Good Practice Guide 13 or GPG 13 is a list of measures that outline how UK government data must be protected. Under GPG 13, UK government organizations have a responsibility to use monitoring, logging, and other security measures to protect sensitive data.
What is GPG 13?
GPG 13, formally known as Good Practice Guide 13, is issued by the UK’s National Cyber Security Centre (NCSC) to support organizations in securing their IT systems. Its main focus is on managing user authentication and access controls, which are vital for protecting sensitive information and ensuring that only authorized users can reach critical systems.
The guidelines stress the use of strong authentication methods, including multi-factor authentication (MFA), and advocate strict controls over user accounts. This involves careful procedures for account creation, management, and deletion, as well as regular reviews to revoke access when no longer necessary, helping to maintain a principle of least privilege.
Another cornerstone of GPG 13 is the zero-trust approach. Every user, device, and application is treated as potentially compromised, requiring continuous verification for each access attempt. This is particularly relevant in modern IT environments where networks are distributed and traditional perimeter security is no longer sufficient.
Audit and monitoring practices are also emphasized. Organizations are encouraged to regularly inspect access logs and monitor user activity, which aids in spotting unauthorized or unusual behavior early, enabling prompt corrective action.
In essence, GPG 13 provides organizations with a structured framework to strengthen cybersecurity by combining robust authentication, precise access controls, continuous monitoring, and zero-trust principles—helping to safeguard systems and data in today’s complex digital landscape.
Who Needs to Follow GPG 13?
While the regulatory guidelines of GPG 13 were mainly designed for Her Majesty’s Government (HMG) departments and agencies, service providers can also find themselves needing to comply. Service providers with access to government data should also comply with the requirements.
What are the Penalties for Non-Compliance?
GPG 13 is a guide rather than a policy. As a consequence, there aren’t any penalties or fines for non-compliance beyond the potential risk and loss of sensitive data. Being compliant with GPG 13 is a matter of ethics and best practice rather than legal necessity.
From an ethical standpoint, agencies should take all necessary measures to protect the data they hold from being compromised in case there is a knock-on effect on citizens or other organizations.
The Four Recording Profiles
GPG 13 has four recording profiles, with different variations in the amount of protection you should have against cyber threats. The recording profiles are identical to the HMG Information Assurance Standard Segmentation Model, and are broken down into four categories (from low to high segmentation):
- Aware – An obligation to be aware of public domain threats, common attack vendors, and known vulnerabilities.
- Deter – An obligation to deter attacks from a skilled hacker (must implement controls to deter an attack!).
- Detect/Resist – An obligation to detect and resist an attack from a sophisticated attacker.
- Defend – An obligation to defend against an attack from a sophisticated attacker.
Agencies must choose which level of organization to apply to what data. To decide the level of segmentation to use agencies should examine the potential consequences of the loss of the data in question, and the effect on the UK or EU government, UK citizens, or businesses.
GPG 13 Compliance Checklist: Protective Monitoring Controls
There are 12 PMCs outlined in GPG 13. These controls boil down to using network monitoring tools to identify threats to the network and connected devices. The network monitoring solution used should also offer features like alerts, notifications, and automated reports so that the user can respond to critical events promptly.
Here is the list of controls:
- Ensure logs have accurate and consistent time stamps.
- Record cross-boundary traffic and confirm its validity.
- Analyze boundary traffic and identify suspicious activity.
- Identify status changes to devices, servers, and work stations with alerts and automated reports.
- Record suspicious activity in your network with notifications.
- Track, record and analyze network connections.
- Establish alerts to recognize and analyze suspicious user and workstation activity.
- Create a backup and business continuity plan that protects data integrity and availability.
- Define factors that classify as critical events and deliver real-time alerts and reports.
- Confirm the validity and integrity of auditing processes.
- Develop a procedure for producing accurate reports for accessing the performance of your PMC compliance.
- Provide proof that security measures, including monitoring data collection, are lawful and secure.
1. Ensure Logs Have Accurate Time Stamps
The first requirement is that you have the ability to view timestamps from log data. Timestamps are used to tell you when a security event has happened. From a regulatory perspective having accurate timestamps provides you with a record of network events that you can use to see what’s happening. To meet this requirement you will need to use a log management tool or a log analyzer (such as ManageEngine EventLog Analyzer or LogRhythm).
2. Record Cross-Boundary Traffic
The second requirement states that agencies must record business traffic crossing a boundary. More specifically you must record, analyze, and report business traffic to make sure that all traffic is authorized. Any malicious traffic should be stopped, prevented, or alerted.
3. Recording Relating to Suspicious Activity at a Boundary
Recording relating to suspicious activity refers specifically to monitoring network traffic crossing a boundary to detect suspicious behavior. You should have the means to detect if an attacker is attempting to access a device or there is a deviation from normal network usage.
4. Recording of workstation, server or device status
You must also be able to monitor changes to the status or configuration of devices. Workstation, server or device recording should allow you to identify whether changes on a device have occurred due to malware or through a genuine user mistake. The monitoring should also be able to identify indications of an attack such as repeated system restarts or through the use of unusual processes.
5. Recording relating to suspicious internal network activity
Monitoring internal boundaries is just as important as monitoring cross-boundary traffic. Agencies must detect suspicious activity that signifies that an attacker has breached the internal network. Tools like intrusion detection systems and intrusion prevention systems are examples of tools that could help to identify this.
6. Recording relating to network connections
It is also necessary for agencies to monitor temporary connections to the network made by remote access, VPN, wireless, or other types of transient connection. Monitoring temporary connections is important in case an attacker is trying to gain access to your network through alternative means.
7. Recording of session activity by user and workstation
To make sure that user behavior is legitimate agencies must monitor user or session activity and access to verify a system hasn’t been breached. The monitoring solution should be able to detect unauthorized or suspicious activity to make sure that no malicious entities have access to confidential data.
8. Recording of data backup status
In the event that a cyber attacker does breach the network and cause damage, organizations should be able to identify and recover information assets that were damaged. This means being able to recover lost files and revert to the status of the asset before the attack.
9. Alerting critical events
To ensure you respond to security events quickly you must have a monitoring solution with near real-time notifications. Notifications should be as close to real-time as possible but you don’t necessarily need a solution with instantaneous alerts (though this would be advantageous from a security standpoint).
10. Reporting on the status of the audit system
This requirement states that you must be able to confirm the validity and integrity of auditing processes. In other words, you should be able to verify the integrity of the data that you collect.
11. Production of statistical management reports
You must be able to produce reports to provide feedback on the performance of the Protective Monitoring system. Reports provide an additional investigation into security events and provide more of an audit trail. It is necessary to obtain a network monitoring solution that allows you to generate reports (a solution that allows you to schedule reports that can help to make sure you don’t forget).
12. Providing a legal framework for Protective Monitoring activities
Finally, you must make sure that all monitoring of systems and communications is conducted in accordance with the law. This means that you mustn’t violate the law or the rights of individuals when collecting data. In addition, you must make sure that any accounting data collected is treated as sensitive information and protected.
Network Monitoring
The best way to ensure you comply with these requirements is to deploy a network monitoring solution that can give you the combination of visibility, alerts, and reports. Picking the right network monitoring solution(s) will go a long way towards defending against threats and prevent you from falling victim to an attacker. For the purposes of GPG compliance, we’re going to look at the log management requirements and LogRhythm.
Log Management Requirements
Log management is a topic that comes up consistently in the GPG 13. To satisfy all of the requirements, there are a number of components you need to address. The specific guidelines on log management depend on the level of segmentation or risk level that the system faces:
| Level of Segmentation | Log Retention Time | Log Checks | Compliance Review |
|---|---|---|---|
| Aware | Up to 3 months | Once a month (Minimum) | Annual (Minimum) |
| Deter | 3-6 months | Once a week (Minimum) | Annual (Minimum) |
| Detect / Resist | 6-12 months | Once a day (Minimum) | Every 6 months (Minimum) |
| Defend | Over 12 months | Once an hour (Minimum) | Every quarter (Minimum) |
More broadly you must also be able to record user access (specifically unauthorized users), file access attempts, view successful or unsuccessful logins and logouts, configuration changes, and policy changes. To help meet the requirements above, it is highly recommended to use a log analysis tool. We’ve included LogRhythm below as an example.
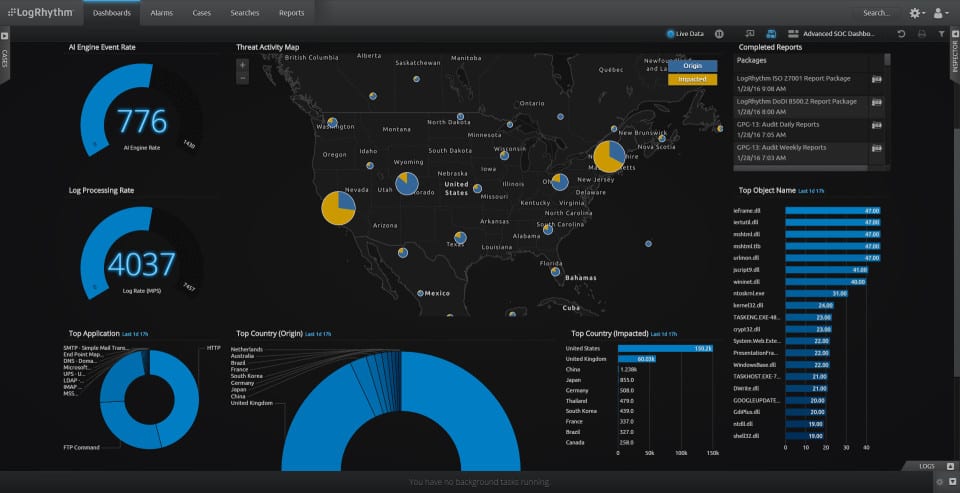
LogRhythm (Log Management Software)
LogRhythm is a log monitoring solution that matches the control requirements outlined in GPG 13. The software offers automated log management and event messages from a centralized perspective. The log management capabilities of the software meet the first challenge of detecting threats.
Key Features:
- Deployment options
- Log collection and consolidation
- Log file management
- Auditing support
- Threat detection
Why do we recommend it?
LogRhythm is a cloud-based SIEM tool that relies on the consolidation of log messages from all around the business as its source data. It is the log manager in the platform that gives you GPG 13 compliance functions. You to install agents on different assets around your network and cloud platform accounts.
The software has three modules designed specifically for GPG 13 for the purpose of Protective Monitoring Controls: GPG 13 (standard, GPG 13 Compliance Automation Suite, and GPG 13 Advanced Compliance Suite.) Each is designed to help users apply the level of scrutiny that matches their needs.
Who is it recommended for?
LogRhythm is primarily a threat detection and response system. It requires logs as source data and so the platform also provides a full log manager to enable the threat hunting unit to function effectively. You can tune searches, storage, and archiving to your GPG 13 categories by applying a template.
Pros:
- Available as a virtual appliance, a physical device, or a cloud solution
- Collects and standardizes log messages, enabling them to be unified for searches
- Includes automated threat detection searches and manual analysis tools
- Alerts for threats and data misuse
- Options for automated responses
Cons:
- Doesn’t include a governance module
For greater scrutiny, LogRhythm has a real-time alert system that notifies the user when problematic behavior is recognized. Alerts lower the time to respond and make your remediation strategy much more effective. A fast response will help to fight off more sophisticated attacks. You can view more about LogRhythm here.
GPG 13 Compliance: Monitoring
To comply with GPG 13 regulations you need to use monitoring tools, event log management, event logging, real-time alerts, and reports to improve your visibility.
While you can scrape by and recognize attacks on low priority systems, on high priority systems you will be expected to actively detect and defeat sophisticated attackers. Protecting yourself against the next generation of threats comes down to a combination of vigilance and using the right monitoring tools for the job.
On the higher priority systems be proactive and look for ways to increase your security. For example, if you’re using an intrusion detection system consider switching to an intrusion prevention system that can enact an automated response to an attacker.
There are many solutions on the market that are being designed specifically for regulatory compliance and GPG 13. We recommend that you obtain a monitoring software that complies with existing regulations.
GPG 13 compliance FAQs
What is GPG 13?
GPG 13 stands for the Good Practice Guide 13. It is a set of guidelines that were produced by the Communications-Electronics Security Group (CESG), which is a division of the UK’s Government Communications Headquarters (GCHQ). The CESG is the UK’s national technical authority for data assurance. The standards aim to produce a set of working practices that ensure data activities are properly enforced. The main avenue for data assurance oversight is the collection and collation of log messages that are generated by file systems, access rights management tools, and data management services.
What is protective monitoring?
Protective monitoring involves the collection of live activity data on networks and endpoints to watch over the behavior of users. The purpose of this process is to protect resources, with particular attention paid to activities related to data. Protective monitoring has become increasingly important as data breaches have increased and hackers have created increasingly sophisticated techniques, such as advanced persistent threats (APT).
What is the purpose of logging and monitoring?
Logging and monitoring have two purposes, one is to catch malicious activity as it happens and the other is to reveal previously undetected malicious activities after the fact. Live monitoring requires inputs from both hardware and software and these reporting messages are termed “logs.” A monitoring system needs to collect these messages and search through them for specific activities. Each monitoring system is produced with different aims and so some activities might not be spotted immediately – the operating search algorithm might not be searching for that specific type of behavior. Although missing an attack as it happens is a failure of system security, being able to discover that an attack has occurred is important because it renewables system managers to take steps to close security loopholes – better late than never.