Network security is an essential concern for small businesses, especially as the digital landscape continues to evolve and cyber threats become more sophisticated.
Small businesses often face unique challenges when it comes to protecting their data, infrastructure, and networks. Limited budgets, a lack of dedicated IT staff, and insufficient awareness about potential risks can leave them vulnerable to cyberattacks, data breaches, and other security incidents.
This guide is designed to provide small business owners and IT administrators with practical advice and actionable steps to safeguard their networks from potential threats. We offer an overview of key security principles and technologies that can help businesses secure their networks without requiring an extensive security infrastructure. From firewalls and antivirus software to encryption and employee training, the guide covers the essential elements of network security that small businesses need to know.
The guide delves into risk assessment and how businesses can identify potential vulnerabilities in their systems, applications, and processes. It also outlines strategies for establishing strong network defenses, such as configuring secure routers, using VPNs, implementing multi-factor authentication, and maintaining regular software updates. By understanding these core security practices, small businesses can significantly reduce their exposure to cyber threats.
We outline the importance of educating employees about best practices in network security, as human error is often a leading cause of security breaches. By cultivating a culture of security awareness and implementing proactive security measures, small businesses can build a resilient network that supports growth and mitigates risks. Overall, this guide equips small businesses with the knowledge and tools needed to protect their networks.
See also: 30+ free tools for website security
Educate Your Employees on Security Best Practices
Before implementing any new procedures or tools you need to make sure that your employees have a baseline knowledge of potential threats. After all, having elaborate security procedures in place won’t protect you if the staff doesn’t know what they’re doing. In order to prevent a security threat from taking root then teaching your employees a range of best practices is the best way to begin.
Password Management
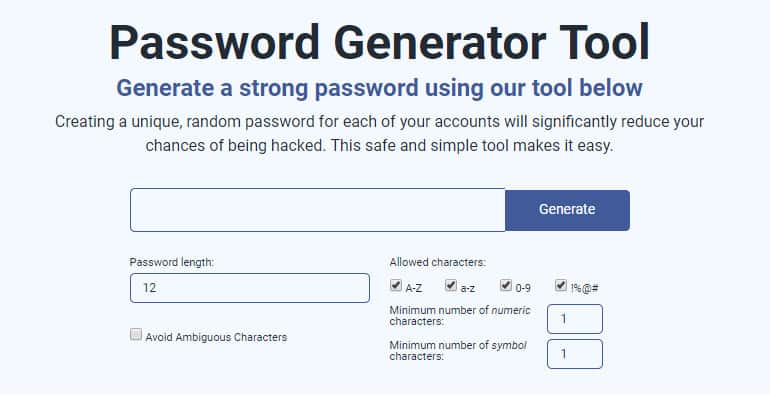
Consider Using A Password Manager Tool
Password management is one of the most important best practices for the staff to follow. It provides the staff with a fundamental way to restrict access to key systems, accounts and services.
Although most computer-literate staff will know about the importance of picking strong passwords, there will be many that won’t or don’t. This means that it is beneficial to take a leading hand and write up some organizational guidelines on password requirements.
Train Staff on Picking Password
When doing this the first thing you want to make clear is that the staff should be using a unique password that isn’t used anywhere else. The password itself should comprise a mixture of uppercase letters, lowercase letters, numbers, and symbols. This will provide you with substantial protection from a brute force hacking attempt.
It is also a good idea to provide information on password storage. Complex passwords are good for cybersecurity, but they are often very difficult to remember. To make passwords easier to remember it can be a good idea to store them within an encrypted password management software solution or app.
Regularly Update Passwords
The final ingredient to successful password management is making sure that passwords are regularly updated. However, there is a right way and a wrong way to encourage this. If you urge staff to update too often you will end up with weak passwords as staff run out of ideas (or motivation!) to keep generating new passwords.
As a general guideline, two to three changes every year should be the minimum. However, a password should always be changed if you suspect it has been compromised or you or a member of the staff is currently using a weak password.
See also: Best Password Managers
Use Two-Factor Authentication
Even though passwords are very important, they aren’t impervious to breaches. A dedicated attacker can run through billions of passwords in a matter of minutes. Many organizations have turned to two-factor authentication as an additional barrier to prevent these attacks from gaining traction.
Two-factor authentication is when you sign into your account and are then prompted to provide a second piece of information to confirm your identity. In most cases, this will be a code that is texted to your mobile phone number or another email address, although it can also be something like a fingerprint as well.
Many companies choose to use physical devices such as key fobs instead that are beyond the reach of hackers. Two-factor authentication makes a hacker’s job ten times harder and is a welcome addition to password security. Online services like Google have started to use two-factor authentication in order to crack down on unauthorized users.
Lock Computers and Devices

One way that the staff can immediately make a business more secure is to lock their computers once they walk away. It seems simple but there are many instances of confidential information being stolen or breached from inside an organization. For example, in the past, Fellowes found that over 250 million business records were reported lost or stolen within a two year period.
Keeping computers locked is one of the best ways to ensure the physical security of your data. Whereas many staff will be aware of the importance of passwords the threats raised by leaving a device open can be overlooked easily. In order to prevent the loss, theft, or destruction of data it is important to make staff aware of the dangers.
Within your cybersecurity policy detail that both computers and mobile phones should remain locked when not in use. While most employees aren’t criminals there is a minority who wouldn’t think twice about accessing private data. You can also set up devices to lock users out after being inactive for a certain amount of time.
Report and Scrub Lost Devices

Controlling access to devices is incredibly important but, in the event, that a device goes missing you need to make sure the staff reports it. Research from EE indicates that employees lose more than 10 million devices every year. This is problematic given that these devices contain important information which can be used by cybercriminals.
The ideal response to this scenario is that a member of the staff will report when a device goes missing so that its data can be destroyed remotely. There are a variety of different software products available that will track or remotely erase data on lost devices. However, these are only effective if the device loss is reported quickly.
Savvy cybercriminals have been known to put a device on airplane mode to prevent data from being erased. As a result, your employees need to respond immediately in order to minimize the damage. The key to making this process run smoothly is to educate staff on the importance of reporting lost devices promptly.
Having all devices installed with software for remote data destruction or tracking and encouraging staff to report quickly will leave you less open to future attacks. Including this information within your cybersecurity policy will also provide the staff with a resource that they can consult for future reference. A cybersecurity policy will make it easier to remember the steps to take in the future.
Use a VPN
When working online, every connection you make is a potential threat. Using a virtual private network (VPN) is a tried and tested method of keeping your data safe from hackers. A VPN encrypts your usage data and hides your IP address so that you can browse anonymously. Within a small business environment, a VPN can keep your data safe when being transferred between employees.
You don’t need to spend lots of money to pay for your own VPN either as there are plenty of VPN service providers available at a competitive price. Encouraging the staff to use VPNs will greatly reduce the potential for cybercriminals to gain access to confidential information and stop them using it to conduct a breach.
See also: Best VPN Services
Ramp up to SASE
Secure Access Service Edge (SASE) is an advancement on the connection security offered by VPNs because it integrates access rights management (ARM). With this combination in one app, you can control the access of users to specific applications. This opens up a new security option that provides unified network protection for hybrid systems. That term means the use of off-site cloud services alongside on-premises resources.
Even very small businesses these days find themselves with the complication of trying to protect connections to cloud services – if you have a subscription to Microsoft 365 or Google Workspace, you are operating a hybrid network.
Fortunately, operating network security for the complexities of hybrid systems is not very difficult. There are many new SASE services emerging that offer cloud consoles and guided setups so you can implement this cutting-edge cybersecurity system with ease. Take a look at Check Point’s SASE, which has created a series of plans that are ideal for small businesses.
See also: Ultimate Guide to SASE and Best SASE Tools
Apply Privacy Settings
Over the past decade or so, many organizations have started to use social media and other online services to enhance their day-to-day processes. This brings with it a new host of vulnerabilities. Every member of the staff who conducts activity online is leaving a digital trail of personal information that can be harnessed for phishing attacks and other malicious reasons.
Any staff using LinkedIn, Facebook, Twitter or Google+ should be advised to keep their privacy settings as high as possible. More specifically, you want them to make sure that only friends can view information such as their birth date or location. Limiting the amount of information available to non-friends helps to minimise the amount of data that can be pulled by cyber attackers.
Stick to Secure File Transfers
Any organization that processes sensitive information such as email addresses and credit card numbers should be using a secure file transfer system. A secure file transfer system will encrypt sensitive information and make sure that no unauthorized users get access to it.
Many organizations use email as a file transfer service. This is far from ideal as these aren’t encrypted. Likewise, file transfer protocols such as FTP are also unencrypted and vulnerable to outside access. There are a number of ways to avoid these threats, including Secure File Transfer Protocol SFTP and email encryption, but the most popular is by using a managed file transfer (MFT) service.
There are a variety of different MFT solution providers on the market. It is advisable to use MFT because it provides you with one of the most efficient and easy ways to conduct secure file transfers.
Keep Your Software Updated
One of your greatest assets against cyber threats is your software. Keeping your software updated against external threats is vital for protecting your service over the long term. In 2017, the WannaCry ransomware attack plagued organizations across the world exploiting a vulnerability that was previously patched in Windows. Organizations could have prevented the attack simply by having up-to-date software.
Unfortunately, the WannaCry attack is unlikely to be the last of its kind. Many malware attacks leverage vulnerabilities left by unpatched software to gain access to a system. Software updates act as a barrier against this by fixing known bugs, security issues, and general vulnerabilities to improve performance and prevent loss or destruction of data.
It is essential that small businesses encourage the staff to keep software regularly updated. Downloading a new software patch and restarting your computer can be the difference between retaining your data or losing it to a cyber attacker. Staff should be informed to patch everything from web-browsers to OS updates.
Much of the software on your computer will need to be manually approved before it can be implemented but in many cases, you can set auto-update to keep you updated when a new patch comes up. It is important to remind the staff that they also need to make sure that their mobile apps are up to date, as these can also be vulnerable to external threats.
Related:
Ransomware statistics 2017-2018
How to prevent ransomware
Run a Penetration Test
Even though having security measures in place is an excellent idea, you never know if your organization can stand up to a cyber attack until it happens. That is why more and more businesses are working with “ethical hackers” to hack into their key systems. These hackers are security professionals who simulate malware and ransomware attacks to test how robust an organization’s cybersecurity measures are.
A penetration test can tell you how well-protected you are against an attack and point to ways for you to improve your overall enterprise security. It will test your current defenses and highlight a new load of vulnerabilities that you were completely unaware of. This is important because it could be these exact vulnerabilities that a cyber attacker decides to target during a real attack.
Once a penetration test has been completed you will be provided with a rundown on all of your current vulnerabilities alongside a list of recommendations for you to implement in order to protect these in future. Generally, these risks are prioritized so you can go after the most pressing issues first.
A penetration test will not only tell you what issues to address but also leave you in a better position for regulatory compliance as well. If you’re in an organization that is affected by the Payment Card Industry Data Security Standard (PCI DSS) then you will need to implement a penetration test in order to comply.
We highly recommend you conduct a penetration test as it is the only way you’ll see if your cybersecurity stands up to the pressure of a real attack. Though the costs can be significant, it can pale in comparison to the costs raised by a security breach and any subsequent downtime or data loss you experience.
See also: Wireshark tutorial
Stay Vigilant!
It can be easy to overlook this step but encouraging the staff to stay vigilant adds another layer of protection. There will be times when even the best cybersecurity features are not enough to prevent an attack. Vigilant staff will act as a last line of defense to stop problems before they occur or to take that initial response once a threat has become apparent.
This means if suspicious activity is spotted locally or virtually, it should be reported to the relevant team member or the IT department. Being proactive about addressing potential threats can be the difference between a threat that slips through the net unnoticed or an attack that causes minimal damage.
Ultimately the effectiveness of this step depends on the execution of your staff. However, if you provide the staff with cybersecurity training and inform them about general best practices then they will have the basics in place to be able to diagnose when a problem is occurring.
The most important thing is to make it clear to the staff that they have a responsibility to ensure the cybersecurity of the business. A team of the staff keeping a collective eye on the cybersecurity of the office can make a monumental difference when it comes to threat response.
See also:
Cybersecurity institutes and associations
Cybersecurity resources: A big list of tools and guides
Respond to Employee Feedback
Finally, one of the most important factors to consider is responding to employee feedback. How effective your cybersecurity policies are all comes down to how well they are executed by your staff. If the staff feel frustrated because current guidance takes up lots of their time, then it is important to respond to this feedback.
Of course, you want to keep a high standard of security measures in place but it is important to be open to suggestions about how processes could be improved. This will not only help to increase staff satisfaction but will also lead to a more nuanced cybersecurity policy as well.
Working alongside your staff makes sure that cybersecurity is taken seriously and your plan doesn’t become outdated and ignored. The worst thing you can do is implement a cybersecurity plan without responding to employee feedback and refining it over time.
Network Security: A Matter of Policy and Implementation
Following the guidance and best practices above will go a long way towards making sure your business and your team are ready to respond to cyber threats. However, it is important to realize that even with all these measures in place threats can still get through. Whether it’s down to human error or a system failure, mistakes happen.
Implementing a well-rounded strategy will help to keep these to a minimum but you can’t prevent them completely. The most you can do is make sure that your staff is aware of cybersecurity best practices and policies; this way they will be more aware of how to prevent and respond to cyber attacks. Ultimately, effective cybersecurity is a matter of policy and implementation.
Above all else, don’t make the mistake of overlooking any aspect of your cybersecurity policy. You never know how or when an attack could strike so don’t be tempted to neglect any part of your physical or virtual security. Your data and your reputation rest on it.