As cyber threats continue to increase in both complexity and frequency, organisations require robust security information and event management (SIEM) solutions to detect, monitor, and respond to incidents in real time.
Datadog Cloud SIEM and Elastic SIEM are two leading SIEM platforms, each offering strong capabilities for organisations with different security requirements. Both provide visibility across network traffic, cloud environments, and application logs, helping teams identify anomalies, potential breaches, and system vulnerabilities.
Datadog Cloud SIEM is a cloud-native platform designed to simplify the detection, investigation, and response to security events. It uses machine learning and advanced analytics to highlight unusual behaviour and speed up incident response. With extensive integrations across cloud services and applications, it is particularly well suited to organisations operating in cloud-first environments. Its unified visibility and automated workflows also help streamline security operations.
Elastic SIEM is an open-source solution built on the Elasticsearch platform, known for its scalability and flexibility. It offers highly customisable dashboards and analytics, making it a strong choice for organisations that require greater control over how security data is processed and visualised. Its ability to ingest large volumes of data and perform fast searches makes it effective for detecting and investigating threats at scale.
In this article, we compare Datadog Cloud SIEM and Elastic SIEM, highlighting their strengths and differences to help determine which solution best fits different organisational security needs.
Overview of Datadog Cloud SIEM
Datadog entered the SIEM application market with the launch of Datadog Cloud SIEM in 2020. Datadog Cloud SIEM (Security Information and Event Management) is a SaaS-based solution that provides end-to-end security coverage of dynamic, distributed systems. It is part of the Datadog Cloud Security Platform and is designed to provide a single centralized platform for the collection, monitoring, and management of security-related events and log data from across the enterprise. This enables security teams to identify and respond to suspicious behavior patterns more effectively than would be possible by looking at data from individual systems.
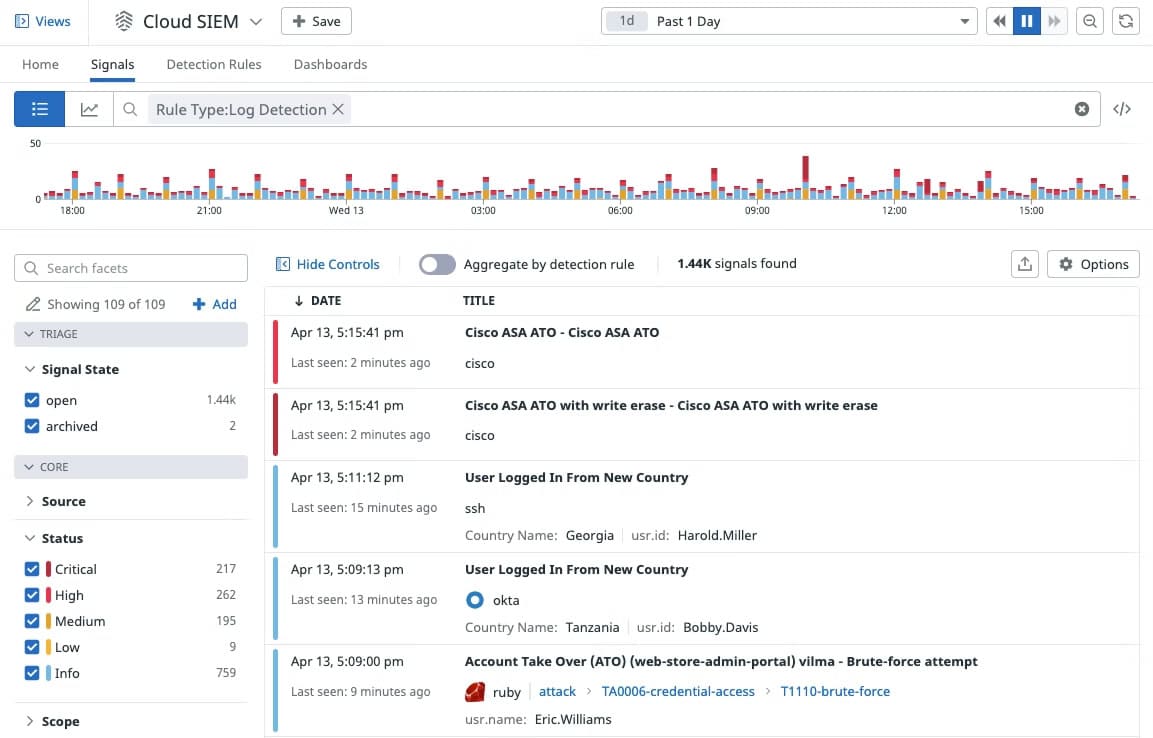
With Datadog Cloud SIEM, you can analyze operational and security logs in real-time regardless of their volume. Developers, security, and operations teams can leverage detailed observability data to accelerate security investigations in a single, unified platform.
Key features and capabilities include:
- Observability and security See all of your security data in one place, and correlate them with runtime events, application and service logs, and more. Development, security, and operations teams can access the same observability data and drive security investigations in a single, unified platform.
- Out-of-the-box dashboards The Security Overview dashboard allows you to have a high-level view of your security posture. The IP Investigation and User Investigation dashboards enable users to correlate specific IP addresses and users with security signals, events, and logs, so they can quickly hone in on malicious activity patterns.
- Out-of-the-box threat detection rules Datadog Cloud SIEM comes equipped with out-of-the-box threat detection rules that don’t require a query language for widespread attacker techniques and misconfigurations that are mapped to the MITRE ATT&CK framework.
- Built-in vendor-backed security integrations Built-in security integrations with AWS CloudTrail, Okta, G Suite, and more enable users to ingest additional security data in minutes, which provides deeper context and helps accelerate investigations.
A free personalized demo and a free 14-day-trial with full access to all the features are available on request. After that, the software is generally sold through monthly subscription plans based on hosts, events, or logs.
Overview of Elastic SIEM
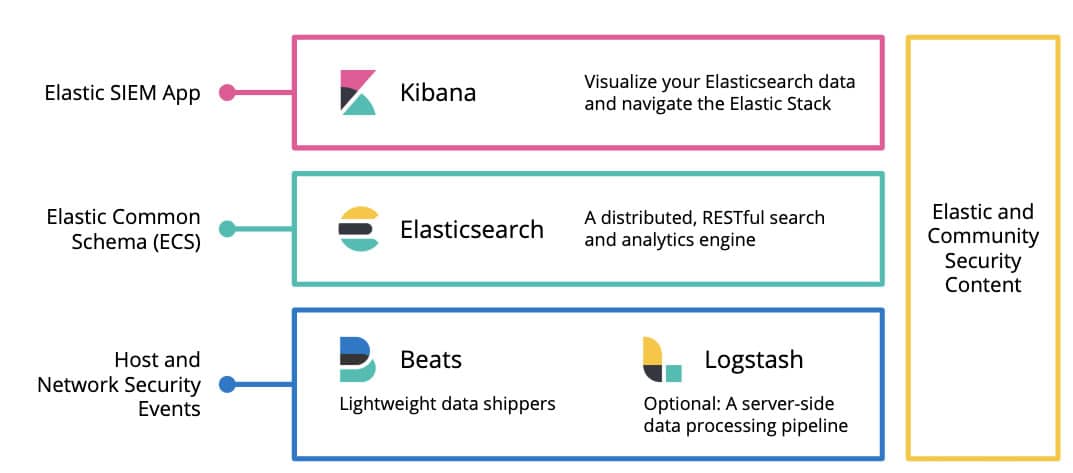
Elastic marked its official entry into the SIEM market with the launch of Elastic SIEM in 2019. Elastic SIEM is an on-premises and cloud-based SIEM solution that enables organizations to detect, investigate, and respond to evolving threats. It is not a standalone product but rather builds on the existing Elastic Stack capabilities used for security analytics including search, visualizations, dashboards, alerting, machine learning features, and more. It provides a single centralized platform to harness, monitor, and manage security-related data at cloud speed and scale from across the enterprise. Because Elastic SIEM correlates data from a wide variety of event and contextual data sources, it can enable security teams to detect and respond to suspicious behavior patterns more effectively.
Elastic Security has been recognized in the 2021 Gartner Magic Quadrant for Security Information and Event Management (SIEM).
Key features and capabilities include:
- Analyze your environment at will Monitor and correlate years of historical data, and access built-in trend charts for key data fields.
- Automate detection with high-fidelity rules Automate detection of suspicious activity and tools with behavior-based rules powered by research from Elastic Security Labs. Detections are aligned with MITRE ATT&CK® and shared openly for review and activation.
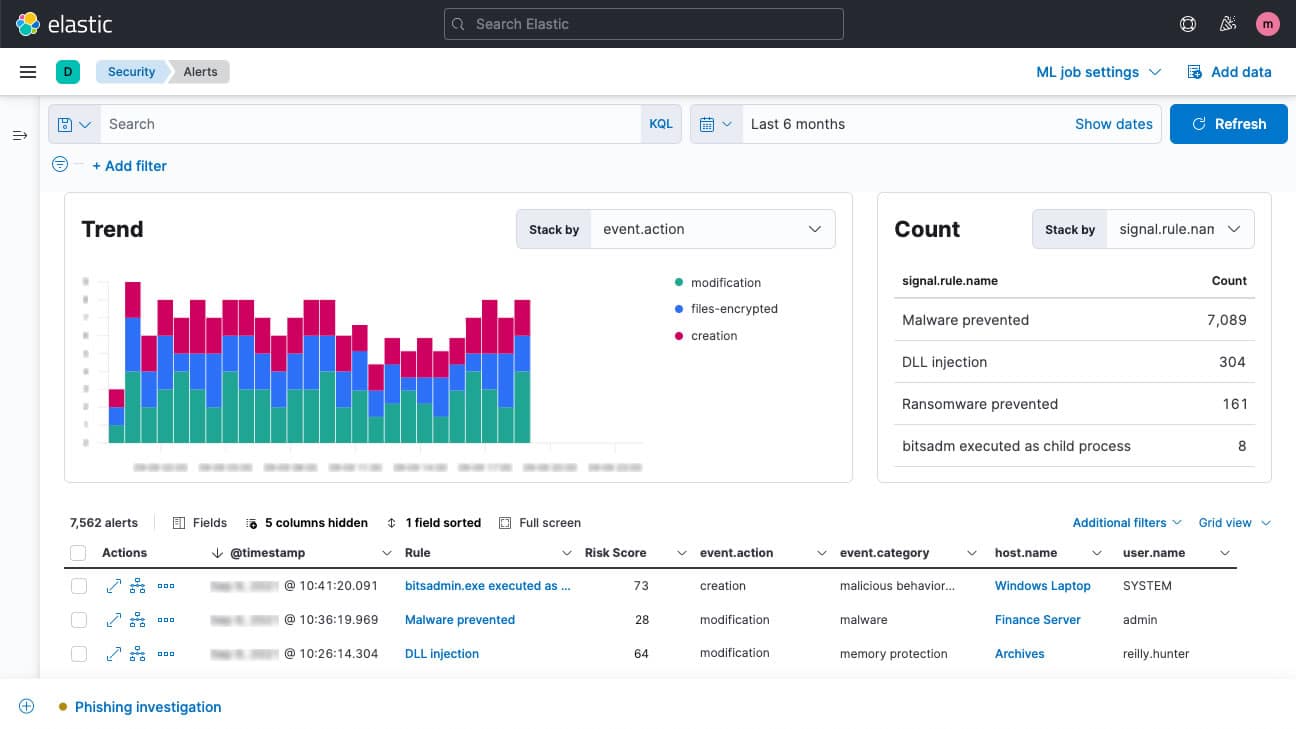
- Assess risk with ML and entity analytics Expose unknown threats with anomaly detection powered by prebuilt ML jobs, and gain insight into the entities at highest risk with security analytics.
- Streamline investigation, automate response Standardize team processes with detailed investigation guides and built-in case management, including SOAR and ticketing workflow integrations.
You can access Elastic SIEM through the Elastic Cloud or by downloading its default distribution. A free Elastic Cloud trial with full access to all the features is available on request with no credit card required. After the trial, you will be required to purchase a valid license to continue using the service.
Datadog Cloud SIEM vs Elastic SIEM: How They Compare
Deployment model
Just as the name implies, Datadog Cloud SIEM is a cloud-based application for cloud-native environments; which means there are no on-premise system requirements and no installation hassles other than the usual sign-up process using an internet-connected device with a supported browser. However, you’ll be required to install local agents specific to the device or service you wish to monitor for the most part. This deployment makes it ideal for organizations that don’t want to burden themselves with any resource-intensive on-premise SIEM solution
On the other hand, Elastic SIEM offers both SaaS-based and self-hosted (on-premises) versions. The SaaS-based version just like Datadog needs no installation other than the usual sign-up process using an internet-connected device with a supported browser. However, you’ll also be required to install a single unified local agent app. The SaaS solution can be deployed in multiple public clouds like AWS, Google Cloud, and Microsoft Azure. Elastic SIEM’s flexible deployment model makes it ideal for organizations that want to have granular control, but it comes at a cost—you also have to manage it yourself.
Data collection and analytics
Datadog Cloud SIEM collects logs from many different sources into Datadog. All ingested logs are first parsed and normalized (reformatted) for consistency, easy correlation, and analysis. This helps to uncover malicious activities on the network, preventing bad actors from concealing their tracks. Once logs are collected, ingested, and processed, they are available in Log Explorer. Log Explorer is where you can search, enrich, and view alerts on your logs. This makes it easy to search and filter log data across your entire infrastructure for threat detection and investigation.
Elastic SIEM allows you to stream logs, metrics, traces, content, and more from your apps, endpoints, infrastructure, cloud, network, workplace tools, and every other common source in your ecosystem. The Elastic Common Schema (ECS)— an extensible field mapping specification that makes it easy to normalize data from disparate sources enables cross-source correlation, search, and analysis. The schema on read feature via runtime fields and searchable snapshots equip organizations to eliminate blind spots and streamline processes. Elastic provides a good-looking user interface where you can access built-in trend charts for key data fields.
Incident/threat detection and mitigation
Datadog detects threats based on rules and creates a security signal. Datadog provides out-of-the-box rules for widespread attacker techniques, mapped to the MITRE ATT&CK framework. Detection rules take full advantage of Datadog’s “Logging without Limits”, which lets you customize what logs you want to index while still ingesting, processing, and archiving everything. Rules apply to the full stream of ingested, parsed, and enriched logs so that you can maximize detection coverage without any of the traditionally associated performance or cost concerns of indexing all of your log data.
Elastic SIEM incident/threat detection exposes unknown threats with anomaly detection powered by prebuilt machine learning jobs. Elastic SIEM automates the detection of suspicious activity with built-in case management, and behavior-based rules powered by research from Elastic Security Labs. Detections are aligned with MITRE ATT&CK and shared openly for review and activation. This enables you to gain insight into the entities at highest risk with threat intelligence and security analytics.
Elastic SIEM also comes with SOAR (Security Orchestration Automation and Response) and ticketing workflow integration capabilities. With SOAR capabilities enabled, organizations can collect data about security threats from multiple sources and respond to low-level security events without human assistance. By automating routine actions, SOAR helps security teams to become more efficient and frees up their time for more demanding tasks.
Notifications and Alerts
Datadog’s approach to alerts and notifications is based on machine learning (ML), which it calls Watchdog. Watchdog uses ML techniques to identify problems in your infrastructure, applications efficiency, and services, and flag anomalies. Alerts in Datadog are called Monitors. Users can receive alerts using Pagerduty, Slack, and email. These can be based on nearly any metric that Datadog can capture. As a result, every alert is specific, actionable, and contextual—even in large and temporary environments. This unique approach to alerts and notifications makes Datadog stand out and helps to minimize downtime and prevent alert fatigue.
Alerts in Elastic SIEM work by running checks on a schedule to detect conditions defined by a rule. When a condition is met, the rule tracks it as an alert and responds by triggering one or more actions. The threat intelligence rules provided by Elastic trigger alerts that attract the attention of network support staff to the SIEM console for further information. The Alerts page displays all detection alerts. From the Alerts table, you can filter alerts, change an alert’s status, and start investigating and analyzing alerts in Timeline. The Alerts page offers various ways for you to organize and triage detection alerts as you investigate suspicious events. Elastic SIEM allows you to extend alerts by connecting them to actions that use built-in integrations for email, webhooks, IBM Resilient, Jira, Microsoft Team, PagerDuty, ServiceNow, and Slack.
Reporting and Integration
Instead of generating the usual out-of-the-box reports that most network admins expect, Datadog’s approach to reporting aims to make metrics easily searchable, and it does excellently. Cloud SIEM is fully integrated with all of Datadog’s application and infrastructure monitoring products, which allows users to seamlessly pivot from a potential threat to associated monitoring data to quickly triage security alerts. Datadog’s 600+ integrations let you collect metrics, logs, and traces from your entire stack
as well as from your security tools, giving you end-to-end visibility into your environment. Datadog integration with Slack and PagerDuty allows you to automatically loop in relevant teams when a high-severity rule detects a threat. You can also export security signals to collaboration tools like JIRA or ServiceNow.
Elastic SIEM reports are used in different segments of a business to analyze, gain insights, and make decisions. Elastic SIEM provides reports that enable organizations to meet compliance requirements for CSA STAR and HIPAA. However, the service isn’t yet fully integrated with SOX or PCI-DSS compliance. Whether your data is in a single cloud, across multiple clouds, or on-premises, Elastic gives you the flexibility to use a variety of data ingestion methods. Elastic SIEM supports integration with over 250 technologies. This allows you to get data from your on-premise and cloud infrastructure, applications, and services into your SIEM platform. Although this is half the number that Datadog supports; nonetheless it doesn’t matter as long as it meets your integration requirements.
Licensing and Price Plans
Datadog Cloud SIEM pricing model is per GB of analyzed logs, per month billed annually or on-demand. An analyzed log is a text-based record of activity generated by an operating system, an application, or other sources analyzed to detect potential security threats. Datadog charges for analyzed logs based on the total number of gigabytes ingested and analyzed by the Datadog Cloud SIEM service.
Elastic SIEM follows a resource-based pricing model that allows you to pay only for resources you consume, independent of the use case. Whether you are using Elastic Cloud or deploying self-managed Elastic software, the core pricing meter for Elastic is based on the underlying resources consumed to run your use case. Elastic licensing is predictable and doesn’t multiply based on data ingest, agent count, or use case. Simply deploy what you need and adapt as your vision evolves.
Choosing Between Datadog Cloud SIEM and Elastic SIEM
Although Datadog and Elastic are two newcomers in the SIEM market, they are certainly not new in observability and logging space—as both have distinguished themselves over the years. Deciding between the duo shouldn’t be about which is better, but about which best meets your business needs. You need to consider a variety of factors such as:
- Is the SIEM solution capable of meeting your organization’s security and compliance requirements?
- How much native support does the SIEM tool provide for relevant log sources?
- Does the SIEM solution possess the capabilities of next-generation SIEM functionalities such as SOAR and UEBA?
- What is the total cost of ownership, is vendor support available in your region, and to what extent?
Datadog’s ability to support and integrate with more than 600 technologies makes it more versatile and adapted to many different functions, provides deeper context during investigations, and lets you cast a wider net to catch possible security issues. However, the lack of SOAR and UEBA capabilities makes it less effective in tackling modern security challenges. Nonetheless, Datadog Cloud SIEM is an excellent tool for existing Datadog customers and organizations that don’t have dedicated IT personnel to keep tabs on the infrastructure at a granular level.
Elastic SIEM’s self-hosted or cloud deployment option gives organizations the flexibility to choose the deployment model most suitable for them. The self-hosted option is ideal for organizations that want to be in complete control, but it will require an investment in skilled human resources to manage it. Elastic SOAR capabilities put it in a better position to collect data from multiple log sources, identify hidden threats, and provide automated responses without human intervention. This creates a more effective defense against modern security challenges.




