
The terms Virtual Network Computing (VNC) and Virtual Private Networking (VPN) sound similar but are very different things.
VNC provides remote control of a computer at some other location allowing users to operate that computer as if they were sitting in front of it. Any resources that are available at the remote computer, such as printers and network drives, are available. Users at the remote site can see what the remote user is doing, and even interact with them.
By contrast, a Virtual Private Network (VPN) simply connects you to a remote network, but does not provide a desktop for you to use. Rather, you use your own desktop to access the resources that exist on that network, such as printers, network drives, and internet connections.
The fundamental difference between the two is that your computer joins a remote network when using a VPN, whereas you can only view and use a remote computer when using VNC.
- Virtual Network Computer/Computing
- Virtual Private Network
- VNC versus RDP
- Deeper dive into the Remote Framebuffer Protocol (RFB)
- VNC Forks
Virtual Network Computer/Computing
VNC is primarily used in two ways these days: to remotely access a work desktop from home (or other location), or to allow remote technical support people to take over a computer for support activities.
Common uses of VNC
Remote workers
Many companies allow workers to remotely access their desktops while away from the office using VNC. This provides some security because employees don’t need to take company documents and emails with them in order to respond to after-hour issues. Instead, they can always just log in to their work computer and the company data never has to leave the premises.
Business Continuity Processes (BCP)
There are many disasters that can occur which make physical access to a workplace impractical. Having VNC access to work computers removes the necessity to have physical access to a computer and can help work continue during these times.
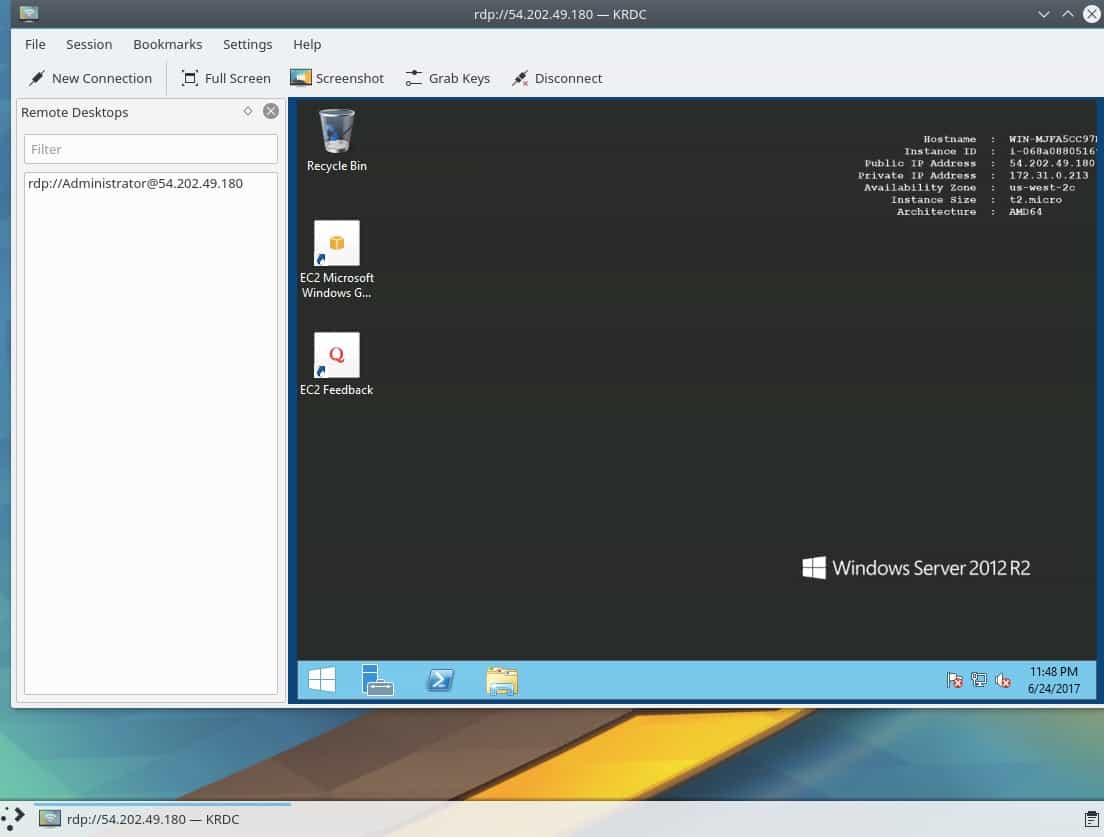
It’s also quite common today for parts, or all, of a company’s networking infrastructure to be located offsite; sometimes very far away in a cloud somewhere. When access to servers is completely remote, it’s possible to lose access to a server via the normal means. Some cloud providers offer the ability to launch a temporary VNC instance to allow remote access to the console in those cases.

Remote Technical Support
VNC is the perfect solution for remote tech support. It allows a remote technician to control your desktop as if they were onsite, and it requires almost no knowledge on the part of the person requiring support. Many companies use VNC in their internal IT departments to assist with routine tasks, and there are a lot of third party support companies that use VNC as well. VNC is particularly useful for support because the person receiving the support can watch what is happening, and even interact when necessary, such as when required to enter a password that the support person does not know.
Pros of VNC
VNC is a very mature product that has been in development since the 1990s. It operates on a very robust, but simple, protocol called the Remote Framebuffer Protocol, which we discuss in more detail later on.
VNC is essentially platform independent because the mechanism used to transport desktop images and keyboard presses back and forth exists under
the operating system. A specific operating system client and server application needs to exist, though, but there are VNC client and server applications for virtually every operating system imaginable, including mobile phones, these days.
Cons of VNC
Due to the basic way in which VNC works, it uses a lot of bandwidth to transfer desktop images to the client. In low bandwidth situations, this may cause an issue. However, most VNC clients allow users to specify both the resolution of the remote screen (the screen size) and also the color depth to use. A low resolution, grayscale screen can be transferred fairly quickly and work well over lower bandwidth connections.
The most basic form of VNC encoding uses the raw encoding method. If the client and server are so disparate that they do not share any advanced encoding methods, then the raw screen will be sent from the server to the client pixel-by-pixel in left-to-right, order. Most modern implementations try to reduce this problem by sending only changed pixels. This works well for small movements like mouse cursor changes, but bogs down when the entire screen changes such as when reading a document or web page.
Another potential disadvantage of VNC is that since it only facilitates the use of a remote desktop, only the applications available on that desktop can be used. If you wish to use an application that you have on your local computer on the remote computer, the only way to achieve that is to install that same application on the remote computer. Depending on your use-case for using VNC, this may be a problem.
Security of VNC
Due to the widely available selection of VNC clients and servers, there is a similarly widely varied availability of security. The base RFB protocol encrypts passwords, but due to weaknesses in the process passwords can be successfully sniffed from the network by a skilled and determined adversary.
Many modern VNC implementations add encryption so that the entire VNC connection is encrypted, but not all do this. For example, TightVNC only weakly encrypts passwords and makes no attempt at all to encrypt the rest of the session. It is important to review the VNC application you intend to use to ensure it provides an acceptable level of security.
If you need to use a VNC application that doesn’t provide suitably strong encryption, it’s possible to tunnel VNC through an SSH tunnel or a VPN. Both options will encrypt the entire transport tunnel so the encryption of the VNC client becomes less important.
Another security advantage of VNC over a VPN is the separation of environments. When connected to a remote network over VPN, the local computer is a member of the network and therefore any worms or viruses that are present on the local computer can be transferred to the remote network. This is less likely in a VNC session because only keyboard and mouse clicks and screen data are transferred across. A file would have to be purposely transferred to the remote machine to allow a local virus infection to spread to the remote network.
Virtual Private Network
A VPN has a single purpose: to create a private network between your computer and some remote network by utilizing the public internet as the carrier. VPNs have been used for remote work since the mid-90s but didn’t reach mainstream adoption until recently.
Common uses of a VPN
Once a VPN connection is established, the potential uses of that private network are unlimited. However, we generally see VPNs used in two main ways these days: to allow workers to access company network resources remotely, and to use the internet connection at the remote site as a proxy to the public internet.
The general public’s use of VPNs may be the more common use these days. More and more people are adopting VPNs to protect their internet traffic from prying eyes, and to obtain an IP address in a different country to evade things like Netflix geographic filters. VPN use is also popular to access censored content in countries such as China and the UAE.
Related: Best VPNs for 2017.
Pros of a VPN
The benefits of a VPN are greatly dependent on your use case. If privacy is a concern, then the fact that VPNs encrypt the traffic between your computer and the VPN entry point is a benefit. If your intent is to evade geographic filtering, or to use an IP address that is not directly associated with you, then the remote internet proxying that some VPNs provide is the best benefit.
Another benefit to using a VPN is that you can use your local applications against the remote network just like you would if you were at home. For example, a remote network may allow VNC connections to the desktops on it, but not expose those VNC servers to the public internet for security reasons. In that case, connecting via VPN to the remote network first, and then using your local VNC client to access the desktops is a more secure way to allow that.
Since you’re connected to the remote network, things like file copying from one remote folder to a local folder, and printing remote documents to your local printer are also possible.
Cons of a VPN
VPNs are more complicated to set up than a VNC connection. The configuration of the server can be especially complicated in some cases and while most vendors and companies provide client configuration files, non-technical users may still have a hard time configuring their VPN clients.
User provisioning on the server side is also more involved. In a VNC situation, generally all a remote user needs is a password to get past the VNC authentication. With a VPN, there may be multiple credentials required, and sometimes client certificates and private keys need to be distributed through some secure channel prior to a connection being made.
Security of a VPN
Security is provided when using a VPN via encryption. Different VPN implementations have varying degrees of encryption that range from totally broken
(PPTP “Point-to-Point Tunnelling Protocol) to very secure
(Perfect Forward Secrecy in OpenVPN and other protocols).
VNC versus RDP
The Remote Desktop Protocol (RDP) and VNC look to be the same thing at face value. They both provide a remote desktop and look identical in most cases. However, they are slightly different things.
VNC is cross platform because it is dumb. It simply ships a copy of the desktop graphic over the network to your viewer. RDP, on the other hand, has some knowledge of both the remote and local systems and does not need to ship such large chunks of data. Rather, instructions on how to draw the remote desktop are sent to the local system and the RDP client recreates the remote desktop. RDP is a proprietary Microsoft product and is contained in all versions of Windows since Windows XP. It is therefore mostly used in Windows environments but client and server applications do exist for other operating systems.
As a Microsoft product, RDP also has the advantage of integrating with Active Directory and LDAP. This means that user provisioning is much easier.
Example: If you open a file explorer window on a remote machine while using VNC then that entire graphic of that file explorer window needs to be transferred across the network. Using RDP, the remote computer only needs to send instructions about the window size and location. The RDP client will take that information and reconstruct the window on the local client. Due to this, RDP is much more performant than VNC as it transfers less data across the network.
Another major difference is that a client using RDP is viewing their own desktop which nobody on the remote server side can see. On the other hand, VNC shares a user’s desktop which means that the remote person and the local person can see what each other are doing, and also share control of the same desktop. Neither situation is inherently better than the other. Rather, each supports a specific use case.
Deeper dive into the Remote Framebuffer Protocol (RFB)
A framebuffer contains the data required by a computer to represent some graphic on a computer monitor. The Remote Framebuffer protocol allows that representation on the remote computer (the VNC server) to be transferred to the client computer (the VNC client) which enables the client to display the screen.
As with most protocols, when a client and server connect, they engage in a negotiation to find out what each other’s capabilities are. The connection is only established once both parties agree on the minimal level of functionality they can both support. This allows a wide variety of clients to use a wide variety of servers without having to ensure that both parties are running the same version of the software. That type of flexibility is the reason why RFB, and therefore VNC, has enjoyed such longevity.
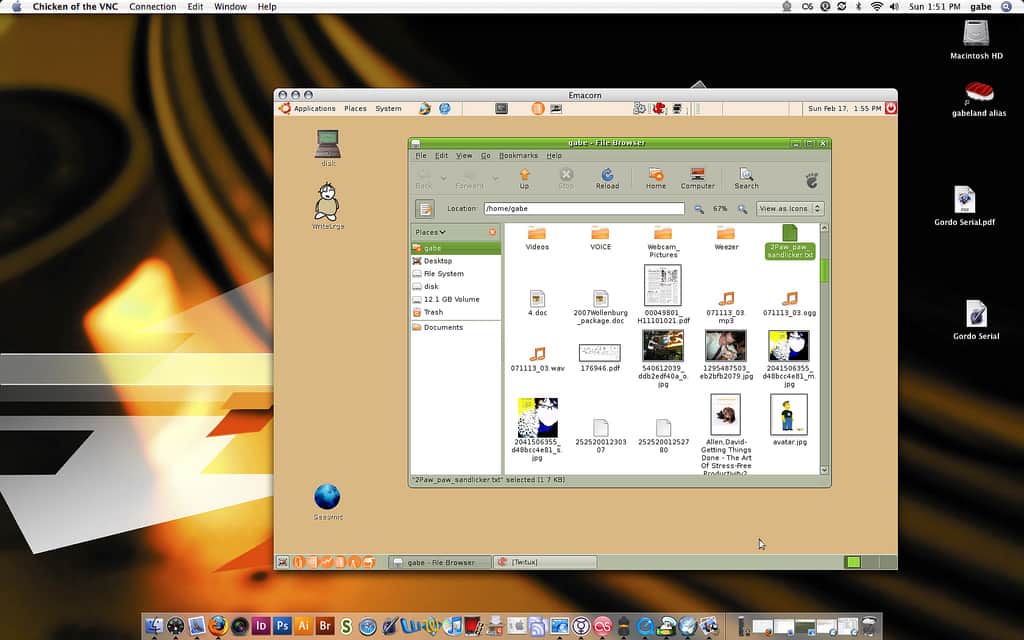
This is a VNC connection from my laptop to my desktop. Note that both sides are using the same RFB protocol so there’s no need for either side to step-down, and they agree to use VncAuth(2) as the security type.
Sun Jun 25 08:58:45 2017
DecodeManager: Detected 4 CPU core(s)
DecodeManager: Creating 4 decoder thread(s)
CConn: connected to host server-machine port 5901
CConnection: Server supports RFB protocol version 3.8
CConnection: Using RFB protocol version 3.8
CConnection: Choosing security type VncAuth(2)RFB is now a free protocol which anyone can use. Developers are able to extend parts of the RFB protocol by adding new data encoding and security types, but in order to make sure those additions don’t conflict with some other developer’s additions, they must apply for a unique booking number with RealVNC, the company that maintains the types
booking list.
VNC Forks
It’s very hard to categorize what VNC can do
because there are so many variations of it written by many different authors. The basic pass the graphic
VNC protocol is very limited in that it knows how to accept mouse clicks and keyboard presses, and it knows how to ship the changed view of the remote desktop back to the client. It can’t do much else and due to this it is limited, but also extremely reliable at those basic tasks.
Many different authors have built upon that basic functionality and there are literally hundreds of VNC server/client applications available now. Some of them far extend that basic functionality into much more. However, each of these is essentially an island unto itself because bolting functionality onto a VNC server doesn’t automatically make that functionality available to every VNC client that connects to that server. Only VNC clients that have also been modified will know that functionality is available and be able to use it.
On one hand, that creates a shotgun scatter market of VNC applications and it can be confusing to know which offering is best for your particular situation. On the other hand, the mere fact that the underlying RFB protocol allows functionality to be added to it without breaking is quite an impressive feat. In most cases, when a VNC client connects to an advanced VNC server which can offer functionality that the client can’t handle, that connection will still work. It will just be limited to whatever the VNC client can understand which is a graceful way to handle this situation. However, this is not always the case because some VNC clients have been so heavily modified, or use different encryption methods, which can make it necessary to use the specific VNC client with that VNC server.
See also: Our VPN protocols cheat sheet.

Excellent explanation, excellent article.