. For example, it will set up a monitor to focus on mail servers and another to watch an Apache Web server. You set up playbooks that tell Fail2Ban what to do when it detects suspicious activity.

Alert situations include excessive failed login attempts. A problem with Fail2Ban is that it focuses on repeated actions from one address. This doesn’t give it the ability to cope with distributed password cracking campaigns or DDoS attacks.
The monitoring scope of the system is defined by a series of “filters.” These instruct the IPS on which services to monitor. These include Postfix, Apache, Courier Mail Server, Lighttpd, sshd, vsftpd, and qmail. Each filter is combined with an action to perform in the event of an alert condition being detected. The combination of a filter and an action is called a “jail.”
Who is it recommended for?
Fail2Ban runs on Unix, Linux, and macOS but not on Windows. Although there are some interesting features in this system, it operates at the command line and so small business owners and other non-technical users will struggle to get the best out of Fail2Ban. However, it is open source and free to use, so anyone can give it a try.
Pros:
- Completely Free: Fail2Ban is a completely free tool, making it accessible to users without additional costs.
- Automatic IP Blocking: Its ability to automatically ban attacking IP addresses enhances security by mitigating threats in real-time.
- Flexible Banning Durations: IP addresses can be blocked for a short time or permanently.
Cons:
- No Paid Support: Fail2Ban lacks paid support options, which may limit access to dedicated technical assistance and advanced features.
- Limited Platform Support: Fail2Ban is available for Unix, Linux, and Mac operating systems only, restricting its deployment options.
RAT programs and examples
There are a number of remote access systems that could have legitimate applications, but are well-known as tools that are mainly used by hackers as part of a Trojan; these are categorized as Remote Access Trojans. The details of the best-known RATs are explained below.
Back Orifice
Back Orifice, which is also referred to as BO is an American-made RAT that has been around since 1998. This is the granddaddy of RATs and has been refined and adapted by other hacker groups to produce newer RAT systems. The original system exploited a weakness in Windows 98. Later versions that ran on newer Windows operating systems were Back Orifice 2000 and Deep Back Orifice.
This RAT is able to hide within the operating system, which initially makes it difficult to detect. However, nowadays, most antivirus systems have the Back Orifice executable files and occlusion behavior logged in their databases as signatures to look out for. A nice feature of this software is that it has an easy-to-use console that the intruder can use to navigate around the infected system. The remote element can be slipped into a target computer through a Trojan. Once installed, this server program communicates with the client console using standard networking procedures. Back Orifice is known to use port number 21337.
Beast
The Beast RAT attacks Windows systems from Windows 95 up to Windows 10. This uses the same client-server architecture that Back Orifice pioneered with the server part of the system being the malware that gets installed surreptitiously on the target computer. Once the server element is operational, the hacker can access the victim computer at will through the client program. The client connects to the target computer at port number 6666. The server is also able to open connections back to the client and that uses port number 9999. Beast was written in 2002 and is still widely in use.
Bifrost
This Trojan begins its infection with the installation of a server builder program. Initially, this program just makes contact with a Command and Control server and waits for instructions. The Trojan infects Windows systems from Windows 95 to Windows 11. However, its capabilities are reduced on Windows versions XP and later.
Once it is triggered, the server builder will set up a server program on the target computer. This enables the hacker, using a corresponding client program to get access to the compromised machine and execute commands at will. The server software is stored in C:\Windows\Bifrost\server.exe or C:\Program Files \Bifrost\server.exe. This directory and file are hidden and so some anti-virus system checks fail to detect Bifrost.
The server builder does not end its operations once the server has been created. Instead, it operates as a persistence system and will recreate the server in a different location and with a different name if the original server installation is spotted and removed. The server builder also employs rootkit methods to mask server processes and make the operating intrusion system very difficult to detect.
Since Windows Vista, the full destructive capabilities of Bifrost have been slowed down because many of the services that the malware uses require system privileges. However, if a legitimate user is tricked into installing the disguised server builder with system privileges, the Bifrost system can become fully-operational and will be very difficult to remove.
Related: The best free rootkit removal, detection and scanner programs
Blackshades
Blackshades is an off-the-peg hacking tool that was sold to hackers by its developers for $40 a pop. The FBI estimated that its producers earned a total of $340,000 selling this software. The developers were shut down and arrested in 2012 and a second wave of arrests in 2014 captured more than 100 users of Blackshades. However, there are still copies of the Blackshades system in circulation and it is still in active use. Blackshades targets Microsoft Windows from Windows 95 to Windows 11.
The toolkit includes methods of infection, such as malicious code to embed in websites that trigger installation routines. Other elements propagate the RAT by sending out links to infected web pages. These are sent to the social media contacts of an infected user.
The malware enables a hacker to get access to the target computer’s files system and download and execute files. Uses of the program include botnet functions that get the target computer to launch denial of service attacks. The infected computer can also be used as a proxy server to route hacker traffic and provide identity cover for other hacker activities.
The Blackshades toolkit is very easy to use and enables those who lack technical skills to become hackers. The system can also be used to create ransomware attacks. A second obfuscation program sold alongside Blackshades keeps the program hidden, enables it to relaunch when killed, and evades detection by anti-virus software.
Among attacks and events that have been traced to Blackshades are a 2012 campaign of disruption that targeted Syrian opposition forces.
See also: 2017-2018 Ransomware statistics and facts
The Ransomware Removal Handbook: Dealing with common strains of ransomware
DarkComet
French hacker Jean-Pierre Lesueur developed DarkComet in 2008, but the system didn’t really proliferate until 2012. This is another hacker system that targets the Windows operating system from Windows 95 up to Windows 11. It has a very easy-to-use interface and enables those without technical skills to perform hacker attacks.
The software enables spying through keylogging, screen capture, and password harvesting. The controlling hacker can also operate the power functions of a remote computer, allowing a computer to be turned on or off remotely. The network functions of an infected computer can also be harnessed to use the computer as a proxy server to channel traffic and mask the hacker’s identity during raids on other computers.
DarkComet came to the cybersecurity community’s attention in 2012 when it was discovered that an African hacker unit was using the system to target the US government and military. At the same time, DarkComet attacks originating in Africa were launched against online gamers.
Lesueur abandoned the project in 2014 when it was discovered that DarkComet was in use by the Syrian government to spy on its citizens. The general populace had taken to employing VPNs and secure chat apps to block government surveillance, so the spyware features of DarkComet enabled the Syrian government to circumvent those security measures.
Mirage
Mirage is the key RAT used by the state-sponsored Chinese hacker group known as APT15. After a very active spying campaign from 2009 to 2015, APT15 suddenly went quiet. Mirage itself was in use by the group from 2012. The detection of a Mirage variant in 2018 signaled that the group was back in action. This new RAT, known as MirageFox was used to spy on UK government contractors and was discovered in March 2018. Mirage and MirageFox each act as an agent on the infected computer. The Trojan part of the intrusion suite polls a Command and Control address for instructions. Those instructions are then implemented on the victim computer.
The original Mirage RAT was used for attacks on an oil company in the Philippines, the Taiwanese military, a Canadian energy company, and other targets in Brazil, Israel, Nigeria, and Egypt. Mirage and MirageFox get onto target systems through spear-phishing campaigns. These are usually targeted at the executives of a victim company. The Trojan is delivered embedded in a PDF. Opening the PDF causes scripts to execute and they install the RAT. The RAT’s first action is to report back to the Command and Control system with an audit of the infected system’s capabilities. This information includes the CPU speed, memory capacity and utilization, system name and username.
The initial system report makes it seem as though the designers of Mirage made the RAT in order to steal system resources rather than access data on the target system. There is no typical Mirage attack because it seems that each intrusion is tailored towards specific targets. The RAT installation can be presaged by a fact-finding campaign and system checks. For example, the 2018 attack on British military contractor NCC gained access to the system via the company’s authorized VPN service.
The fact that each attack is highly-targeted means that a lot of expense is entailed by a Mirage infection. This high cost shows that Mirage attacks usually only aim at high-value targets that the Chinese government wishes to undermine or from which to steal technology.
Dealing with Remote Access Trojan threats
Although much RAT activity appears to be government-directed, the existence of RAT tool-kits makes network intrusion a task that anyone can perform. So, RAT and APT activities are not going to be limited to attacks on the military or high tech companies, security awareness is key to stop any security breaches of your networks.
RATs combine with other malware to keep themselves hidden, which means that installing antivirus software on your computers isn’t enough to prevent hackers from controlling your system with these methods. Investigate intrusion detection systems in order to defeat this hacker strategy.
Have you experienced a network intrusion that resulted in damage or loss of data? Have you implemented an intrusion prevention strategy to head off the RAT problem? Leave a message in the Comments section below to share your experiences.
Related Post: The Best Remote Administrator Tools
Why trust us?
The Comparitech.com team consists of experienced IT professionals, cybersecurity experts, and technology specialists with years of hands-on experience in assessing and testing IT systems. Our expertise spans a wide range of software and hardware solutions, ensuring in-depth analysis and unbiased reviews. We leverage industry best practices to deliver trustworthy, accurate insights, helping businesses and individuals make informed decisions on technology investments and cybersecurity strategies.
Our Methodology for Choosing RAT Detection Tools
At Comparitech, we apply a rigorous methodology to evaluate and select the best Remote Access Trojan (RAT) detection tools. Our process ensures that we recommend reliable, effective, and secure solutions. Here’s how we assess RAT detection tools:
1. Detection Accuracy
We assess the tool’s ability to accurately detect known and unknown RATs. This includes evaluating its detection capabilities for hidden threats, as well as its ability to identify suspicious network activity, unauthorized access, and anomalies.
2. Ease of Use
We prioritize user-friendly interfaces and straightforward setup processes. A tool with a clean, intuitive interface and easy-to-understand features ensures that IT teams can quickly implement it without requiring excessive training.
3. Performance and Impact
We test how the tool affects system performance. An ideal RAT detection tool should operate efficiently, without consuming excessive resources or causing delays in other business processes.
4. Customization and Alerts
We evaluate how customizable the tool is, particularly its alerting and notification features. Effective RAT detection tools should allow users to set specific thresholds, receive real-time alerts, and configure response actions based on various detected threats.
5. Compatibility
We consider the tool’s compatibility with multiple operating systems (Windows, macOS, Linux) and its integration with other security software or IT management platforms. This ensures the tool works seamlessly within your existing infrastructure.
6. Support and Updates
We assess the availability of regular software updates and the quality of vendor support. A reliable RAT detection tool should be regularly updated to address emerging threats and offer responsive support when needed.
7. Cost-Effectiveness
We analyze pricing models, ensuring that the tool offers good value for the features provided. We consider the cost relative to the protection and functionality the tool delivers for both small and large enterprises.
By considering these factors, we identify RAT detection tools that provide robust protection, ensuring businesses can safeguard their systems from malicious remote access threats effectively.
Broader B2B Software Selection Methodology
When selecting B2B software, a methodical approach is critical to ensuring the chosen tool meets the specific needs of the organization. At Comparitech, we follow a structured process to assess and recommend software solutions that deliver optimal value for businesses. Here’s how we approach B2B software selection:
1. Business Needs Assessment
We begin by understanding the unique needs of the business, including its goals, processes, and workflows. This helps ensure that the software aligns with business objectives and addresses specific pain points, from operational efficiency to security requirements.
2. Feature Evaluation
We thoroughly review the features of the software, focusing on its capabilities to meet the business’s needs. The software should offer relevant functionalities that improve productivity, streamline processes, and integrate smoothly with existing tools and infrastructure.
3. Scalability and Flexibility
We assess how well the software scales with the business’s growth. The chosen solution must accommodate expanding users, data, and functionalities, ensuring it remains relevant and adaptable as business requirements evolve.
4. Usability and User Experience
We evaluate how easy the software is to use for both technical and non-technical users. An intuitive user interface and seamless navigation are essential to ensure that employees can effectively adopt the tool without requiring extensive training.
5. Integration and Compatibility
We consider the software’s ability to integrate with existing systems, applications, and third-party tools. The solution should work cohesively within the business’s IT ecosystem, reducing the need for additional customization or workaround solutions.
6. Security and Compliance
Security is a top priority when selecting B2B software. We assess the software’s security features to ensure it meets the necessary standards and protects sensitive business data. Additionally, compliance with industry-specific regulations is crucial, particularly for sectors like finance, healthcare, and retail.
7. Vendor Reputation and Support
We consider the vendor’s reputation in the market, including their history of reliability and customer satisfaction. Additionally, the quality of support offered is vital, as prompt and effective assistance can significantly impact the software’s success within the organization.
8. Cost Considerations
Cost is always a key factor in software selection. We evaluate the pricing structure, ensuring the software provides value for money, balancing the cost against the features, support, and benefits offered. We also take into account any additional costs for implementation, training, and maintenance.
9. Trial and Evaluation
We strongly recommend testing the software through a free trial or pilot program to assess its performance in a real-world business environment. This allows businesses to evaluate the software’s functionality, ease of use, and overall fit before making a long-term commitment.
By applying this methodology, we ensure that the selected software aligns with business goals, provides long-term value, and fosters operational efficiency across teams and departments. This thorough approach helps businesses confidently make informed software decisions. We go into more detail about this strategy in our B2B software methodology page.
Remote Access Trojans FAQs
Can a Remote Access Trojan be installed to BIOS?
Access to the BIOS has been known to the world’s hackers since 2015. Many believe that the NSA was planting RATs and trackers on BIOS even earlier.
How is a Remote Access Trojan RAT different from a regular Trojan?
A Trojan is a virus that gets onto a victim computer by passing itself off as a legitimate piece of software. A RAT is a Trojan that the hacker can use to gain regular access to the target system.
What is the Sakula Remote Access Trojan RAT?
Sakula is a RAT that is used to intrude on IT systems serving government departments and agencies, healthcare facilities, and other large organizations. Sakula acts as a hacker platform and can facilitate a range of malicious activities, including ransomware attacks.
















Same thing happen to me, I think once a device gets infected it uses everything thats on the device to pass it to all devices,( Bluetooth, Nfc, wifi, etc) it remembers every single connection it had in the past, I’m still sure I have not gotten it out of my devices
Thanks so much for the reply. I have some computer specialists coming by tomorrow so I will pass this on… I already restored factory settings on the routers I have 2 that I use at different times thinking I could fix the problem. It is defiantly being spread through the router and yes you are correct that there is like this persistent program but it seems to be revived even after restoring from factory settings. I really don’t care about the spying on me. I’m pretty boring it’s just making me unable to function or have access to the internet that is so very frustrating. All the hours spent just trying to make it so I can print or send an email…, insane!
U r awesome so thanks!
I know that
This has totally happened to me. I am nobody with a very small art business. However I do have a sociopathic x husband that is mixed up in some shady stuff. Sounds mostly like bifrost as it took over and became administrator and limited my access to do anything. It even took control of my antivirus bitdefender software and the encryption vaults. It has killed my Mac and my pc. My routers are totally compromised and some kinda of virus has infected my iPad and iPhone. Apple wants me to bring In all the devices and iMac for a clean sweep because they were unable to do anything remotely. I have just unplugged the pc and the router. I’m just going to get a new pc. If you look hard enough you can find the remote devices like keyboard and mouse. And the “root” codes are everywhere. I am not very knowldgeable regarding any of this stuff. It is the busiest time for my business and I literally can’t do anything. It even rendered my Roku unusable. I don’t know what to do and I’m scared that anything i plug in will get infected. Advice? I just ordered the bit defender box 2 thing but the hackers seem pretty persistent and aggressive.
Wow, Angela, Your situation is astonishing. My main observation is that these RATs have to get transferred from one device to another somehow. A telling detail is that your Roku also got infected. That seems to indicate that this RAT was not spread by you plugging in an infected USB stick from one device to another or transferring an infected file to all of your equipment. I would guess that your suspicions are correct: you have been targeted. The only common entry point for all of those devices would be through your internet service. I would also guess that the RAT has got a persistence module onto your router. Whenever you connect a cleaned device to the router, the RAT will get reinstalled onto it. Look through the menu of your router for a “Restore factory settings” option and activate it. That will wipe out any changes to the firmware of the router and delete the RAT. You will have to get each device disinfected elsewhere and then connect each and check that the RAT has gone before you connect the next.
If you are being targeted by a bitter ex, you should also look into DDoS protection and look into getting a VPN for yourself and your business to filter out any other potential attacks.
I have my fingers crossed that you can surmount all of these problems.
Stay strong,
Stephen
I have the same issue but it has gone from my home and tablet to my car stereo. I am not sure but I think it could possibly be through Bluetooth.
I am agree with it