Encryption probably isn’t something that you spend a lot of time thinking about, but it’s a fundamental aspect of your online safety. A range of encryption types underlie much of what we do when we are on the internet, including 3DES, AES, and RSA.
These algorithms and others are used in many of our secure protocols, such as TLS/SSL, IPsec, SSH, and PGP. In this article, we will discuss what encryption actually is, what it does, some of the key concepts behind it. We will give you an introduction to these major types of encryption and the secure protocols that use them.
What is encryption?
Encryption is essentially a code used to hide the contents of a message or data. It’s an ancient technique, but the old methods are far simpler than what we use today. The earliest encryption methods tended to involve either changing the order of the letters, or substituting letters with other characters.
An example of an early encryption cipher would be to swap “a” with z”, “b” with “y”, “c” with “x” and so on. The key to this code is the knowledge that each letter is swapped with the one that holds its opposite position in the alphabet. Under this kind of code, “Don’t tell anyone” would become:
Wlm’g gvoo zmblmv
Over time, particularly in the 20th century, people got much better at breaking these codes, so it became important to come up with more difficult codes. The advent of computers made cracking codes once thought complicated quite trivial. Many early computers were used for military code breaking.
Things were further complicated by the rapid growth of digital communication and its complex security needs. Now, sophisticated types of encryption form the backbone of what keeps us safe on the internet.
Symmetric-key encryption
Symmetric-key encryption.
The first type of code we’ll introduce is called symmetric-key encryption. It involves a single key to both encrypt and decrypt the data. The code mentioned above would be a very simple form of symmetric-key encryption, because the cipher (a=z, b=y, c=x, etc.) can be used to both encrypt and decrypt information.
The versions we use today, like 3DES and AES, are far more complex. They involve adding a key to the data as well as many rounds of substituting and transposing it using complex mathematical formulas. These algorithms make the final ciphertext look completely alien from the data that it’s supposed to represent.
As an example, when we encrypt “Don’t tell anyone”, with a key of “Notapassword” into an online AES encryptor, it gives us:
W3qpPyoTpri24JsOAv3oYUti/Sbi/LTcpuRvk0DZISY=
As you can see, this looks nothing like the original message, and it is far beyond the capability of anyone’s brain to figure out the cipher. Given a sufficient key-length and the correct implementation, it’s also unfeasible for computers to break AES, so we consider it safe to use in our current technological climate.
Symmetric-key cryptography is great to use when just one person needs to encrypt and decrypt data, or when multiple parties have an opportunity to share the key beforehand. While it’s useful in a number of situations, there are others where it can be problematic.
What if someone wants to communicate securely with someone that they’ve never met before? They obviously wouldn’t have had a chance to share the key beforehand, and they probably don’t have a secure channel that they can use to send the code through to their intended recipient. This brings us to the other major type of cryptography, public-key encryption.
Public-key encryption
Public-key encryption is also known as asymmetric encryption because it requires one key for encrypting data and another for decrypting it. If you need to securely exchange information with someone you haven’t previously had an opportunity to exchange keys with, public-key encryption algorithms like RSA give you a way to do it.
Each user generates a key pair, made from both a public and private key. The public key is shared openly, while the private key is kept secret as a password. Due to a complex mathematical relationship between the two keys, once data has been encrypted with a public key, it can only be decrypted by its matching private key.
To send a message with this type of encryption, the sender must first seek out their recipient’s public key. They encrypt the data with this public key and then send it to the recipient. Even if the data is intercepted by an adversary, it cannot be read without the private key. The recipient then decrypts the message with their private key, and if they would like to respond, they seek out the public key of their correspondent and repeat the process.
Public key encryption is slow and resource-heavy. Rather than using it to encrypt whole files, it is generally used to encrypt symmetric keys that are in turn used to encrypt files. Since the public-key encryption keeps the symmetric key locked-up, and the symmetric key is needed to open the files, only the person with the corresponding private key can access the encrypted data.
What can encryption be used for?
Encryption can do far more than just secure data from prying eyes. It can also be used to prove the integrity and authenticity of information using what is known as digital signatures. Encryption is an important part of digital-rights management and copy protection as well.
Encryption can even be used to erase data. Since deleted information can sometimes be brought back using data recovery tools, if you encrypt the data first and throw away the key, the only thing that can be recovered is the ciphertext and not the original data.
Where is encryption used?
You may not notice it, but unless you live in the woods, you probably encounter encryption every day. Most of the connections you make to major websites will be encrypted with TLS indicated by HTTPS and/or a padlock in your web browser’s URL bar. Your WhatsApp messages are also encrypted, and you may also have an encrypted folder on your phone.
Your email can also be encrypted with protocols such as OpenPGP. VPNs use encryption, and everything you store in the cloud should be encrypted. You can encrypt your whole hard drive and even make encrypted voice calls.
A vast amount of our communication and finance systems use encryption to keep our information secure and away from adversaries. Encryption is also a key aspect of securing cryptocurrency wallets, an important part of protecting the Tor network, and it is used in many other technologies as well.
See also: PGP Encryption
Which type of encryption is the most secure?
This is somewhat of a trick question for two separate reasons. The first is that there are many different types, each with their own uses. It wouldn’t make sense to compare something like RSA to AES, because they solve different problems.
The second issue is that “most secure” doesn’t necessarily mean best or most practical. We could make each of our algorithms many times more secure by simply using larger keys or repeating the algorithmic process.
The problem with this approach is that these hyper-secure algorithms would be incredibly slow and use a ridiculous amount of computational resources. This would make them unusable. The recommended algorithms are those that hit the sweet spot between security and practicality.
Currently, the gold standards for secure yet still practical algorithms are:
- AES-256 — For symmetric-key encryption
- RSA-4096 — For public-key encryption
Each of these ciphers use large keys (256 and 4096 bits respectively) to make them more secure.
Major encryption algorithms
There are many different encryption algorithms. Some are designed to suit different purposes, while others are developed as the old ones become insecure. 3DES, AES and RSA are the most common algorithms in use today, though others, such as Twofish, RC4 and ECDSA are also implemented in certain situations.
According to Microsoft’s SDL Cryptographic Recommendations for 2022, all other block ciphers, including RC2, 2-Key 3DES, DES, DESX, and Skipjack, “should only be used for decrypting old data, and should be replaced if used for encryption.”
3DES encryption
The Triple Data Encryption Algorithm (TDEA), more commonly known as the Triple Data Encryption Standard (3DES) is a symmetric key algorithm that gets its name because data passes through the original DES algorithm three times during the encryption process.
When security issues in DES started to become apparent, they were mitigated by running the data through it multiple times with three keys in what came to be known as 3DES. Each of the keys is 56 bits long, just like in DES. By themselves, keys of this size are considered insecure, which is why DES was retired from use. By applying the encryption algorithm three times, 3DES is much more difficult to break.
When we put our message, “Don’t tell anyone”, with a key of “Notapassword” into an online 3DES encryptor, it gives us:
U2FsdGVkX19F3vt0nj91bOSwF2+yf/PUlD3qixsE4WS9e8chfUmEXw==
3DES has three different keying options, but the only one that is allowed by the National Institute of Standards and Technology (NIST) involves three independent keys. While this gives it a key length of 168 bits, meet-in-the-middle attacks (pdf) effectively reduce the real world security to 112 bits.
3DES is still used in finance, some Microsoft offerings, and a variety of other systems, but it looks like it is set to be retired in the near future. According to the second draft of Transitioning the Use of Cryptographic Algorithms and Key Lengths, “After December 31, 2023, three-key TDEA [3DES] is disallowed for encryption unless specifically allowed by other NIST guidance.” This is because 3DES is quite slow and isn’t considered safe compared to other algorithms.
AES encryption
The Advanced Encryption Standard (AES) was developed to replace the DES algorithm as technological advances began to make DES more insecure. It is actually a type of Rijndael block cipher that was selected to be the standard by NIST after years of evaluating it against a cohort of rival algorithms.
AES features three different key sizes, 128-bit, 192-bit and 256-bit. The key size determines whether there will be 10, 12 or 14 rounds of the encryption steps. The process starts with key expansion, which is where the initial key is used to create new keys that will be used in each round. Then the first round key is added to begin encrypting the data.
After this, the rounds begin. These involve substituting bytes, where each byte of data is replaced with another, according to a predetermined table. After this comes shift rows, where each row of data is moved a set number of spaces to the left. The next part of a round is mix columns, where a formula is applied to each column to further diffuse the data. Finally, another round key is added.
These four steps then repeat for either nine, 11, or 13 rounds, depending on whether 128-bit, 192-bit or 256-bit keys, respectively, are used. The AES encryption process is finished by substituting bytes and shifting rows once more, then adding the last round key. The final result is the ciphertext.
As we saw at the beginning of the article, when we entered our message of “Don’t tell anyone” with a key of “Notapassword” into the 128-bit AES online encryptor, it gave us:
X59P0ELzCvlz/JPsC9uVLG1d1cEh+TFCM6KG5qpTcT49F4DIRYU9FHXFOqH8ReXRTZ5vUJBSUE0nqX1irXLr1A==
The AES algorithm is used to secure a vast amount of our data both at rest and in transit. Some of its more common applications can include:
- WinZip
- VeraCrypt
- Signal
- TLS
- SSH
AES is also approved by the U.S. Government for encrypting classified information:
- SECRET data can be encrypted with 128-bit keys.
- TOP SECRET data can be encrypted with either 192-bit or 256-bit keys.
There are a number of known side-channel attacks that affect various implementations of AES, but the algorithm itself is considered secure.
RSA encryption
RSA was the first asymmetric encryption algorithm widely available to the public. The algorithm relies on the difficulty of factoring primes, which allows its users to securely share data without having to distribute a key beforehand, or have access to a secure channel.
As a public-key encryption scheme, its users encrypt data with the public key of their intended recipient, which can only be decrypted with the recipient’s private key. RSA is slow and uses a lot of computational resources, so it is generally only used to encrypt symmetric keys, which are much more efficient.
Due to the nature of RSA’s system of public and private keys, we can’t encrypt a text message with the same “Notapassword” key that we used above. Instead, we will give you a demonstration with a random public key from another online generator. When we encrypt “Don’t tell anyone” with the following public key:
—–BEGIN PUBLIC KEY—–
MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQDPLfAcyE5w+6qQE6W5g2vmX55v
q9rsMqP4QWrYS1UMAVJ4DTYLT09d0MR00yxBn6f3wvJkxQXihTnsSKvtO09Ld4/f
LGIeoYvulzp73mvPtIO2wjzP6eb0ndM42CAnxVtzzWmFXH3AYvCQ0AK+OJnJQVZ4
GgimzH4wwO9Uc6bEawIDAQAB
—–END PUBLIC KEY—–
We get:
G7qrc4WRKADzcc1a9tdFHTas8bsV2rQqgBuxQJ2O8Uvf++t/Ss8DBe+7kDWgSXqKGOytkYKX/DjMLUJnTxd2iVQeDF4my8O9Gl9bnUN+OlH1e5dy6QnyEcrk+3GtAynHW3+BK4fa7ypnJFEG6/R9E9w5eAn49nAR12w5NxsbCoo=
The above message can only be decrypted back to its original form with the following private key:
—–BEGIN RSA PRIVATE KEY—–
MIICXwIBAAKBgQDPLfAcyE5w+6qQE6W5g2vmX55vq9rsMqP4QWrYS1UMAVJ4DTYL
T09d0MR00yxBn6f3wvJkxQXihTnsSKvtO09Ld4/fLGIeoYvulzp73mvPtIO2wjzP
6eb0ndM42CAnxVtzzWmFXH3AYvCQ0AK+OJnJQVZ4GgimzH4wwO9Uc6bEawIDAQAB
AoGBAK5C4XgUM4Zs6GYPYJHNrPA09TrQvm91mN2ziH8tvfc/FXLNCewxZXxvoQ7y
oIMCG3IWk3OXFQAXN0U7SwFbpbE8G7J0xXftTj9nxGjb0NL3zJrJcg+VUjQ8P63F
EsEFh6tqur2j/sYQIFsgQuJ6b4gPdaLJ6rK7tVPIQ2G/TlABAkEA9wkTgdnpm9a5
3uxpUGB+pq4pAteVhWcHlWxRyEpC6Fv+D/QOkB+fkG0HUPnmGDS0HiYOYMSHL91r
dND2iHXGawJBANaymut04nAQzWhj/Vb1KSY1UjN5i7j1NZ4b2E8MWZht90exk0NY
0wxnqFR8SIHMtUnWqRIqVijEcIa7ETRmegECQQCEMmA1CecglS0MZZkKAUllayfZ
NIL4S6VcSgYN1+esLqZr5R/x8mpSQHY82C5Q38tPou/oyuLJM4Vwku6LIfOXAkEA
tQEXAvMkBH7l7eB+sVU3P/MsPiF23pQ8g/PNxbcPwibTlynqkZjNNWQe0juFlYjU
PlAvchUnVm9mvu/vbVIIAQJBALQXwqZXfQIftvBmjHgnoP90tpN4N/xcIqMTX9x3
UZVFWPERBXfklGTOojPYO2gVVGZWr2TVqUfV3grSno1y93E=
—–END RSA PRIVATE KEY—–
RSA is often used in TLS, it was the initial algorithm used in PGP, and it’s often the first algorithm that someone turns to when they need public-key encryption. Many VPNs rely on RSA to negotiate secure handshakes and set up encrypted tunnels between servers and clients. RSA is also used to create digital signatures, which verify the authenticity and integrity of data.
A number of vulnerabilities have been discovered in various implementations of RSA, but the algorithm itself is considered safe as long as 2048-bit (or larger) keys are used.
Read our full guide on RSA Encryption
Security Protocols
The remainder of this article isn’t about encryption algorithms like those we have just discussed. Instead, they are secure protocols, which use the above encryption algorithms to keep our data safe in a number of different situations.
TLS/SSL
Transport Layer Security (TLS) is still often referred to by its predecessor’s name, Secure Sockets Layer (SSL), but it is really an updated version of SSL with a range of security enhancements. TLS is one of the secure protocols that you will encounter most frequently. Whenever you see “https” or the green lock next to a URL in your web browser’s address bar, you know that TLS is being used to secure your connection to the website.
It differs from the three systems mentioned above in that TLS isn’t an encryption algorithm, but a protocol that has become an Internet Standard for securing data. This means that TLS isn’t the mechanism that does the encrypting; it uses algorithms like RSA, AES, and others to do that.
TLS is simply the agreed-upon system that is used to protect data in a range of situations. TLS can be used to encrypt, authenticate and show whether data retains its original integrity.
It is most often used over transport layer protocols such as HTTP (what we use for connecting to websites), FTP (what we use to transfer files between a client and a server) and SMTP (what we use for email).
Adding TLS to these protocols secures the data being transferred, rather than leaving it out in the open for anyone who intercepts it to access. On top of allowing your web browser to securely connect to a website, TLS is also used in VPNs for both authentication and encryption.
TLS is comprised of two layers, the Handshake Protocol and the Record Protocol. The Handshake Protocol is used to initiate the connection. When the connection is being established, the client and server decide which version of the protocol will be used, authenticate each other’s TLS certificates (certificates that verify the identity of each party), choose which algorithms will be used for encryption, and generate a shared key through public-key encryption.
The Record Protocol then secures the data packets being transferred with the shared keys that were generated in the Handshake Protocol. Symmetric-key encryption is used to make the process much more efficient.
On top of encrypting data, the Record Protocol is charged with dividing the data into blocks, adding padding, compressing the data and applying a message authentication code (MAC). It also does all of these processes in reverse for data that is received.
Like all protocols, over time a number of flaws were discovered in SSL, which led to the development of TLS. TLS features a range of additions that bolstered security, but it has continued to be updated over time. TLS 1.3 was defined in August 2018, but version 1.2 is still commonly used.
IPsec
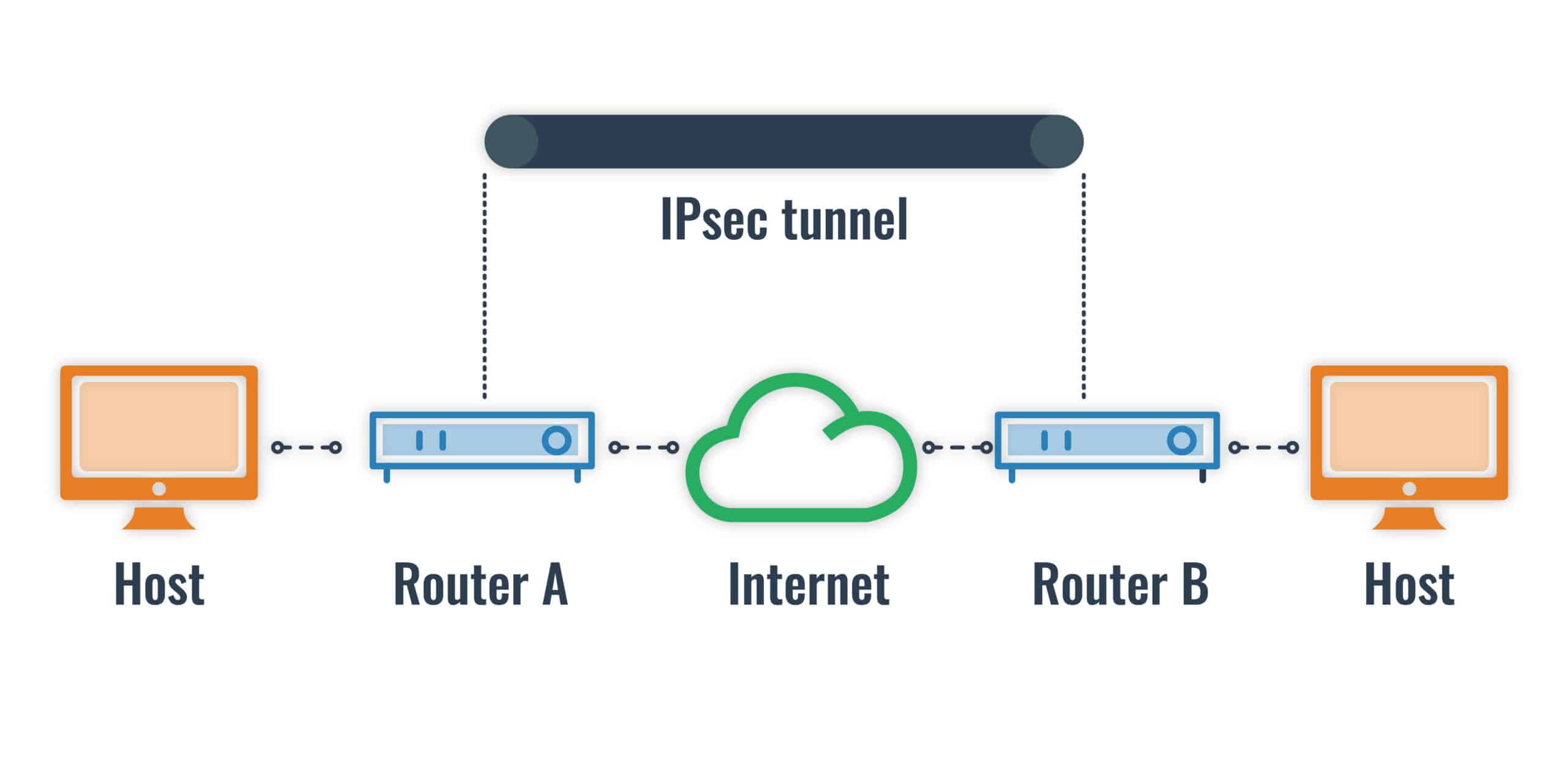
IPsec stands for Internet Protocol Security, and it is most prominently used in VPNs, but can also be used in routing and application-level security. It uses a range of cryptographic algorithms for encrypting data and protecting its integrity, including 3DES, AES, SHA and CBC.
How IPsec’s tunnel mode can encrypt data and keep it safe as it travels across the open internet.
IPsec can be implemented in two different modes, tunnel mode and transport mode. In tunnel mode, both the header and the payload are encrypted and authenticated, then sent in a new packet with another header. It’s used by VPNs in host-to-host, host-to-network and network-to-network communications.
Transport mode only encrypts and authenticates the payload and not the header. The data transits through an L2TP tunnel, which provides the end-to-end security. It is generally used to connect clients and servers, or a workstation to a gateway.
When it comes to VPN configurations, IPsec can connect faster and be easier to implement, but in many instances, using TLS can be more advantageous overall. While the Snowden leaks showed that the NSA was attempting to undermine the security of IPsec, it is still considered safe to use as long as it is implemented correctly.
SSH
Secure Shell (SSH) is yet another secure protocol that is used in a variety of scenarios. These include securely accessing a remote terminal, as an encrypted tunnel (in a similar manner to a VPN) by using the SOCKS proxy, securely transfering files, port forwarding, and much more.
SSH is made up of three separate layers: the transport layer, the user authentication layer and the connection layer. The transport layer allows two parties to connect securely, authenticate each other, encrypt data, validate data integrity and establish several other parameters for the connection.
In the transport layer, the client contacts the server and keys are exchanged using the Diffie-Hellman key exchange. A public-key algorithm (such as RSA), symmetric-key algorithm (such as 3DES or AES), the message authentication algorithm and the hash algorithm for the transmission are also selected.
The server lists the supported authentication methods to the client, which can include passwords or digital signatures. The client then authenticates itself over the authentication layer using whichever system was agreed upon.
In the connection layer, multiple channels can be opened once the client has been authenticated. Separate channels are used for each line of communication, such as a channel for each terminal session, and either the client or the server can open a channel.
When either party wishes to open a channel, it sends a message to the other side, with its intended parameters. If the other side can open a channel under those specifications, it is opened and data is exchanged. When either party wishes to close the channel, they send a message to the other side and the channel is closed.
While an SSH tunnel is not a VPN, it can be used to achieve some similar results. You can use a SOCKS proxy to encrypt your traffic from the SSH client to the SSH server. This allows you to encrypt the traffic from each application, but it doesn’t offer the universality of a VPN.
The Snowden leaks contained files which suggested that the NSA may be able to decrypt SSH under some circumstances. While some implementations may be vulnerable, the SSH protocol itself is generally considered safe to use.
PGP
PGP is the final security protocol that we will talk about today. It allows its users to encrypt their messages as well as to digitally sign them to prove their authenticity and integrity. Since the early nineties, it has been an important tool for protecting sensitive information in emails.
The protocol itself is actually called OpenPGP, but PGP has a long and convoluted history that involves the initial program and PGP Inc., a company that formed around the development. PGP Inc. has since been acquired by other corporations multiple times, with some of its assets now owned by Symantec and other companies.
The OpenPGP standard was developed in 1997 so that PGP could become a globally used and interoperable system. It can be freely implemented into a variety of email clients, but one of the most commonly used configurations involves Gpg4win, an open-source encryption package for Windows.
OpenPGP can be used with a number of different algorithms, such as RSA or DSA for public-key encryption; AES, 3DES and Twofish for symmetric key encryption; and SHA for hashing.
In the course of its development, a number of vulnerabilities have been found in various implementations of OpenPGP. New versions have addressed these security flaws, the latest of which, EFAIL, was discovered in 2018.
As long as HTML rendering and JavaScript are disabled while viewing emails, and automatic reloading of external content is stopped, PGP is still considered secure. Some clients such as Thunderbird have also released updates that mitigate these problems.
Is encryption safe?
When it comes to security, nothing can be completely safe. If you wanted to, you could build a wall 100 feet high to protect your house. This would prevent most robbers from being able to get into your house, but it would also be expensive and inconvenient. Although it may prevent most thieves from getting in, it won’t be impenetrable. Anyone with a ladder that’s 100 feet high could still gain access if they wanted to.
Encryption is essentially the same. We could use far more complex algorithms to make our data even safer, but it would also make the process much slower and less convenient. The aim of security is to make an attack too costly and time-consuming to be mounted against you. The right defenses will depend on what you are trying to protect, how valuable it is, and how highly targeted it is.
If you are just a regular person who wants to keep their Facebook password safe, you won’t have to go to the same lengths as the U.S. Government when they transmit military secrets.
For the average person, the most likely threat against their Facebook password would be bored hackers or low-level scammers. In contrast, governments have to worry about highly skilled groups with nation-state backing and tremendous amounts of resources at their disposal. These adversaries are far more capable, which means that security must be much tighter in order to make successful attacks unlikely.
Despite this, all of the encryption algorithms and security protocols that we have discussed today are considered safe. By “safe”, we mean that it is unfeasible for anyone to crack them at their core using current technology. Of course, this all depends on these protocols and algorithms being correctly implemented and used.
Since the threat landscape is constantly evolving, new vulnerabilities are always being found against various implementations of these algorithms and protocols. The cryptography industry is currently wrestling with the prospect of quantum computers becoming powerful enough to render crack today’s encryption methods, this is where post-quantum encryption comes in.
In 2016, NIST launched a Post-Quantum Cryptography Standardization to help future-proof data against quantum computers. The selected algorithms were published in 2022, and included the CRYSTALS-Kyber, CRYSTALS-Dilithium, SPHINCS+, and Falcon algorithms.
One of the creators of the “Cryptographic Suite for Algebraic Lattices” (CRYSTALS) cryptographic primitives is Vadim Lyubashevsky — a cryptographer working for IBM Research – Europe.
He says that lattice cryptography hides data inside complex algebraic structures called lattices. These can be thought of in terms of the so-called “knapsack problem.” In reality, the math behind the primitives is fiendishly complicated and beyond the scope of this article.
Perhaps the most important thing is that the implementation of quantum-safe cryptography shouldn’t be particularly disruptive. Lyubashevsky says that “if today’s cryptography is replaced by lattices, the user wouldn’t see any changes, except maybe a speed up in performance.”
In summary, whatever encryption you decide to use, it’s crucial to stay up-to-date on the latest developments and risks. By keeping abreast of the latest issues, implementing the relevant security measures properly, and using them within the appropriate guidelines, you should be able to use each of these types of encryption with confidence.
Read our full series of security articles
Encryption algorithms:
- What is AES?
- What is RSA?
- What is 3DES encryption and how does DES work?
- Encryption, Hashing and Salting (what are they and how do they differ?)
Security protocols:
- Email encryption (overview)
- PGP Encryption
- How to use PGP encryption with Windows
- How to use PGP encryption with Outlook
- How to use PGP encryption with Gmail
- Beginner’s guide to SSL
- What is SSH and how does it work?
- What is TLS and how does it work?
- What is IPsec and how does it work?
Cryptography
- Beginner’s guide to cryptography
- Public-key cryptography
- What is the Diffie–Hellman key exchange and how does it work?
- What are digital signatures and how do they work?


Excellent article Josh Lake. Your approach to explaining digital security, encryption, algorithms, protocols etc., benefits all levels of techies.
I see this article was written in 2020. Will you be keeping the article updated; given all the time you spent developing it to help novices like myself? Much appreciated.
Hi Mary,
I really appreciate your feedback and I’m glad you find our work useful. Honestly, we probably don’t update it as much as we should, but I am still working on covering important cryptography topics. You may find some of these helpful:
https://www.comparitech.com/blog/information-security/what-is-sha-2-how-does-it-work/
https://www.comparitech.com/blog/information-security/what-is-a-collision-attack/
You can also click on my name and view all of my articles. Many of them concern cryptography, and I try to explain the concepts as simply as I can.
Brilliant explanations for the novice
Many people think that hashing is encryption, but it is not … it is a cryptographic algorithm to ensure integrity. Hashing is a one-way function, where as, encryption is a two-way function. Is this statement true?
Yep, that’s the gist of it.
Which algorithm is best for hashing? I read at many places that MD5 is broken. Generally, people use SHA for hashing. But bcrypt is recommended over SHA. And recently Argon is also coming up.
Please suggest.
It depends on the situation, but SHA2 is probably the most universal at the moment.
I found this web site helpful thanku