This is a comprehensive list of tools that can help you secure your privacy online. We’re not saying you should use all of them–you certainly don’t need three VPNs or four antivirus programs–but we wanted to offer a fair amount of choice. Our recommendation is that you consider using one tool from each category on each of your devices. Both mobile and desktop apps are included here, and they are all free or have a no-expiry free tier.
VPNs and Proxies
VPNs and proxies route your internet connection through a server in another location, making it appear as though you are accessing the internet from somewhere else. VPNs also encrypt all your internet traffic, making them a must-have privacy tool. Besides making web surfing more anonymous, VPNs and proxies can also be used to evade firewalls and unblock location-restricted content such as Netflix.
OpenVPN
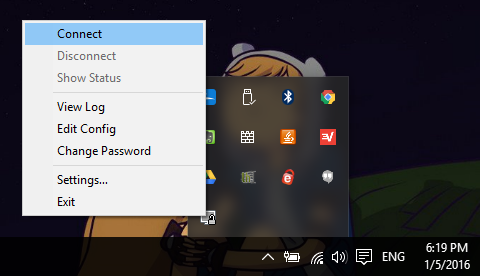
Most paid VPNs utilize the free OpenVPN protocol. OpenVPN offers a user-friendly GUI, but requires a server to connect to. Check out our guide on how to roll your own VPN with OpenVPN and a free Amazon Web Services account.
OS: Platform agnostic
Windscribe
One of the better free VPNs out there, if you opt to go the free route. Offers unlimited bandwidth, a decent range of server locations, and ad-free browsing.
OS: Windows, MacOS, iOS, Android,
Proxy SwitchySharp
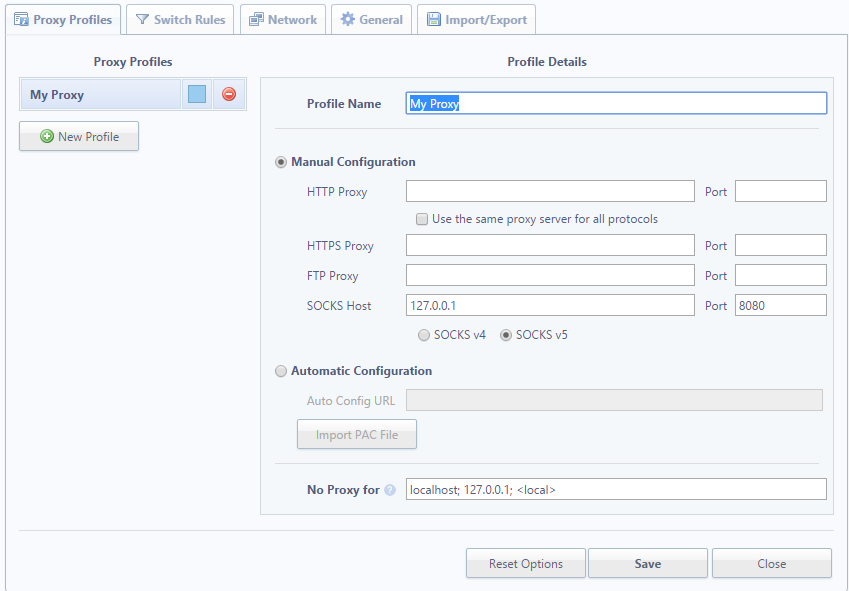
Browser extension that allows you to manage and switch between proxies. Can specify specific domains to access through the proxy.
Platform: Chrome
FoxyProxy
A browser extension for managing and switching between proxies similar to Proxy SwitchySharp, but for Firefox.
Platform: Firefox
Tunnelbear
A mobile VPN that offers up to 500MB of data per month for free. More data is available in the paid tiers.
Platform: Android, iOS, MacOSX, Windows, Chrome, Opera
Cocoon
Cocoon is a privacy-focused web browser with a built-in encrypted proxy that can be toggled on or off at any time. It’s marketed toward expats in China who want an easy way to access websites blocked by the Great Firewall. It will also mask your IP address, store all cookies in an isolated cloud so they cannot be used to identify you, and run real-time antivirus. The company does inject ads from its internal ad network into the browser, but these ads are based only on the URL and content of the page you are currently visiting. The company does not log any of your browsing activity, nor does it share any of your info with third parties.
DNS Leak Test

Once you have a VPN, it’s a good idea to test it for leaks. Leaks occur when information is sent through the internet but outside of the VPN tunnel. This can divulge your real IP address and location to your ISP or someone else. Comparitech’s own DNS Leak Test scans for DNS, IPv6, and WebRTC leaks.
Antivirus
Antivirus scans, quarantines, and removes malicious files from your computer. Typically an antivirus program covers viruses, malware, spyware, and other threats, but some are limited to a specific type. Not only do these menaces threaten to damage your computer and files, but many of them also invade your privacy by collecting personal information or injecting ads into your browser.]
Bitdefender
A great and effective entry-level antivirus program with a free edition. Read our full review of Bitdefender here.
OS: Windows, iOS
Malwarebytes
A scan and removal tool that focuses on Malware, including Trojans, rootkits, rogues, spyware, and more. Offers a free tier.
OS: Windows, MacOSX, Android
Panda
Perhaps the most lightweight of the reputable free antivirus programs out there. Includes a file encryptor and file shredder, wi-fi protection, and parental controls among other features. The Windows version includes the most features, while others are more basic.
OS: Windows, MacOSX, iOS, Android
Backup and Storage
Many of us use online backup and storage services like Google Drive and Dropbox, but most are not encrypted and protected to a degree we can honestly consider private. Here we’ve listed some options that are up to Comparitech’s privacy charter standard.
IBackup
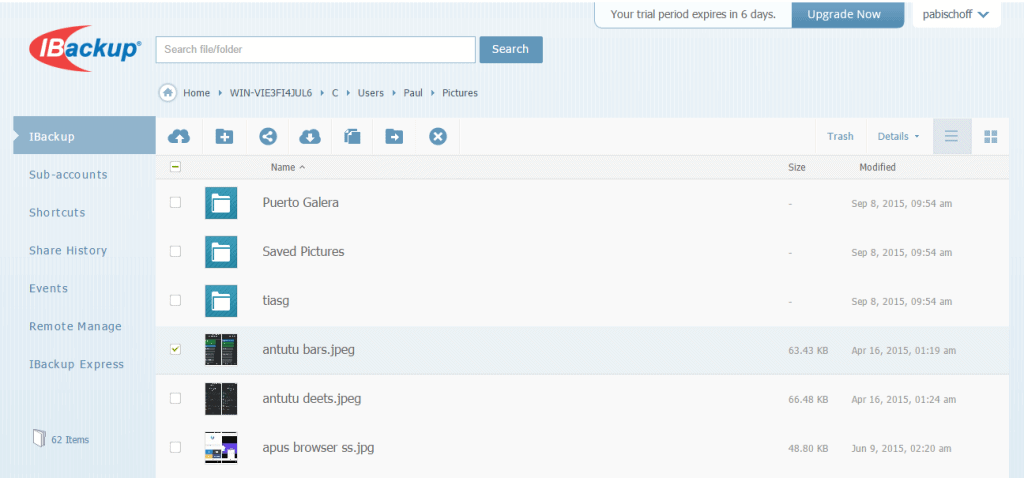
Cloud backup service with a 5GB no-expiration free tier. Meets our cloud backup privacy charter requirements when it comes to encryption and security practices. Can also back up photos and videos from social media accounts.
OS: Windows, MacOSX, Android, iOS, Windows Phone
Crashplan

Backup software that’s free if you provide your own storage media, such as an external hard drive or a second computer. Cloud backup on Crashplan’s servers requires a subscription. Meets our cloud backup privacy charter requirements. Read our Crashplan review here.
OS: Windows, MacOSX, Linux
File encryption apps
These apps allow you to encrypt selected files on your device. Many of them can be used to encrypt files and folders prior to uploading to the cloud, which keeps your data safe even on vulnerable servers.
Boxcryptor
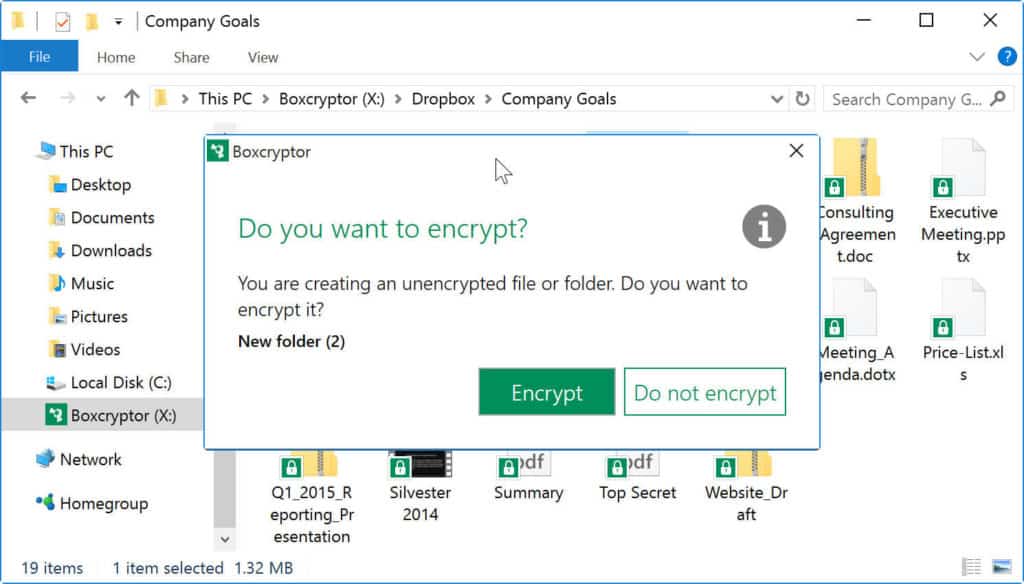
Allows you to create a folder anywhere on your computer, and everything placed in that folder is encrypted using the 256-bit AES standard. To view the files in that folder, run the Boxcryptor app, navigate to the desired file, and enter your password/key. If you’re using a cloud storage service like Google Drive or Dropbox, this folder can be placed inside the respective app’s sync folder.
OS: Windows, MacOSX, Chrome, iOS, Android, Windows Phone, Blackberry
Viivo
Update: Viivo has been discontinued.
Viivo creates two folders on your computer. The first is just a seemingly normal folder stored locally where you put files. The second folder makes a copy of everything in the first folder and encrypts it. The second folder is the one you want to upload to the cloud. It can be put in your Dropbox or Google Drive folder, for instance.
OS: Windows, MacOSX, iOS, Android
nCrypted Cloud
nCrypted Cloud places Google Drive, Dropbox, and other supported cloud storage sync folders into an nCrypted Cloud folder. Encryption doesn’t happen automatically. Right click files within those folders to encrypt and decrypt them. The blue lock icon next to the file or folder icon indicates it has been made private and is now encrypted with the AES 256-bit.
OS: Windows, MacOSX, iOS, Android
Cloudfogger
Update, 11 June 2016: Cloudfogger has been discontinued.
Cloudfogger lets you select existing folders to encrypt rather than having to create new ones. This is often a better option for those who have a lot of files that need to be encrypted but don’t want to move them around.
OS: Windows, MacOSX, iOS, Android
EncFSMP
EncFSMP uses much of the same open-source code as BoxCryptor and works in a similar manner. Create an encrypted folder anywhere on your local drive, and anything you put in that folder is automatically encrypted. You can create, edit, and export passwords for these folders.
OS: Windows, MacOSX
Cryptonite
A file encryption app for Android that uses the open source EncFSMP (see above). Creates a folder on your device, which you can place in a Dropbox or Google Drive sync directory. Anything placed in this folder is encrypted before being uploaded to the cloud.
OS: Android (Update: no longer on Google Play, only available on GitHub)
AxCrypt
File encryption software that integrates with Windows to compress, encrypt, decrypt, store, send and work with individual files.
OS: Windows
Read more: The best apps to encrypt your files before uploading to the cloud
Disk encryption software
These apps will encrypt your entire hard disk, making it impossible for anyone to access anything on your computer without the encryption key. Some come pre-installed on Windows and Mac computers.
Diskcryptor
A full disk encryption system that can encrypt either the entire hard drive or a specific partition, including the partition that the OS is installed on. Diskcryptor uses 256-bit AES, Twofish, Serpent or a combination of cascaded algorithms in XTS mode to carry out encryption.
OS: Windows
FileVault 2
Similar to Diskcryptor, but for Macs. Encrypts the entire OSX startup volume using 128-bit AES/XTS. Filevault 2 performs on-the-fly encryption and decryption. Requires OSX Lion or later and a working recovery volume.
OS: MacOSX
BitLocker
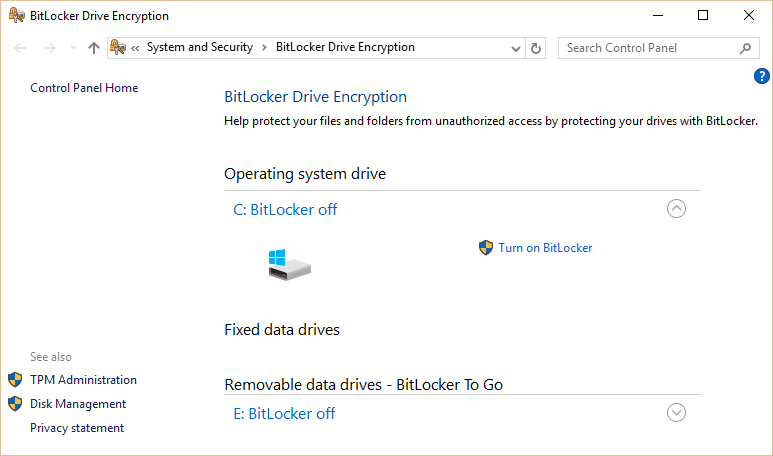
A full disk encryption system similar to Diskcryptor that comes pre-installed on some versions of Windows.
OS: Windows
VeraCrypt
The successor to TrueCrypt, VeraCrypt is a full disk and partition encryption system that claims to be more immune to brute force attacks than competitors. Accessing encrypted partitions is slowed down, but does not effect applications in use.
OS: Windows, MacOSX, Linux, Android, iOS
Secure messaging apps
If you’re worried about someone snooping on your online conversations, these apps offer end-to-end encrypted chat capabilities. Some are standalone products, while others work with existing messenger apps.
Cryptocat
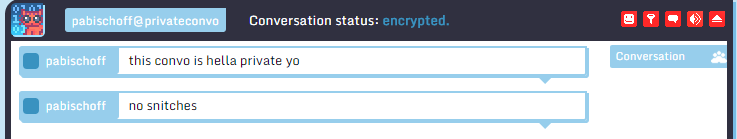
Chat app that encrypts messages on local device before sending. Supports group chats, file and photo sharing, and can scan Facebook Messenger to see which of your friends are also using Cryptochat.
Platform: Chrome, Firefox, Safari, Opera, MacOSX, iOS
Pidgin
A free chat client that encrypts messages sent through AIM, MSN, Yahoo, and several other desktop chat networks.
OS: Windows, MacOSX, Linux
TorChat
Decentralized peer-to-peer instant messaging client that utilizes the location-hiding Tor network. No need to install or configure. Can run from a USB drive.
OS: Windows, Linux
Password Managers
If you have trouble memorizing all your passwords, these apps allow you to remember just one master password to unlock all your accounts, both on the web and on desktop applications. Besides the convenience aspect, it also helps protect users from keylogging viruses that track what you type.
LastPass
Browser plugin that stores passwords for you so you only need to remember one. Passwords are stored with AES-256 bit encryption, salted hashing, and PBKDF2 SHA-256. LastPass cannot gain access to your passwords. LastPass is one of our favorite password managers, you can get it free here or if you want to read more first head over to our LastPass review.
Platform: Windows, Mac, Linux, iOS, Android, Blackberry, Windows Phone, Firefox OS, Microsoft Surface RT, Chrome
KeePass
Similar to LastPass. Stores passwords for all of your installed apps and programs in addition to websites and apps. It’s slightly more tricky to configure than most password managers but is very popular among techies. Our KeePass review has more details.
OS: Windows, MacOSX, Linux
MasterPassword
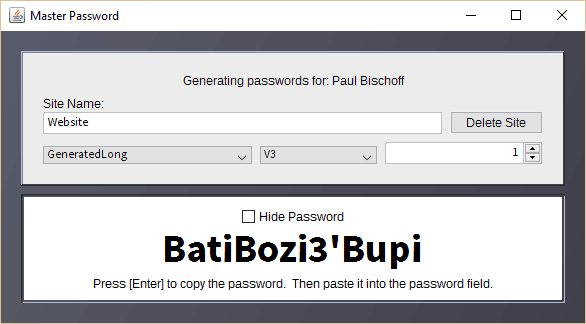
A password manager that guarantees your passwords can never be lost. Instead of storing passwords in an encrypted vault like other password managers, your passwords are generated on demand from your name, the site, and the master password. This algorithm-based model makes it so you don’t need to sync, restore, or even be connected to the internet to access your passwords, and it even works on devices you’ve never used before.
Platform: iOS, Android, MacOSX, Windows, web app
DataVault Password Manager
The free Android version of DataVault Password Manager by Ascendo secures passwords using 128-bit AES encryption. Supports fingerprint authentication. You can easily view all the accounts that you’ve stored passwords for in a categorical list view. You can also set it to time out or wipe data after multiple failed login attempts.
Platform: Android, Windows (free trial), Mac and iOS (paid)
Strong Password Generator
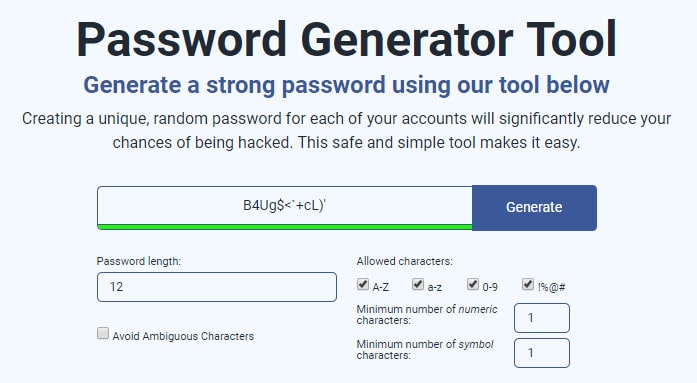
Comparitech’s own Smart Password Generator instantly creates unique, random passwords that you can use with all of your accounts, significantly reducing the chances of being hacked. The tool runs completely in your browser and nothing is sent to the server.
Password Strength Test
If you already have a password and just want to test how strong it is, you can use Comparitech’s Password Strength Test. Using a number of different factors, we can analyze your password for weakness and give you an estimate of how long it would take a hacker to brute force it. Everything happens on the front end in your browser and no information is sent to our servers.
Email Encryption
Email is a communication used by most everyone online and won’t be going anywhere anytime soon. The problem is that email isn’t encrypted and has serious privacy flaws. These apps let you encrypt your email correspondence so only the intended receiver can decrypt it.
Mailvelope
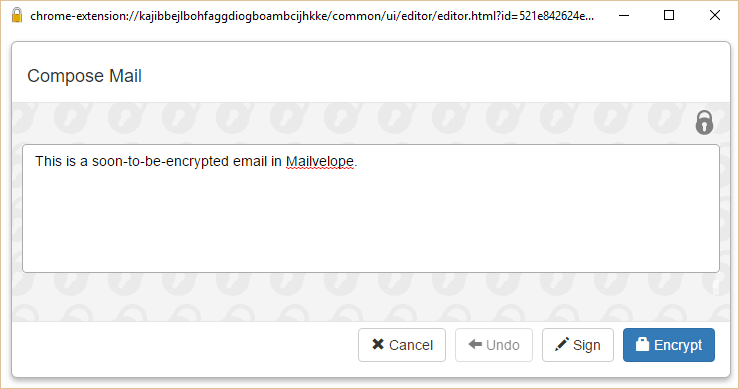
A browser extension that integrates with your web-based email client, such as Gmail. Lets you create, import, and store public encryption keys. A button in the composer will let you write and encrypt messages within normal email. Uses PGP encryption. Can also be used to decrypt email.
Platform: Chrome, Firefox
EnigMail
A browser extension similar to Mailvelope that encrypts email using OpenPGP.
Platform: Firefox
GPGTools
Email encryption tool for Apple Mail. Encrypt, decrypt, sign, and verify email. Note that Macs come with an encryption protocol pre-installed called S/MIME as opposed to PGP/MIME, so this may be redundant.
OS: MacOSX
GNU Privacy Guard
Encryption software used to encrypt any file on a computer. That file can be sent to someone else, and only that person can decrypt based on the PGP key-pair system.
OS: Windows*, MacOSX, Linux
Thunderbird
From the makers of Firefox, Mozilla’s Thunderbird email program is a customizable, open-source alternative to Outlook and web-based email clients. It includes a series of security features including Do Not Track and phishing protection.
OS: Windows, MacOSX, Linux
Ad Blockers
Advertisements online aren’t just annoying, they often contain malicious code that steals your personal data or try to serve you viruses. Ad blockers solve both problems. Some specifically target malicious ads, while others block advertisements altogether.
Adblock Plus
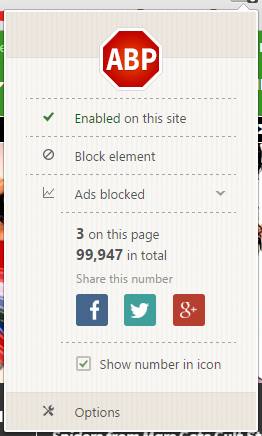
A browser extension that blocks malicious ads that track users, serve malware, and are generally annoying. Customizable and comes with a whitelist of tolerable ads to support websites.
Platform: Firefox, Chrome, Android, Opera, Internet Explorer, Safari, Yandex, Maxthon, Edge
Privacy Badger
A browser extension that blocks ads and other webpage elements that attempt to track users. Technically not an ad blocker, but ends up blocking many ads that track users or serve malware. One of the few extensions that blocks fingerprinting, an up-and-coming method of tracking users that could one day replace cookies.
ublock
A lightweight ad blocker extension that also weeds out tracking and overhead to make browsing faster.
Platform: Chrome, Safari, Firefox
Nixory
Browser extension that focuses less on ads and more on preventing spyware and tracking.
Platform: Chrome, Firefox, Internet Explorer
Ghostery
An anti-tracking and ad-blocking extension that claims to have the largest database of tracking companies. Emphasizes control of which trackers are allowed and which aren’t.
Platform: Chrome, Firefox, Safari, Opera
Anonymizers
These apps make your online activity anonymous to anyone who might be snooping. Most of these apps are Tor-based, which bounces your connection off a series of relays, making your effectively untraceable.
Peerblock
Peerblock keeps a running blacklist of IP addresses from known “bad” computers. It’s long been used by frequent torrent downloaders to prevent record and movie industry minions from monitoring P2P activities, but it also blocks communication with spyware and advertising servers, those that have been compromised by hackers, and even entire countries. The blacklist is split up into several categories such as education, P2P, spyware, etc.
OS: Windows
Tor
Tor is one of the oldest and most popular ways to make yourself anonymous online. Also known as the onion router, Tor is a network of relays scattered around the world. Users’ internet connections are bounced around these relays at random, preventing snoops from analyzing your web traffic and figuring what your up to.
OS: Agnostic
Tor Browser
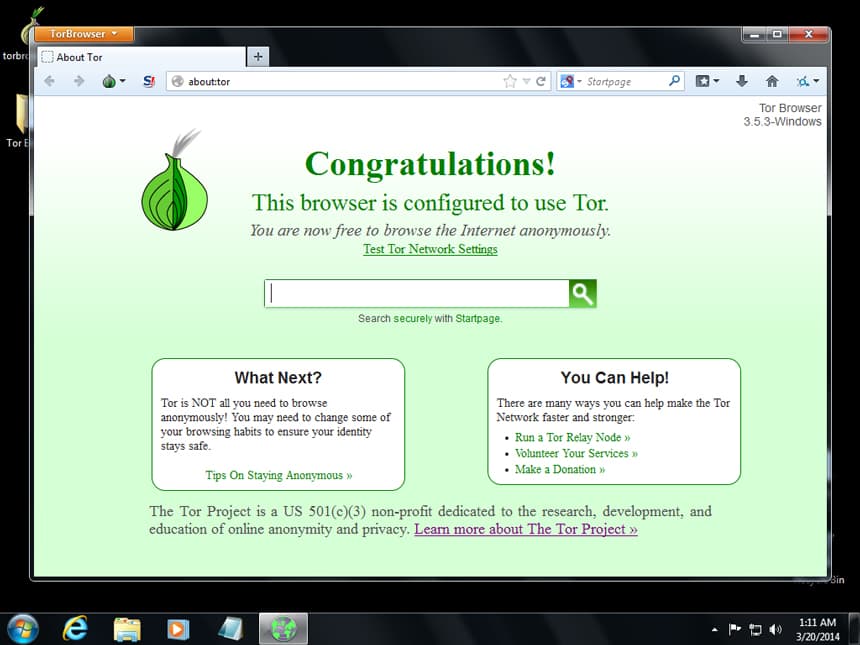
A web browser that utilizes the Tor network and includes some other privacy-minded features. With no need to install, it can run off a USB flash drive.
OS: Agnostic
Tails
Another tool built by the people who brought us Tor and Tor Browser, Tails is an entire self-contained operating system that can be run from a USB drive, DVD, or SD card. Files, emails, and instant messages are all encrypted, and no trace of Tails or anything you do on it is left on your computer.
OS: Agnostic
Orbot
The Tor network app for Android phones.
OS: Android
I2P
Similar to Tor, this “network within a network” makes online activity and communication anonymous to surveillance and monitoring.
OS: Windows, Mac, Linux, Android
Search engines
Every time you enter a search query into Google, Google remembers. The same goes for most other mainstream search engines. If you don’t want your searches associated with your online dossier, try one of these anonymous search engines.
StartPage
When you enter a query into StartPage, it removes all identifying information and submits it to Google on your behalf. It doesn’t record your IP address, log your visit, or use tracking cookies. Can be added to Chrome as the default search engine. All search results come with a proxy link underneath them, allowing you to click through to any site while retaining your privacy through a proxy.
DuckDuckGo
Unlike StartPage, which uses Google, DuckDuckGo is an entirely independent search engine. It doesn’t use tracking cookies and comes with a fair amount of customization for users. Can be set as the default search engine in Chrome.
ixquick
By the same people who make StartPage, ixquick is pretty much identical except it combines and returns results from several top search engines (instead of just Google) after scrubbing your personal information from the query. Offers advanced search, global search, and power search.
Disk wiping
These apps completely wipe a computer of everything except the operating system. They even remove the footprints left behind by deleted files and leave no proof that they were ever used.
Darik’s Boot and Nuke
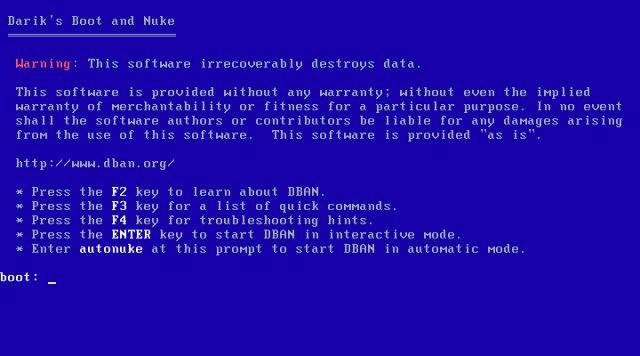
Erasure software that deletes the contents of all detected hard disks from a bootable USB drive or CD/DVD. Useful if you need to wipe a computer clean before recycling or selling it. Leaves no certifiable proof that the hard drives were wiped. If you need to wipe a solid state drive (SSD), then try DBAN’s sister software, Blancco 5.
OS: Agnostic
Eraser
Even after you delete a file, that empty space left over leaves a footprint. Eraser completely removes selected files from Windows by overwriting it several times with “carefully selected patterns.”
OS: Windows
Intrusion detection
These apps monitor your computer and incoming internet traffic in real time to detect intrusions by hackers and probes.
Snort

Open source network intrusion prevention system that performs real-time traffic analysis used, among other things, to detect probes and attacks.
OS: Windows, Linux
OSSEC
Intrusion detection system that performs file integrity monitoring, log monitoring, rootcheck, and process monitoring. Sends alerts via email and the program log.
OS: Windows, MacOSX, Linux
Windows 10 anti-spying
As more and more PC owners make the jump to Windows 10, criticism has surfaced regarding the operating system’s quiet collecting of user activity. Prevent Windows 10 from spying on you and sending information to Microsoft by using these tools.
Spybot Anti-beacon
A lightweight application for disabling any and all tracking features built into Windows 10 that sends usage information to Microsoft. More recently it’s been updated to block Windows 7, 8, and 8.1 tracking as well.
OS: Windows
W10 Privacy
Aggregates several privacy settings in Windows 10 that are normally hidden in multiple, disparate menus into a single place.
OS: Windows
O&O ShutUp10
Similar to W10 privacy in that it aggregates several disparate privacy settings into one place on Windows 10. Does not require installation and runs immediately from the executable file downloaded to your PC.
OS: Windows
Destroy Windows 10 Spying
Like W10 Privacy and O&O ShutUp10, this app lists several Windows 10 privacy settings under three simple tabs: Main, Settings, and Utilities.
OS: Windows
TinyWall
A free lightweight firewall that lets you control the advanced firewall settings built into Windows more easily, plus other added protections. Simple and doesn’t require much technical skill.
OS: Windows
Windows 10 and VPNs
Windows 10 users can add a further layer of anonymity with a VPN. We do have a list of the best VPNs for Windows 10 however none of the free options made our top recommendations. Even so, picking one of the better free VPNs is better than not having one. Head back up to the free VPN section near the top of this article to see some of our preferred options.
Fake/burner email
If you want to send an anonymous email from a fake or temporary account, these apps have your back. Useful to register for one-off online accounts.
Proton Mail
Switzerland-based end-to-end encrypted email service. Open source, zero-knowledge, donation-based web and mobile apps. Must apply for an invite due to limited server capacity.
Platform: web app, iOS, Android
Zmail
Email software that lets you send emails from fake email addresses. Useful if you don’t want to use your actual email or open your regular email client. It’s also useful for testing email servers.
OS: Windows, MacOSX, Linux
Guerrilla Mail
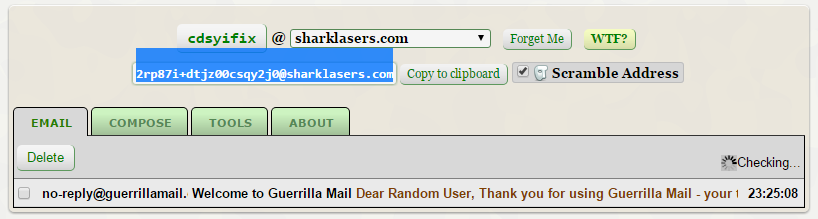
Temporary disposable email address service. No registration required. Can be used to register for websites where you don’t want to give out your real email address. It even includes a password manager to help remember the passwords associated with those email addresses.
Social media privacy
Over a billion people have Facebook accounts, but we’re willing to bet only a fraction of them understand the depths of all the privacy settings available to them. These tools help manage and monitor your privacy on the world’s biggest social networks.
Privacy Checkup
A relatively new feature built into Facebook that gives you a sort of interactive tour through the main Facebook privacy settings. To find it, click the lock icon next to your notifications on Facebook’s desktop version. Privacy Checkup is useful, but it still overlooks a couple of important settings and can’t be reached manually on mobile.
Platform: Facebook
Other Mobile Apps
Any mobile apps that we couldn’t categorize into the above groups, we put here. That doesn’t make them any less important, though.
Signal
Encrypted voice calling and instant messaging app for smartphones. All chats, files, photos, and voice calls are encrypted. Users can verify the identity of their correspondents by comparing key fingerprints. During calls, users can check the integrity of the data channel by checking if two words match on both ends of the call.
OS: iOS, Android
LBE Privacy Guard
An Android app that helps you more easily control the granular permissions requested by other apps. It intercepts apps’ vital actions like sending SMS or making phone calls and requests to sensitive information, then asks the user to confirm these actions and requests before continuing. Anything not explicitly OK’ed by the user is rejected.
OS: Android
Other browser extensions
A few more useful browser extensions to make surfing the web more anonymous, secure, and private.
NoScript
Allows JavaScript, Java, Flash and other plugins to be executed only by trusted web sites of your choice to prevent malicious attacks. Includes a whitelist of trusted sites. Blocked scripts can be unblocked from the status bar at the top of the browser or by right-clicking and selecting the option from the context menu.
Platform: Firefox
ScriptSafe
Similar to NoScript, but for Chrome.
Platform: Chrome
Click&Clean
Chrome extension that checks whether you have enhanced private data protection and will help you to prevent tracking of your online activity. Deletes browsing data when Chrome closes and scans your PC for Malware.
Platform: Chrome
Disconnect
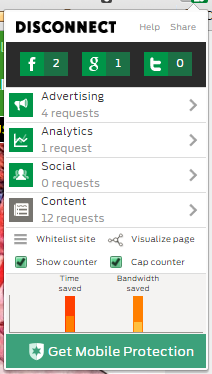
Disconnect combines a variety of tactics to create a suite of anti-tracking tools. It disables tracking cookies, encrypts browsing data, blocks malware, and anonymizes search queries. A premium version is available that comes with a VPN and some other extras.
Platform: Chrome, Firefox, Safari, Opera, iOS, Android
HTTPS Everywhere
Many websites have HTTP and HTTPS versions of their sites. HTTPS Everywhere forces the latter, more secure versions to load whenever available.
Platform: Chrome, Firefox, Firefox for Android, Opera
DNS
DNS, or domain name systems, are what allow you to type in “comparitech.com” instead of an IP address made up of seemingly random numbers. Default DNS resolvers, however, can be poisoned by hackers, are vulnerable to phishing scams, and can monitor user activity. These alternatives offer a safer solution.
DNS.WATCH
This free DNS resolver promises to never keep logs or censor content. It promises speed on top of privacy.
OpenDNS
Extends the domain name system (DNS) to add phishing protection and content filtering. Despite the name, it is not open-source software.
Google DNS
Alternatively, you can also try out Google’s public DNS service. The procedure for changing your DNS settings varies according to the operating system and version and the device.
OS: Platform agnostic
Other desktop tools
A few final tools for your consideration.
Evernote Encryption
If you’re an Evernote user, you can encrypt notes containing sensitive information. The note title and metadata is not encrypted, only the content. It appears as a lock icon which you click, then type in a password. Unique passwords can be set for each note.
KeyScrambler Personal
Free keyboard encryption software. Should your computer be infected with a keylogger, which records every keystroke and sends what you type to thieves and hackers, this tool scrambles the output so attackers get the indecipherable encrypted text.
Wireshark
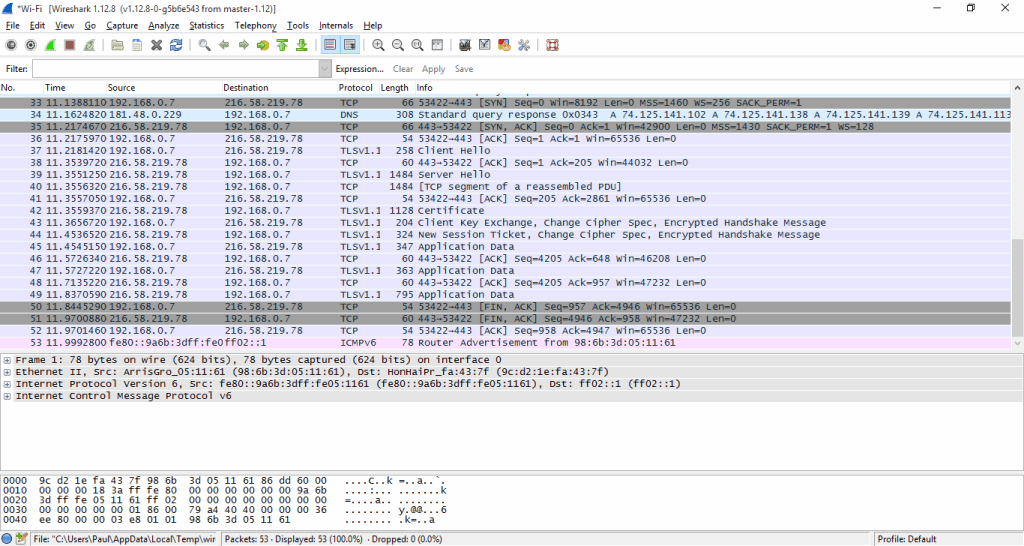
A network protocol analysis tool that can be used to track all traffic to and from a computer. Not a privacy tool in itself, but check out how we used it to find out which country our cloud data is being stored in.
Window Washer
Deletes traces of activity left on your computer and clears up disk space.
OS: Windows
Panopticlick
This simple web-based tool from the Electronic Frontier Foundation analyzes your browser to check for potential privacy vulnerabilities. It checks to see if your browser blocks tracking ads, invisible trackers, and fingerprinting, and will give you a detailed analysis of any that aren’t blocked. We recommend using this after you’ve finished installing the browser extensions on this list.
Platform: Agnostic
Do Not Track
This website lets you know if you’ve enabled anti-tracking settings in your browser. If not, it will direct you to an external website with instructions for how to disable tracking. The Do Not Track registry is sort of like the web version of the United States’ Do Not Call registry. It requests websites not track you by adding an HTTP header to websites you visit.
Platform: Agnostic
Something we missed? Let us know in the comments!









hi, how come you didn’t include Epic Browser? thx!
Another notable Fake/burner email service for receiving emails/messages from others is EmailOnDeck (https://www.emailondeck.com).
They utilize HTTPS, TLS and securely wipe their logs.
Hi Paul,
Great list, thanks for putting it together. Disconnect runs on PCs too, and I would suggest it is better than Ghostery – who make money from the analysis of your activity. Blur is also a good alternative for blocking trackers, as well as disguising the emails you provide to sign up to services. Its premium edition does something similar with your credit card details.
I would suggest our own product, incloudnito, but it is not free! Frustrated by the amount of trouble required to be anonymous, we decided the only way would be to give users secure access to a virtual machine (VM). The browser on the VM is configured to stop tracking. The VM connects to all the sites, so any malware or spyware, doesn’t end up on your own device.
Some of the tools above are used to improve the security of the VMs. Control over the configuration, and the ability to kick of a ‘clean’ instance, means we can cater to the needs of the most security-conscious clients. These are the folks we designed it for! Let me know if you would like more information, or go to the site and request a free trial.
Hi Sean, thanks for commenting. This list is reserved for free tools only (otherwise there’d be no end to it!) but I’d be happy to try out incloudnito in a different capacity.
I have a couple of suggestions for those worried that Windows 10 is spying on them. Take a look at SpyBot Anti-Beacon, W10 Privacy (here: http://www.winprivacy.de/) and O&O ShutUp10.
Thanks Stuart, I’ll take a look at these and add them in.
Under (or above) Snort, you should have added Tinywall (Windows), the “free, lightweight and non-intrusive firewall.” It’s absolutely essential, IMO.
It’s not OSS, but it is “no cost, 100% free, no ads, no artifical limitations, no upgrades.”
If you install it on Win10 you can get frustrated watching your PC repeatedly send data collected about you to hundreds of Microsoft IPs.
Hi Timmy,
Thanks for the suggestion. I’ll add it to the list!
-Paul