It seems like every time we read the news these days, there is another report of a serious data breach that affects millions of people and their personal information.
So, how often do data breaches happen, how serious is the issue of data breaches and what impact does it have on individuals and businesses? In this article, we reveal the most interesting, recent data breach statistics and facts. The results are highly disconcerting.
We’ll also discuss the laws surrounding cybersecurity and data breaches, and consider what individuals can do to protect themselves against the effects of a data breach. Let’s get to the facts.
Data breach statistics and facts
We’ve collected the most interesting data breach statistics and facts from recent studies:
1. Cybersecurity as a business risk
Businesses increasingly consider cybersecurity a critical business risk, not just an IT issue. This shift in mindset is highlighted by Gartner’s findings, which emphasize the integration of cybersecurity into core business strategies. Companies focus on approaches like human-centric design and zero-trust architecture to align cybersecurity efforts with broader business objectives. For a more in-depth understanding, check out the report from Cyber Magazine.
2. Cyberattacks via third parties
Cyberattacks through third-party services are rising, posing a significant challenge for businesses. The interconnected nature of modern organizations with external vendors, cloud services, and SaaS applications increases the complexity of managing cybersecurity risks. Addressing these challenges requires a proactive strategy for risk management, as emphasized by recent guidelines and regulations. You can read more at Security Boulevard for detailed insights into these challenges and strategies.
3. 56% of customers now actively show an interest in a company’s cyber-resilience
New data reveals that in 2022 cybersecurity is becoming a social phenomenon. Consumers are increasingly contacting companies to ask them about their cybersecurity, and to ask what their risk exposure might be if they decide to use that company’s service or product.
According to the latest research from Gartner, 56% of customers frequently express interest in the cybersecurity of the organizations they do business with.
4. 45% of US companies have experienced a data breach
The 2021 Thales Data Threat Report found that almost half (45%) of US companies suffered a data breach in the past year. But this could be higher due to the potential for as yet undetected breaches. Interestingly, the same number of respondents had noticed an increase in the scale, frequency, or sophistication of these attempts. This figure is a reduction from 2019 when 65 percent of companies had experienced a breach.
5. California has suffered more data breaches than any other state in a 15-year period
A Comparitech study looked at the number of data breaches experienced by companies in each state, as well as the corresponding number of records exposed. California was by far the front runner with 1,777 breaches and 5.6 billion records exposed between 2005 and 2020. In second place was New York with 863 breaches and 295 million records exposed. Third place went to Texas with 819 breaches and 294 million records exposed.
6. The US suffers from the most data breaches
As reported by Cobalt, in 2023, the United States continued to have the highest cost of a data breach at $5.09 million. Globally, the average cost of a data breach in 2023 was $4.45 million, marking a 15% increase over three years.
7. One of the first 2020 data leaks involved 250 million records
Microsoft got off to a bit of a poor start in 2020. We reported in January that it had suffered a massive leak of data involving more than 250 million customer support logs dating back more than a decade.
Comparitech uncovered the data leak alongside security researcher Bob Diachenko in late 2019, although Microsoft didn’t disclose the breach until January 2020. Information contained in the logs wasn’t particularly sensitive in nature, although customer logs could prove very valuable to tech support scammers.
8. At least four 2020 breaches involved over a billion leaked records
While the Microsoft breach was a big one, it was by no means the largest. Other notable breaches in 2020 involved CAM4 (10.88 billion records), Advanced Info Service (AIS) (8.3 billion records), and Keepnet Labs (5 billion records). Of course, there’s also the SolarWinds breach that was discovered in December, the full fallout of which is yet to be determined.
2021 data breaches did not seem to be as severe as they were the year before. The biggest data breaches in 2021 were:
- Comcast (1.5 billion)
- Brazilian resident data leak (660 million)
- Facebook (533 million)
- LinkedIn (500 million)
- Byeka (400 million)
9. Companies that have experienced a breach underperform the market by more than 15% three years later
Another Comparitech study examined the share prices of 34 companies listed on the New York Stock Exchange that had experienced major data breaches. We found that after 14 market days (roughly three weeks from the date the breach was made public), share prices had dropped by 3.5 percent on average. Although share prices tend to recover after that, when we looked at long-term results, we found that the share prices of affected companies didn’t keep up with the NASDAQ average. One year after the breach, companies underperformed the NASDAQ by 8.6 percent, and after three years, companies were underperforming the NASDAQ by 15.6 percent on average.
10. 62% of companies in the Americas have experienced a data breach within the last year
A 2022 KPMG survey of senior risk executives found that 62% of companies in the Americas experienced a data breach or cyber incident in 2021, and that same number say they experienced an economic loss as a result of cyber crime in the past year. This shows that there can be regional differences in the level of data breaches, as this figure is higher than it is for the US alone.
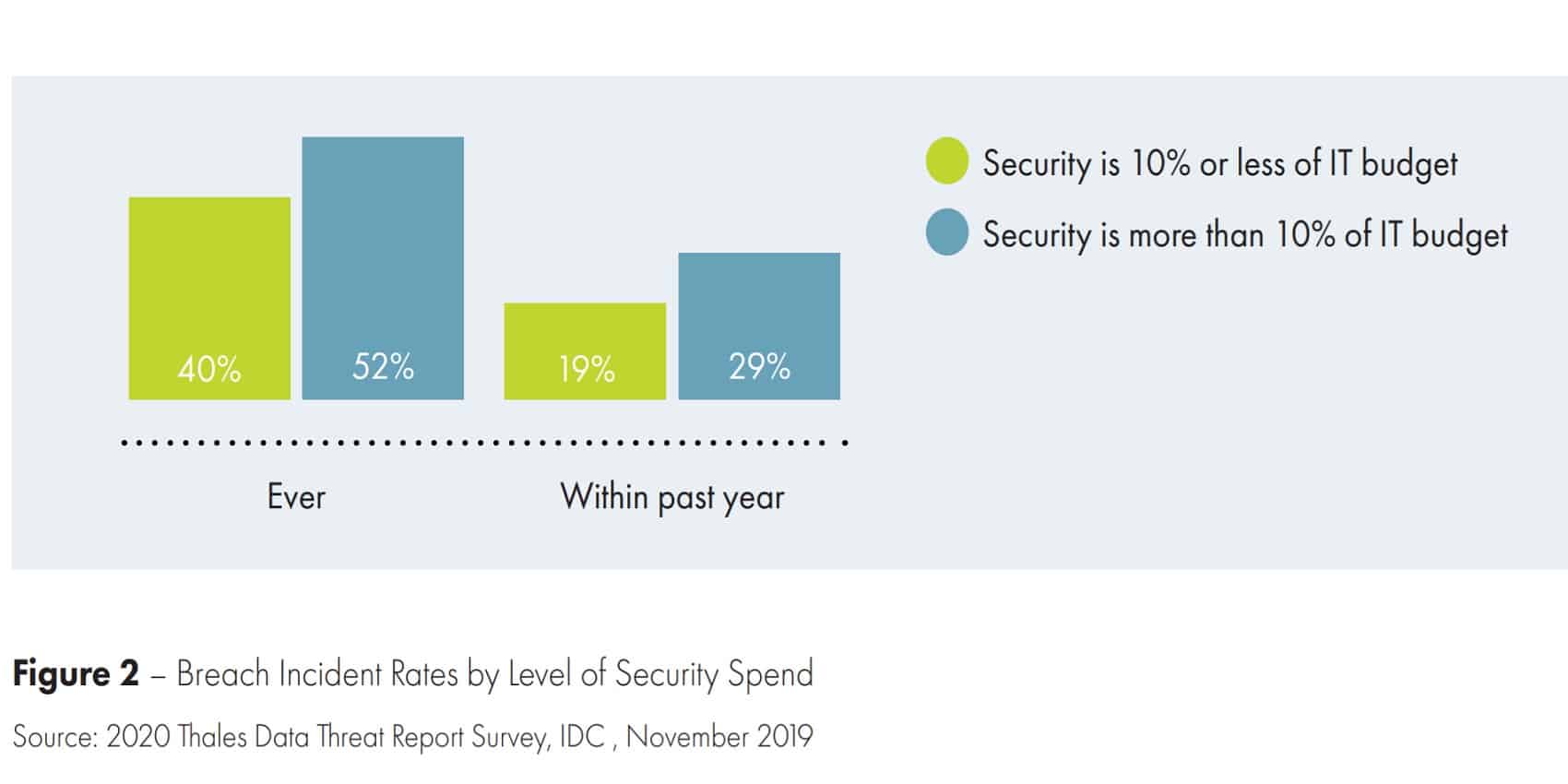
11. In 2020, 50% of organizations spent only 6–15% of their security budget on data security
One of the key findings of the Thales study was that despite the massive threat that data breaches represent, many organizations aren’t allocating much of their budget to securing data. However, newer research from Gartner shows that worldwide spending on data security increased by 17.5% between 2020 and 2021, indicating that organizations are taking the threat of data breaches more seriously.
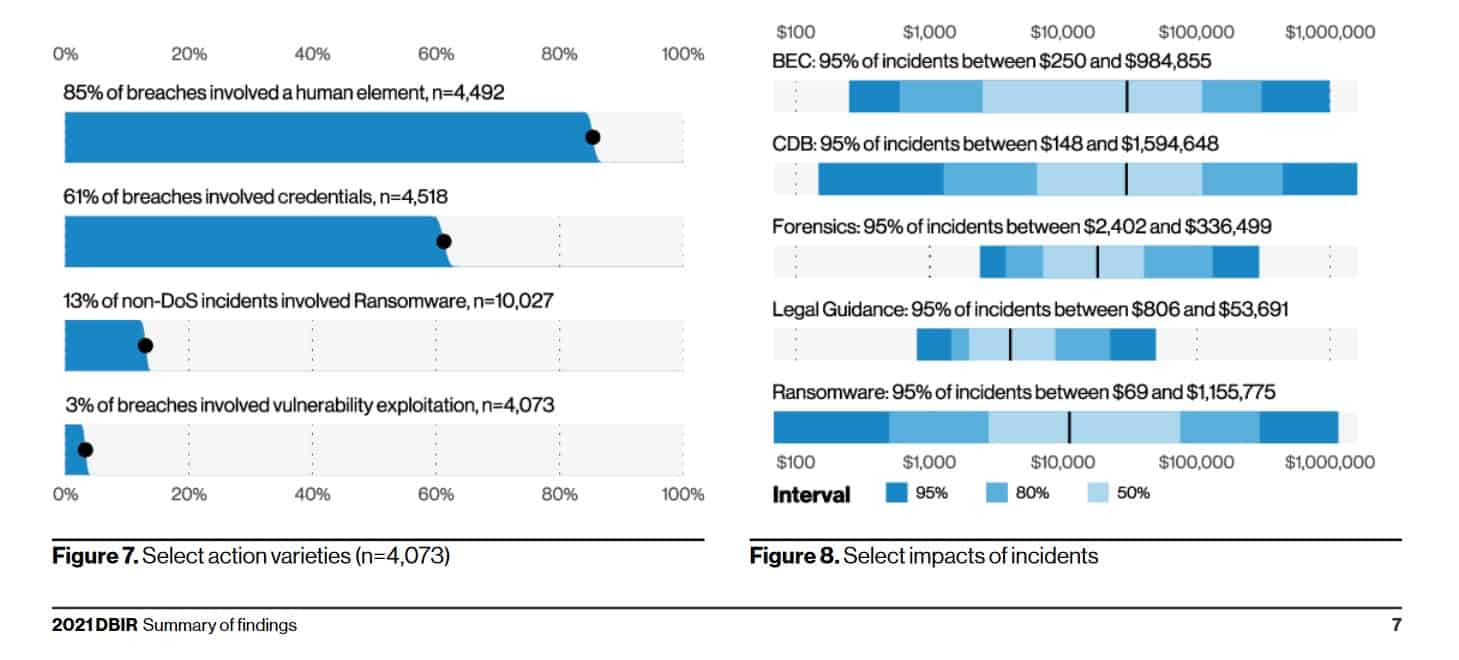
12. 28 percent of data breaches affected small business victims
The Verizon 2021 Data Breach Investigations Report is based on analysis of more than 79,000 security incidents, including over 5,200 confirmed data breaches. It provides us with a trove of interesting facts, including that in over 60% of cases, stolen credentials were used.
See also: Improving cyber security for small businesses
13. 7 out of 10 cloud infrastructures are breached within a year
The State of Cloud Security 2020 report by Sophos noted that large breaches involving the cloud are becoming commonplace. 70 percent of IT professionals reported their cloud infrastructures experiencing a breach in the year prior. The report reveals that most cloud computing security incidents have one of two root causes. They are either the result of stolen or phished credentials, or misconfigurations have led to the breach.
According to a 2022 report from Fugue, 36% of 300 cloud engineering and security professionals surveyed say their organization suffered a serious cloud security leak or breach in the past year.
14. Organized crime groups are responsible for 80% of breaches
The Verizon report also offers insight into who is responsible for attacks. Interestingly, more than 75% of breaches entail organized crime groups. Also of note, less than 5% involved internal personnel or outsiders. Not surprisingly, well over 70 percent of data breaches are financially motivated.
15. 22% of data breaches entail phishing attacks
In its study, Verizon sought to discover how breaches occur and found over one-third involve phishing attacks, around 25 percent entail hacking, and 17 percent center around other miscellaneous forms of hacking, such as ransomware.
16. Discovery time for 60% of data breaches is weeks or longer
Wondering how long it takes for companies to discover and react to breaches? The Verizon report reveals it’s not as quick as you’d like, especially considering stolen credentials are involved in over 60% of breaches. With more than half of companies taking weeks to discover a breach, by the time a company issues an email blast telling customers to change their passwords, it could already be far too late.
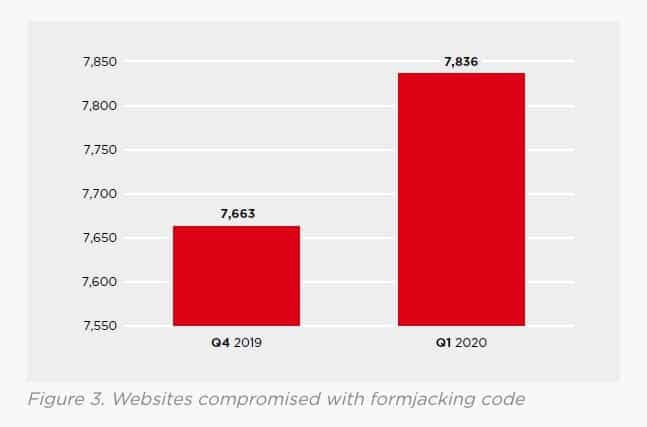
17. Almost 8,000 websites per quarter are compromised with formjacking code
Formjacking involves criminals using JavaScript code to hijack website payment forms such as those found on ecommerce sites. Also referred to as digital card skimming, it’s used as a means to steal credit card information as well as other valuable data. According to Symantec Threat Landscape Trends – Q1 2020, there were 7,836 sites compromised via formjacking in Q1 2020. This was up compared to 7,663 in the previous quarter.
18. Enterprise ransomware attacks are on the rise
Ransomware attacks (which hold files or systems hostage) represent a huge threat to data security. According to the Symantec Security Summary – April 2021, ransomware payments jumped 171% in 2020, with the highest payout doubling to $10 million.
The statistics from Symantec also found that firmware is becoming a more popular target for attackers. One contributing factor is that, despite 80% of organizations experiencing a firmware attack in the last two years, over 20% of respondents said that their firmware data wasn’t monitored.
19. The average price of a stolen payment card is $13 in the underground economy
2022 research from NordVPN analyzed information from 135,000 British cards sold on the dark web, finding that the average price of a British payment card is £11.06 ($15). This is more expensive than the world average of £9.70 (around $13).
According to reports from 2020, a cloned card with a PIN can sell for $15-$35 with American Express details being the most valuable. Meanwhile, online banking credentials for accounts holding $2,000 or more can sell for $65.
20. Gmail account credentials are worth an average of $156
While this figure seems high, it makes sense when you consider that many people link other accounts to their Gmail account. As such, Gmail access could enable an attacker to reset the passwords on any connected accounts.
21. The number of data breaches soared in 2021
According to the Identity Theft Resource Center (ITRC), the number of data breaches in the first nine months of 2020 dropped 30 percent compared to the same period in 2019. The number of individuals impacted was over 292 million, down 60 percent from 2019. One possible reason for the drop is that as organizations moved to a remote-work model as a result of the pandemic, they became more aware of cybersecurity issues and tightened practices.
However, the Identity Theft Resource Center, in its 16th annual Data Breach Report, finds that the number of data breaches at corporations was up more than 68% in 2021, beating the previous record rise in 2017 of 23%.
22. $4.24 million is how much the average data breach in the US costs
The IBM 2021 Cost of a Data Breach Report highlighted that 2021 saw the highest average cost of a data breach in 17 years, rising from $3.86 million in 2020 to $4.24 million.
Individual breaches are becoming costlier and entail the loss or theft of an increasingly high number of consumer records. This cost includes things like lost business, notification costs, and other damages.
23. Compromised credentials caused the most breaches
The same IBM study found the most common initial attack vector, compromised credentials, was responsible for 20% of data breaches at an average cost of $4.37 million.
24. Remote work due to COVID-19 increased cost
The average cost was $1.07 million higher in breaches where remote work was a factor in causing a breach, compared to those where remote factor was not a factor, according to IBM.
25. Security AI had the biggest cost-mitigating effect
IBM noted that automation and security artificial intelligence (AI), when fully deployed, offered the biggest cost mitigation: up to $3.81 million less compared to organizations that lacked security AI.
26. A zero-trust approach helps reduce cost
In the latest report from IBM, we find that the average cost of a breach was $1.76 million less at organizations with a mature zero trust approach in place, compared to organizations without zero trust.
27. Cloud migration impacts costs and containment
The IBM researchers also discovered that organizations further along in their cloud modernization strategy were able to contain a data breach on average 77 days faster than those in the early state of their modernization journey.
28. Social engineering attacks are the gravest threat to public administration
The Verizon report underscored that social engineering attacks (a type of cyber crime where the attack fools the target through impersonation) account for 69% of all public administration breaches.
29. Almost two-thirds of companies leave more than 1,000 sensitive files open for anyone
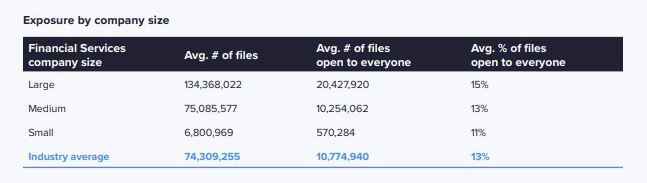
The 2021 Varonis Financial Services Data Risk report examines Data Risk Assessments conducted by Varonis engineers, to determine the extent of exposure of critical and sensitive information within financial services organizations such as banks, insurance firms, and investment companies.
One area of interest is the number of folders that are open for anyone in the company to view. Varonis found that 13 percent of folders are open to everyone.
But perhaps more concerning is when sensitive files are left open. Sensitive files include those containing things like credit card information, health records, or regulated information such as that subject to GDPR, PCI, or HIPAA. Varonis found that in 64 percent of financial services companies, every employee has access to more than 1,000 sensitive files. Indeed, the study found that 15 percent of all sensitive files are accessible by any employee.
30. Employees of large organizations can access 20 million files
Varonis found that in 2020, each employee has access to an average of 11 million files. For large organizations, this number is almost double at 20 million.
31. In 2021, the number of individuals impacted by data breaches was down slightly
The Identity Theft Resource Center (ITRC) examines publicly-available data breach disclosures and released its key findings for 2021. It found that nearly 294 million people were impacted by data breaches. This is a decrease compared to the over 300 million individuals impacted by publicly reported data breaches in 2020.
However, this figure has to be contextualized. While the number of individuals impacted has decreased slightly, the number of total breaches has increased, and substantially. In 2021, there were 1,682 breaches at US corporations, an increase of 754 over the previous year.
32. Customer PII is the most common and most expensive type of record lost or stolen
Data from IBM shows that in 2021, customer personally identifiable information (PII) was included in 44% of breaches and the average cost per customer PII record was $180.
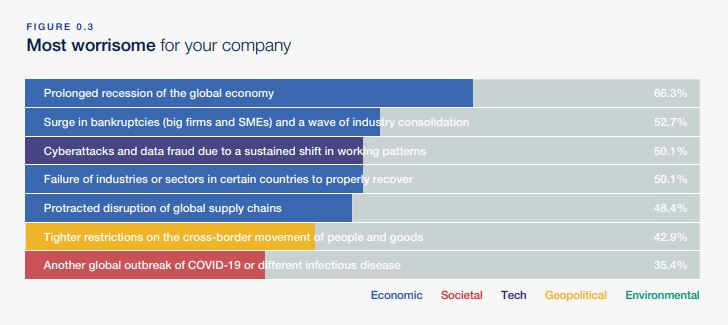
33. Cyberattacks and data fraud are named as some of the biggest global risks
The World Economic Forum Insight Report 2020 outlines the biggest global risks, including natural disasters and weapons of mass destruction. Cyberattacks and data fraud rank as third in terms of the most worrisome for companies (ahead of infectious disease concerns) and eighth in most likely fallout for the world.
34. 58% of organizations don’t acknowledge data breach disclosures
Comparitech security researchers regularly scan the internet for leaked databases and then provide disclosure to the organization responsible for the data. The team undertook a study to determine the response time to these disclosures. 23 percent of organizations responded within a day, 12 percent within two days, and two percent within three days. A further five percent took four to 17 days respond. Surprisingly, more than half (58 percent) never sent a response at all.
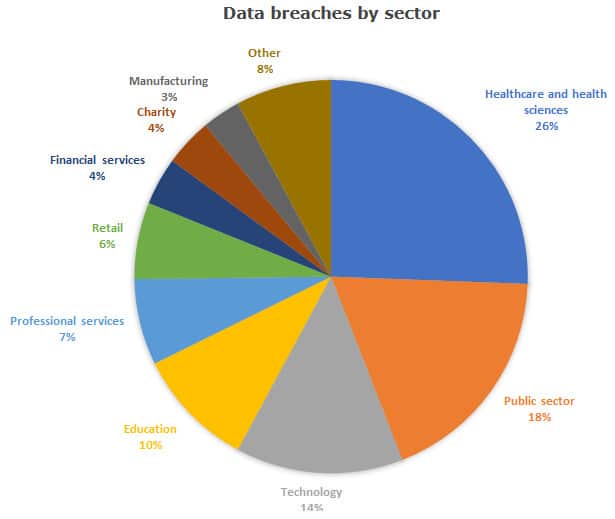
35. Healthcare was the most vulnerable sector in Q1 2022
IT Governance produced a Q1 2022 report on data breaches which found that healthcare and health sciences encountered the highest number of breaches, accounting for 26% with 65 breaches. It was closely followed by the public sector, accounting for 18% of incidents (47).
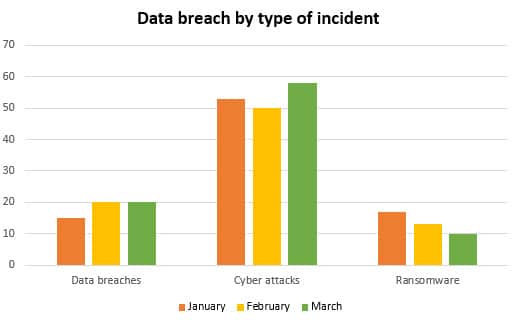
36. Cyberattacks were the most common breach type in Q1 2002
The report from IT Governance continued, stating that cyberattacks remain the most common type of data breach, as has been the trend for the past year. Of all publicly disclosed incidents, cyberattacks account for 61% (161 attacks) of incidents.
37. 93% of attacks successfully penetrate a corporate network
An alarming study from positive Technologies has shown that in 93% of cases, an external attacker can hack into a corporate network successfully. The study was conducted among financial organizations, government bodies, IT, industrial, fuel, and energy companies.
38. In 2021, cyberattack attempts increased by 50%
Checkpoint reported that cyberattack attempts were up 50% in 2021 versus 2020. Checkpoint defines a cyberattack as a phishing attempt, malicious file downloads, command and control attempts, exploiting vulnerabilities, and malicious website access. In the study, all attempts were prevented.
Reporting of data breaches
Until fairly recently, it was common to learn of a data breach well after it took place. We might learn of a massive breach months or even years after the fact. In some cases, this could be because the company itself did not discover the breach for a long time. However, in other cases, it has come to light that businesses have hidden breaches or the facts surrounding them, in order to prevent damage to the company’s reputation.
For example, in 2017, it was revealed that Uber had covered up a 2016 data breach affecting 57 million customers. In October 2018, Google admitted to a data breach affecting half a million users that had begun three years prior and was discovered in March 2018. And as recently as April 2021, personal data pertaining to over 350 million Facebook users was publicly posted in an online hacking forum.
Obviously, not notifying customers about a breach represents a huge privacy threat as they won’t know to take measures to mitigate any potential damage. For example, if you know your password has been breached, then you’ll change your password.
In order to protect citizens’ right to know when their privacy has been breached, many countries now have firm laws in place mandating what companies need to do in the case of a discovered data breach. These laws center around reporting of the breach and notifying customers, but may also cover things like how breach information should be recorded and stored.
For example, at the end of 2018, Canada made changes to The Personal Information Protection and Electronic Documents Act (PIPEDA), outlining exactly how organizations subject to the act need to react to a data breach. Also in 2018, Alabama became the final state in the US to enact a data breach notification law. More recently, 2021 saw a number of data protection bills and laws passed across numerous international jurisdictions.
See more statistics:
What can individuals do about data breaches?
Individuals are heavily dependent on companies to safeguard their information. They also trust that they will be notified immediately after a breach is discovered. That being said, there are some steps you can take to safeguard your data:
- Use strong, unique passwords: This way, even if someone has your username or email, it will be difficult for them to break into an account. Long strings of letters, numbers, and symbols are a good idea. Passwords should also be unique to each account in order to prevent hackers from using a breached account’s login information on other accounts, an attack known as credential stuffing. You can use a password manager to help you generate and remember passwords.
- Adhere to warnings: If you hear about a breach in the news or receive a notification from a company you deal with, act right away. Change your password immediately and find out what information may have been breached so you can take action. For example, if your credit card number may have been leaked, you might want to replace it.
- Watch out for phishing emails: Although you should take breach notifications seriously, note that this could also be a tactic used by cybercriminals. Fraudsters may send phishing emails (under the guise of password reset emails) that lead to fake (phishing) sites designed to steal information such as login credentials. If you get a password reset email, ensure it’s legitimate by checking for common signs of a phishing email, such as a misspelled company name or poor grammar. You can skip the links and go directly to the company website to change your password.
- Look for secure sites: When carrying out online activities, especially those involving financial or personal information, ensure you’re using a trusted website (one that begins with HTTPS://). Even if you spot a good deal, it’s not worth handing over your payment information to a company that isn’t going to safeguard your data.
- Use a VPN: Avoid things like online banking and shopping when connected to public wifi networks. Using a VPN can encrypt your connection and keep your data safe from hackers and other snoopers, even on unprotected wifi. We particularly recommend NordVPN.
- Use Two-Factor Authentication (2FA): If your credentials are exposed in a data breach, 2FA or Two-Step Verification (2SV) can prevent a criminal from accessing your account. You’ll be required to enter a one-time code sent to your phone or email upon logging in.
- Use have I been pwned?: Sign up to this website to get a quick notification in case your email address has been involved in a data breach. Note you need to sign up separately for every email address you use.
- Monitor your accounts: You can’t always trust that a financial institution or payment platform will catch something awry with your account. Check statements regularly to make sure no one has access, and check your credit report to ensure no new accounts have been opened in your name. Don’t forget to check loyalty and reward accounts too; these are often forgotten but can be of great value to criminals. Identity theft protection services can automate some of these checks.
Typical signs of a data breach
Signs of a data breach can vary depending on the type of attack, but some common indicators could alert you to an incident.
- Unusual activity in user accounts: Signs of compromised user accounts include login attempts from unusual locations or devices, creating new accounts without your knowledge, and changes to existing account information.
- Unusual network activity: If your monitoring systems detect unusual traffic patterns or an increase in outbound data transfers, this could signal that data is being exfiltrated from your network.
- Increase in website errors: An increase in website and web application errors can sometimes indicate malicious activity, such as an attack on your systems.
- Suspicious emails and attachments: If you receive suspicious emails containing unexpected or unusual attachments, this could signify a phishing attack, which is often used in data breaches.
- External reports: With the rise of media coverage and regulatory requirements around data security, you may hear reports of a data breach before you even notice the signs. It’s essential to respond quickly and thoroughly when you receive such information.
These are some common signs indicating a security incident or data breach. Regularly monitoring your systems and responding quickly to suspicious activity can help protect businesses from cyberattacks.
Data breach statistics FAQs
What are the most dangerous types of data breaches?
Two of the most dangerous types of data breaches are undetected and those involving malicious actors. Both can potentially cause significant damage if not addressed quickly and efficiently. Undetected data breaches are often caused by human error, such as leaving a password unprotected or sharing confidential information with the wrong people. These breaches can go unnoticed until it’s too late, leading to financial and reputational loss.
On the other hand, malicious actors actively target organizations to steal confidential data, often for nefarious reasons. Using sophisticated techniques such as malware and phishing attacks, these attackers can access sensitive information without detection. The consequences of such breaches can range from identity theft to even more significant risks like state-sponsored espionage.
What is the most significant data breach in history?
Cyber criminals made history when the Yahoo! Data Breach hit in 2014. Affecting 500 million users, the hackers had managed to swipe a whole host of information such as names, email addresses, phone numbers, and even encrypted passwords from the company’s servers.
Though investigators determined that it was a group based out of Eastern Europe that had been rifling through Yahoo!’s system for two years before being caught, the severity of this breach can’t be ignored. It serves as an important reminder to all companies on how essential digital security measures are – something Yahoo! found out the hard way when they were forced to shell out a record $100 million in damages following their data breach. Needless to say, they’ve taken steps since then to better protect user data.
I've received a suspicious email saying my account has been breached. What should I do?
If you’ve received a suspicious email saying your account has been breached, don’t panic – just take action! Start by reviewing the email address and website to ensure they look legitimate. If not, delete it immediately and never provide any personal or financial information in response. If it’s real, log into the account, change your passwords, and take additional security measures like setting up two-factor authentication. But above all, stay vigilant – hackers only take one slip up to gain access to your accounts.
What types of data are most commonly targeted in data breaches?
Data breaches are a serious threat to personal and organizational security. During an attack, cybercriminals aim to acquire sensitive information, such as names, addresses, social security numbers, and financial details. They may also seek access to login credentials, email addresses, medical records, and intellectual property. The type of information targeted can vary based on the attacker’s objectives and the targeted organization. It is imperative to take measures to safeguard all sensitive information to prevent data breaches from occurring.