October is National Cybersecurity Awareness Month (NCSAM) and the main theme is “Our Shared Responsibility.” While we should be thinking about online security all year round, now is a good time to kick things up a notch.
Often, when we hear the term cybersecurity, we think about corporations and governments that are at risk of mass data breaches due to hacking. However, cybercrime can happen at the most basic level, and is a concern at home, in the office, and on-the-go.
Whether you’re using your work laptop, your smart home devices, or your tablet, cybersecurity should always be a consideration.
Let’s look at a few statistics to see why:
- Cybercrime was the second most reported crime in 2016, and in 2017 cost $600 billion.
- In the first half of 2020 data breaches exposed over 30 billion records.
- More than 60 percent of online fraud is carried out through mobile platforms.
See also: Phishing statistics
As you can see, the fight against cybercrime stretches beyond businesses and governments and the risks are all around you. Becoming complacent and leaving cybersecurity up to the experts would be fuelling the flames of online crime and paving an easier path for criminals. In reality, we all need to work together and share the responsibility of cybersecurity in order to have the best chance of winning the fight.
In this post, we’ll describe some of the simple steps you can take to protect you and your family from the criminals lurking online. We have already published various in-depth guides related to this topic, so you can follow the links to find our more, where appropriate.
Brush up on current cybersecurity topics
You don’t have to be an expert to be a part of the crusade against cybercrime. But it does help to know what’s going on in the world of cybersecurity. You never know; once you get a taste for cybersecurity, you may even want to make a career out of it.
This post and our related guides will serve as a solid basis for your knowledge and understanding of cybersecurity. But remember that the landscape is always changing, so it’s a good idea to subscribe to a blog such as ours or similar, so you can stay abreast of the latest happenings.

If you want to delve deeper, a plethora of cybersecurity resources and tools are at your disposal, as well as dedicated cybersecurity institutes and events dotted around the globe.
Be aware of common scams and attacks
As you delve into the topic of cybersecurity, you’ll become more familiar with the many and varied types of scams and attacks that pose a risk to both individuals and businesses.
When it comes to scams, the notion of cybersecurity is less about defense tools and more about common sense. There are a plethora of scams out there, but we’ve listed some of the common ones below.
- Tax scams might involve emails, phone calls, or text messages and play on people’s fear of landing on the wrong side of the government.
- Romance scams often start on online dating sites but might end up with victims being asked to pay money or take part in criminal acts.
- Travel scams involving hotels and transportation often leave would-be vacationers living a nightmare instead.
- Bitcoin scams come in many different forms including fraudulent mining companies, wallet scams, and extortion schemes.
- Phishing victims are persuaded to hand over personal information that can be used in a later scam. These types of scams often happen over email, but may involve text messages (smishing) or phone calls (vishing) as well.
- Credit card scams can take various forms, but may involve phishing schemes or company data breaches.
Even certain types of code-based attacks such as ransomware and brute force attacks can be defended against using a little common sense. Here are some common types of attacks to be wary of:
- Ransomware is a form of malware that takes over computer files so that hackers can demand a ransom in return for their release.
- Brute force attacks usually use a script or bot to guess information, such as a username or password.
- Botnet DDoS attacks can vary greatly but might involve malware taking over multiple devices to form a botnet that carries out a Distributed Denial of Service (DDoS) attack on a target network.
- Man-in-the-Middle attacks involve someone intercepting information, effectively allowing them to listen in on your communications and other online activity, steal information such as login credentials, and even change the contents of your web traffic.
The methods behind these attacks vary, but email and messaging systems are often used to disseminate them. As such, it’s important to learn how to spot suspect emails and always have your wits about you.
Use an antivirus software
Although an antivirus software should not be relied upon as your sole method of cybersecurity, it can help a lot. Most software is equipped to help detect or defend against certain types of cyber attacks, including various types of malware. Some software comes with additional features to help combat against things like phishing attacks and botnet DDoS attacks.
Some great free options include Bitdefender Antivirus Free Edition (Windows, MacOS, and Android) and Kaspersky Security Cloud – Free (Windows, Android, and iOS).
If you’re willing to pay a few bucks a month for a premium antivirus software, Panda Security and Total Antivirus (Total AV) are some solid choices.
Use strong passwords
This seems like such an obvious one, but it’s alarming how many people still don’t use strong passwords. In fact, almost one-third of network intrusions are the result of compromised user credentials (usernames and passwords). Yes, it can be difficult to remember a different password for each of the dozens of accounts you have. But the risks involved outweigh the convenience factor.
Here are a few tips for creating a strong password:
- Use a different password for every account.
- Use a mix of upper and lower case letters, numbers, and symbols.
- Make the password as long as possible — at least eight characters.
If you’re having trouble, you can use our password generator tool to help.
And if trying to remember all of those passwords is too much, you might want to consider using a password manager, such as LastPass or Dashlane. One perk of these is that they can help you protect against phishing sites. They won’t recognize the site and won’t autofill your information, which should raise a red flag as to the site’s validity.
Take extra care when using public wifi hotspots
While you’re at home, chances are you’ll feel safe and secure using your own network. But most people are increasingly using internet while on-the-go. And that often means connecting to a public wifi hotspot.
These might seem secure, especially if you’re at a mall, hotel, or reputable coffee shop, but the reality is these are prime spots for hackers to lie in wait.
When connecting to any public wifi network, you should always take precautions, including ensuring you connect to a secure network, avoiding sending sensitive information such as bank login details, and using a VPN connection (more on that below).
You may not have believed it a couple of decades ago, but the phenomenon that is social media is now an inevitable and integral part of our everyday lives. While there are countless benefits to using media, there are also a number of inherent risks. Sites like Facebook, Snapchat, and Instagram each have their own potential privacy and security issues.
The ability to post every detail about your life online for the world to see can be a dream for some. But every piece of information posted is ripe for the picking by cybercriminals. In fact, they don’t even need to do any hacking or otherwise to get the information.
Any gathered information can be used in wide range of scams and attacks (including physical ones). Clearly, you want to keep you and your family safe from such situations, so it’s important to follow best practices when using social media.
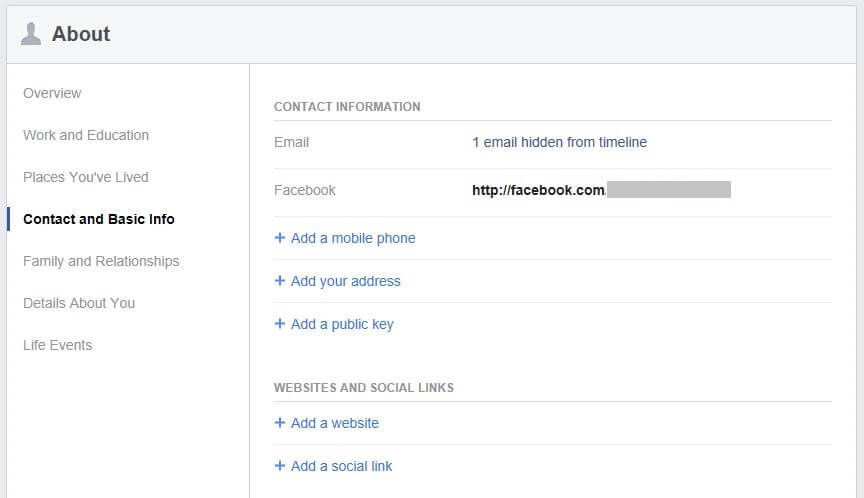
Be sure to adjust your privacy settings for each platform and check back regularly in case the options have changed. Always think twice about posting any kind of personal information such as your phone number, address, and current location. Remember that even photos can give away too much information about you and your family, for example, where you work or where your kids go to school.
Protect your children’s privacy online
On that note, it’s not just you who needs to have their wits about them while online. Your kids need to be educated about cybersecurity and know how to protect their privacy too. A 2017 Australian study found that kids as young as eight years old have shared things like their last name, address, and phone number on social media.
Here are some tips for navigating social media with your child:
- Set up your own account on each platform and “follow” and “friend” your child where possible.
- Get them to avoid using social logins for other platforms as they may be mining data from their social media accounts.
- Help your child adjust their privacy settings for each account, remove as much identifying information as possible, and even use fake information if needed.
- Consider using built-in parental controls or purchasing parental control software, especially if you have younger kids.
How you help your child will depend on their age, maturity, and experience level with social media, but it’s good to keep this an open discussion topic in the home.
Consider encryption your files and communications
If you want to be extra vigilant about keeping the digital information in your home safe, you may want to consider encryption. When data is encrypted, even if it falls into the wrong hands, it will be unreadable.
Encryption can happen at various levels and there are plenty of methods and tools out there to help you. You can encrypt your files and folders using tools such as Hider 2 for MacOS or BitLocker and EFS for Windows. You may choose to encrypt your email too, by adjusting the settings within your account.
One more encryption method which we recommend everyone use is a VPN. We’ll explain this in the next section.
Use a VPN to encrypt your website traffic
A VPN, or Virtual Private Network, will encrypt all of the internet traffic flowing to and from your device. This means that even if someone does manage to intercept it, it will be unreadable. This stops hackers from snooping, but it also prevents your ISP, network administrator, or a government agency from tracking what you’re doing online.
When you connect to a VPN, your traffic flows through an intermediary server before reaching its destination. As a result, it appears that it’s coming from a different IP address, and your real IP address is masked. Most VPN providers operate servers all over the world and you can choose the location of the one you want to connect to.
Because of the location spoofing effect, a VPN also enables you to bypass geo-restriction measures put in place by many different types of platforms. This means you can gain access to sites that might otherwise be blocked due to your location. This includes popular streaming platforms like Netflix and Hulu, sports streaming sites, and gambling websites.
There are free VPN services 
Most services will allow you to connect multiple devices — anywhere from three to ten, depending on the provider — under one plan. You can even configure a VPN to your home router so that every connected device is automatically protected.
Wrapping up
Cybercrime is a reality for everyone, not just governments and businesses. By doing your part, you can not only protect yourself and your family, but also help in improving security for the general population. Simply follow the advice in this post, and you’ll be well on your way to becoming a true crusader in the fight against cybercrime.



