Legal professionals operate in an environment where protecting sensitive information is essential to maintaining client trust and meeting professional obligations. Law firms, in-house teams, and independent practitioners manage large volumes of confidential data, including legal documents, case files, and personal client information, making them prime targets for cyber threats.
Cybersecurity in the legal sector is not solely an IT concern. It requires organisation-wide awareness and responsibility, as lawyers, paralegals, and administrative staff all play a role in safeguarding data. Failing to maintain strong security practices can lead to serious consequences, including reputational damage, financial penalties, and loss of client confidence.
At the same time, legal professionals must navigate an increasingly complex regulatory landscape. Frameworks such as the General Data Protection Regulation (GDPR) and other regional laws impose strict requirements on how sensitive data is handled, stored, and shared. Compliance with these standards is critical, adding another layer of importance to effective cybersecurity measures.
With threats like ransomware, phishing, and data breaches becoming more frequent and sophisticated, legal organisations must ensure their defences are strong and adaptable. Cybercriminals continue to refine their tactics, making it essential for firms to stay ahead with updated security strategies and tools.
This guide explores the key cybersecurity challenges facing the legal profession and outlines practical approaches to addressing them. From securing communication channels and protecting mobile devices to managing third-party risks, it provides insight into how legal organisations can better protect sensitive information in a digital-first environment.
By taking a proactive and informed approach, legal professionals can reduce exposure to cyber risks and ensure that client data remains secure as both technology and threat landscapes continue to evolve.
Examples of cybersecurity breaches in law firms
To illustrate some of the cybersecurity threats legal professionals face, let’s take a look at some real-life examples of breaches that have made the headlines over the past several years.
Cravath/Weil (email hacks)
This 2016 breach involved 48 US law firms, and although they weren’t named, media personnel were able to deduce that Cravath, Swaine, & Moore and Well, Gotshal & Manges were two of the firms involved. The reason for this attack was an insider trading scheme; hackers found out information about upcoming mergers by hacking into merger law firm employees’ emails. They used the gathered data to earn $4 million in the scheme. Three Chinese citizens were charged in the attack.
DLA Piper (ransomware attack)
A June 2017 ransomware attack (using the Petya ransomware) on DLA Piper meant the firm and its employees couldn’t use their phones or access emails for a full three days. The irony of this case was that DLA Piper markets itself as a firm with superior cybersecurity expertise.
Panama Papers (leak by anonymous source)
This case, dubbed the “Panama Papers,” made major headlines in 2016 and beyond as more than 11.5 million documents belonging to Panamanian law firm Mossack Fonseca were leaked to the public. Aside form revealing attorney-client privileged information, including financial data, illegal dealings by the firm were exposed. It had created shell companies for use in tax evasion and fraud, and to evade international sanctions.
The fallout of the leak by a still unknown source affected not just the firm, but many public officials and wealthy individuals as well. The Icelandic Prime Minister at the time resigned due to the leak.
A similar breach occurred at law firm Appleby in 2016, exposing many prominent people (including the Queen of England) to accusation of tax evasion and similar crimes. This breach was nicknamed the “Paradise Papers.”
Thirty Nine Essex Street (watering hole attack)
A watering hole attack is a specific type of targeted security exploit. Attackers reach a group of end users by compromising a site that they are known to frequent. In 2014, UK law firm Thirty Nine Essex Street found itself in the center of a watering hole attack. Although it’s unknown what method they used, hackers managed to compromise the firm’s website. They were then able to infect visitors to the site, with the end targets being the firm’s various energy sector clients.
Trust Account (phishing scam)
This 2012 scheme was an unwelcome Christmas present for a Toronto law firm. Using a phishing scam, hackers accessed the firm’s trust account via the company bookkeeper’s computer. It’s believed the bookkeeper clicked on a seemingly harmless email attachment which downloaded a virus onto the computer.
The virus, known as the Trojan banker virus, had the ability to mimic a bank’s website. Through this trick, the bookkeeper unknowingly handed over the password to the law firm’s trust account. Once the hackers had access to that, they were able to steal funds. It wasn’t until days after the attack that the firm noticed it was missing a six-figure amount from the account.
WordPress (content management system hack)
While many attacks target law firms specifically, this was more widespread, but did affect a number of law firms. A flaw in a WordPress addon released in 2016 allowed hackers to bypass WordPress authentication measures. This gave them access to the admin panels of WordPress websites and enabled them to change the contents of web pages. Law firms as well as companies in other industries were left with defaced pages and missing content.
Bad check scams
While this isn’t an individual example, bad check scams are rife in the law industry so are certainly worth a mention here. Law firms are often involved in transactions between various accounts on behalf of clients. In many cases, clients will send their lawyer a check and the lawyer will wire funds, often to a foreign account. With large sums of money passing through these types of transactions every day, they offer an ideal opportunity for fraudsters.
In a bad check scam, one of these transactions takes place as normal, except the original check sent by the client turns out to be a fake. The problem is that fake checks usually aren’t discovered right away and the wire transfer will have taken place prior to the discovery, putting the lawyer out of pocket for the funds.
Cybersecurity best practices for law firms
As you can see from the above examples, no one is immune to cybersecurity threats. Here are the main steps you can take to protect you and your clients:
- Have a cybersecurity strategy and communicate it
- Use strong passwords (and a password manager)
- Use a firewall and antivirus software
- Watch out for phishing emails
- Look out for other suspicious emails and popups
- Use a VPN
- Secure physical devices
- Back up data securely to the cloud
- Use encrypted communications
- Get an SSL certificate
- Vet new software with extreme caution
- Browse securely
- Search securely
- Consider a hosted virtual desktop
- Tighten network security
Let’s go into each of these in more detail:
1. Have a cybersecurity strategy and communicate it
Careful planning is key and it’s important for law firms to have a solid and well-researched strategy in place for cybersecurity. Waiting for a significant breach to happen before putting things into action is a poor, reactive strategy.
Ensure all things are covered in the plan, including which security services and software should be used and protocols for dealing with information securely on a day-to-day basis. Note that for many firms, the use of third-party security companies is necessary for things like penetration tests, vulnerability scans, and malware scans.
You also need to think about worst-case scenarios and what course of action you will take in case of a breach. Have a response plan and test it. Develop and test incident response, business continuity or disaster recovery plans, and communications plans.
As important as having a plan is making sure all staff are fully trained. While there’s a lot of common sense involved in cybersecurity, educating staff about risks and general best practices is crucial.

2. Use strong passwords (and a password manager)
Most password best practices are common sense. Use a different password for every account and create long passwords that are hard to guess. They should have a mixture of upper and lowercase letters, numbers, and symbols, and definitely avoid using the most commonly used passwords (you can find the top 500 on our password manager page).
However, with so many accounts required for various applications, it can be difficult to remember all these passwords. A password manager can help you with that. It will remember all of your passwords, and autofill features mean they’re automatically entered in the appropriate site.
This means you don’t have to remember your passwords or store them in your browser (which is a big no-no from a security standpoint). Password managers can also help you detect phishing sites as they won’t autofill forms on unknown sites. Some popular options include Sticky Password, LastPass, and Dashlane.
Aside from using strong passwords, you might also want to consider two-step verification (2SV). Some applications have this built in but there are also third-party applications you can use to enforce 2SV. With this, you need to verify your password login by a secondary means, such as by entering a code sent by text message or email.
There is also two-factor authentication (2FA) which uses something physical for the secondary authentication step. This may be a biometric verification method such as a retina scan or fingerprint, or it could involve a device like a keycard or fob. Yubico is one company that specializes in such devices.
3. Use a firewall and antivirus software
While you will likely need additional security, using the basics such as enabling your firewall and using a good antivirus software can still help greatly.
A firewall works by acting as barrier between your network or computer and the internet. It closes ports to prevent communication with your device. You can do this manually, but a firewall will close all ports, simplifying the process. Aside from stopping threats like malicious programs sent by hackers from entering your computer, it can prevent data leaving.
Software firewalls are often built into a device, but some can be purchased separately, such as Comodo and TinyWall. Hardware firewalls can also be purchased separately but often come built into routers.
Antivirus software can help protect against viruses and other forms of malware by detecting and often removing the threat.
There are free antivirus software options available, but they are typically limited and the paid alternatives don’t cost that much anyway. Some popular options are Bitdefender and Kaspersky.
See also: Best free firewalls
4. Watch out for phishing emails
Hopefully, you and your colleagues have your wits about you when it comes to various online scams, but with hackers and other cybercriminals becoming more savvy, it’s increasingly important to know what to look out for.
Phishing attacks involve someone gleaning information using social engineering. An attacker poses as a trusted authority figure to trick victims into handing over passwords or financial info. Attacks may take place via phone, SMS, or email, and might involve links to phishing websites (fake sites designed to look legitimate in order to steal your information). Information they may be looking for include financial data or login credentials to various accounts.
Special forms of phishing include spear phishing (where the attack is targeted toward an individual or group) and whaling (targeting executives and other senior management personnel). If someone in the organization were to fall for these types of attacks, it would pose a serious cybersecurity risk.
Phishing is less likely to be successful if you’re in the practice of using digital signatures to authenticate the source of an email and to verify that no one has tampered with it. Digital signatures use public-key cryptography and are nearly impossible to forge (the private key of the sender would need to have been compromised).
5. Look out for other suspicious emails and popups
Not all malicious emails involve phishing and many are designed to get you to download malware onto your device. Malware covers all sorts of computer issues, including viruses, Trojans, ransomware, and spyware. These can cause a range of effects: for example, ransomware holds your files hostage until you pay a fee or some other form of payment. Spyware is designed to reside on your computer without your knowledge and record activities, often by taking screenshots or logging keystrokes.
The problem is that malware can be very easy to download (for example, by simply clicking the wrong link in a popup up or email) and you might not know its there. As such, it’s crucial to watch out for potentially dangerous emails, popups, or sites, and employ the use of strong antivirus software that can detect when malware is present.
6. Use a VPN
A Virtual Private Network (VPN) is excellent for securing the data traveling to and from your device. It encrypts all of your internet traffic, making it unreadable to third parties, including Internet Service Providers (ISPs), government agencies, and hackers.
VPNs are especially useful in prevention against man-in-the-middle attacks where a snooper intercepts your web traffic to steal or alter information. These are common attacks over public wifi networks which are known for their poor security. While you should avoid sending sensitive information over public wifi networks, if you do have to do it, use a VPN.
Bear in mind that when you use VPN, the provider itself will still be able to view your activity. However, reputable VPN providers don’t keep logs of activity or any information that can be tied to an individual. Look out for true no-logs or zero-logs policies when shopping for a VPN.
VPNs can be installed on individual devices (including smartphones and tablets) or they can be configured to routers to protect every device connected to a network. Many providers have special business and enterprise packages geared towards companies large and small.

For larger companies, such as law firms with multiple offices, a site-to-site VPN can be useful. This will secure connections between sites and extend the company’s network such that digital resources in one location are available in other locations.
7. Secure physical devices
It’s possible to have your phone, tablet, or laptop stolen from just about anywhere, and of course, sometimes we just lose things. As such, it’s important to secure your devices as much as possible.
Keep every device locked when not in use with a password, PIN, or pattern. Where available, make sure you have finder apps such as Find My iPhone or Find My Device installed and enabled. Not only can these help you locate a lost device or determine if it has been stolen, they can also help you remotely lock or erase your device.
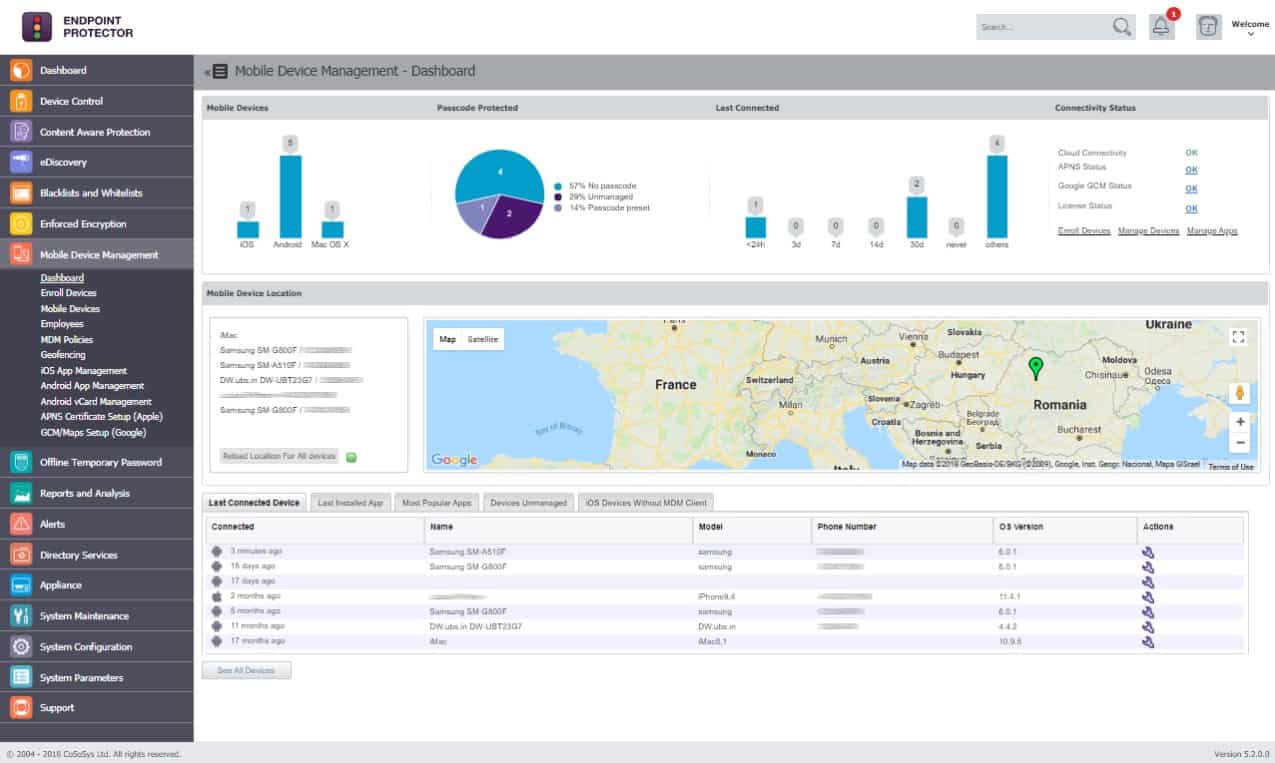
For enterprise-owned devices, Mobile Device Management (MDM) might be a good option. Solutions including ManageEngine Mobile Device Manager Plus and AirWatch Workspace ONE give you control over a network of devices. They enable you to manage access (including remote locking and erasing), secure communications, and limit the risk of malware. There are also Mobile Application Management (MAM) tools (often bundled in MDM software) that give you control over the delivery of software to devices.
If, for some reason, devices need to be left unattended somewhere, such as at a library or even at the office, you might want to consider a physical lock. Kensington locks and those produced by similar brands can secure your device by inserting into a special hole. These are mostly suitable for laptops or desktop devices, although there are options for tablets (think of those point-of-sale locks).
In case someone does manage to steal your device or has access to it when you’re not around, full disk encryption can ensure that the contents are unreadable to anyone without the decryption key. BitLocker and Veracrypt are two popular options for full disk encryption.
8. Back up data securely to the cloud
As a legal professional, it’s vital that the information you have digitally stored remains safe. Physical threats such as fire or theft or cyber threats like a virus or ransomware attack could put everything at risk.
One way to ensure the safety of your data is to ensure it’s constantly backed up. While a physical hard drive might be preferred for particularly sensitive information that you wouldn’t trust a third party with, these still have their downsides, in that they are also at risk of physical damage or theft.
The other option is to back up data to the cloud. Using the right service, cloud backup can be secure and convenient. Popular options are IDrive, CrashPlan, and Backblaze. All of these services encrypt files by default, but for an extra layer of security, you may want to consider encrypting data before you send it to the cloud.
If you do decide to keep sensitive information on your device, it’s a good idea to password protect individual files as well as the device itself.
9. Use encrypted communications
We’ve talked about securing stored data and general web traffic, but what about communications? Face-to-face meetings are generally the most ideal in terms of privacy. Of course, the identity of the participants in the meeting could be exposed by security camera footage or GPS tracking data. But short of a hidden recording device being present, the contents of the meeting should remain private.
While in-person meetings are generally more private, there are no doubt countless occasions when phone calls, messages, and emails are more appropriate or convenient. Thankfully, there are options to help you make all of these forms of contact far more secure. For VoIP and messaging systems, some secure options include Signal, Threema, Telegram, Viber, and Dust.
For email, you can use Hushmail; this encrypts the contents of your email, but metadata such as the subject line, sender and receiver names, date, and time will still be visible. You can use it alongside a disposable email address such as one from Guerrilla Mail or Mailinator. You just sign up for an account anonymously and delete it when you’re done.
If you need to send files securely, then encrypted email will have limitations in terms of file size. Instead, there are special methods you can use to send files securely. Secure File Transfer Protocol (SFTP) involves the use of a Secure Shell (SSH) server that can understand FTP commands. Both SolarWinds and Rebex offer free SFTP servers, while Syncplify.me has a paid alternative.
For enterprise users, Managed File Transfer (MFT) may be a better solution for secure file transfers. MFT tools are strictly regulated and offer a high level of security and greater control over communications, transfers, and workflow. Cornerstone MFT is one popular option and the company offers a 30-day trial to see if it’s a good fit.
10. Get an SSL certificate
Obtaining an SSL certificate and implementing HTTPS is good for business for a couple of reasons. First, it lets the user know that the website is authentic, so they can rest assured they’re not visiting a fake site.
Second, it encrypts the traffic going between the website and the user. This makes it unreadable to any third parties who may be attempting to snoop. This could be ISPs or government agencies monitoring user activity or hackers implementing man-in-the-middle attacks.
SSL certificates are fairly simple to obtain through authorities like Cloudflare, Let’s Encrypt, and Comodo.
11. Vet new software with extreme caution
While we’ve recommended a lot of software in this post, it’s important to treat any new software with caution. As part of your security protocol, new digital products and services should be researched and reviewed. Even if the application itself isn’t corrupt, there’s a chance it has security vulnerabilities that could enable a hacker to get through. Here are some tips:
- Go with reputable applications that offer long-term support and updates. If you have the resources, review software codes on all web-based applications
- Ensure that staff know they are not to download applications on any devices that are used for any work-related tasks. Everything should be reviewed prior to installation.
- Develop security contracts for outside vendors and applications that have access to the firm’s network.
- Keep all software up to date. Updates often patch security holes that could otherwise leave you vulnerable to attack.
12. Browse securely
Your browsing and search history can give away a lot of information about you, your client, or the case you’re working on. Browsing securely is a little more complex than it ought to be, but it is possible. Private browsing mode might seem like a good option, but this really just hides your history from anyone who has access to your device.
You could use a private browser such as Comodo Dragon or Epic Privacy Browser, but these are limited in functionality. What’s more, you can get the same level of security by deleting cookies.
A more superior option is the Tor browser which encrypts your data and sends it through multiple computers (called nodes) run by volunteers. It does come with its downfalls, including offering a slow browsing experience, but it is considered the best option for browsing anonymously. This is especially true if you use it along with a VPN.
There’s also the option to browse Tor via a “live” operating system, such as Tails. To use it, you run a CD or USB and boot the OS onto your device. There’s no installation process required, which means that once you shut down, there’s no trace of activity on your device.
Deleting the DNS cache and disabling HTML Web storage are other steps you can take to make browsing more secure. Privacy extensions such as ScriptSafe and NoScript can help too.
13. Search securely
As a legal professional, no doubt you’ll use private logins to access much of your research materials, but there are probably still countless occasions where a good old Google search would deliver a wealth of information. Of course, Google and other popular search engines like Bing track and store your search history, so can never be considered secure.
All it would take is one or two searches to unwittingly disclose information about your case. You can change your settings within these search engines to limit the amount of information stored. And you can view and erase your past search history for Google and Bing by visiting the individual sites. Or you might consider forgoing these platforms altogether in favor of a more private alternative.
Although we don’t hear about them as much as the above search engines, there are more private options. For example, StartPage by Ixquick and DuckDuckGo don’t track your activity at all, so could never share it with others. And since they don’t track your activity, as a bonus, you won’t have to deal with ads.
14. Consider a hosted virtual desktop
A Hosted Virtual Desktop (HVD) — also known as a Virtual Hosted Desktop (VHD) or Desktop as a Service (DaaS) — can help boost cybersecurity and make it far easier to work remotely or on the go. Providers include Citrix and Amazon.
A HVD essentially gives you a PC setup, but without the need for an actual PC. An entire copy of your desktop is stored on a HVD provider’s servers (in the cloud) and is accessible from anywhere. It includes all applications that you’d find on the device so you don’t need to worry about installing software on multiple devices and multiple users can have access to the same desktop.
Because the virtual desktop is accessed through the cloud, it’s isolated and protected from things like USB ports, wifi networks, and the device camera. What’s more, the provider takes care of all updates, storage, backups, and more. This means many of the security best practices you’d normally have to carry out are done for you.
There are downsides to using a HVD, including having to trust your information with a third party. Practical problems arise too, with latency and bandwidth increases cited as two major concerns. There are also complex licensing issues when you have multiple users and devices.
15. Tighten network security
This mostly applies if you have control over company security and are responsible for ensuring that employees are not able to accidentally or intentionally access or leak information. There are a couple of things you can do to tighten overall network security.
The primary target of data thieves is personally identifiable information (PII). As a legal professional, you should know the severe legal costs attached to PII disclosure. Data Loss Prevention systems protect you from damaging PII leakage.
There are a number of potential enemies in the fight to protect data. You can have disgruntled or bribed workers, who are categorized as an “insider threat.” Data thieves practice intrusion and aim for PII. An example of a suitable DLP tool is Endpoint Protector by CoSoSys.
Another way to avoid information falling into the wrong hands is to implement Network Access Control (NAC) software that affords the administrator granular control over who can access what, including when they can access resources and from which device. This is particularly helpful when a company employs remote workers or operates a Bring Your Own Device (BYOD) system.
Image credit: “Lady Justice” licensed under CC BY 2.0