At the recent summit between President Donald Trump and North Korean leader Kim Jong Un in Singapore, journalists were handed a goody bag containing, among other things, a USB-powered fan.

In the sweltering Singapore temperatures; a thoughtful gift one might think. But security experts across the world thought otherwise, cautioning the USB device may be a ploy to infect devices with spyware.
With North Korea now touted as a “hacking superpower” and squarely blamed by Western Governments for the WannaCry ransomware attack that swept the world, impacting institutions as venerable as the UK’s National Health Service, who could blame security experts for their caution?
Coupled with this, hacking systems via USB sticks has become an expedient attack vector in recent times. The tactic was popularised by Stuxnet, a strain of malware used to damage an Iranian nuclear plant thought to be infected through a thumb drive.
In view of this, it was exciting to be able to get my hands on one of these USB fans for forensic examination. This is one of the actual items handed out to journalists at the summit.
The first thing to note is, counter to many of the tweets and articles that appeared on this issue, this fan was not for use in a PC or laptop and did not come with a standard USB connector. It was in fact equipped to plug into the mini-usb port or iPhone lightning port on mobile phones that are used for charging the device.
You can see an example of the type of fan here, which looks in every way identical to the fan given to journalists.
Software audit
In my examination of the fan, I conducted investigations only on an Android device and also with a micro-USB to USB adapter. This gave me the ability to plug the fan into a standard USB port on my forensic laptop.
A Protocol analyzer was leveraged to capture and analyze USB data packets – no unusual data was observed. A forensic comparison of the operating system before and and after plugging in the USB fan revealed no unusual system changes or additional files, executables, etc.
From this examination I could find no evidence of system changes, downloads, code being run as HID (Human Interface Device), unusual packets or communication, nor anything else to suggest malicious activity. All security scans also detected nothing suspicious.
I then moved on to the physical examination.
Hardware inspection
The bag containing the device indicated the fan was made in China. Obviously this is not definitive proof of origin but I think it fair to say it would be foolhardy for the North Koreans to so publicly and blatantly package spyware pointing to China.
My physical analysis compared the USB fan to a comparable fan on the market and checked for the addition of any listening, monitoring, or communication mechanisms. The chips were found to be identical in every way.
Here’s the fan stripped of its outer covering exhibiting no unusual features:

Here is the chip itself. When compared with another mini fan chip I could see no discernible difference:
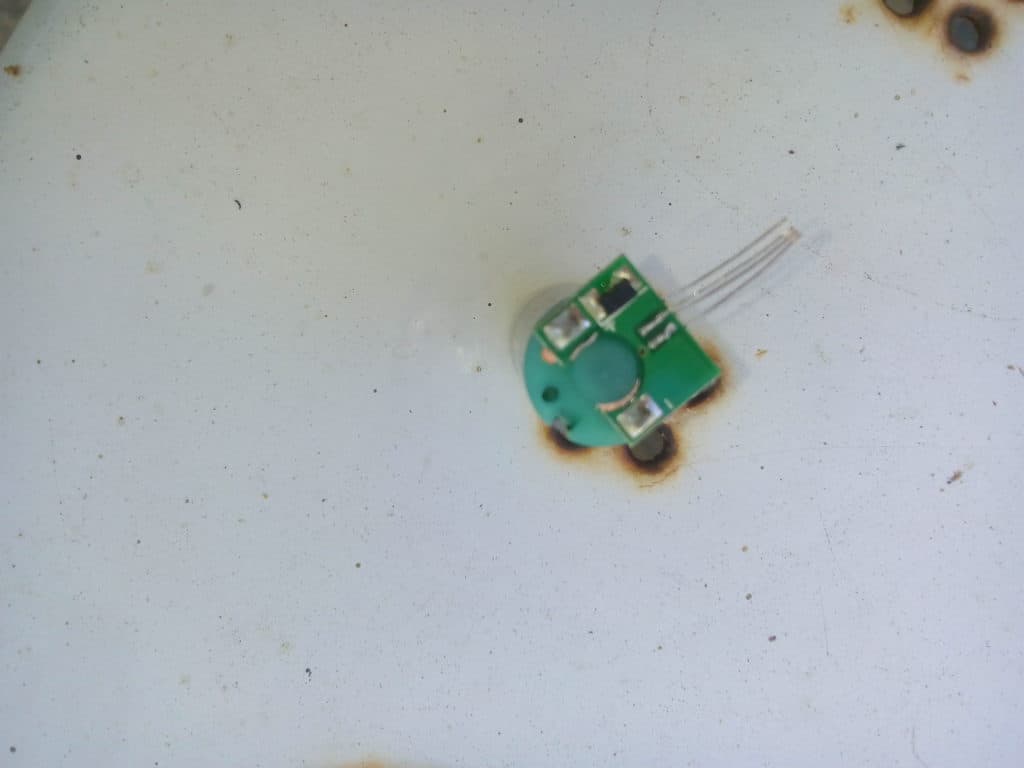
And finally inside the motor:

Again, nothing unusual, and the same as a comparable mini fan.
This one is clean. Are the rest?
From my analysis I can conclude with a reasonable degree of certainty this mini USB fan does not contain spyware or malware. I threw everything I have and know at it and came back with nothing.
It’s worth noting that if I were a North Korean spy and wanted to leverage this fan as spyware in this context, I would not infect them all, but rather a select few, targeting only those journalists I deem most important. In other words, just because this fan was non-malicious, doesn’t mean they all were.
While researching, I could not find any report of infection of a mobile device via a mini-usb fan.
Irrespective of my findings, the security community were right to communicate their warnings. Physical attacks on systems leverage USB drives that download malicious code for spying. Keylogging, exfiltrating data, and a plethora of other attack types are ubiquitous in today’s climate.
Beware plugging anything unfamiliar into your device, especially that interesting USB stick you found in the office car park with “Private & Confidential” written on it in indelible pen.
Stuart Winter-Tear (@StegoPax) is a researcher and secure design analyst at Continuum Security where he does threat modeling and secure architecture design.