A standard VPN connection encrypts your data, but if you’re looking for maximum security against government tracking or nationwide censorship, we’d suggest using one with multi-hop servers.
Simply put, a multi-hop VPN adds additional layer of encryption to your internet connection by “chaining” or “cascading” two VPN servers together. Sometimes, providers call this a double VPN feature, but you’ll often see these terms used interchangeably. This guide will explain everything you need to know about multi-hop VPNs and why you might need one.
What’s wrong with a normal VPN?
Normally, Virtual Private Networks route incoming and outgoing traffic through a single server. The process goes like this:
- Your device encrypts your internet activity
- This encrypted data is sent to the VPN server
- The server decrypts the data
- Your data proceeds to its final destination.
The same process happens in reverse for incoming traffic.
A normal setup like this provides sufficient privacy and security for most users but still has a few weaknesses. If someone manages to compromise that server, your Internet Service Provider (ISP), government agencies, network administrators, websites, apps, and hackers could correlate the traffic going into the VPN server with the traffic going out.
The VPN server can record your real IP address and online activity even if it has a “no logs” policy. Even assuming the VPN provider is trustworthy, providers don’t normally own their own data centers, which house the servers you rely on.
An attacker can see the IP address of the VPN server you’re connected to. If they can somehow breach the data center where that VPN server is housed, the user is vulnerable to traffic correlation. This would allow them to correlate the encrypted traffic between the end user device and the server and identify the user.
If a well-armed adversary was to somehow compromise your connection to the VPN server—servers in data centers can be hacked, abused by staff, or monitored by government agencies—then they could trace your online activity back to you.
TRY THE BEST MULTI-HOP VPN RISK-FREE
NordVPN is offering a fully-featured risk-free 30-day trial if you sign up at this page. You can use the VPN rated #1 for multi-hop servers with no restrictions for a month—great if you want to see how multi-hop works and if it's something you need long term.
There are no hidden terms—just contact support within 30 days if you decide NordVPN isn't right for you and you'll get a full refund. Start your NordVPN trial here.
Multi-hop VPN advantages
A small handful of VPN providers offer multi-hop VPNs as part of their subscriptions. Our top recommendation is NordVPN, which runs a couple dozen double-hop VPNs to multiple countries. You also get a no-logs policy, fast servers, live support, and strong encryption.
EXCLUSIVE DEAL:Save 68% on NordVPN’s two-year deal here. That works out to only $3.19/mo.
Better security, privacy, and anonymity
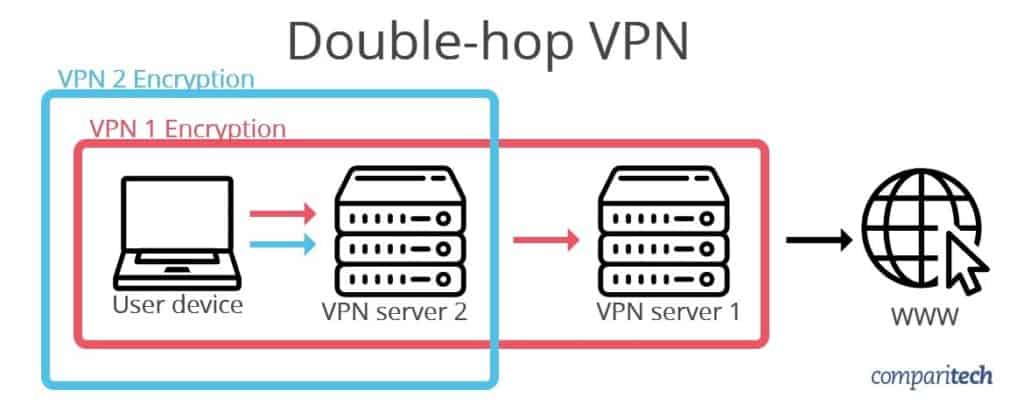
A multi-hop VPN attempts to mitigate these threats. Here’s how a typical double-hop VPN works:
- The VPN encrypts your data
- It then applies a second later of encryption
- Packets of data arrive at the first VPN server.
- The server removes the second layer of encryption
- Packets of data arriev at the second VPN server.
- The server removes the second layer of encryption (meaning the data is fully decrypted)
- The decrypted data moves on to its final destination.
Note that each layer of encryption is removed in the reverse order that it was applied—last in, first out. The first VPN to encrypt data on the device will be the last server in the chain, and the last one to encrypt data will be the first in the chain.
This tunnel within a tunnel solves a few of the problems that impact normal VPN connections. For instance:
- Although your ISP or an attacker can see your data going to a VPN server, they cannot see the second VPN server, and therefore cannot monitor traffic coming out of the VPN to correlate with the encrypted data going in.
- Similarly, websites and apps you use while connected to a multi-hop VPN can see the second VPN server where traffic exits, but not the first one where it enters, making correlation nearly impossible.
Most VPNs use shared IP addresses, meaning everyone on a single server shares the same IP address. This makes it much more difficult to trace online activity back to a single user. Sending traffic through two pools of users with shared IP addresses provides additional security by making traffic correlation exponentially more difficult.
If an attacker compromises the first server in the chain, the user’s data is still encapsulated in a second layer of encryption. If an attacker compromises the second server, they will still not be able to trace back any data beyond the first server.
Bypassing censorship
VPNs are frequently used to bypass censorship, whether in an office or school environment or in an autocratic country like China. If the entity doing the censoring figures this out and blocks a range of VPN servers, a double-hop VPN might be necessary to unblock the web.
Let’s say China blocks or throttles all internet traffic to the US, including US-based VPN servers. If you need to access some content that’s only available in the US, switching to a different country won’t suffice. Instead, a multi-hop VPN could allow you to connect to Canada (or another country) first, and then the US. The censor won’t be able to monitor for the US server, and therefore allows the connection to pass through.
Multi-hop VPN disadvantages
Performance and speed
Internet speed and device performance will both take a hit when using a multi-hop VPN.
- The farther away your chosen server is, the higher your latency. As such, multi-hop servers are not suitable for online gaming.
- The slowest server in the chain bottlenecks your connection. Most VPN users notice slightly slower speeds when connected and this problem gets more prominent when using two or more servers.
- Decrypting two or more layers of encryption instead of just one is more demanding on your device hardware.
In a rare few cases, the connection between the two servers might be faster than a direct connection to the second server. In this case, a multi-hop VPN can improve latency by navigating around the roadblock, but this scenario seldom occurs in a way that’s reliable enough for a multi-hop VPN to really benefit users over a single VPN.
Will not protect you from your VPN provider
Multi-hop VPNs mitigate some of the traffic correlation risks associated with single server VPN connections, but they won’t protect you from nefarious VPN providers. If both of the servers in the chain belong to the same provider, it would be simple for that provider to monitor your online activity and keep logs of what you do online. Because the provider has control of both servers, using a double VPN does nothing to protect from the VPN provider.
One solution is to use VPN servers from separate providers (see below), and another is to use your own VPN server in combination with a provider’s. These methods require much more technical expertise to set up compared to the multi-hop options built into some provider’s apps, and are beyond the scope of this article. Suffice to say they have their own challenges and privacy issues.
Multi-hop VPN vs Tor
If anonymity and accessing the dark web is your goal, Tor will probably serve you better than a multi-hop VPN. Tor servers, called nodes or relays, are decentralized, meaning they aren’t operated by a single entity. Tor traffic always passes through at least three of these nodes, which is more than the typical two offered by most multi-hop VPN services.
Each time you access a different domain, your internet traffic takes a different, random route through the Tor network. Each node only knows the location of other nodes that immediately precede and follow it. That means no one node has knowledge of the entire route that your traffic takes to its destination. Similar to a multi-hop VPN, each node removes a layer of encryption, revealing the IP address of the next node in the chain.
Tor does not allow you to choose where these nodes are located, whereas a multi-hop VPN does. Tor is also somewhat vulnerable to traffic analysis, although it’s extremely rare. Many apps and websites might block internet traffic from Tor exit nodes. And Tor is generally slower than a VPN.
Tor + VPN
It’s possible to combine Tor with a VPN, but experts argue as to whether this actually provides much benefit to the user. The easiest way to use Tor with a VPN is to simply connect to a VPN and then open the Tor Browser. Traffic is first sent through the VPN, and then the Tor network.
If you’re feeling like you need to maximize your privacy at the cost of performance, a multi-hop VPN combined with Tor is certainly an option, but probably not one that’s necessary for the vast majority of users.
Can I use two VPNs at the same time on the same device?
It is possible to connect two VPN clients to separate servers at the same time on a single device. However, this will generally not result in a multi-hop VPN as we have described above. Instead, people using multiple VPNs on a single device are typically using them for split tunneling. In other words, it creates two parallel tunnels instead of a tunnel inside a tunnel.
Split tunneling uses a set of rules that determine the routes your internet traffic will take, depending on its source or type. For example, you may want BitTorrent traffic to travel through one VPN, and data from all your other apps to travel through a different VPN. So long as the two rulesets that determine this behavior do not overlap, the two VPNs can operate independently.
Simply installing two VPN apps on a single device and connecting both without establishing IP routes ahead of time can cause trouble, such as memory leaks and DNS errors. The exact result varies depending on the particular VPN clients’ implementation.
We tested a few VPNs on Windows 10 to see what would happen if we connected them simultaneously. In our testing, one of two things happened. Either the first VPN prevented the second from connecting at all (ExpressVPN prevents NordVPN from connecting) or the second VPN took over completely (PrivateVPN took over even though Ivacy, which has now merged with PureVPN, was still connected). The VPNs did not operate in tandem, and running a traceroute gave the same results with one VPN connected as with two.
In short, connecting two VPNs at the same time on the same device is not the same as using a multi-hop VPN. In fact, it can result in undesirable behavior and errors.
Chaining VPN servers from different providers
You can chain VPN servers from different providers, but there’s a better option. We recommend installing one VPN on your laptop and the other on your wifi router or a virtual machine. This has a similar result to using a double-hop VPN from a provider like NordVPN. The flow of data looks like this:
- VPN A on your device encrypts data and sends it to the router or VM.
- The router’s VPN or virtual machine encrypts the data a second time and sends it to VPN B’s server.
- VPN server B receives the data, removes the second layer of encryption, and sends it on to VPN server A.
- VPN server A receives the data and removes the first layer of encryption. Finally, it sends the fully decrypted data on to its destination.
The process happens in reverse for incoming internet traffic. Websites and apps can only trace traffic back to VPN server A, while your ISP only sees that information is being sent to VPN server B.
Real-World Use Cases for Multi-Hop VPNs
A multi-hop VPN isn’t something every user needs, but it can be a useful extra privacy tool in certain high-risk scenarios. Below, we’ve listed a few practical use cases where routing your internet traffic through multiple VPN servers can be helpful:
- Journalists and activists: Especially those working under repressive regimes where censorship, surveillance, and data requests are common.
- Whistleblowers and researchers: Anyone handling sensitive information or leaking documents needs stronger protection from tracking or data theft.
- Healthcare professionals and lawyers: Individuals handling client records can reduce exposure to hacking or snooping.
- Privacy advocates and high-profile individuals: Users at elevated risk of being tracked or targeted benefit from added anonymity. This includes activists, employees at NGOs, political dissidents, etc.
When privacy, security, or jurisdictional concerns are critical, it is a good idea to use multi-hop connections or Double VPN. Running your data through two consecutive VPN servers makes it harder for anybody to connect your online activities to your home IP address.
Routing your encrypted traffic through two VPN servers creates a barrier against time-correlation attacks, which is essential for protecting your online activity from being linked back to your IP address.
We recommend using a multi-hop VPN whenever you require stronger protection than a standard VPN connection that uses a single VPN server.
Understanding Jurisdictional Server Pairings
When you use a multi-hop or Double VPN connection, it’s vital to understand how the jurisdictional server pairings affect your privacy.
A multi-hop VPN connection provided by a VPN service will typically bounce your data through two VPN servers: one acting as the entry node and the other as the exit node. The entry node is your point of connection into the VPN network, and the exit node is where your traffic re-enters the internet.
This structure creates a layer of privacy by separating your real IP address from the websites or services you’re using. However, it also introduces legal considerations. Because your online traffic passes through two different jurisdictions, your data could theoretically be exposed to two sets of surveillance laws or government requests.
Many VPN providers don’t disclose which countries are used in their server pairings, which creates jurisdictional confusion for their users. We recommend using services that either disclose the locations or let you manually select your hops. This gives you a full understanding of your traffic routing.
Key takeaway? Using a multi-hop VPN connection makes it harder to associate your real IP address with your browsing activity. However, VPN users need to consider where their data is going on both the first and second hops, as these introduce jurisdictional considerations regarding the potential for data requests, warrants, and covert surveillance.
Will Double VPN Slow Down My Internet?
Yes. A Double VPN connection routes your internet traffic through two VPN servers, which inevitably increases latency and reduces speed. This is due to both the added encryption and the increased distance your traffic must travel.
The slowest server in the chain will typically become the performance bottleneck. This is why multi-hop VPNs aren’t ideal for time-sensitive tasks like online gaming, video calls, or large file transfers.
Double VPN is most useful in high-risk scenarios, such as when:
- You’re operating under strict internet regulations
- You need to protect against traffic correlation
- You’re trying to keep your source IP fully hidden from destination websites
However, for everyday use such as streaming, torrenting, browsing, or accessing regional content, a single-hop VPN tunnel is usually sufficient.
Disable Double VPN for Better Speed
If your VPN feels sluggish and you’ve enabled Double VPN or multi-hop, you may have forgotten to turn it off. We recommend disabling this feature when you’re not specifically working in a sensitive or high-risk environment.
Switching back to a regular VPN connection will ensure faster speeds while still providing solid security and privacy for most daily tasks.
Multi-hop VPN: FAQs
Is a multi-hop VPN and a double VPN the same thing?
Yes, double VPN is just another term for a multi-hop VPN. In both cases, your data is routed through two or more servers upon connecting. As a result, this data is encrypted multiple times, providing you with an extra layer of security. However, you’re likely to experience slower speeds as the data has to travel further before reaching its destination.
Is a multi-hop VPN safe?
Yes, multi-hop VPNs are safe, and in most cases, are more secure than standard VPNs. While an average VPN encrypts your connection to prevent hackers from spying on your data, traffic correlation is still a possibility. A multi-hop VPN provides additional security for your device to prevent more sophisticated attacks.
Do Free VPNs Provide a Multi-hop Feature?
No, free VPNs do not usually offer a multi-hop feature. Multi-Hop is a relatively new technology that allows you to connect to multiple servers simultaneously and chain them together, thus increasing your level of security and privacy. This feature requires additional costs for the service provider and is unavailable in most free VPN services. If you are looking for a VPN with multi-hop, opt for a premium VPN service. Paid VPN services generally provide more features and better security than their free counterparts.
Can I use Double VPN on mobile?
Yes. Some of our recommended VPNs offer multi-hop VPN support on Android and iOS. However, you may need to manually enable this feature in the app. Remember that using double VPN or multi-hop on mobile can slow down your traffic and lead to battery drain. This means you should only use it when you require additional privacy, prevention of surveillance, and protection against time correlation attacks.
Multi-hop VPN vs. Tor: Which is better?
Both technologies protect your privacy, and both route your internet traffic through multiple server locations or “nodes.” However, they function very differently.
A multi-hop VPN uses encrypted, private VPN servers operated by a VPN provider. This means you know exactly where your data is going and who controls the servers—usually a company with a published privacy policy and clear data handling practices.
Tor (The Onion Router), by contrast, routes your traffic through public, decentralized nodes that anyone can volunteer to run. You have no way of knowing who operates each node or what their motives are. That creates potential risk, especially if one of those nodes is run by a hostile party or subject to surveillance.
While Tor is excellent for anonymity and access to the dark web, it comes with performance limitations and real-world risk. A multi-hop VPN offers more consistent speeds, private infrastructure, and avoids the dangers of Tor’s public exit nodes, which could be hosted by hackers, data brokers, or even government snoops.