Sumo Logic is a cloud-based analytics platform designed to help organisations make sense of machine-generated data through real-time log management, monitoring, and troubleshooting. Since launching in 2010, it has developed into a broad observability and security solution that supports operational, performance, and security use cases across modern IT environments.
The platform is built to process large volumes of data from applications, infrastructure, and security systems, turning it into actionable insights. It enables teams to monitor systems in real time, detect anomalies, and generate alerts for potential issues before they escalate. Its analytics capabilities also help organisations identify patterns and trends that support more proactive decision-making.
Sumo Logic integrates with major cloud providers such as AWS, Microsoft Azure, and Google Cloud, as well as on-premises systems, allowing organisations to centralise monitoring across hybrid environments. In addition to observability, it also supports security monitoring and SIEM-style use cases, helping teams detect and respond to potential threats more efficiently.
Widely adopted across industries including technology, healthcare, finance, and retail, Sumo Logic is used by organisations looking to simplify log management and improve visibility across their systems. Its cloud-native architecture allows it to scale easily while maintaining consistent performance and reliability in complex environments.
How Does Sumo Logic Work?
At its core, Sumo Logic works by collecting log data across all of your servers and analyzes those logs to create real-time security and operational insights.
During the initial setup, Sumo Logic will require small agents called Collectors to be installed on each endpoint you wish to collect data from. These Collectors are configured to pull relevant log information from that server, to your Sumo Logic cloud for processing. As that unstructured data enters the system, Sumo Logic can automatically or manually be searched through to detect intrusions, identify insider threats, or provide root cause analysis for complex issues.
Having a centralized SIEM platform allows you to analyze security incidents from one place no matter what server or application generated the event. Other issues such as compliance failures and application errors can be detected through the platform through its logging analysis. The true value of a SIEM product such as Sumo Logic becomes more clear as your business and networks become more complex over time.
Now that we know a bit about how Sumo Logic works, let’s dive into each of the features Sumo Logic brings to the table.
Getting Started With Sumo Logic
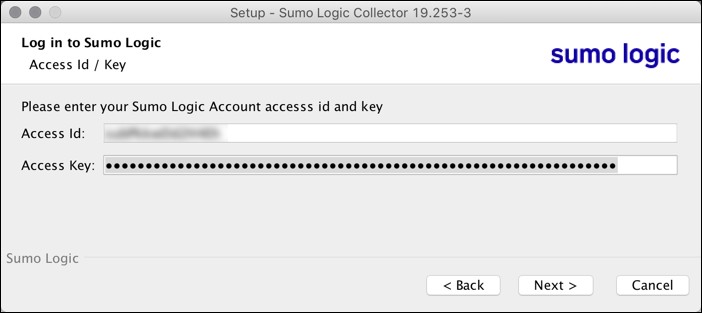
We mentioned briefly that Sumo Logic utilizes Collectors to gather data. These lightweight endpoints are relatively easy to deploy and can be installed manually or through an automated process such as group policy or batch script. Currently, Collectors can be installed on Windows, Linux, or macOS.
Compared to other SIEM solutions, the agent installation process for Sumo Logic is simple and doesn’t require too many complex steps. You can install the Collector with either the UI installer or the command line installer. If you pick the UI installer, some of the more advanced installation options won’t be available. Having both options available allows less technical individuals to get started with Sumo Logic without having to learn programming or how to use the command line.
The next step is connecting a Source to your Collector. A Source is where Collectors connect to collect data from your site. Sources let you better organize your data and can have up to 1000 Collectors associated with them. Sources can vary depending on your environment. For example, there are Sources for dedicated Windows Event Logs, Docker logs, Syslogs, and other host metrics.
It may sound a bit complex, but this can all be done right in the Sumo Logic Collection dashboard through a guided wizard. You can easily test to make sure your Connectors and Sources are working together by entering a query for that data. If you get a result, you’ll know you’re up and running.
Searching Inside Sumo Logic
Searching inside of Sumo Logic for your data is similar to platforms such as Graylog or Splunk. As you build your query the search bar will predict and suggest functions as you begin to type them. One of my personal favorite parts of searching in Sumo Logic is having the ability to visualize your search data as you type it out.
Below the search bar, you can see your data as a visualization, in chart form. Below that, you’ll see the individual rows and tables as you query your data and make changes. If you find yourself needing to query and compare the same data sets over time you can easily save your searches. You can also organize those search queries into folders either for your own personal use, or to be shared with a team.
Dashboards and Panels
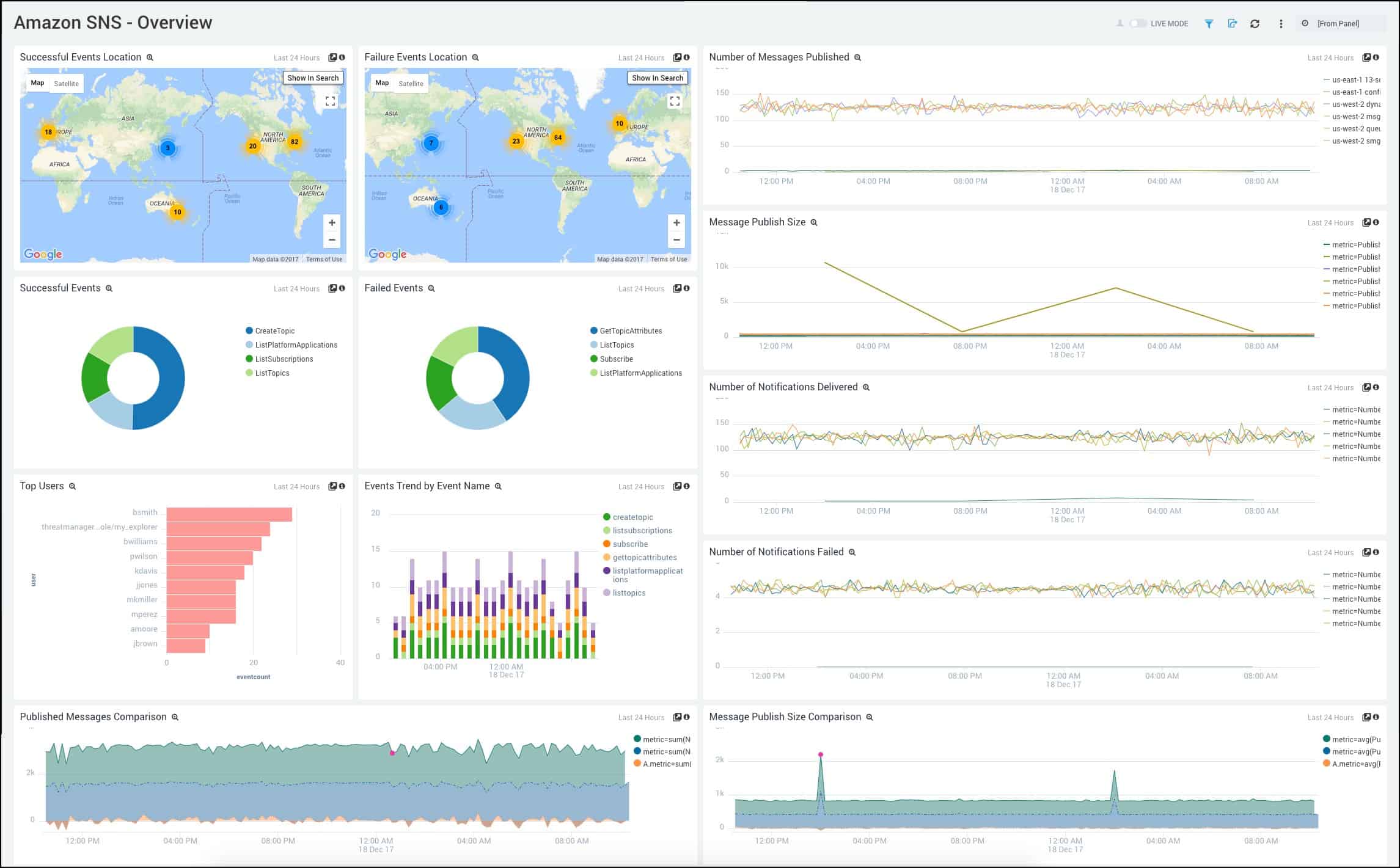
The key to conceptualizing your newly formed insights is being able to understand and visualize them as a whole. Sumo Logic uses fully customizable dashboard views to present relevant data in real-time. Each metric can be displayed by a number of panels that you can add or remove to your dashboard view.
Changing the configuration or output of an existing dashboard is easier than I initially thought. Above each panel is a button that shows you exactly what query is powering that module. Clicking on this lets you edit that query to completely transform how that module displays data.
If you just want to change how the data is displayed you can also toggle between 10 different data views with a few simple clicks. Any panels you create can be dragged and locked into place based on your preference. Once you have the exact look and feel of how you want your dashboard to be displayed you can either save it or share it with your team via a URL link.
If you don’t want to spend the time creating dashboards or panels, the Sumo Logics App Catalog has hundreds of preconfigured dashboards that contain alert templates, and searches that are ready to go in just one click. While using Sumo Logic you’ll find the App Catalog to be one of the more powerful tools on the platform, especially if you have a smaller team that might still be learning how to fully leverage the power of advanced analytics.
Creating Alerts In Sumo Logic
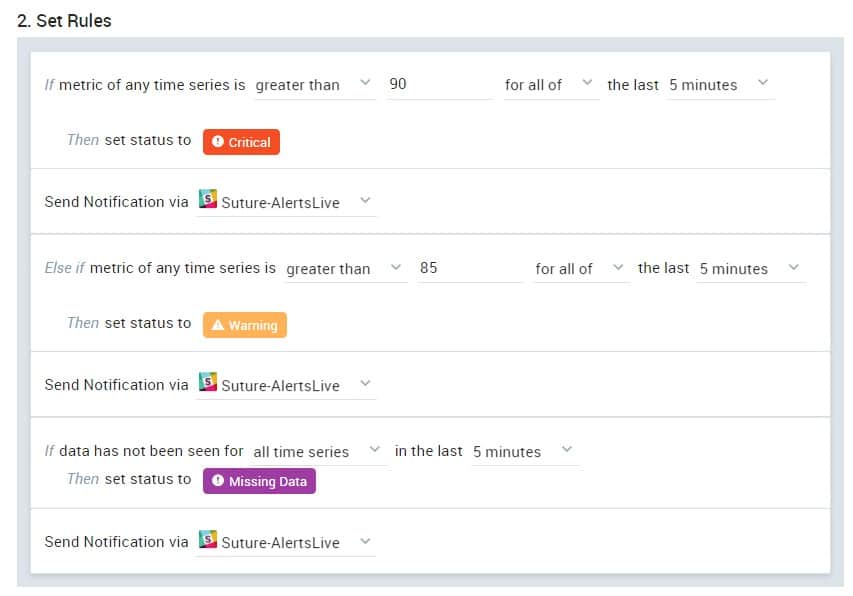
Alerts can be configured based on log data or metrics and are based on a specific query or condition you define. Finding where to create the alert did take some time. Rather than having a dedicated alert button, Sumo Logic has the option to save the query as an alert type when you click Save As. If you want to actually receive an alert you’ll have to make sure you schedule that query to run. This can be done after you save your query. This process is fairly simple but could have been designed to be easier to find.
You’ll have the option to set the time range for the alert, as well as specific alert conditions that can be configured to help cut down on repetitive and unnecessary alert volumes. Notification options range from email, webhook, ServiceNow, or custom script execution. Having the option to execute a script on a set of conditions gives you a wide variety of automated remediation options. Lastly, you can choose to save an alert to index rather than send out a notification. This option records the event and saves the query to an index, where it can be searched at a later time with increased search performance.
Creating alerts can be as simple or as complex as your search queries allow for, and there are no real restrictions to what can be configured. Sumo Logic can use basic numerical-based operators to track problems, or slightly more complex outlier queries that track the deviation of the average mean, rather than a specific number. This helps keep your alerts accurate as traffic increases and decreases over time.
Rather than building these alerts from scratch, you can find many examples and samples of the most common alert queries in the Sumo Logics Query Library.
Apps and Integrations
We touched on Apps a bit earlier in this article, but we’ll go into a bit more detail of what you can expect when integrating applications into Sumo Logic. The App section was built to provide users with instant insights across some of the most popular platforms available. You simply find the integration you want to add and click Add to Library.
Once added, you’ll have dozens of queries already in place and displaying data. These out-of-the-box solutions can be modified and changed to your liking to really jumpstart the onboarding process.
There are hundreds of preconfigured queries and dashboards for dozens of major brand integrations such as Amazon, Google, Microsoft, and Cisco. In regards to SIEM and security tool integrations, Sumo Logic currently supports over 20 threat detection platform orchestrations.
For integrations that aren’t covered in the Apps library, Sumo Logic can provide you with support. There is also a dedicated community forum that can answer questions, however, it may not be as active as some open-source platforms such as Graylog.
Pros & Cons
Pros:
- Flexible and robust alerting and reports
- Supports multiple environments (Linux, Windows, and Mac OS)
- Simple installation – Uses wizards to streamline install and add-ons
- Has a host of templates and premade assets making the experience user friendly
Cons:
- Better suited for small to medium-sized businesses
Sumo Logic Price
Sumo Logic has five different levels of SIEM offerings based on log capacity, data retention, and capabilities. For those who just want to get their feet wet, you start using Sumo Logic completely for free under the Free plan.
This plan allows you to send up to 500MB of data per day and retains log data for one week. However, under the free plan, you’ll only get access to about a fifth of the features that the Enterprise Operations plan includes. In the free version, you can still search and create visualizations, view live and historical data, and utilize predictive analytics and outlier detection.
Paid plans are available for a 30-day trial and utilize a credits system that charges your account based on data usage per day. Rather than trying to charge your card after a trial, if after the 30 days you don’t stay on your paid plan, your account will simply just revert back to a trial plan.
At the most basic paid level, Sumo Logic Essentials will cost $2.50 per GB of log data ingested and offers 365 days of data retention. The Essentials package does contain many of the most popular features Sumo Logic offers, but excludes capabilities such as premium support, ingest budgets, and search API access.
When you factor in the level of flexibility and control you have over your pricing, Sumo Logic is definitely on the more affordable end of the spectrum when it comes to cloud-based log management and security.
Why Choose Sumo Logic
Sumo Logic was built to make security intelligence accessible no matter how many servers you have in your network, and it did a good job of doing exactly that. With Sumo Logic’s flexible pricing plans, easy onboarding, and a feature-filled app store, it’s definitely a tool you’ll want to give a fair shot. If you’re still doing your homework on SIEM products, be sure to check out our post on the best SIEM Tools.
Sumo Logic Alternatives
If you’re looking for alternatives for Sumo Logic, we’ve provided a shortlist of comparable tools worth mentioning below.
- SDatadog Leverages real-time and historical data to provide actionable insights, automated remediation, and alerting across your cloud or on-premises environment.
- ELK A popular open-source tool dedicated to free log management and incorporates tools such as Elasticsearch, Logstash, and Kibana for extended functionality.
- Sentry.io Provides logging solutions primarily focused on serving software development teams and the DevOps industry.
- Splunk A feature-rich SIEM platform aimed at serving vast enterprise environments. Splunk excels at combining state-of-the-art technology with easy-to-use interfaces.
- Heimdal Threat Hunting and Action Center A cloud-based SIEM that coordinates the efforts of at least three on-premises Heimdal cybersecurity packages to create a system-wide security framework.
- SolarWinds Security Event Manager A comprehensive full-suite security tool aimed to help MSPs manage complex security events without complex integrations or setup.