Electronic commerce is growing, and quite frankly, there’s simply no stopping it. Better known as “e-commerce”, online shopping raked in nearly$2 trillion in 2016, with current projections placing that number as high as $4 trillion by 2020. Yet there’s another growth metric that coincides with the rise in e-commerce that makes the trend less than ideal: a stark rise in cyber crimes.
The cost of cyber crimes is projected to reach $2 trillion by 2019, which, one might note, is the current value of e-commerce, and half the projected value of e-commerce by 2020. To date, more than 40 million Americans have had their credit card data stolen (around a quarter of all Americans with credit cards), much of which is directly related to online payments and credit card data stored online. Given how increasingly dependent society is on online payments, and the fact that digital theft also appears to be increasing right along with it, it’s certainly wise for consumers to be wary about clicking on the “pay now” button. Is there any way to actually avoid the worst case scenarios?
Yes and no.
A particularly diligent hacker will almost always be able to find a way to steal data from somewhere, even if his attempts are blocked by more highly secure systems. Over 20 percent of data breaches, in fact, are inside jobs (pdf) from employees who have easy access to sensitive customer data. Regardless of how hackers end up getting your account information, you can lessen your chances of becoming a cyber crime victim by utilizing a few useful tips.
1. Only make online purchases from SSL/TLS secured sites
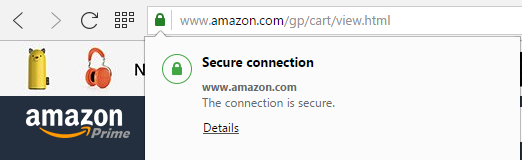
An increasing number of websites rely on what’s called SSL/TLS encryption to secure online data. This type of encryption is incredibly difficult for hackers to break into, edging on impossible with current computer processing power. What you’re looking for, in this case, are websites that have been verified in their use of this high-level encryption standard. Thankfully, it’s very easy to identify. Just look for the padlock symbol and/or an “HTTPS” in front of the web address:
In the case of Amazon, the largest online retailer by sales, you’ll find the use of a high-level SSL/TLS certificate issued to the company by Symantec. Few people would say that they don’t trust making an online payment on Amazon, as highlighted by the site’s significant volume of sales.
We’ve covered SSL/TLS encryption in-depth, which you can read more about here. To put it simply, there are multiple certificate levels a company can purchase. What you don’t want are retailers who purchase the cheapest level of SSL/TLS security from lower tier companies, which simply verify the website’s ownership. Higher-level certificates require a complete and rather extensive evaluation of the site’s identity, ownership, and security features. Companies that purchased the highest level certificates are typically rewarded with the company’s name emblazoned next to the web address bar. Ebay provides just one example of this:
Does a company need to have their name next to the web address to be fully secure? Not at all. Amazon, for example, does not have that certificate level, while eBay only utilizes it when you’re ready to make a purchase.
Does a company always need to have SSL/TLS certificates? Again, not at all. For users, the most important areas to secure on a website will be any place where you may be inputting personal information, such as credit card numbers or usernames and passwords. Pages on a website that don’t involve any two-way interaction don’t necessarily need to be secured with expensive SSL/TLS certificates, but it’s good for companies to purchase some security even for those pages.
A website’s SSL/TLS security level should be your primary means to judge a website’s safety level for making online payments, but not your only point of reference for how to pay safely online.
2. Only make payments through sites that utilize reputable and secure online payment gateways
Online payment gateways, such as PayPal and Authorize.net, exist primarily for convenience, but also to help secure your online payments, even when you’re making purchases on less-than-secure websites. When using hosted payment gateways like PayPal and Amazon, your financial information, such as credit card or banking information, never actually ends up in the hands of the merchant. These services also help ensure that you don’t have to create new accounts on different websites, preventing those websites from collecting the vast majority of your information.
Integrated payment gateways, however, allow the website to gather and store your credit card information. This is the case with any website in which you don’t see the name of a separate payment system listed (e.g., PayPal). Websites that use Authorize.net, for example, are using an integrated payment gateway and will store your information. Amazon uses its own, homegrown system, but also sells its large customer database to other companies as a hosted gateway.
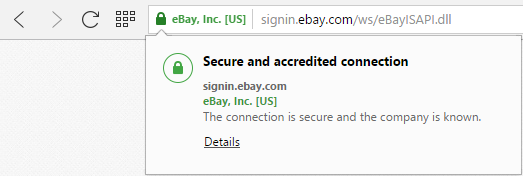
You can easily see the safety provided by such services everywhere on the internet. For example, I had never heard of the website SmartBargains.com, but for the sake of argument, I went there and picked a random item to purchase. After clicking on the button to buy my item, I was greeted with this screen:
I don’t know Smart Bargains. I have no idea how trustworthy they are as a company with user data. But the fact that they utilize merchant accounts with PayPal and Amazon means I don’t have to worry about them stealing my financial and personal information. I could certainly utilize their integrated payment gateway, but I don’t know how trustworthy their site actually is. They provide me with alternative means of payment that I do trust, making them more trustworthy as a website in my eyes.
As long as I can verify that those hosted gateway logins are legitimate (again, by checking to make sure that there’s an HTTPS certificate on the PayPal or Amazon pages after clicking over to them), then I can safely assume Smart Bargains is safe to buy from. It won’t guarantee that I’ll receive the product I purchased, but at least I know my data is secure.
PayPal, Google Wallet, Apple Pay and other such systems act as a middleman of sorts, withdrawing the funds from your account and then passing them along to the receiving site. This can often include sending the merchant your shipping details if need be. All the merchant site sees during this transaction is the credited funds, not the financial information involved in transferring those funds.
This sort of intermediary service makes it possible for sites that lack higher-level SSL/TLS encryption to enjoy the benefit of a secure payment system. It also helps prevent situations where anyone working for those websites might steal your personal information and use it enjoy the good life on your dime.
Trustworthy integrated and hosted payment systems should align to Payment Card Industry Data Security Standard (PCI DSS). Chances are, you won’t know whether the site does or does not align with these standards if it’s not using a recognizable hosted payment gateway like Apple Pay, PayPal, Amazon, Visa Checkout, or Google Wallet. This is why you should avoid making online payments from websites you don’t know or don’t trust, especially if that site doesn’t advertise its payment gateway or doesn’t offer alternative hosted gateways.
There are a large number of online payment gateways, many of which are highly secured. Other such services include SecurePay, Stripe4, 2Checkout.com, First Data Corporation, BluePay Processing, PaySimple, Fastcharge.com, Paynova, and Chronopay, among many others. If you’re unsure of a site’s payment security system, don’t feel bad about abandoning the purchase. In its 2016 American Express Digital Payments Survey, American Express found that 42 percent of shoppers have backed out of making an online purchase due to safety concerns.
3. When making purchases outside of your home network, opt for mobile data networks over public wifi
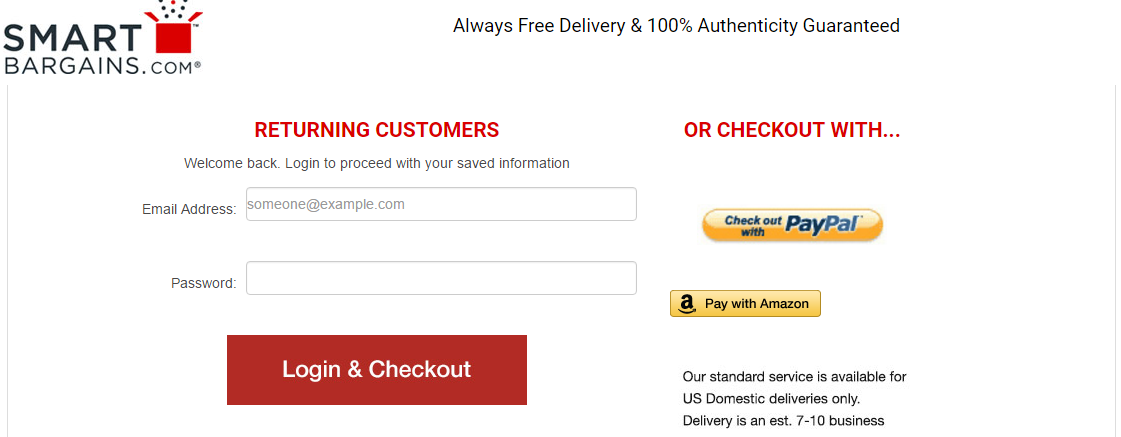
This comes down to data security while on public networks. Public wifi networks are fantastic services to help you avoid using up your data plan on your mobile device, but they’re also far from secure. In this case, hackers can use what are called man-in-the-middle attacks to steal your data.
Once connected to the public wifi, hackers can insert themselves into the hosting router. After this is accomplished, they can see any data that is passing through that router. That includes your passwords and yes, credit card and bank account data that might be passing between your computer and the router.
Symantec provides a rather solid graphic to help visualize how this works:
Not all public wifi is created equal. Secured networks are certainly safer than open or unsecured networks. Still, even secured public wifi networks that require a password or access key can be hacked. Your own, home network is always the safest, with a wired network or and your mobile data network being the safest options.
An easy workaround for this is the use of a virtual private network, or VPN, while connected to public wifi. VPNs will encrypt your data, even before it passes through the public wifi router you’re using.
4. Don’t use the same password across multiple sites
American Express, one of the largest financial institutions in the world, provided us with helpful information regarding safety and security with online payments. The company recommends that consumers “create different passwords across all banking, email and social media accounts, and update all passwords every six to 12 months.”
If your data is stolen from one website, including login and password information, any other website that has that same information becomes compromised. Hackers can track down your other accounts and steal additional information from those sites as well. In its Digital Payments Security Survey, American Express notes that only 44 percent of online shoppers use a different password for different online accounts, while only 30 percent create new passwords for their accounts once or twice a year. The survey also indicates that a disparagingly large 17 percent never change their passwords at all.
5. Consider creating separate payment accounts just for online purchases
Far from being a necessary option, this method can help keep your primary accounts completely separated from your online purchasing. If your secondary, dedicated online payment account is hacked, you won’t have to worry about losing your entire life’s savings (not that you should have all of your life savings wrapped up in one bank account, of course).
- One way to do this is to transfer money from your bank to PayPal before making online purchases. When you utilize PayPal, the system will transfer money that’s stored in your PayPal first, then transfer money directly from your bank or credit card if need be
- Alternatively, you might utilize a prepaid debit card, like the American Express Serve Card
This may be a particularly good method to employ if you have young children, teenagers or young adults beginning college who will be using those cards to make online purchases. Instead of giving them access to your credit card or bank-connected debit card (a sign of trust, to be sure, but perhaps not the wisest option), you can set them up with their own, separate account you can load money into. This is particularly true with the American Express Serve Card, which also provides you with the ability to create subaccounts in which each subaccount receives its own prepaid debit card.
American Express informs us that Serve Card members and members of other American Express cards “are not held liable for any fraudulent charges on their account.” This makes using American Express Serve, and potentially other prepaid debit cards like it, particularly beneficial given the liability maximums that one can be responsible for with traditional debit cards connected to checking accounts.
6. Use credit cards over traditional debit cards.
Financial website NerdWallet expertly summed up the reasoning behind this issue:
“With a credit card, the card issuer must fight to get its money back. With a debit card, you must fight to get your money back.”
Credit cards are essentially loans you take out from the bank or credit card company that you pay back later. Until you pay it back, it’s not your own money you’ve used to make the purchase; that money belongs to the bank. Therefore, If someone steals your credit card information and racks up, say, $10,000 in credit card debt on your account, you can more easily get the crediting agency to forgive this debt if you can prove it wasn’t you. They’ll have to pursue recompense from whoever stole your account information and may even have insurance that recoups their money.
Meanwhile, If you lose money directly from a checking account/current account, which is where your traditional debit card is drawing from, you may not be able to get that money back — and the immediate damage can be far more difficult to deal with. Given that it’s your money you’ve lost, it’s your responsibility to fight to get that money back. Unfortunately, you won’t even get all of it back.
According to the Federal Reserve’s Regulation E, or “Reg E”, the Electronic Funds Transfer Act, consumers are required to report fraudulent activity on their accounts within a certain time frame. If your account information is stolen after using your debit card online, you have 60 days to report it. You won’t have any liability as long as it didn’t involve the physical theft of an access device (such as a phone with a connected account or a debit card), but your bank will have 10 days to investigate, at which point they will need to return the amount to your bank.
There is, however, no guarantee that your bank will conclude your information was actually stolen and that fraudulent charges were involved. You may find yourself in a situation where you never see the return of your money at all.
7. Check for a website security seal — but don’t place your faith in it
This may be one of the most overlooked, yet most often abused and somewhat controversial security features for online retailers. A security seal is given to websites that utilize a third-party online security company. Many websites will hire these companies to provide their website with high-level security or to verify that their company utilizes high-level security. Those sites will then advertise their own business at the bottom of the site with their “seal”, in the form of an image. Most commonly, that seal only appears on pages related to making online purchases or where users are prompted to enter personal information to create accounts.
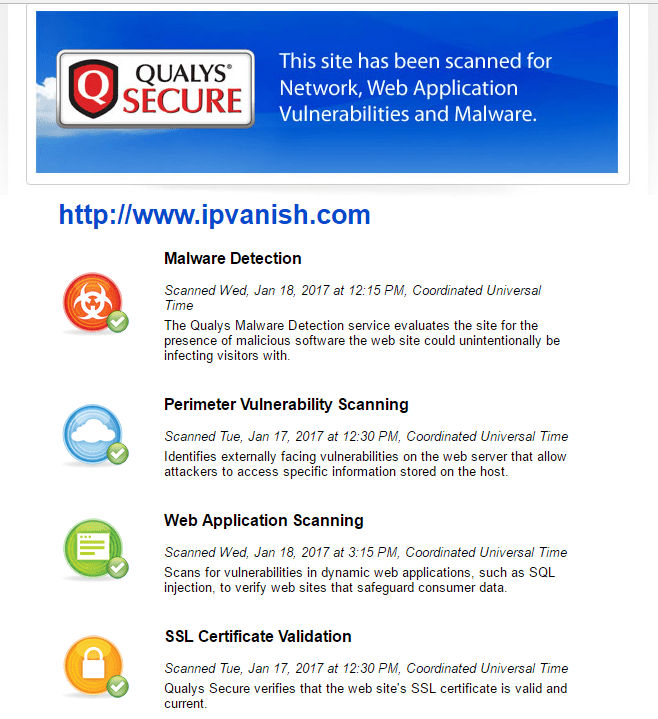
For example, on the website for VPN service IPVanish, there is no security seal on the home page. Yet one does exist on the page for creating and paying for a new account:
By clicking on the seal, you also bring up additional information to verify the validity of the seal and the website’s security features:
This provides a certain amount of trust for the site, at least related to its security features against outside hacking. It does not guarantee that those working internally can’t or won’t steal your data. This is ensured through the use of reputable payment gateways.
Here’s the problem with these seals: They’re easily spoofed, and they often don’t mean much at all.
Many websites use seals that you cannot click to bring up more information from the issuing site or company. Additionally, some sites that issue these seals may allow you to search their website for partners, but this is also not always the case. At the end of the day, the seals are just images, easily replicated or faked, and often dishonestly placed onto the bottom of websites.
It’s good to check for a seal, but don’t let a website’s use of one make or break your buying decision. Just check for the existence of a seal as another potential positive notch for a website you may have questions about. In many cases, websites that have or have had issues with their reputation will utilize a seal. Chances are you won’t find such seals on more reputable sites like Amazon or eBay. They don’t have security seals because they don’t need them to help portray a positive image.
8. Check to see if the website has a history of data breaches
Although this information is not always easy to obtain, you may be able to do a simple web search to see if the website in question has experienced a data breach of any kind. Under both federal and many state laws, companies and required to report data breaches to the federal government and to the site’s customers.
Some resources do exist online to help make this process easier. The website Breach Level Index not only provides ongoing statistics on data breaches, it also maintains and regularly updates a database of breaches that includes the company name or website name, type of breach, the number of records stolen, date those records were stolen, the location, and the industry.
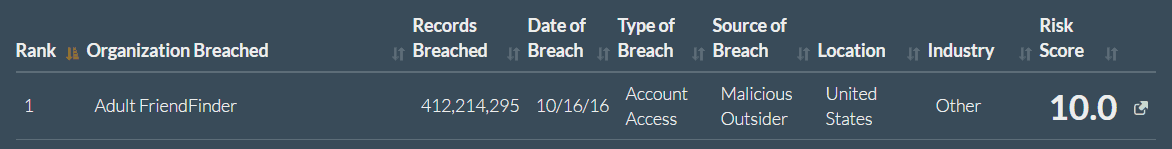
In 2016, for example, the worst data breach the site recorded was for Adult FriendFinder, an adult-oriented website that not only collects very personal and identifying information but also credit card data:
As you can see, Adult FriendFinder’s breach was massive, and given the site’s purpose (similar to, but not the same as Ashley Madison), the type of data stolen from the accounts means personal and very revealing information went into the hands of hackers — information that could easily be used to hold account holders for ransom in a similar fashion to what occurred following the Ashley Madison breach.
You will also note that breaches on this site are assigned a “risk score”, where a 2.9 or below indicates a breach where stolen data is mostly inconsequential (such as usernames stolen, but no adjoining passwords), up to a 10, which indicates an extremely large breach where extremely sensitive financial or personal data was lost. The site even includes a Risk Calculator for companies interested in how severe a potential or recently occurring data breach might be.
The database only goes back to 2013, so any breach older than that from your merchant in question will not show up. You may find news reports on that company by doing a web search, but this may often turn up nothing if the merchant website is too small, is owned by another company, or rebranded and changed names following a breach.
We’ve written about some of the biggest data breaches in history. Our findings are pretty clear: the companies most people rely on are increasingly becoming targets, while the average number of records lost in data breaches is getting larger and larger with time. Ultimately, every company is going to get hacked. Data will get lost. That does not mean you should not trust any website at all. However, you should strongly consider how seriously the sites you’re using handle their security and how they might handle a potential data breach.
Knowing this information may or may not make any difference to you. However, if you find that a site has had multiple data breaches over the past few years, it can weigh heavily on your decision to use their website. After all, a website with repeated, high-risk data breaches may not take data security seriously enough to warrant your business. That said, some sites are just more likely to be targeted, something that is simply unavoidable in today’s time. Either way, identity theft is a very real concern for anyone giving away their information online.
Use any and all information you can use to make an informed decision
There’s no substitute for caution when it comes to making online payments. Any of the information above could help decrease your risk of exposing your personal data to hackers and thieves, but you’ll never be fully secure even then. And remember: if you’re not quite sure about a website, there’s no harm in just walking away.