Staying safe while torrenting can seem like a daunting prospect. After all, there’s a huge amount of conflicting information out there, with some people recommending firewall apps like PeerBlock and others claiming a VPN is vital for anonymous torrenting. Below, we’ll explain what these two technologies are, and the differences between them, and let you know which is better for torrenting: PeerBlock or VPN.
What is PeerBlock, and how does it work?
PeerBlock is a firewall application that uses blacklists (essentially a list of banned IP addresses) to prevent certain IP addresses from connecting to your computer. One of the potential uses of PeerBlock is by torrenters to avoid detection from torrent monitoring agencies. This is done by denying access to your computer from agency IP addresses, thus preventing them from knowing you are part of a torrent swarm.
Generally, the idea of IP blacklists is flawed. Specifically, the idea that dedicated torrent monitoring companies are unable to easily subvert something as fragile as an IP blacklist seems like wishful thinking.
What is a VPN, and how does it work?
VPNs, or Virtual Private Networks, send your internet traffic through an encrypted server somewhere else in the world. This not only prevents your activities from being monitored by your service provider, it also gives you an IP address from whichever country your chosen server is in.
In other words, anyone who tries to trace you via your IP address will eventually find out that it belongs to a VPN provider. As long as you choose a no-logs service, that’s where the trail will run cold since there’ll be no record of which users were connected at a specific time or what they did while connected.
What’s the difference between a blacklist and a whitelist?
While the concepts of blacklisting and whitelisting, as they pertain to computer security, may seem similar, they are very different. Whitelisting allows only the IP addresses you have explicitly listed to connect to your computer. Blacklisting allows every IP address except the ones you have explicitly listed to connect. Both concepts have their place, but blacklisting is much less reliable.
The reason the concept of IP blacklists is flawed is because of the dynamic nature of IP addresses. Every device on the internet has an IP address, but it can’t reliably identify a single person or computer because IP addresses are constantly reassigned by their owners. Therefore, the notion that a single IP identifies a company that you want to block doesn’t really follow.
Further, in the case of torrent monitoring, the companies involved in this have a vested interest in avoiding your blacklist, so they employ a wide range of tools to avoid detection.
IP lists: reliability issues
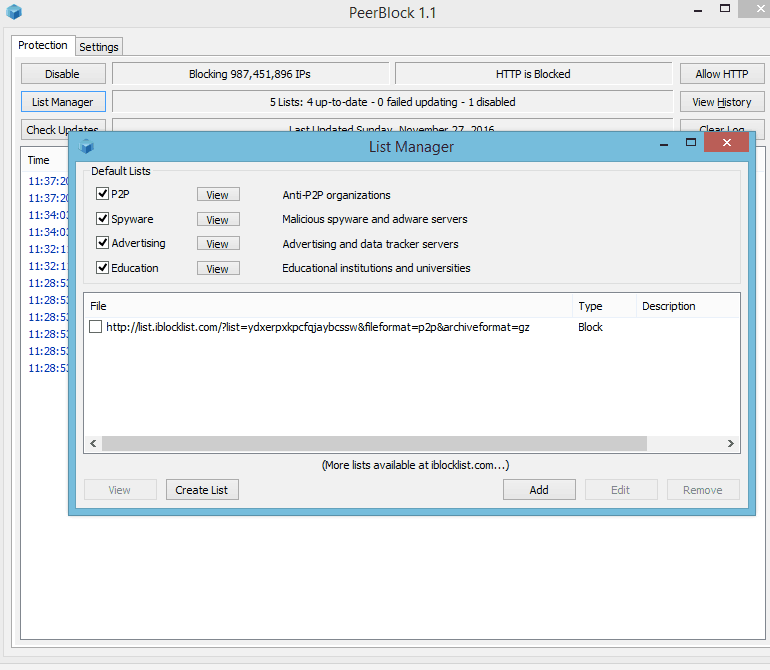
The specific implementation of PeerBlock’s blacklist is the use of lists from IBlocklist.com. There are a number of IP lists broken down into categories like agencies and countries.
As a quick test to the integrity of some of the lists, I audited the Russia and Nigeria IP lists. I found five IPs in the Nigeria file that were identified as belonging to other countries by the GeoLite database from MaxMind, and over 100 in the Russian file that were reported as belonging to other countries.
This is a fairly typical example of how transient IP addresses can be. It’s not easy to say which location is correct for any of those IPs, but the inconsistency highlights how little faith should be attributed to an IP address accurately representing any meaningful information about the machine on the other end.
Exposing your real IP address
Now that we’ve determined that there are IPs in blacklists that should not be there, it’s not too big a leap to assume the opposite is also true: there are IPs that should be in these block lists that are not. That means they won’t be blocked by PeerBlock, and thus, the owners of those IPs will be able to connect to your computer. They can then participate in the same torrent swarms that you are participating in and will be able to see your IP address.
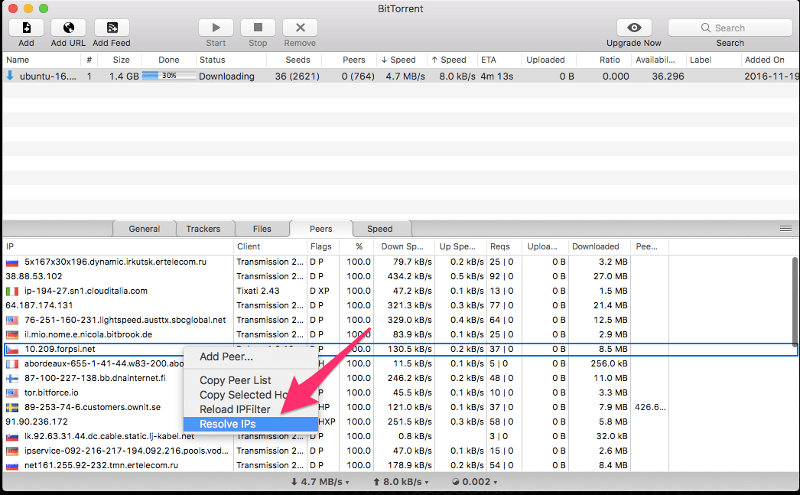
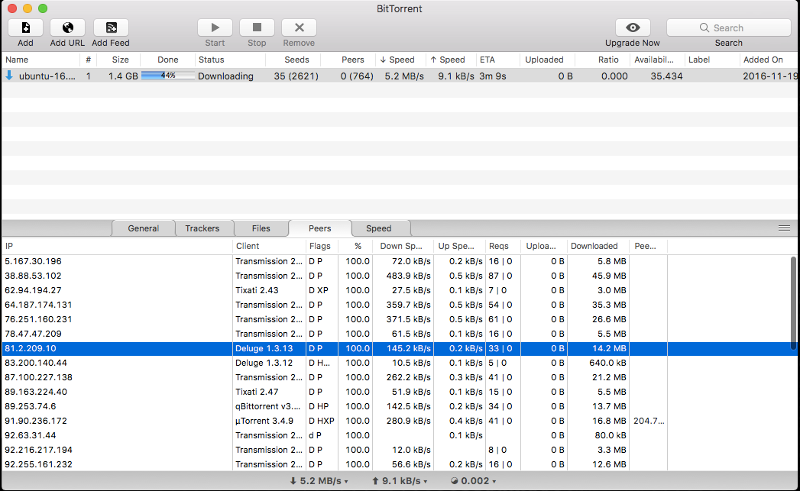
The above screenshot of the BitTorrent client for MacOS shows how readily available the IP addresses of other participants in a swarm are. The bottom frame of the main window contains the reverse DNS of everyone seeding the torrent being downloaded.
A quick right-click resolves those DNS entries and exposes the IP address. That’s one short step away from running an IP Whois to determine what ISP owns that IP address which, in turn, can identify you personally.
It’s also worth noting that every blocked IP slows down your torrent speed. Some claim the IBlocklist lists used by PeerBlock contain far too many IPs, which seems plausible given the results of the quick GeoIP test. It also appears that a subscription is required to keep IBlocklist lists up to date, although I was able to initially add lists to PeerBlock without a problem. To update the lists without purchasing them, Peerblock must be completely uninstalled and reinstalled.
A VPN is a better solution
A VPN is a better solution than PeerBlock when it comes to torrenting because a VPN hides your real IP address. This negates the need for an application like PeerBlock because you’re not exposing your real IP address, to begin with. If a monitoring agency successfully evades a blacklist and sees your IP address, then they will only see the VPN’s IP address. As well, some VPNs come with a kill switch that blocks all Internet traffic unless the VPN is established.
However, not all VPNs are created equal. The important features of a VPN that you intend to use for torrenting are speed, shared IP addresses, and a kill switch.
The need for speed is self-explanatory. Every layer added to your network connection adds some latency. There’s simply no way around that, but a fast VPN provider can minimize the effect.
A portion of VPN anonymity relies on how it handles IP address assignments. VPNs that use shared IP addresses are better for torrenting because many people are using that IP at the same time. It’s, therefore, more difficult to trace the IP address seen in the swarm back to you for that purpose at that time.
And the kill switch, as already mentioned, is another very important feature. VPNs can be fickle and unexpectedly drop connections. Most VPN clients will reconnect when that happens, but for that brief period of time, while it is reconnecting, your real IP address can be exposed to the swarm. A kill switch feature prevents that from happening because it blocks internet activity until the VPN connection is reestablished.
Check out our article on the best VPNs for Torrenting for more information about which VPNs are the most suitable.
Remember to check your VPN is working
Once you’ve set up your VPN, you may wish to ensure it is working as you expect. There are various IP checker tools out there that will allow you to verify that your IP address has actually changed and is really pointing to another location.
To see how your IP address is being shown specifically in a BitTorrent client, you can use a BitTorrent tracker site such as IPMagnet. It provides a magnet link to add to your BitTorrent client. Once you do that, the site will show you what IP you’re advertising to the swarm.
PeerBlock vs VPN: Frequently Asked Questions
Can I use PeerBlock and a vpn at the same time?
You can technically use PeerBlock and a VPN simultaneously, but there really isn’t much point. To begin with, most major VPNs block unsolicited connections by default, so you’re protected already and won’t have to worry about specific IP addresses trying to connect.
Additionally, VPNs and PeerBlock both slow down your connection and using both services simultaneously would reduce your speeds even further. This isn’t what you want when downloading large files, and especially not if you’re already on a fairly slow connection. Instead, we’d recommend just using a VPN and choosing a P2P-optimized server (if available).
Is PeerBlock free to use?
Yes, PeerBlock is completely free and open-source. However, due to how easy it is to bypass its IP address blacklist, we wouldn’t recommend using it while torrenting. You’d be far better served by a reputable no-logs VPN.
Can I use a free VPN?
Free VPNs are available, but we’d advise against using them, especially if you’re looking to torrent anonymously. To begin with, these services usually have a very low monthly bandwidth limit (often just 100 MB or so), making them impractical for regular usage. Further, you’ll often find that speeds are capped until you pay for a premium plan.
There are security issues to consider too. After all, it’s extremely difficult to tell who actually runs a free VPN company, which means you don’t know who has access to your data. We’ve even seen free VPNs lie about the logs they keep. While price is important, we recommend taking other factors into account, such as a service’s speeds, security features, and customer support, instead of using whichever VPN is free.
Will I get into trouble for using a VPN?
VPNs are not illegal in most countries, so you won’t get into trouble for using them. However, if you use a VPN to commit illegal activities like torrenting pirated media, then you may be subject to criminal prosecution. Additionally, some countries have restrictions on VPN usage, so it is important to check your local laws before using a VPN. Overall, as long as you are not using a VPN to do something illegal, you should not have any problems.
Is torrenting legal?
The good news is that torrenting is legal, as is the use of VPNs in the vast majority of countries. However, it’s what you’re torrenting that could result in potential legal issues. Torrenting copyrighted material without permission is illegal in many countries, including the US, UK, and Canada. In order to protect your privacy and avoid getting in trouble for inadvertently downloading the wrong torrent, it’s a very good idea to use a VPN.







Is there any free vpn’s out there?
Tons: https://www.comparitech.com/blog/vpn-privacy/free-vpn/